One of many high challenges dealing with enterprise homeowners is making certain safe distant connections to firm networks and assets to remain protected from information breaches. In a current IBM report, the common price of an information breach in 2024 was estimated at $4.88 million — which IBM says is the best complete ever recorded. With this, it isn’t a shock that deploying enterprise-level digital non-public community options has change into a high precedence for a lot of companies.
Enterprise VPN options present a safe gateway for companies to attach their staff to their company networks. Safety features akin to multi-factor authentication, disabling break up tunneling, implementing a most connection-time window after which staff should re-authenticate, and mandating complicated, rotating passwords are a number of examples of how enterprise VPNs enhance and bolster safety.
Given the wide selection of VPNs in the marketplace, here’s a roundup of the highest enterprise VPN options.
Prime enterprise VPN options comparability
The desk beneath highlights a number of the key options of enterprise VPN options and the way they evaluate with each other.
Cisco AnyConnect: Finest total

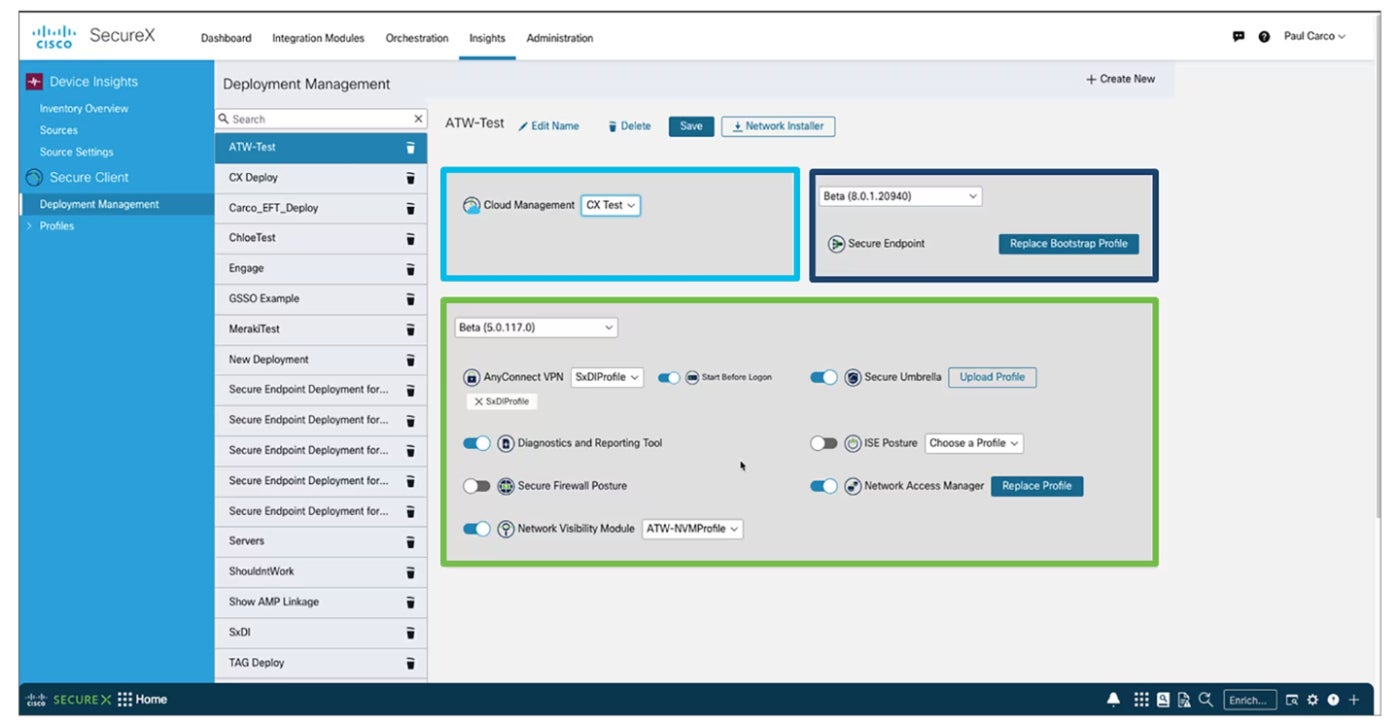
Cisco AnyConnect is my greatest total choose for its wide selection of safety capabilities, high quality buyer help, and user-friendly expertise. It makes use of multi-factor authentication and establishes a 24-hour utilization window, after which a person’s connection drops and they’re required to log in once more.
