Safety professionals are at all times looking out for evolving menace methods. The Sophos X-Ops workforce lately investigated phishing assaults concentrating on a number of of our staff, one among whom was tricked into giving up their data.
The attackers used so-called quishing (a portmanteau of “QR code” and “phishing”). QR codes are a machine-readable encoding mechanism that may encapsulate all kinds of knowledge, from strains of textual content to binary information, however most individuals know and acknowledge their most typical use as we speak as a fast method to share a URL.
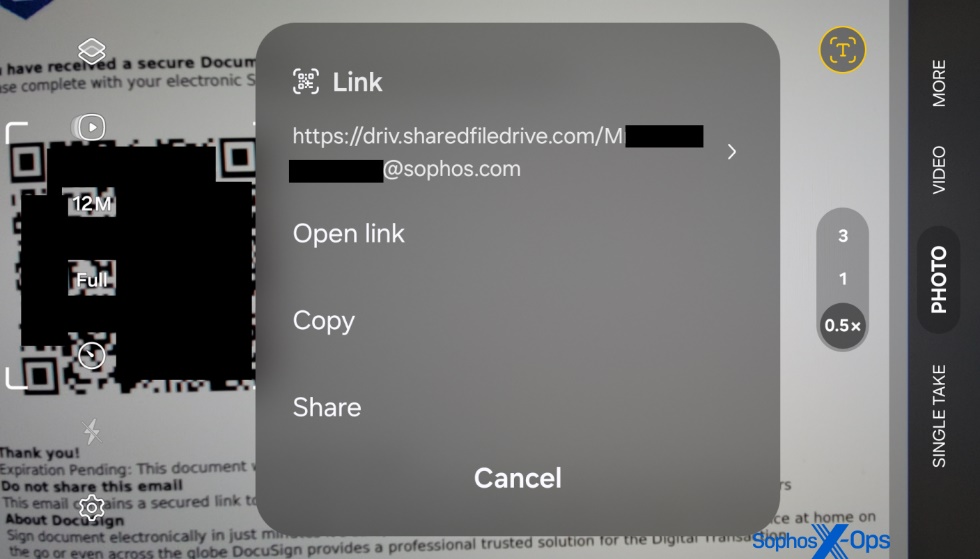
We within the safety business usually train folks resilience to phishing by instructing them to fastidiously have a look at a URL earlier than clicking it on their pc. Nevertheless, not like a URL in plain textual content, QR codes don’t lend themselves to scrutiny in the identical manner.
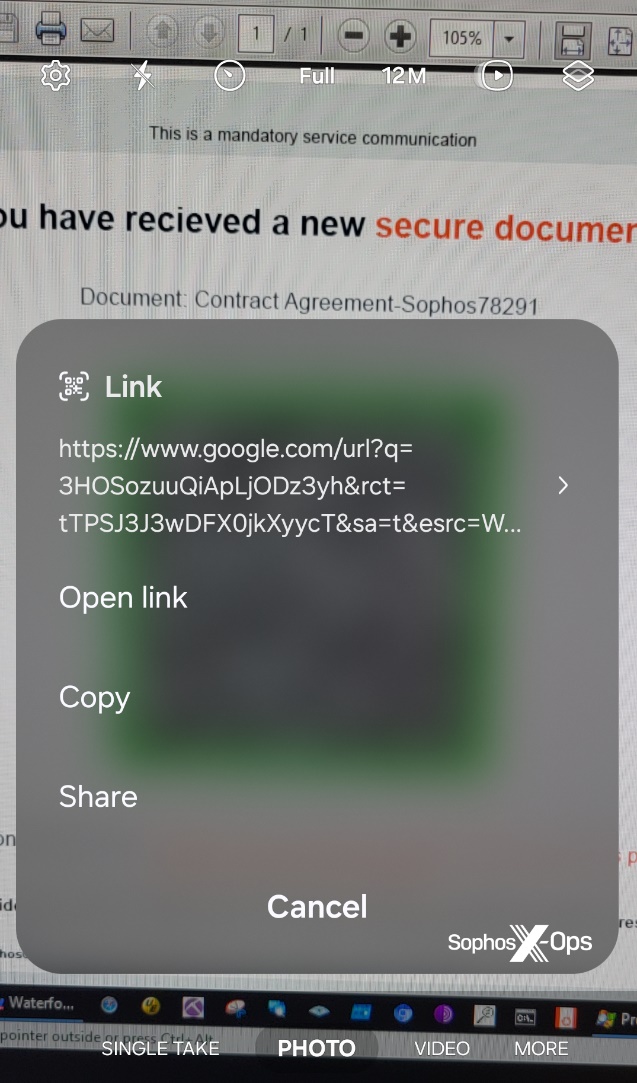
Additionally, most individuals use their cellphone’s digital camera to interpret the QR code, relatively than a pc, and it may be difficult to fastidiously scrutinize the URL that momentarily will get proven within the cellphone’s digital camera app – each as a result of the URL might seem just for just a few seconds earlier than the app hides the URL from sight, and in addition as a result of menace actors might use a wide range of URL redirection methods or providers that conceal or obfuscate the ultimate vacation spot of the hyperlink introduced within the digital camera app’s interface.
