Software program Highlight: CrowdStrikeCrowdStrike Falcon® Subsequent-Gen SIEM is a cloud-native platform that mixes first- and third-party safety and IT knowledge, menace intelligence, AI, and automation to assist organizations detect, examine, and reply to threats with unprecedented pace and effectivity.
|
Safety info and occasion administration (SIEM) is a tool and environmental evaluation technique supposed to assist safe and shield firm operations, knowledge, and personnel. By offering a complete evaluation of security-related particulars and associated suggestions, SIEM instruments help in making certain compliance and remediating potential or lively threats.
A latest report revealed by the IMARC Group discovered that the worldwide SIEM market reached virtually $5.8 billion in 2023. The identical report says the market is anticipated to climb to round $14 billion, particularly with extra firms investing extra assets in defending towards potential threats and resolving vulnerabilities.
With that in thoughts, we check out the most effective SIEM instruments and SIEM software program options accessible as we speak.
Prime SIEM software program comparability
These wishing to undertake SIEM or planning to improve a legacy SIEM instrument to a contemporary platform ought to fastidiously consider the accessible instruments. Options resembling cloud and on-prem performance, remediation capabilities, and the platforms supported ought to be among the many high areas to be thought of.
| Cloud | Hosted on-prem | Remediation | Platforms | Pricing | |
|---|---|---|---|---|---|
| SolarWinds SEM | Sure | Sure | Contains some automated remediation options. | Home windows, Linux, and Mac. | Begins at $2,992 |
| CrowdStrike Falcon Subsequent-Gen SIEM | Sure | No | Full vary of remediation capabilities. | Home windows, Linux, Mac, and Chrome. | Contact for quote |
| Splunk Enterprise Safety | Sure | No | Some remediation capabilities. | Home windows, Linux, and Mac. | Reportedly $173 per thirty days as much as $1,800 per GB |
| Datadog Safety Monitoring | Sure | No | Restricted remediation capabilities. | Home windows, Linux, and Mac. | Begins at $15 per host, per thirty days |
| LogRhythm SIEM | Sure | Sure | Restricted remediation capabilities. | Home windows, Linux, and Mac. | Contact for quote |
| RSA NetWitness SIEM | Sure | Sure | Restricted remediation capabilities. | Home windows, Linux, and Mac. | Contact for quote |
| ManageEngine Log360 | Sure | Sure | Restricted remediation capabilities | Home windows, Linux, and Mac. | Customized quote by way of on-line type |
| IBM Safety QRadar SIEM | Sure | Sure | Full remediation capabilities. | Home windows, Linux, and Mac. | Customized quote by way of on-line value estimator |
| Trellix Enterprise Safety Supervisor | Sure | Sure | Remediation capabilities solely accessible with buy of extra Trellix modules. | Home windows, Linux, and Mac. | Contact for quote |
| AT&T USM Wherever | Sure | No | Remediation included | Home windows, Linux, and Mac. | Begins at $1,075 per thirty days |
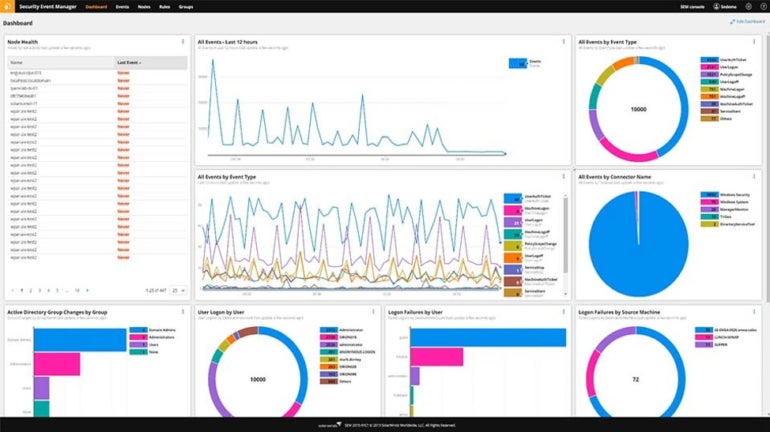
SolarWinds: Finest for log aggregation