SEE: Can a VPN Be Hacked? (TechRepublic)
A spotlight for me is the way it performs a system examine on authentication to find out whether or not a workstation meets sure necessities, like anti-malware software program or company area membership, earlier than it permits entry to the corporate community. This ensures solely company-managed methods are allowed on the VPN. I additionally like how AnyConnect can block entry to untrusted servers, show safety merchandise put in, and run diagnostics to collect info for evaluation and troubleshooting. It disables break up tunneling, that means when a person is related to the VPN, they will solely entry company assets and nothing on an area dwelling community or the web.
Why I selected Cisco AnyConnect
I picked Cisco AnyConnect for its user-friendly set up course of and intuitive interface. I additionally discover nice worth in its suite of security measures, akin to system examine and server blocking, that make it a robust possibility amongst different enterprise VPN options with extra restricted capabilities. Per my analysis, it additionally will get glowing opinions from customers when it comes to its stability and total reliability.
Pricing
- Contact the seller for pricing particulars.
Options
- Permits entry to the enterprise community, from any gadget, at any time, in any location.
- Supplies visibility and perception into endpoint conduct.
- Affords multi-factor authentication.
- Affords always-on help.
Execs and cons
| Execs | Cons |
|---|---|
| It’s straightforward to obtain and set up. | There is no such thing as a free trial. |
| It may be used on a number of gadgets. | Lacks kill change functionality. |
| Supplies nice buyer help. |
Checkpoint Safe Distant Entry: Finest for web-based shopper help

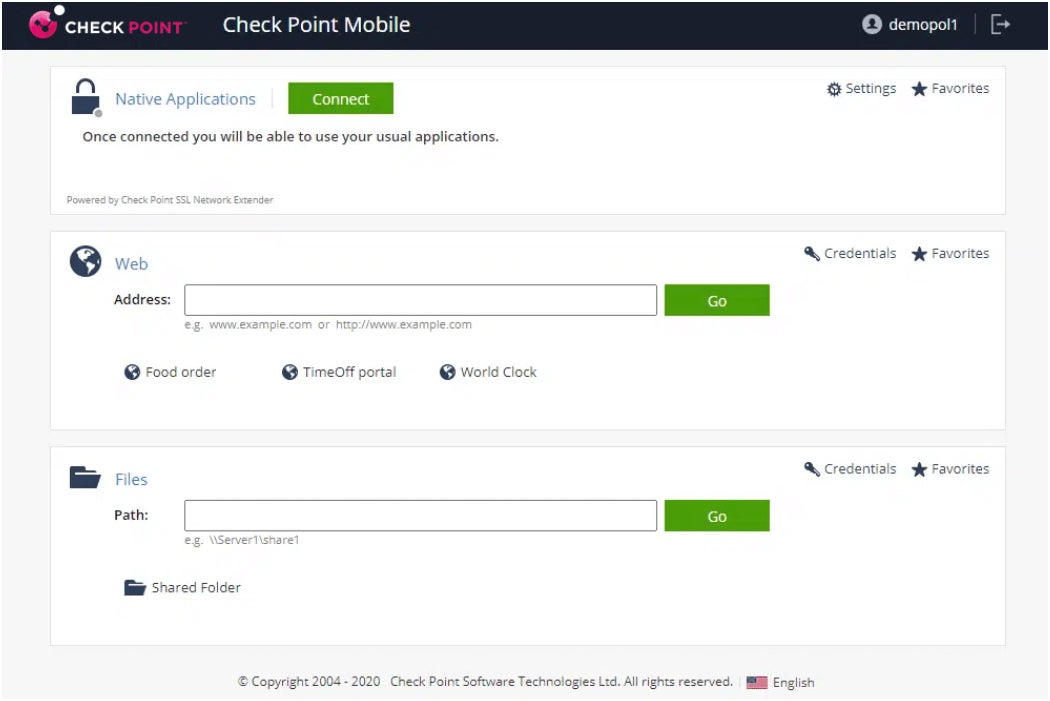
For high quality internet shopper help, I like to recommend Checkpoint Safe Distant Entry VPN. It may create {custom} set up packages pre-configured with the goal IP tackle(es) for purchasers to authenticate to. Like AnyConnect, it’s secured by multi-factor authentication (on this case, both arduous tokens or smooth tokens, which function as an app on cell gadgets).
SEE: How A lot Does a VPN Value? + Financial savings Ideas (TechRepublic)
I personally like how break up tunneling is disabled in Checkpoint Safe Distant Entry, identical to Cisco AnyConnect. This implies, for hackers to get to the purchasers, they must configure the corporate proxy server settings, which solely allow entry to public-facing web websites for enterprise use (social media websites have been blocked, as an example). Group memberships decide who can join the place. Checkpoint firewalls function the administration interface for each the VPN and the firewall settings.
I additionally wish to point out that Checkpoint Website-to-Website VPNs are capable of hyperlink two distant areas collectively — permitting visitors to achieve networks on both aspect.
Why I selected Checkpoint Safe Distant Entry
I’ve Checkpoint Safe Distant Entry VPN on this listing for its spectacular SSL VPN portal that enables community entry by an internet browser. Having safe entry to a company community is a significant value-add that many staff and employers will discover helpful, particularly these working in a hybrid setup. I additionally really feel it makes workflows extra environment friendly, since staff can entry vital assets with out having to put in a full-fledged VPN shopper on their gadgets.
Pricing
- Contact the seller for pricing particulars.
Options
- The VPN gives a central administration platform.
- IPsec and SSL VPN help.
- Safe hotspot registration.
- It gives VPN auto-connect.
- Multi-factor authentication help.
Execs and cons
| Execs | Cons |
|---|---|
| SSL help offers web-based entry with out the necessity to set up a VPN shopper. | It doesn’t help menace prevention on iOS, Android, and Linux customers. |
| Compliance scanning help. | Incident evaluation is barely obtainable for Home windows customers. |
| Runs on a number of gadgets, together with Home windows, Mac, and mobiles. | |
| Affords menace prevention functionality. |
NordLayer: Finest for brand new enterprise VPN customers

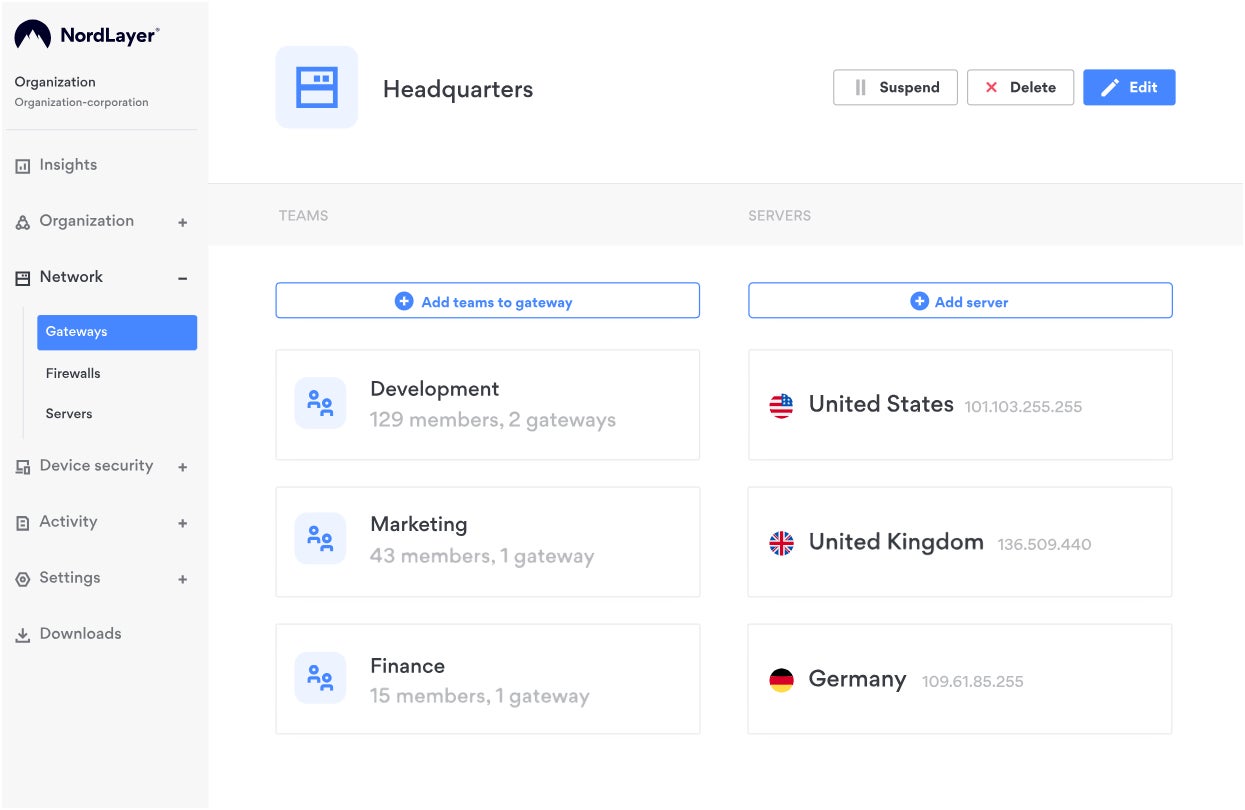
For companies transitioning to an enterprise VPN resolution, I like to recommend NordLayer. It’s a robust distant entry resolution that allows companies to safe their distant staff and defend firm assets on the similar time. If it sounds acquainted, it’s as a result of it’s from the identical firm that created the favored client VPN — NordVPN.