How the quishing assault works
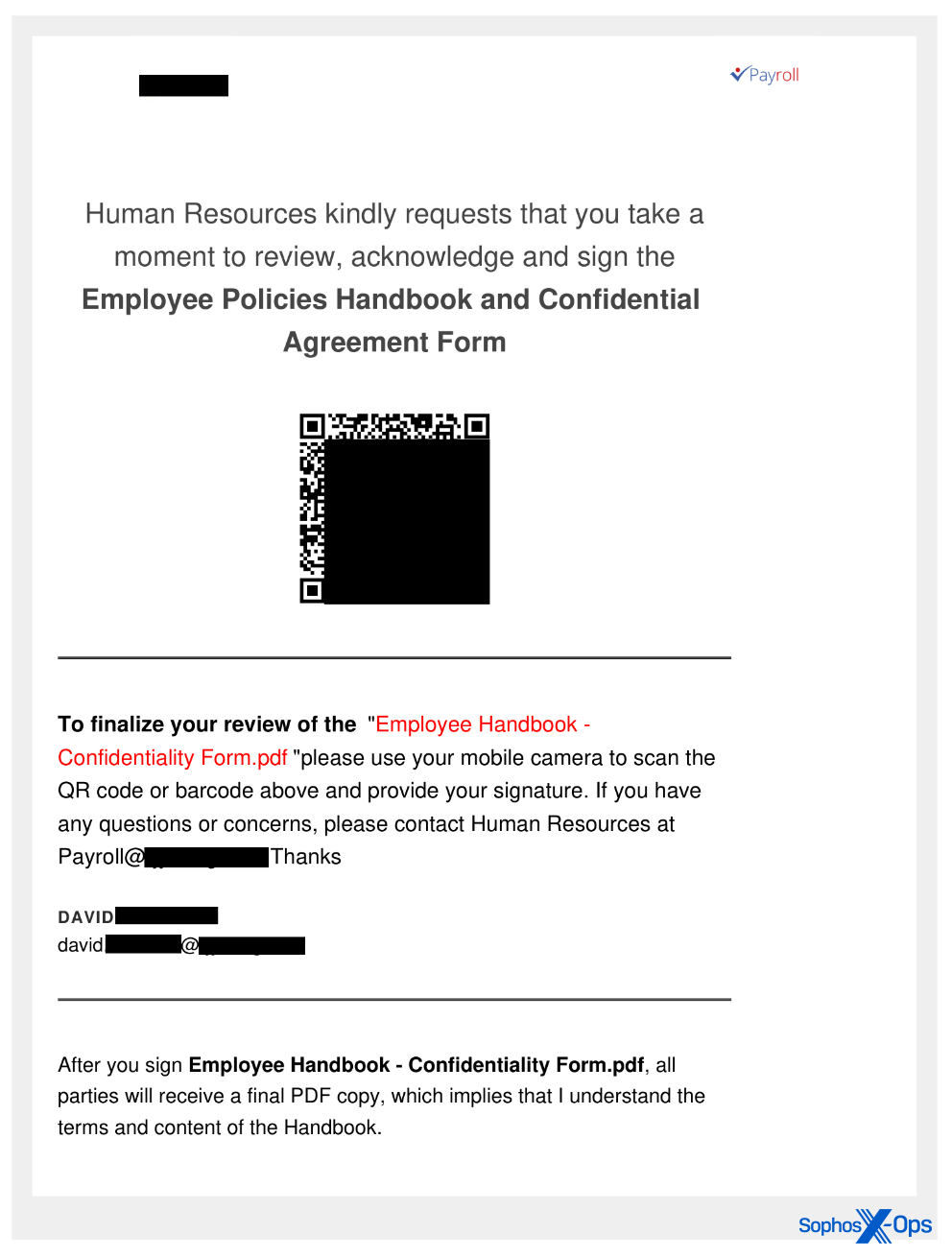
Risk actors despatched a number of targets inside Sophos a PDF doc containing a QR code as an electronic mail attachment in June 2024. The spearphishing emails had been crafted to seem as official emails, and had been despatched utilizing compromised, official, non-Sophos electronic mail accounts.
(To be clear, these weren’t the primary quishing emails we had seen; Workers had been focused with a batch in February, and once more in Might. Prospects have been focused by related campaigns going again not less than a 12 months. X-Ops determined to give attention to the Sophos-targeted assaults as a result of we have now full permission to research and share them.)