SolarWinds Safety Occasion Supervisor (SEM) is targeted on log aggregation and menace detection. It will possibly simply course of and ahead uncooked occasion log knowledge to exterior functions for additional evaluation utilizing syslog protocols, which is an space the place it stands out from the competitors.
Why I picked SolarWinds
I picked SolarWinds for its in depth log aggregation and log evaluation performance. This permits companies to know the precise state of their units, discover the root-cause of every log, and consequently implement methods to enhance the identical. SolarWinds’ capacity to share huge quantities of log knowledge with different functions is a big plus as properly.
Pricing
- SolarWinds annual SEM subscriptions begin at $2,992.
- Perpetual licensing is out there for round $6,168.
Options
- Automation to remediate some incidents.
- Export log knowledge and share it with different groups or distributors.
- Dashboards point out the state of safety, and experiences tackle compliance necessities.
- Pre-built connectors pull knowledge from quite a few sources.
- A file integrity checker tracks entry and adjustments made to recordsdata and folders to detect unauthorized or malicious exercise.
Integrations
- Amazon Net Providers.
- Azure.
- Heroku.
- Apache.
- Oracle.
SolarWinds professionals and cons
| Execs | Cons |
|---|---|
| Good for network-related occasions and analyzing per-host actions, resembling logons, privilege utilization, and registry alterations. | Dashboards can turn out to be cluttered and exhausting to grasp when processing massive quantities of information. |
| Safety features embody knowledge encryption, single sign-on, and sensible card authorization. | Can wrestle with the complexity of very massive enterprise environments. |
| Potential to limit entry from IPs, block functions, and deny entry to detachable media. | Automated doesn’t present a full vary of remediation capabilities. |
Options
- Gather logs at petabyte scale.
- Quickly entry stay knowledge with sub-second latency.
- Quick search, real-time alerting, and customizable dashboards.
- Retain knowledge so long as you want for compliance, menace searching, and historic investigations.

Integrations
- AWS.
- Google Cloud.
- Azure.
- Purple Hat.
- Different CrowStrike merchandise.
CrowdStrike professionals and cons
| Execs | Cons |
|---|---|
| Index-free structure and compression know-how reduce the computing and storage assets required to ingest and handle knowledge. | Developed from the XDR facet, so is extra of a log administration instrument with SIEM-like options than a full-featured SIEM suite. |
| Stated to chop log administration prices by as much as 80% in comparison with various options. | |
| Robust remediation capabilities, courtesy of integration with the CrowdStrike Falcon platform. |
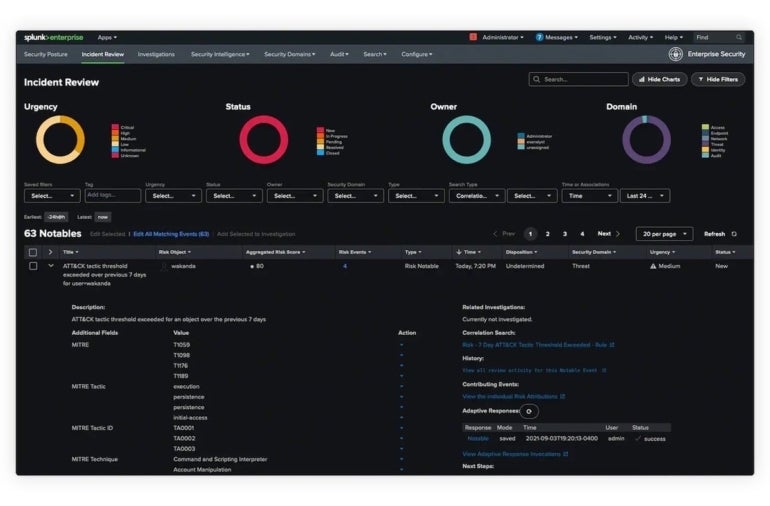
Splunk Enterprise Safety: Finest for cloud-native setting