Like NordVPN, I like how NordLayer gives an intensive suite of security measures with out sacrificing ease of use. A few of its options embrace good distant entry, All the time On VPN, Customized DNS, and DNS filtering by class. One massive benefit I discovered with NordLayer is its transparency with pricing, offering estimated costs relying in your wants or subscription of selection. To me, that is an underrated characteristic that’s excellent for potential enterprise VPN customers.
Why I selected NordLayer
I selected NordLayer for its robust emphasis on ease of deployment, set up, and scalability — which is good for companies that wish to begin utilizing an enterprise VPN. This permits NordLayer to accommodate most, if not all, enterprise sizes with out a lot headache. I additionally like that it gives its personal proprietary NordLynx protocol, based mostly on WireGuard, that’s constructed for each pace and safety.
Pricing
NordLayer has a month-to-month and a yearly possibility for its 4 subscription tiers. Beneath is a fast rundown of its annual pricing.
- Lite: $8 per person, per thirty days; 5 customers minimal; important web entry safety with fundamental web menace prevention.
- Core: $11 per person, per thirty days; 5 customers minimal; superior entry safety, and fundamental community entry management.
- Premium: $14 per person, per thirty days; 5 customers minimal; community entry management options with granular community segmentation.
- Enterprise: $7 per person, per thirty days; 50 customers minimal; custom-fit community safety.
Options
- System posture safety.
- MFA and SSO.
- All the time On VPN.
- Exercise monitoring studies.
Execs and cons
| Execs | Cons |
|---|---|
| Subscription tiers that cater to varied enterprise sizes. | Pretty new to enterprise VPN area. |
| Extremely scalable. | |
| Publicly obtainable pricing. |
SonicWall International VPN Consumer: Finest light-weight enterprise VPN

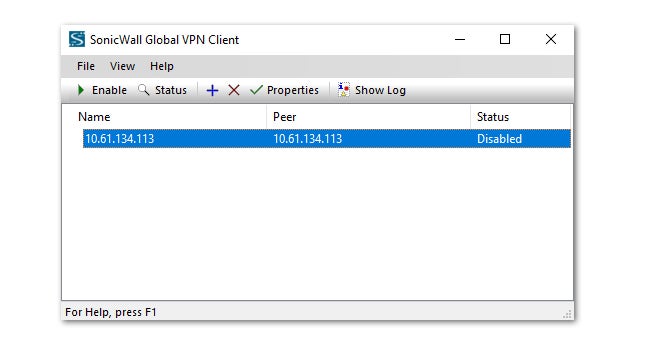
For companies in search of a light-weight possibility, I counsel SonicWall International VPN. It gives a quick and environment friendly product that gives RADIUS/certificates/Sensible Card/USB authentication. It comes with each 168-bit key 3DES (Information Encryption Commonplace) and AES (Superior Encryption) encryption requirements and VPN session reliability that redirects purchasers to different VPN gateways if issues happen. I notably respect how SonicWall comes with particular subnet entry and command-line choices for set up, making it straightforward to deploy by automated software program mechanisms.
Why I selected SonicWall International VPN Consumer:
I chosen SonicWall International VPN to be on this listing for its pace and reliability. It has mixture of robust security measures, akin to AES encryption, an simply configurable interface, and a fast and dependable person expertise. SonicWall additionally has fame for offering high quality buyer help.
Pricing
- Contact the seller for pricing particulars.
Options
- It may be configured both as an IPsec or SSL end-point agent.
- Helps a number of platforms, together with Home windows, macOS, and Linux.
- Affords straightforward setup and configuration.
- Detailed logs and reporting for community directors.
Execs and cons
| Execs | Cons |
|---|---|
| Affords robust encryption and authentication to guard towards cyber threats. | There is no such thing as a free trial or demo. |
| It’s straightforward to obtain and configure. | No web-based model. |
| Appropriate with a variety of platforms and gadgets. | |
| Affords logs and reporting options to watch VPN utilization. |
Fortinet FortiClient: Finest for providing wider VPN safety choices

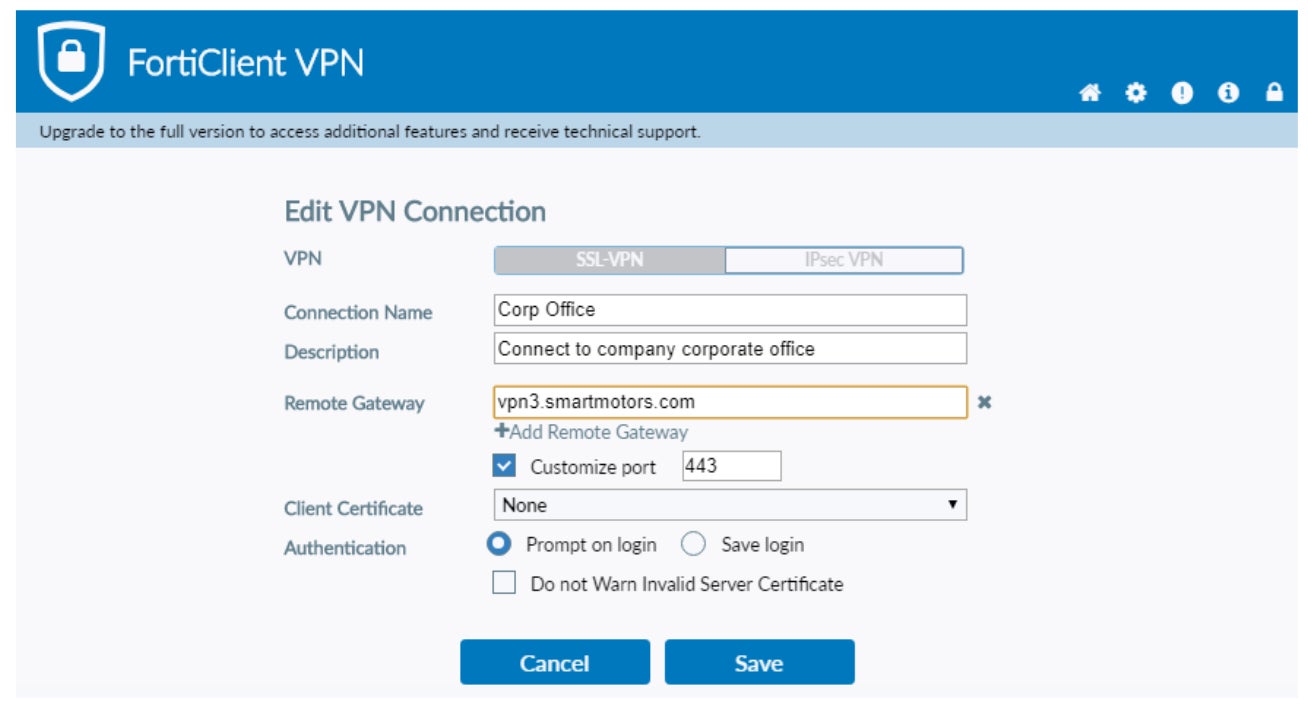
For companies seeking to have flexibility when it comes to VPN safety choices, I like to recommend Fortinet FortiClient. It depends on certificates for integration and deployment and gives entry to internet filtering and a firewall. I additionally like how its Endpoint safety safety capabilities, which makes use of automated conduct evaluation, is included. Fortinet makes use of a “single pane of glass” method that gives one-stop-shopping to handle configuration, deployment, and administration, in addition to examine shopper standing and have interaction in vulnerability scanning and patching.
I respect how Fortinet gives two various kinds of VPN options — IPSec and SSL — and may be built-in into a company’s total endpoint safety technique. This offers a dependable VPN safety possibility for corporations which have staff working remotely.
Why I selected Fortinet FortiClient
I selected Fortinet FortiClient for its intensive protocol suite, making it a good selection when safety is a high precedence. It additionally stood out for me resulting from its huge number of tunneling protocols which are customizable based mostly on safety wants. I additionally like that Fortinet permits potential customers to trial FortiClient to see if it suits their enterprise wants.
Pricing
- Contact the seller for pricing particulars.
Options
- Fortinet helps multi-factor authentication.
- Helps SSL or IPSec tunneling protocols.
- Affords malware safety and anti-exploit help.
- Affords a number of tunneling protocols, together with Level-to-Level, Layer 2, and Safe Socket tunneling protocols.
Execs and cons
| Execs | Cons |
|---|---|
| There’s a free trial possibility. | Integration with anti-virus and threat-detection instruments makes it slightly bit clunky. |
| Totally customizable authentication settings. |
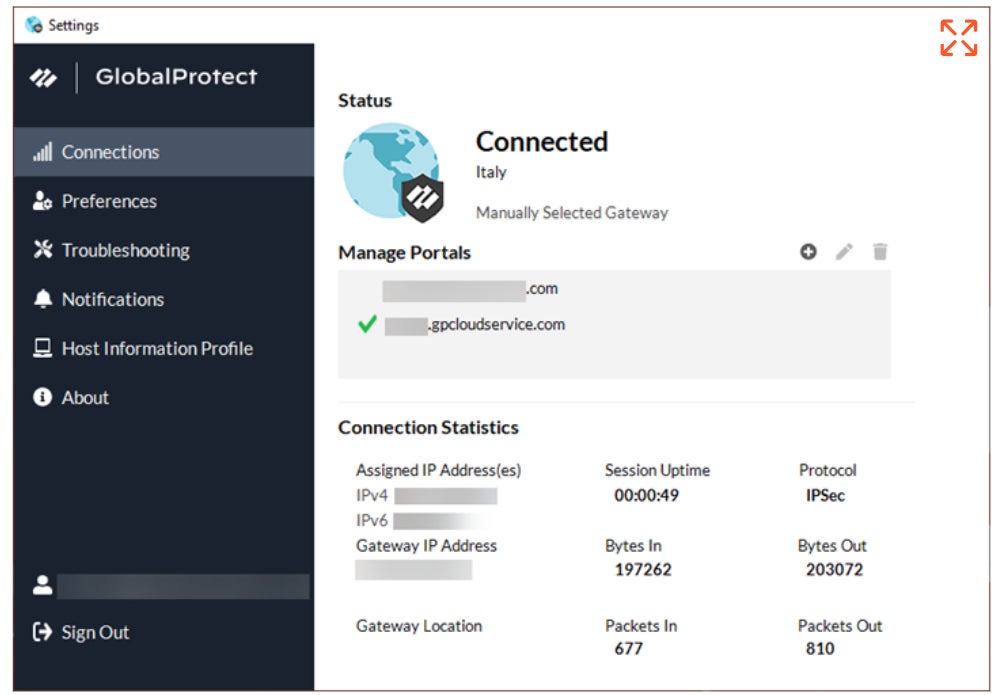
Palo Alto GlobalProtect: Finest for implementing safety insurance policies

For enterprises that need a VPN with dependable safety coverage capabilities, I counsel wanting into Palo Alto GlobalProtect. It gives related options to prior merchandise listed, akin to multi-factor authentication, excessive safety (cookie or certificate-based authentication are two robust options), internet filtering and menace safety. As well as, GlobalProtect depends on Zero Belief ideas.
Personally, I commend GlobalProtect’s spectacular capacity to establish what gadgets are connecting to the VPN and whether or not they’re managed (company-owned or operated) or unmanaged (employee-owned), and offering entry accordingly (gadgets deemed suspicious or unauthorized may be blocked fully). It may additionally decide certificates current on gadgets, working system and patch ranges, anti-malware variations and standing, working software program, and whether or not disks are encrypted and information is being backed up by a product.
Why I selected Palo Alto GlobalProtect
I opted for Palo Alto GlobalProtect resulting from its trustworthiness and reliability in upholding its safety insurance policies and have guarantees to its purchasers. Belief and credibility are vital tenets in high quality safety software program, and GlobalProtect has continued to keep up fame for safeguarding company and person information. I additionally discover its robust utility of zero belief safety ideas as a significant benefit towards related opponents.
Pricing
- Contact the seller for pricing particulars.
Options
- Supplies least-privilege entry help for distant staff.
- Helps multi-factor authentication.
- The software program helps menace prevention.
- Affords full visibility throughout all functions, ports, and protocols.
Execs and cons
| Execs | Cons |
|---|---|
| There’s a demo possibility to take a look at the product. | Deployment could also be tough for first-time customers. |
| Affords analytics and visibility for community visitors, | |
| There’s an always-on, safe connection help. |
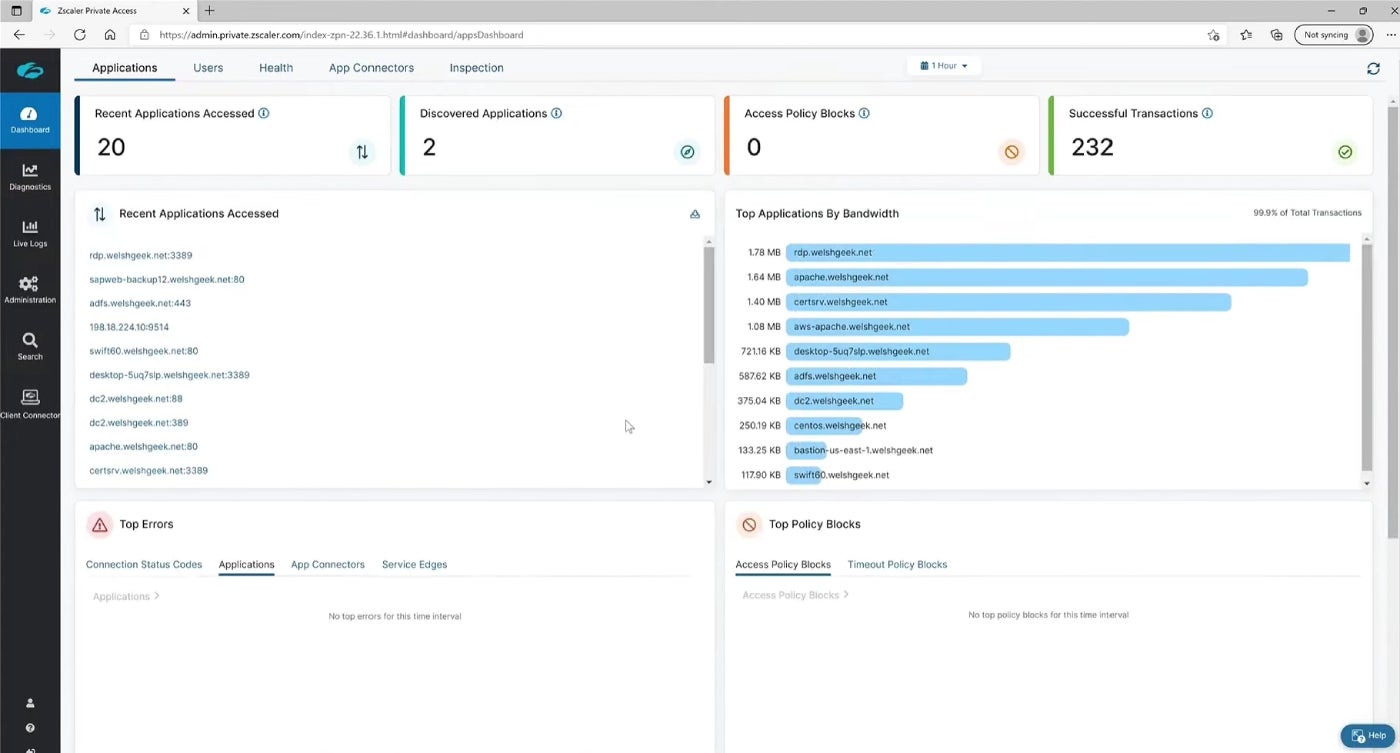
ZScaler Non-public Entry: Finest for zero belief community entry

Should you’re in search of a ZTNA resolution, I like to recommend ZScaler Non-public Entry. As a disclaimer, Zscaler is a special product from the earlier choices on this article. Somewhat than being a conventional end-user VPN shopper, it’s a cloud service that gives entry to functions in cloud environments or on-premises methods by way of a distributed structure. The twist right here is that the functions connect with approved customers by way of safe encryption fairly than vice versa, so customers by no means truly entry the distant networks concerned.
It makes use of normal policy-based entry, relying on customers and functions. For me, I like how ZScaler permits mergers and acquisitions to be facilitated simply as a result of diminished infrastructure setup instances and lack of want for extra networking tools.
Why I selected ZScaler Non-public Entry
I’ve ZScaler Non-public Entry on this listing for its zero belief method that may present organizations peace-of-mind in an more and more hybrid workforce. Whereas it isn’t a VPN per se, I really feel its cloud service adopts most safety in defending company information and provides an extra layer of safety towards potential information breaches.
Pricing
- Contact the seller for pricing particulars.
Options
- A number of gadget help.
- Supplies multi-factor authentication.
- AI-powered community segmentation.
- Helps various kinds of segmentations, together with user-to-app, user-to-device, and workload-to-workload segmentation.
Execs and cons
| Execs | Cons |
|---|---|
| There’s an possibility for a demo. | It’s only cloud-based. |
| Applies the ideas of least privilege to offer customers a safe connection. | |
| There’s safety compliance help. |
Key options of enterprise VPN options
Enterprise VPNs have key options that separate them from the normal client VPNs. Beneath are a number of the differentiating components.
Help for Safe VPN Protocol
Help for safe VPN protocols is a vital characteristic of enterprise VPNs. These protocols are designed to make sure the confidentiality, integrity, and authenticity of knowledge transmitted between distant customers and the company community. Enterprise VPNs usually help a number of safe protocols, akin to OpenVPN, IPSec, and SSL/TLS, to offer quite a lot of choices for connecting to the community securely. Using safe VPN protocols assist defend delicate info from interception, eavesdropping, and different kinds of cyber threats.
SEE: The way to Run a Cybersecurity Danger Evaluation in 5 Steps (TechRepublic Premium)
DNS Leak Safety help
DNS leaks can compromise the safety of enterprise networks by exposing staff’ on-line actions and doubtlessly permitting unauthorized entry to delicate firm information. Enterprise VPN options want strong, built-in DNS leak safety mechanisms to make sure that all DNS queries are routed by the encrypted VPN tunnel and never leaked outdoors.
Centralized administration help
A centralized administration system permits directors to shortly and simply configure VPN settings and insurance policies, monitor VPN visitors and utilization, and troubleshoot community points. With a centralized administration community, admins may implement insurance policies — akin to entry controls and information retention insurance policies, throughout the whole VPN community — making certain that each one customers adjust to firm safety insurance policies and trade rules.
Excessive availability
Excessive availability is one other essential characteristic of enterprise VPNs. Having an enterprise VPN constantly and constantly function correctly is a vital characteristic to be careful for. Any downtime in an enterprise VPN’s efficiency can disrupt enterprise operations, stopping distant staff from accessing company assets and doubtlessly inflicting income losses.
How do I select one of the best VPN resolution for my enterprise?
Earlier than choosing any VPN software program for your corporation, I like to recommend you are taking time to think about the next:
Think about your corporation safety wants
First, contemplate your safety wants and examine in case your potential VPN resolution can meet these wants. As an example, in case your safety want goes past only a safe VPN connection to incorporate, let’s say, compliance help, you need to go for a VPN resolution that provides each. Equally, you also needs to contemplate the way you wish to deploy your VPN software program. Would you like an answer providing solely a cloud-based or downloaded shopper? Your reply will can help you choose one of the best VPN software program for your corporation.
Think about safety capabilities
Whereas all VPN options supply related safety capabilities, some have extra security-focused options than others. Do not forget that safety ought to be the highest precedence when selecting an enterprise VPN resolution. It is best to go for options that present robust encryption, safe authentication, and different security measures to guard towards cyber threats.
Test for compatibility
Compatibility is one other issue to think about earlier than choosing any enterprise VPN resolution. The VPN resolution ought to be suitable with a variety of platforms and gadgets, together with desktops, laptops, cell gadgets, and completely different working methods. This ensures that your staff’ gadgets can simply connect with the VPN with out spending cash on further gadgets.
Think about price
Think about the price of the VPN resolution, together with any {hardware} or software program licenses, upkeep and help charges, and every other bills related to implementation and administration.
Methodology
Whereas there are a number of VPN providers on the market, not all supply options at an enterprise stage. To reach at this listing of one of the best enterprise VPNs, I based mostly our choice on the next parameters: robust security measures, steady connection, multi-device and working system functionality, and buyer help. Other than utilizing a number of the options, I additionally checked out opinions on Gartner to collect third-party opinions and person testimonials on a number of the VPN options.
From these facets, I highlighted the primary differentiating characteristic that makes every particular enterprise VPN value testing.
This text was initially written by Scott Matteson and up to date by Franklin Okeke. The present model comprises further info and updates by Luis Millares.