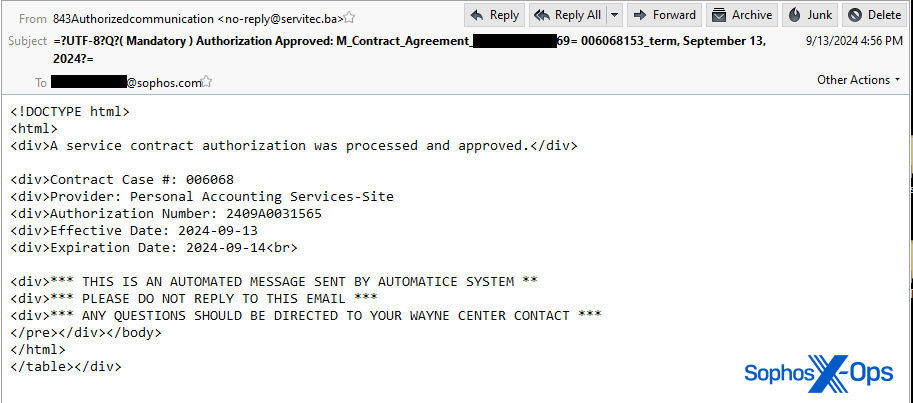
The messages’ topic strains made them seem to originate throughout the firm, as a doc that was emailed straight from a networked scanner in an workplace.
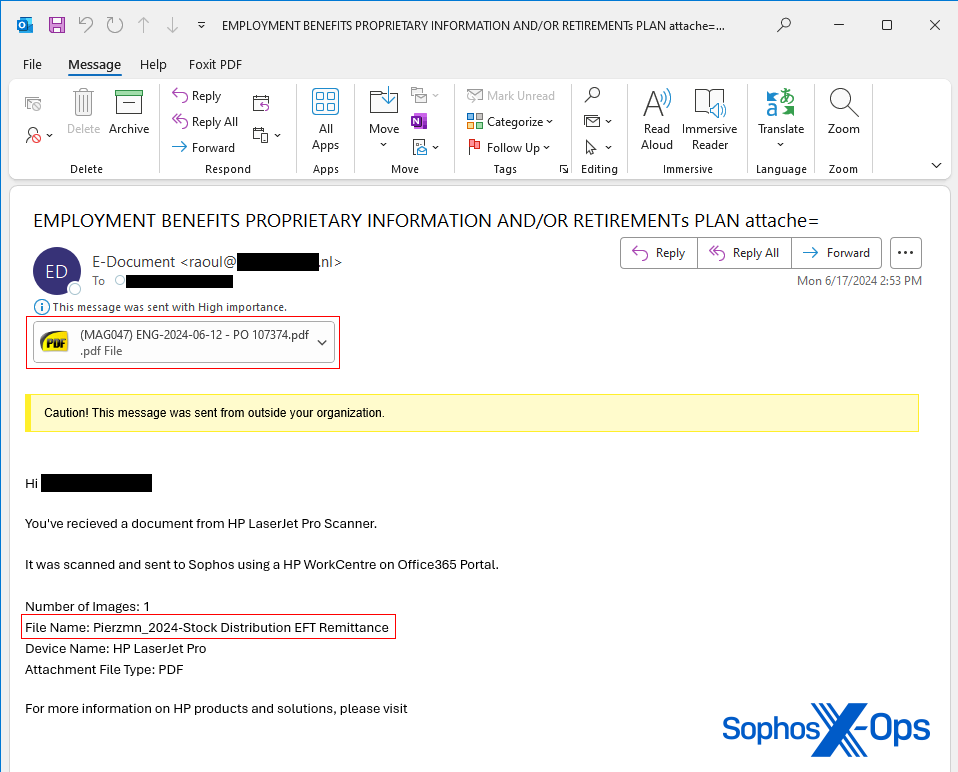
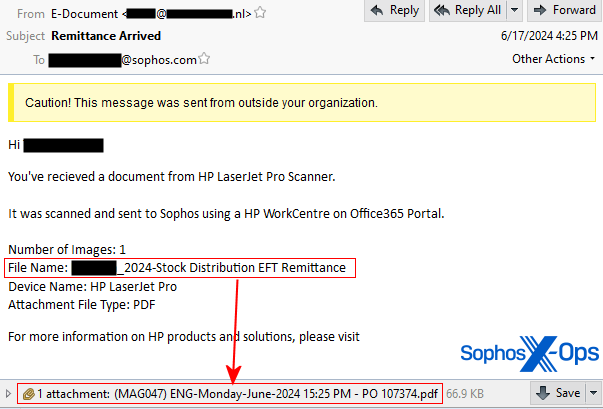
One notable crimson flag is that the e-mail message that presupposed to originate from a scanner had a filename for the doc within the physique of the message that, in the entire messages we acquired that day, didn’t match the filename of the doc hooked up to the e-mail.
As well as, one of many messages had a topic line of “Remittance Arrived,” which an automatic workplace scanner wouldn’t have used, since that’s a extra generalized interpretation of the content material of the scanned doc. The opposite message had a topic line of “Employment advantages proprietary data and/or retirements plan attache=” that seemed to be minimize off on the finish.
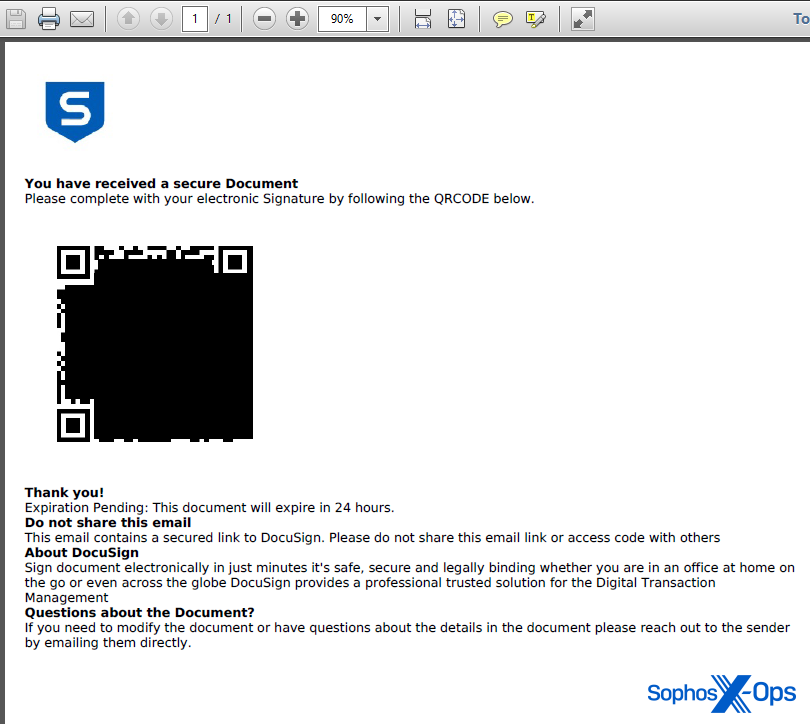
The PDF doc contained a Sophos brand, however was in any other case very plain. Textual content that seems under the QR code states “This doc will expire in 24 hours.” It additionally signifies the QR code factors to Docusign, the digital contract signature platform. These traits lend the message a false sense of urgency.
When targets scanned the QR code utilizing their telephones, the targets had been directed to a phishing web page that appears like a Microsoft365 login dialog field, however was managed by the attacker. The URL had a question string on the finish that contained the goal’s full electronic mail tackle, however curiously the e-mail tackle had an apparently random, totally different capital letter prepended to the tackle.
This web page was designed to steal each login credentials and MFA responses utilizing a method referred to as Adversary-in-The-Center (AiTM).

The URL used within the assault was not recognized to Sophos on the time the e-mail arrived. In any case, the goal’s cell phone had no function put in on it that may have been in a position to filter a go to to a known-malicious web site, not to mention this one, which had no repute historical past related to it on the time.
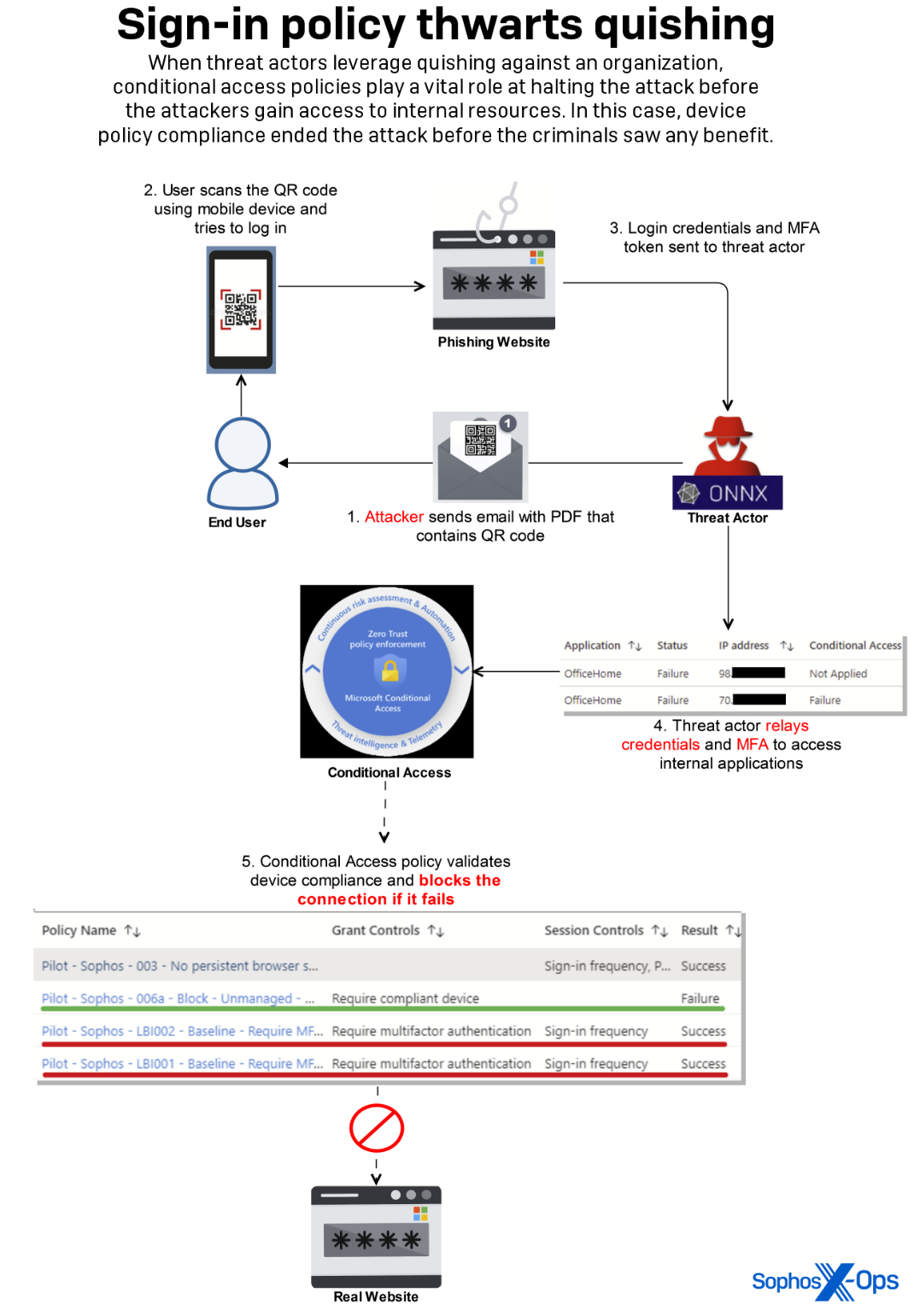
The assault efficiently compromised an worker’s credentials and MFA token by this methodology. The attacker then tried to make use of this data to realize entry to an inner utility by efficiently relaying the stolen MFA token in close to real-time, which is a novel method to circumvent the MFA requirement that we implement.
Inside controls over different facets of how the community login course of works prevented the attacker from gaining any entry to inner data or property.
As we’ve beforehand talked about, any such assault is changing into extra commonplace amongst our clients. Every single day we’re receiving extra samples of novel quishing PDFs concentrating on particular staff at organizations.
Quishing as a service
The targets acquired emails despatched by a menace actor that carefully resemble related messages despatched utilizing a phishing-as-a-service (PhaaS) platform known as ONNX Retailer, which some researchers assert is a rebranded model of the Caffeine phishing package. The ONNX Retailer supplies instruments and infrastructure for working phishing campaigns, and might be accessed through Telegram bots.
The ONNX Retailer leverages Cloudflare’s anti-bot CAPTCHA options and IP tackle proxies to make it more difficult for researchers to determine the malicious web sites, decreasing the effectiveness of automated scanning instruments and obfuscating the underlying internet hosting supplier.
The ONNX Retailer additionally employs encrypted JavaScript code that decrypts itself throughout the webpage load, providing an additional layer of obfuscation that counters anti-phishing scanners.
Quishing a rising menace
Risk actors who conduct phishing assaults that leverage QR codes might wish to bypass the sorts of community safety options in endpoint safety software program that may run on a pc. A possible sufferer would possibly obtain the phishing message on a pc, however usually tend to go to the phishing web page on their less-well-protected cellphone.
As a result of QR codes are normally scanned by a secondary cellular system, the URLs folks go to can bypass conventional defenses, reminiscent of URL blocking on a desktop or laptop computer pc that has endpoint safety software program put in, or connectivity by a firewall that blocks recognized malicious internet addresses.
We spent a substantial period of time researching our assortment of spam samples to search out different examples of quishing assaults. We discovered that the quantity of assaults concentrating on this particular menace vector look like growing each in quantity and within the sophistication of the PDF doc’s look.
The preliminary set of quishing attachments in June had been comparatively simplistic paperwork, with only a brand on the high, a QR code, and a small quantity of textual content meant to create an urgency to go to the URL encoded within the QR code block.
