The truth of PCAPs (packet seize) are that they’re time consuming to create. A number of laborious steps are concerned:
- Discovering a platform that’s in-path and able to internet hosting a PCAP software (if there even is one)
- Executing the PCAP
- Transferring the file to a system to investigate — and these recordsdata could be very giant. This will likely contain the extra step of deploying SFTP or SCP succesful functions on either side of the switch
The web results of all this overhead is that usually I don’t use them until there’s no different alternative. It was transformative within the Black Hat USA 2025 NOC to have the ability to take any observable that correlates to a system and easily proper click on it from the Firepower Administration Middle (FMC) utilizing the ‘Endace PCAP Pivot’ choice, to a richly featured packet evaluation platform, which features a Wireshark integration. The web result’s that I used packet-level evaluation 99% extra typically to large impact in my SOC analyst investigations.
“I used packet-level evaluation 99% extra typically to large impact in my SOC analyst investigations.”
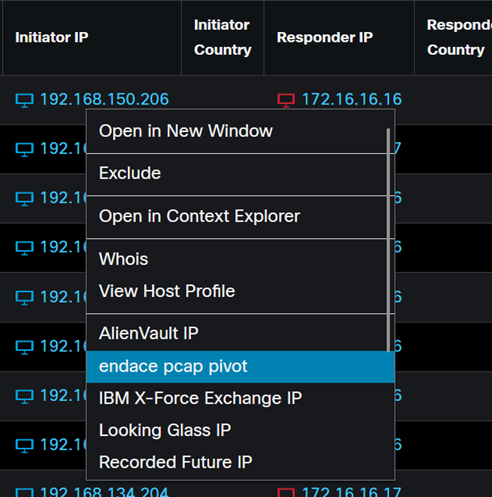
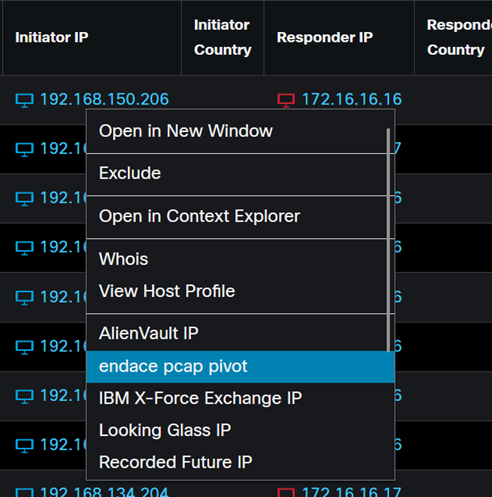
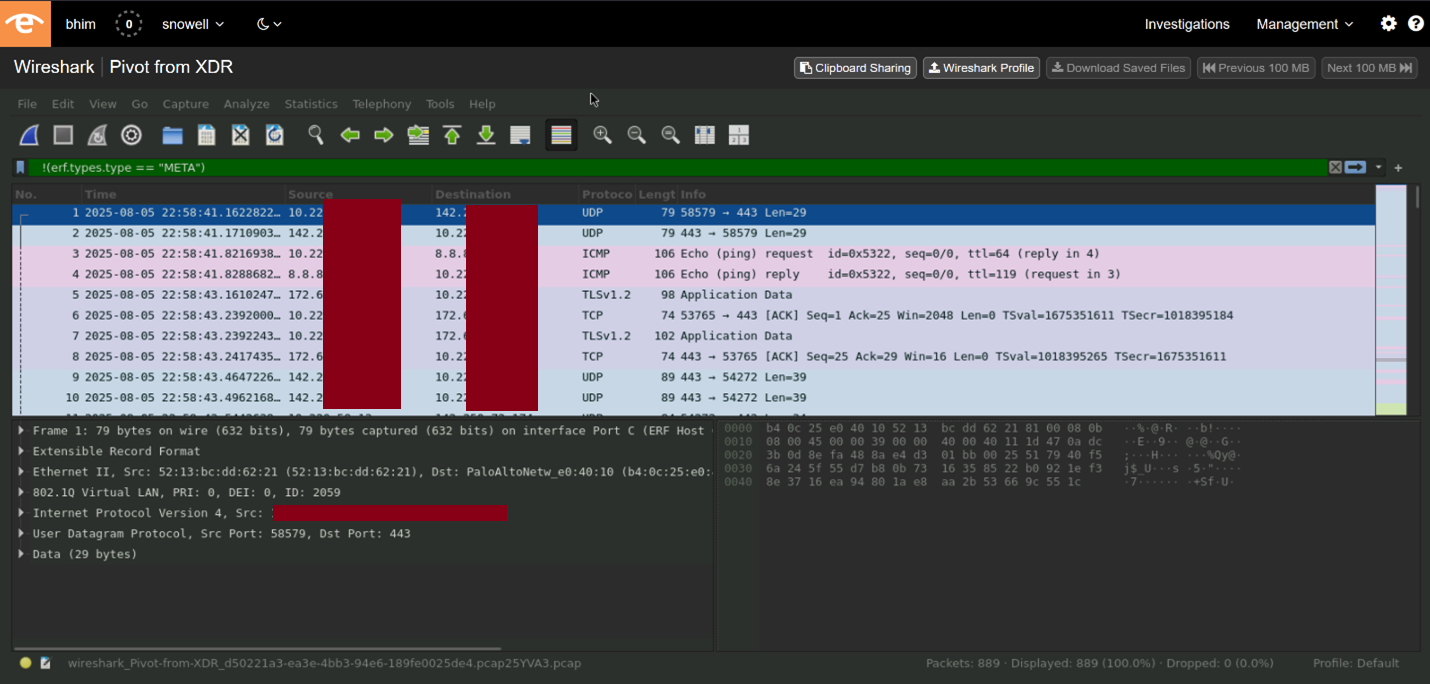
This workflow allowed me to immediately entry the precise packet-level knowledge associated to the observable. As a substitute of relying solely on metadata or logs, I can view the definitive community visitors, together with payloads, timestamps, and session particulars, which gives complete context for my investigations. This direct pivot accelerates my workflow by eliminating guide correlation steps and decreasing the time it takes to validate threats by extra oblique means.