Splunk Enterprise Safety gives cloud-based security-related occasion notifications and log monitoring. It will possibly determine useful resource bottlenecks, failing {hardware}, capability points, and different potential points. Because it developed within the period of the cloud, it’s significantly properly suited to cloud-native environments.
Why I picked Splunk Enterprise Safety
Splunk Enterprise Safety received on this listing for being specifically geared up to guard cloud environments. It permits cloud-native organizations to simply set up safety monitoring and unified visibility within the cloud. Its complete visibility capabilities are coupled with 1,500+ detections, 1000’s of integrations, and risk-based alerting. Splunk’s unified menace detection, investigation, and response service is a safety instrument that many cloud-native firms ought to take into account.
Pricing
- Splunk’s advanced pricing construction is cut up into entity, exercise, workload, and ingest classes.
- Splunk doesn’t publish precise costs, however consumer experiences place them wherever from $173 per thirty days as much as $1,800 per GB.
Options
- Risk detection with machine studying, together with 1,400 detections for frameworks resembling MITRE and others.
- Ingest and monitor tens of terabytes of information per day from any supply, structured or unstructured.
- Attribute threat to customers and methods, map alerts to cybersecurity frameworks, and set off alerts when threat exceeds thresholds.
- Examine safety occasions or suspicious exercise quickly.
Integrations
- AWS.
- Azure.
- Google Cloud Platform.
- Kubernetes.
- OpenShift.
- Kafka.
Splunk professionals and cons
| Execs | Cons |
|---|---|
| Triggers that reply to logged conditions with custom-made response patterns. | Some customers take into account Splunk to be costly when monitoring massive quantities of information in main enterprise environments. |
| Analytics capabilities are in-built, which may produce long-term graphs. | The corporate’s not too long ago introduced acquisition by Cisco might result in lengthy integration delays and lack of progress on its innovation roadmap. |
| View a variety of logs and drill down into particular instances or knowledge sources. | |
| Potential to resolve issues throughout a number of platforms. |
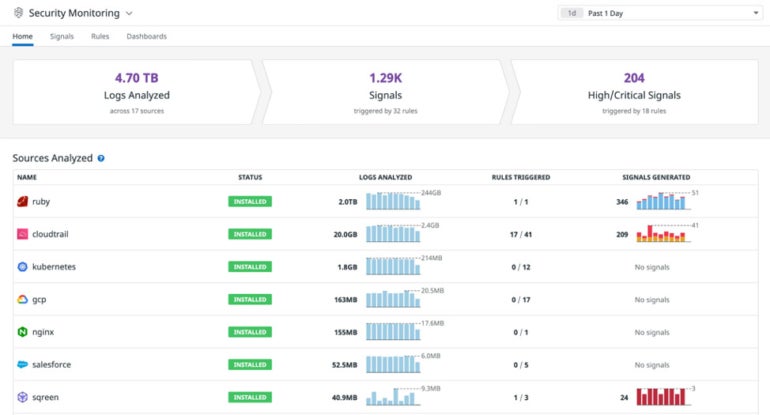
Datadog Safety Monitoring: Finest for personalization

Datadog has designed its platform to be extremely customizable to consumer wants. Datadog Safety Monitoring makes it comparatively straightforward to see at a look what’s occurring with all sources being analyzed. It gives safety monitoring for dynamic environments, real-time safety monitoring instruments, and root trigger evaluation performance. There’s additionally a free trial that lets group’s take a look at drive Datadog to see if it matches their wants and necessities.
Why I picked Datadog Safety Monitoring
I selected Datadog Safety Monitoring for its robust emphasis on user-configuration and customizability. Specifically, organizations can make the most of Datadog’s configurable guidelines to trace down frequent attacker habits and strategies. It’s also possible to customise which logs you wish to index as you proceed to ingest and course of knowledge. That is on high of getting a customizable dashboard and consumer interface.
Pricing
- The professional model prices $15 per host per thirty days, and the enterprise model is $23 per host per thirty days.
Options
- Over 350 detection guidelines and greater than 500 integrations with log sources present full visibility into safety operations.
- Potential to see inside any stack or software at any scale and wherever.
- Infrastructure monitoring, APM, log administration, system monitoring, cloud workload monitoring, server monitoring, and database monitoring, all included.
- Assemble knowledge from logs and different metrics to offer context and reduce incident response time.
Integrations
- Slack.
- SSH.
- AWS.
- Google Cloud Platform.
- Oracle.
- IBM Cloud.
Datadog professionals and cons
| Execs | Cons |
|---|---|
| Datadog takes a monitoring strategy geared towards analytics and is favored by DevOps and IT to handle cloud and infrastructure efficiency. | Datadog stops wanting calling itself a whole SIEM platform, as it’s extra centered on cloud monitoring and safety however has been increasing its cloud SIEM capabilities. |
| Datadog set up is simple, courtesy of agent deployment. | Datadog lacks among the log monitoring capabilities of full-featured SIEM platforms. |
| Dashboards and interfaces are straightforward to customise. |
LogRhythm SIEM: Finest for on-premises

LogRhythm’s SIEM software program is designed to be hosted on-premises. It has constructed AI and automation options into its platform. Reporting primarily based on queries is simple to configure. The system integrates properly with an array of safety and technological options.
SEE: The SIEM Purchaser’s Information (TechRepublic)
Why I picked LogRhythm SIEM
For organizations requiring an on-prem resolution, I like to recommend LogRhythm. You get a holistic safety strategy, getting options resembling embedded modules, menace monitoring, and automatic detection and response. It additionally gives streamlined incident investigation and evaluation capabilities for organizations searching for a chook’s-eye-view of their IT infrastructure. For on-premises deployments, LogRhythm additionally emphasizes offering highly-usable content material for compliance and regulatory necessities.
Pricing
- Contact for curated pricing.
- Quite a lot of pricing choices can be found, resembling perpetual or subscription software program licenses, a vast knowledge plan and a high-performance plan.
Options
- Heightens the detection of safety and potential threats.
- LogRhythm gives an built-in consumer expertise.
- Combines enterprise log administration, safety analytics, consumer entity and behavioral analytics (UEBA), community visitors and behavioral analytics (NTBA), and safety automation and orchestration.
- In addition to an on-prem model, it additionally gives a cloud-based SIEM.

Integrations
- Kibana.
- Development Micro.
- Rapid7.
- Acronis.
- CimTrak.
- CloudSEK.
LogRythm professionals and cons
| Execs | Cons |
|---|---|
| Constructed on a machine analytics/knowledge lake know-how basis that’s designed to scale simply. | Massive upfront funding typically wanted for the on-prem model. |
| Open platform permits for integration with enterprise safety and IT infrastructure. | |
| Embedded modules, dashboards, and guidelines ship menace monitoring, menace searching, menace investigation, and incident response. | |
| Integration with many third-party platforms. | |
| Consumer feedback are favorable concerning the pace and responsiveness of the assist crew. |
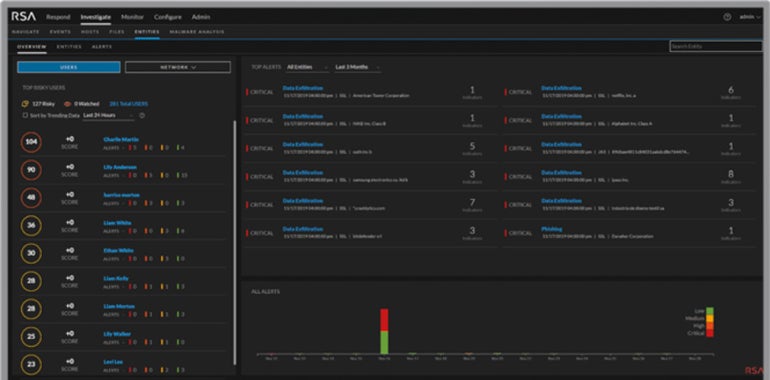
RSA NetWitness: Finest for giant enterprises

RSA, well-known for its multifactor comfortable and exhausting token authentication merchandise, has a powerful footprint within the total safety neighborhood. Its NetWitness SIEM is geared extra towards massive companies, with variations that work each on-premises and by way of cloud.
SEE: Prime 8 Superior Risk Safety Instruments and Software program Choices for 2024 (TechRepublic)
Why I picked RSA NetWitness
RSA NetWitness carved its identify on this listing for being an all-around safety resolution constructed for greater organizations. It gives visibility throughout a variety of seize factors, in addition to having sensible analytics and automation capabilities for each identified and unknown assaults. I discover that enormous companies, particularly, will profit from NetWitness’ fast-performing menace detection — which is ready to reveal the complete assault scope in a well timed method.
Pricing
- Contact for curated pricing.
Options
- NetWitness screens for actionable occasions.
- Conduct analytics observe hacker exercise and recreate full classes to look at the exact anatomy of an assault.
- Intelligence feeds primarily based on customizable info monitor and stay key operations.
- Visibility into log knowledge unfold throughout the IT setting.
Integrations
- Azure.
- AWS.
- Cisco.
- Google Cloud Platform.
- Symantec Endpoint Safety.
- Kaspersky CyberTrace.
RSA NetWitness professionals and cons
| Execs | Cons |
|---|---|
| Simplifies menace detection, reduces dwell time, and helps compliance. | The educational curve and implementation efforts will be steep. |
| Centralized log administration and log monitoring for logs generated by public clouds and SaaS functions. | Some customers require a considerable amount of rack area. |
| Identification of suspicious exercise that evades signature-based safety instruments. |
ManageEngine Log360: Finest for small companies

ManageEngine Log360 is a SIEM that serves companies of all sizes however is particularly suited to small enterprise (SMBs) deployments. It additionally integrates properly with a sequence of different safety and monitoring merchandise that the corporate gives.
Why I picked ManageEngine Log360
ManageEngine Log 360 is on this listing for being particularly helpful to SMBs. It has all of the SIEM options SMBs will profit from, resembling occasion log evaluation and cloud infrastructure monitoring, in addition to menace detection and automatic responses. I significantly like how ManageEngine makes it very accessible for companies to strive Log360’s premium options at no cost — by way of a beneficiant 30-day free trial.
Pricing
- Reply ManageEngine’s on-line type to get a personalised quote.
Options
- Detect inside threats, resembling knowledge exfiltration and consumer account compromise, by recognizing refined adjustments in consumer exercise.
- Determine suspicious or blacklisted IPs, URLs, and domains intruding into your community by correlating your log knowledge with reputed menace feeds.
- Automate responses to occasions with configurable workflows.
- Monitor lively VPN connections and obtain alerts on uncommon VPN actions and VPN entry from malicious sources.

Integrations
- AWS.
- Azure.
- Salesforce.
- Google Cloud.
- ESET Antivirus.
- Cisco.
ManageEngine Log360 professionals and cons
| Execs | Cons |
|---|---|
| Migrate SharePoint environments to Microsoft 365 by deciding on the required SharePoint web site customers, teams, and permission ranges. | Some customers complain of poor assist. |
| Audit adjustments in Energetic Listing infrastructure and Azure AD in real-time. | Could wrestle to scale properly sufficient in massive, advanced environments. |
| Uncover and classify delicate recordsdata, audit customers’ file actions, and analyze file permissions. | |
| Detect, disrupt, and forestall delicate knowledge leaks by way of endpoints, like USBs and printers, electronic mail, and net functions with real-time safety monitoring. |
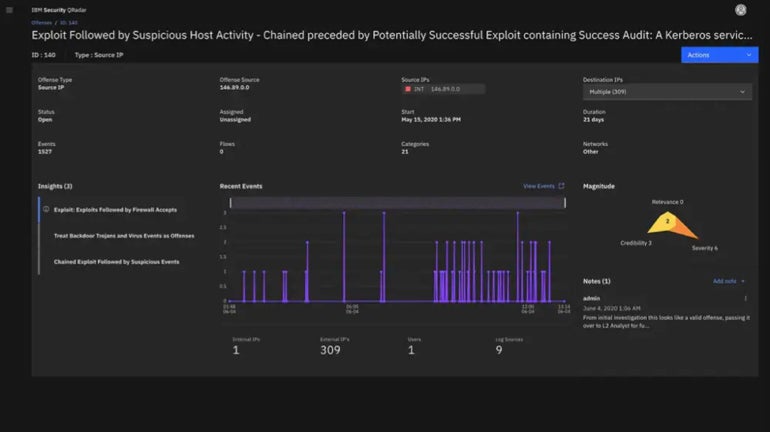
IBM Safety QRadar SIEM: Finest for IBM retailers

IBM QRadar is a menace detection and response resolution that features a SIEM module. As such, IBM Safety QRadar SIEM is particularly suited to enterprises which might be closely invested in IBM instruments and methods, in addition to massive enterprise deployments.
Why I picked IBM Safety QRadar SIEM
I picked IBM’s QRadar SIEM as a sensible selection for firms which have already closely built-in IBM merchandise and instruments into their workflow. Thankfully, Safety QRadar additionally gives a superb variety of integrations with different third-party providers — making it a viable SIEM choice even for firms that don’t have an IBM ecosystem.
Pricing
- Go to IBM’s official on-line value estimator to get a personalised quote.
Options
- Accelerated menace response by dashboards that spotlight alerts that matter.
- Makes use of close to real-time analytics to intelligently examine and prioritize high-fidelity alerts primarily based on severity of threat.
- Identifies insider threats and dangerous consumer habits.
- A part of IBM Cloud Pak for Safety which makes use of AI to offer threat assessments in addition to analytics.
Integrations
- AWS.
- Examine Level.
- Google Cloud.
- Palo Alto Networks.
- Development Micro.
- Carbon Black (VMware).
IBM Safety QRadar professionals and cons
| Execs | Cons |
|---|---|
| Machine learning-based analytics to determine anomalies as potential menace actors. | Lack of integration with different SIEM instruments. |
| QRadar SIEM augments conventional log knowledge by monitoring key community circulate knowledge. | These not utilizing IBM platforms might discover it troublesome to deploy. |
Trellix Safety Operations and Analytics: Finest for Home windows retailers

Trellix Safety Operations (SecOps) and Analytics accommodates the bones of the outdated McAfee Enterprise Safety Supervisor SIEM platform and is now a module often known as Trellix Enterprise Safety Supervisor. That SIEM providing was Energetic Listing-based and well-suited to Home windows environments. However Trellix has expanded it to supply robust cloud assist.
Why I picked Trellix Safety Operations and Analytics
I’ve Trellix Safety Operations and Analytics on this listing for its robust compatibility with Home windows machines, making it a good selection for companies that primarily run a Home windows-centric setting. Apart from that, it gives highly effective automation capabilities for quick detection and remediation. Ideally, this is able to result in decrease threat publicity and quicker response instances when coping with threats.
Pricing
- Contact Trellix for curated pricing.
Options
- The Trellix Helix SecOps platform is a part of a collection that features SIEM to assist IT take management from incident to detection to response.
- Trellix Insights gives menace intelligence to foretell and prioritize threats and prescribe countermeasures.
- Trellix ePO safety administration platform helps IT management and administer all endpoints from a single console.
Integrations
- Trellix Endpoint Detection and Response.
- Trelix Helix.
- Trelix Insights.
- Cisco.
Trellix Safety Operations and Analytics professionals and cons
| Execs | Cons |
|---|---|
| A central view of potential threats with built-in workflows removes complexity. | The total Trellix suite is required to offer full remediation capabilities. |
| Get larger transparency monitoring customers, functions, networks, and units. | Some customers complain that it may be sluggish to reply. |
| Actual-time menace identification and response reduces lead time to guard towards threats. | |
| Can combine merchandise from 650+ third-party distributors. |
AT&T USM Wherever: Finest for asset discovery