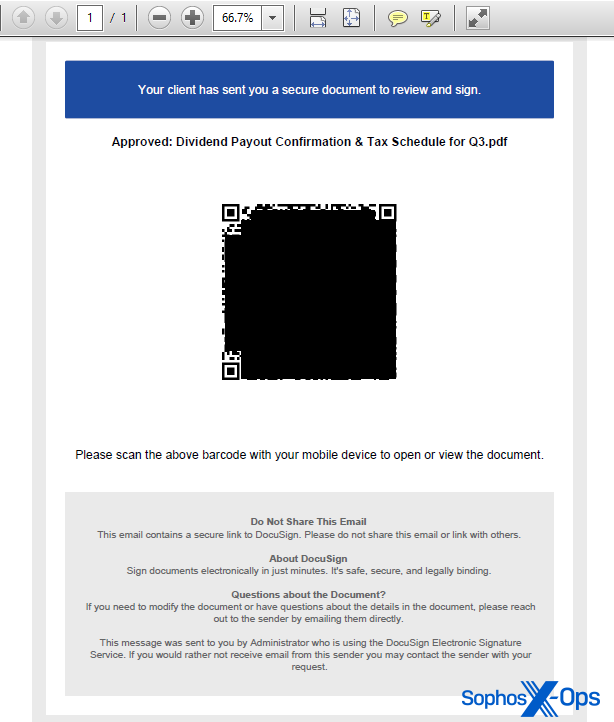
Nevertheless, all through the summer season, samples have change into extra refined, with a larger emphasis on the graphic design and look of the content material displayed throughout the PDF. Quishing paperwork now seem extra polished than these we initially noticed, with header and footer textual content custom-made to embed the title of the focused particular person (or not less than, by the username for his or her electronic mail account) and/or the focused group the place they work contained in the PDF.
QR codes are extremely versatile, and a part of the specification for them signifies that it’s attainable to embed graphics within the heart of the QR code block itself.
Among the QR codes in more moderen quishing paperwork abuse Docusign’s branding as a graphic component throughout the QR code block, fraudulently utilizing that firm’s notability to social engineer the consumer.
To be clear, Docusign doesn’t electronic mail QR code hyperlinks to clients or shoppers who’re signing a doc. In keeping with DocuSign’s Combating Phishing white paper (PDF), the corporate’s branding is abused steadily sufficient that the corporate has instituted safety measures in its notification emails.
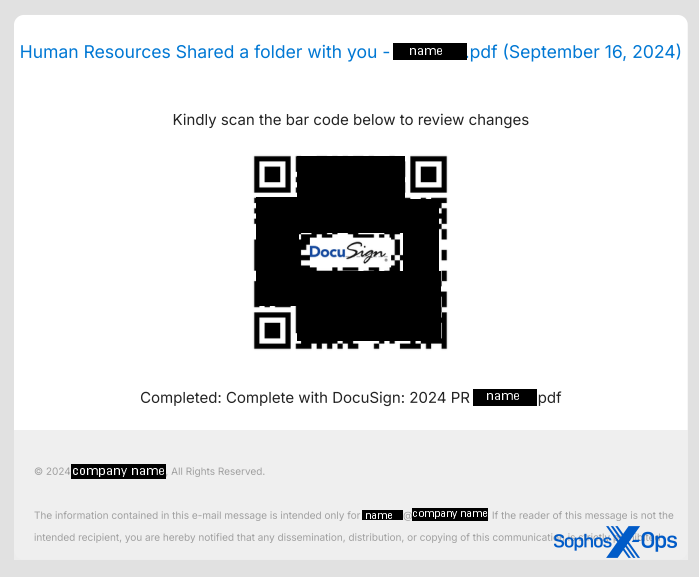
To be clear, the presence of this brand within the QR code can’t convey any legitimacy to the hyperlink it factors to, and shouldn’t lend it any credibility. It’s merely a design function of the QR code specification, that graphics can seem within the heart of them.
The formatting of the hyperlink the QR code factors to has additionally developed. Whereas lots of the URLs seem to level to standard domains which can be getting used for malicious functions, attackers are additionally leveraging all kinds of redirection methods that obfuscate the vacation spot URL.
For example, one quishing electronic mail despatched to a unique Sophos worker previously month linked to a cleverly formatted Google hyperlink that, when clicked, redirects the customer to the phishing website. Performing a lookup of the URL on this case would have resulted within the website linked straight from the QR code (google.com) being labeled as protected. We’ve additionally seen hyperlinks level to shortlink providers utilized by a wide range of different official web sites.
Any answer that purports to intercept and halt the loading of quishing web sites should tackle the conundrum of following a redirection chain to its eventual vacation spot, then performing a repute examine of that website, together with addressing the added complication of phishers and quishers hiding their websites behind providers like CloudFlare.
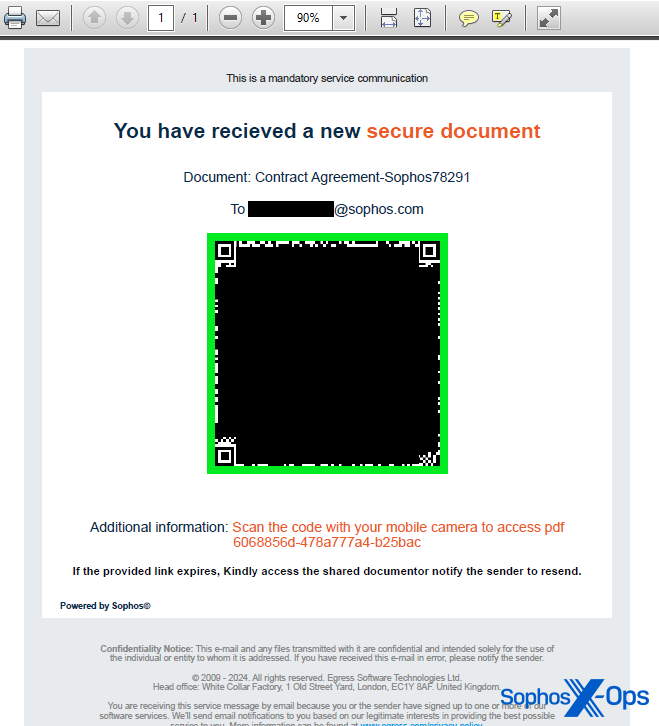
The more moderen quishing electronic mail despatched to a Sophos worker had a PDF attachment with an ironic twist – it seemed to be despatched by an organization whose major enterprise is anti-phishing coaching and providers.