As soon as I’ve pivoted to Endace Imaginative and prescient from the FMC, I acquire the power to carry out back-in-time forensic evaluation on the captured community visitors related to the observable, shifting from one-click right into a high-level visitors composition evaluation. There’s further evaluation out there right here, however that is the Endace Vison facet that’s related to this investigation.
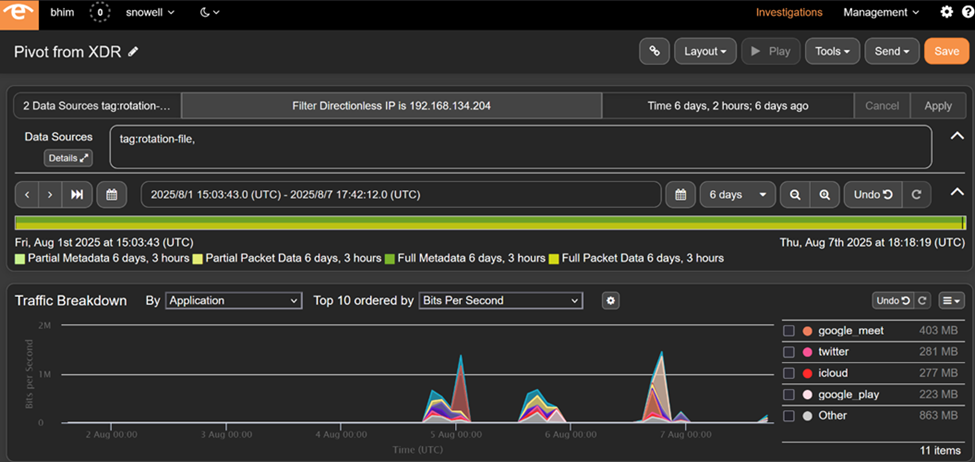
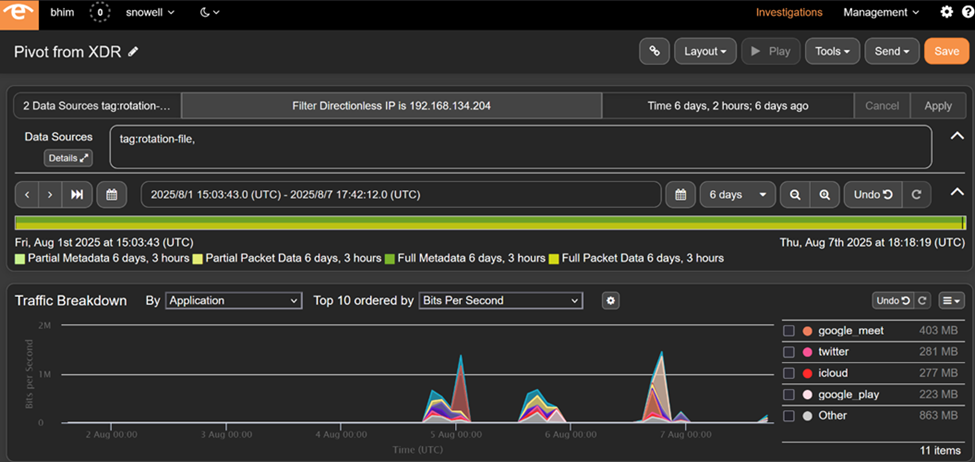
This implies I can reconstruct the total sequence of occasions main as much as, throughout, and after the alert, uncovering hidden assault vectors that may not be evident from alert knowledge alone. The mixing additionally helps real-time and historic visitors evaluation, permitting me to correlate stay menace intelligence with previous community exercise. This holistic view enhances my menace searching and incident response capabilities, enabling extra correct root trigger evaluation and finally quicker containment of safety incidents.
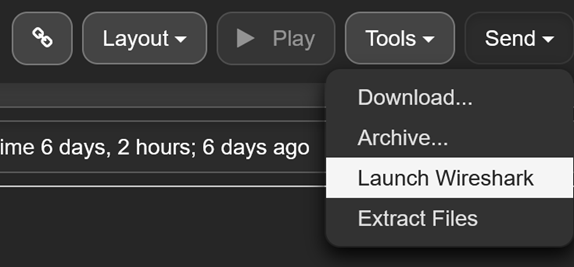
Pivoting from FMC to Endace Imaginative and prescient streamlines my SOC workflows by tightly coupling alerting and proof assortment inside a single operational setting. A single click on allowed me to pivot right into a Wireshark packet degree evaluation for my investigation.
I might drill down from high-level alerts within the Firepower Administration Middle straight into Endace Imaginative and prescient’s packet-level interface with out switching instruments. This seamless transition reduces operational friction, permitting me to answer threats with a exact immediacy that isn’t out there with out it. The mixing additionally helps automated workflows and enriches alert knowledge with definitive packet proof, enhancing the general efficacy of my safety investigations, that took moments, not hours, to allow packet detailed evaluation.
I sit up for utilizing this functionality in different Safety Operation Facilities. Try my weblog sequence on different SOC work.
About Black Hat
Black Hat is the cybersecurity business’s most established and in-depth safety occasion sequence. Based in 1997, these annual, multi-day occasions present attendees with the newest in cybersecurity analysis, growth, and tendencies. Pushed by the wants of the group, Black Hat occasions showcase content material straight from the group by Briefings shows, Trainings programs, Summits, and extra. Because the occasion sequence the place all profession ranges and educational disciplines convene to collaborate, community, and focus on the cybersecurity subjects that matter most to them, attendees can discover Black Hat occasions in america, Canada, Europe, Center East and Africa, and Asia. For extra info, please go to the Black Hat web site.
We’d love to listen to what you assume! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media
Share:
