New studies from each Microsoft’s Digital Crimes Unit and the U.S. Division of Justice expose a disruptive operation towards greater than 100 servers utilized by “Star Blizzard” — a Russian-based cyber menace actor specializing in compromising e-mail packing containers to exfiltrate delicate content material or intrude with the goal’s actions.
Who’s Star Blizzard?
Star Blizzard is often known as Seaborgium, Callisto Group, TA446, Coldriver, TAG-53 or BlueCharlie. Based on numerous authorities entities across the globe, Star Blizzard is subordinate to the Russian Federal Safety Service (FSB) Centre 18.
The menace actor has been lively since not less than late 2015, based on a report from cybersecurity firm F-Safe. The report indicated the group focused navy personnel, authorities officers, and assume tanks and journalists in Europe and the South Caucasus, with a main curiosity of gathering intelligence associated to overseas and safety coverage in these areas.
Based on studies:
- Since 2019, Star Blizzard has focused the protection and governmental organizations within the U.S. in addition to different areas similar to the educational sector or totally different NGOs and politicians.
- In 2022, the group expanded and began focusing on defense-industrial targets in addition to US Division of Power services.
- Since January 2023, Microsoft has recognized 82 totally different targets for the menace actor, at a fee of roughly one assault per week.
SEE: Easy methods to Create an Efficient Cybersecurity Consciousness Program (TechRepublic Premium)
Modus opérandi
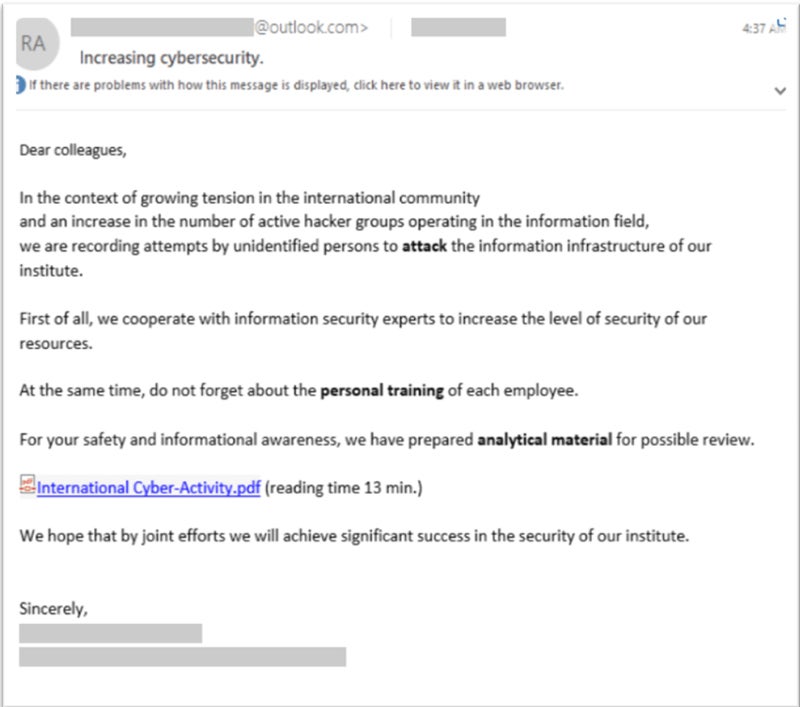
Star Blizzard is understood for organising infrastructure to launch spear phishing assaults, usually focusing on the private e-mail accounts of chosen targets. These accounts usually have weaker safety protections than skilled e-mail accounts.
As said by Microsoft’s Assistant Basic Counsel Steven Masada in a press launch: “Star Blizzard is persistent. They meticulously research their targets and pose as trusted contacts to realize their targets.”
As soon as infrastructure is exploited, the menace actor can shortly swap to new infrastructure, rendering it tough for defenders to detect and block the used domains or IP addresses. Particularly, the group makes use of a number of registrars to register domains and leverage a number of link-shortening providers to redirect customers to phishing pages operated utilizing the notorious Evilginx phishing package. The group additionally makes use of open redirectors from reputable web sites.
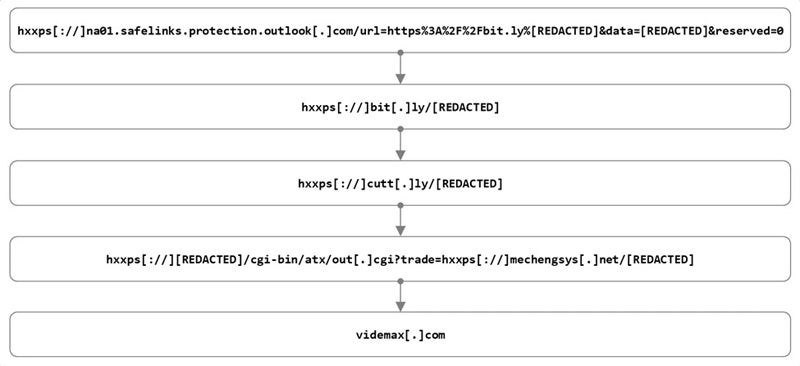
The menace actor has additionally used altered variations of reputable e-mail templates, similar to OneDrive file share notifications. On this case, the group used newly created e-mail addresses meant to impersonate a trusted sender so the recipient could be extra more likely to open the phishing e-mail. The e-mail would include a hyperlink to a modified PDF or DOCX file hosted on a cloud storage service, in the end resulting in the Evilginx phishing package. This allowed the attackers to execute a man-in-the-middle assault able to bypassing Multi-Issue Authentication.
Huge disruption
The DOJ introduced the seizure of 41 Web domains and extra proxies utilized by the Russian menace actor, whereas a coordinated civil motion from Microsoft restrained 66 further domains utilized by the menace actor.
The domains had been utilized by the menace actor to run spear phishing assaults to compromise focused techniques or e-mail packing containers, for cyberespionage functions.
Star Blizzard is predicted to shortly rebuild an infrastructure for its fraudulent actions. Nonetheless, Microsoft studies that the disruption operation impacts the menace actor’s actions at a important second, when overseas interference in U.S. democratic processes are at their highest. It can additionally allow Microsoft to disrupt any new infrastructure sooner via an current courtroom continuing.
Need safety from this menace? Educate and prepare your employees.
To keep away from Star Blizzard, studies recommend that organizations ought to:
The menace actor’s phishing emails seem like from recognized contacts that customers or organizations anticipate to obtain e-mail from. The sender deal with could possibly be from any free e-mail supplier, however particular consideration needs to be paid to emails acquired from Proton account senders, because the menace actor has usually used that e-mail supplier prior to now.
Ought to doubt come up, customers shouldn’t click on on a hyperlink. As an alternative, they need to report the suspicious e-mail to their IT or safety employees for evaluation. To attain this, customers needs to be educated and skilled to detect spear phishing makes an attempt.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.