The PDF hooked up to the more moderen Sophos-targeted quishing electronic mail had footer data that seems to imitate authorized notices from an organization known as Egress, a subsidiary of the anti-phishing coaching agency KnowBe4. Nevertheless, the area the QR code pointed to belongs to a Brazilian consulting agency that has no connection to KnowBe4. It seems that the consultants’ web site had been compromised and used for internet hosting a phishing web page.
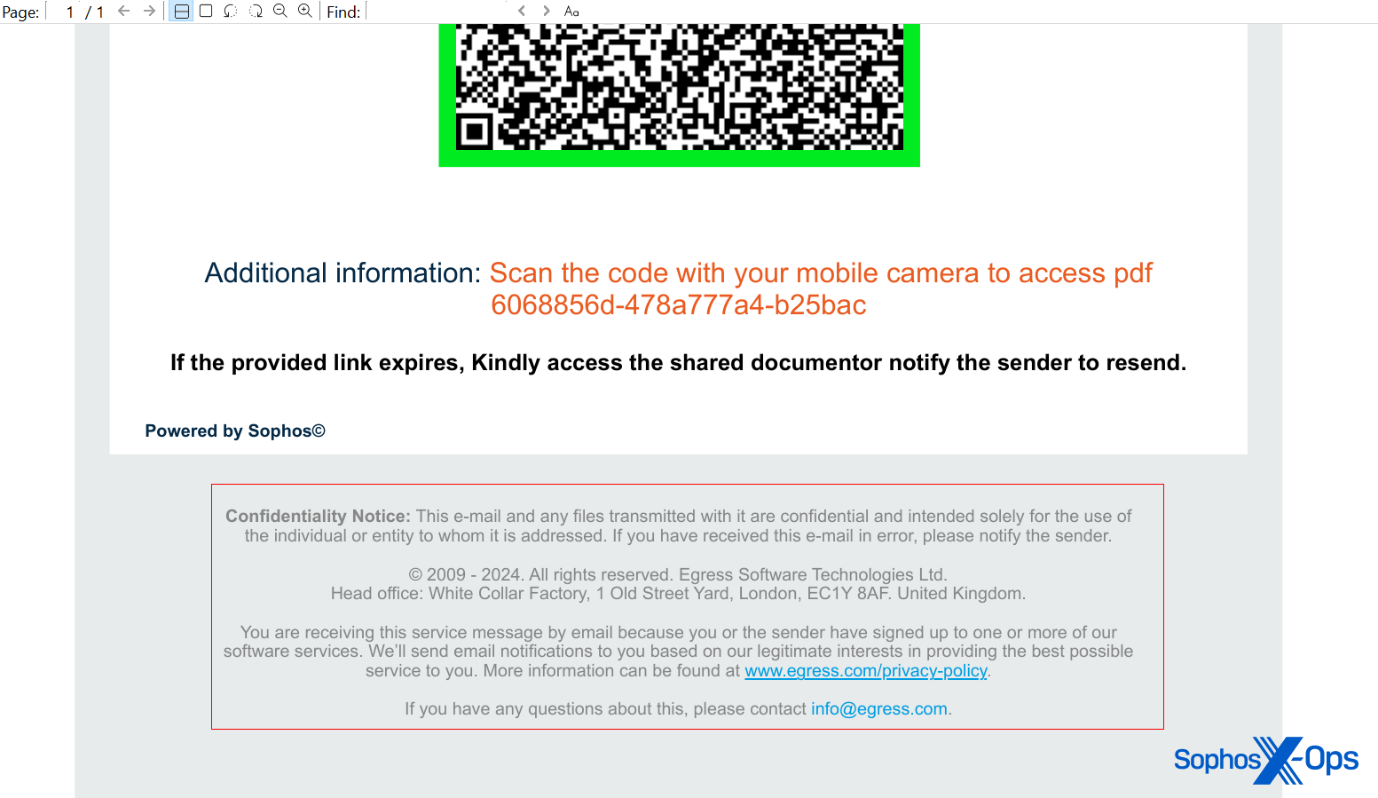
That message additionally contained physique textual content that made it seem it was an automatic message, although it had some very curious misspellings and errors. As with the earlier messages, the physique textual content indicated a filename for the attachment that didn’t match what was hooked up to the e-mail.
MITRE ATT&CK Ways Noticed
Advice and steerage for IT admins
If you’re coping with the same QR-code-enabled phishing assault in an enterprise setting, we have now some strategies about easy methods to take care of all these assaults.
- Material centered on HR, payroll, or advantages: A lot of the quishing emails concentrating on Sophos use worker paperwork as a social engineering ruse. Messages had topic strains that contained phrases like “2024 monetary plans,” “advantages open enrollment,” “dividend payout,” “tax notification,” or “contract settlement.” Nevertheless, not one of the messages got here from a Sophos electronic mail tackle. Pay specific consideration to messages with related material, and be sure that all official messages pertaining to those topics come from an electronic mail tackle inner to your group, relatively than counting on third occasion messaging instruments.
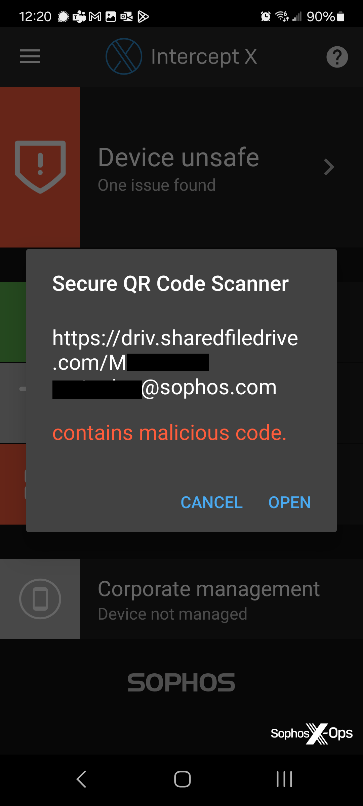
- Cellular Intercept X: Intercept X for Cellular (Android/iOS) features a Safe QR Code Scanner, out there by the hamburger menu within the higher left nook of the app. The Safe QR Code Scanner protects customers by checking QR code hyperlinks in opposition to a database of recognized threats and warns you if Sophos’ URL repute service is aware of a web site is malicious. Nevertheless, it has the limitation that it doesn’t comply with hyperlinks by a redirection chain.
- Monitor dangerous sign-in alerts: Leverage Microsoft’s Entra ID Safety, or related enterprise-level identification administration tooling, to detect and reply to identity-based dangers. These options assist determine uncommon sign-in exercise which will point out phishing or different malicious actions.
- Implementing Conditional Entry: Conditional Entry in Microsoft Entra ID permits organizations to implement particular entry controls primarily based on situations reminiscent of consumer location, system standing, and danger stage, enhancing safety by guaranteeing solely approved customers can entry assets. Wherever attainable, related defense-in-depth procedures needs to be thought-about as a backstop for probably compromised MFA tokens.
- Allow efficient entry logging: Whereas we advocate enabling all of the logging described right here by Microsoft, we particularly recommend enabling audit, sign-ins, identification protections, and graph exercise logs, all of which performed an important position throughout this incident.
- Implement superior electronic mail filtering: Sophos has already launched part 1 of Central E mail QR phish safety, which detects QR codes which can be straight embedded into emails. Nevertheless, on this incident, the QR code was embedded in a PDF attachment of an electronic mail, making it troublesome to detect. Part 2 of Central E mail QR code safety will embrace attachment scanning for QR codes and is deliberate for launch throughout the first quarter of 2025.
- On-demand clawback: Sophos Central E mail clients who use Microsoft365 as their mail supplier can use a function known as on-demand clawback to search out (and take away) spam or phishing messages from different inboxes inside their group which can be much like messages already recognized as malicious.
- Worker vigilance and reporting: Enhancing worker vigilance and immediate reporting are essential for tackling phishing incidents. We advocate implementing common coaching classes to acknowledge phishing makes an attempt, and inspiring staff to report any suspicious emails instantly to their incident response workforce.
- Revoking questionable energetic consumer classes: Have a transparent playbook on how and when to revoke consumer classes which will present indicators of compromise. For O365 apps, this steerage from Microsoft is useful.
Be good to your people
Even beneath one of the best situations, and with a well-trained workforce like the staff right here at Sophos, numerous types of phishing stay a persistent and ever-more-dangerous menace. Happily, with the fitting stage of layered safety, it’s now attainable to mitigate even one thing as probably critical as a profitable phishing assault.
However simply as essential because the technical prevention ideas above are the human components of an assault. Cultivating a tradition and work surroundings the place workers are empowered, inspired, and thanked for reporting suspicious exercise, and the place infosec workers can quickly examine, could make the distinction between a mere phishing try and a profitable breach.
Going deeper
Sophos X-Ops shares indicators of compromise for these and different analysis publications on the SophosLabs Github.