AlienVault Unified Safety Administration platform (USM) is now AT&T USM Wherever. It discovers property and gathers knowledge about operating providers, customers, working methods, and {hardware} info. This asset focus means it will probably decide up any units within the setting that it protects.
Why I picked AT&T USM Wherever
USM Wherever received its place on this listing as a stable instrument for companies that prioritize menace detection and asset discovery above all else. It will possibly detect vulnerabilities and threats on the cloud, the community, or on-prem — making it a digital detection resolution for every type of IT infrastructures.
Pricing
- Necessities – $1,075 per thirty days; tailor-made for small IT groups as a safety and compliance instrument.
- Normal – $1,695 per thirty days; catered in direction of IT safety groups that require automation and deep safety evaluation.
- Premium – $2,595 per thirty days; geared in direction of IT safety groups whose aim is to fulfill PCI DSS audit necessities.
- You might also reply USM Wherever’s on-line type to get a personalised citation.
Options
- Mechanically collects and analyzes knowledge throughout the assault floor.
- Risk intelligence offered by AT&T Alien Labs.
- Helps an ecosystem of AlienApps to orchestrate and automate actions in direction of different safety applied sciences and reply to incidents.

Integrations
Trellix Safety Operations and Analytics professionals and cons
| Execs | Cons |
|---|---|
| Good for individuals who need their cybersecurity and SIEM providers managed by another person. | Not appropriate for organizations that want to keep up tight management over their very own property for sensitivity or compliance causes. |
Key options of SIEM software program
All SIEM software program instruments care for log monitoring and administration. Additional vital options embody whether or not the instrument is cloud-based, whether or not it may be hosted on-prem, whether or not it consists of remediation capabilities, and what platforms it runs on.
Cloud
Nowadays, most SIEM software program relies within the cloud. Cloud-based merchandise are simpler to deploy, simpler to handle, and less complicated to run. And with so many enterprises working in a number of clouds, SIEM instruments within the cloud are a must have. Some distributors present SIEM on a Software program-as-a-Service (SaaS) foundation, and others provide it as a completely managed service.
Hosted On-prem
Some enterprises are averse to working within the cloud attributable to privateness, safety, or compliance causes. They should load SIEM on their very own inside servers. Some distributors provide this selection, whereas others don’t.
Remediation
SIEM originated as a method to simplify the compilation and evaluation of safety logs. It offered enterprises with a method to consider enormous numbers of log entries and alerts and detect potential points or intrusions. Extra not too long ago, nevertheless, SIEM platforms have begun so as to add remediation capabilities. Some provide methods to automate a restricted variety of remediation actions. However a number of instruments present entry to a variety of safety remediations, both inside the SIEM itself or by way of built-in or related instruments offered by the identical vendor.
SEE: All the things You Must Know concerning the Malvertising Cybersecurity Risk (TechRepublic Premium)
Platforms
The SIEM market is very aggressive. Most distributors have to offer instruments that function on all main working methods and cloud environments. However there could be a few holes. These with an intensive Google Chrome presence, for instance, might discover their SIEM choices restricted. It’s vital, due to this fact, to confirm that your potential vendor of selection is absolutely set as much as run their methods in your setting.
How do I select the most effective SIEM software program for my enterprise?
Each one of many merchandise outlined right here gives high quality safety safety and can be of worth to any group — and each group wants some degree of log-based real-time safety evaluation to assist stop and detect threats.
Making the suitable selection when deciding on SIEM software program goes to depend upon firm priorities, necessities, funds, degree of IT experience, and degree of IT availability to evaluate and deal with threats. If cash is not any object and tech employees isn’t ready or prepared to roll up its sleeves and deal with safety dangers, a managed SIEM like USM Wherever could be the method to go. If firm budgets are much less strong and in-house expertise and time are copious, SolarWinds SEM, Datadog, or AlienVault can be among the many candidates. In any other case, choices resembling LogRhythm, CrowdSrike, Splunk, RSA, IBM QRadar and ManageEngine ought to be excessive on the listing of these to contemplate.
Methodology
The SIEM instruments I coated right here had been chosen primarily based on an intensive analysis of official safety function inclusions, prominence in evaluation experiences, and real-world consumer critiques. Every SIEM resolution was analyzed primarily based on its professionals and cons, safety features, and value choices.
As well as, a heavy emphasis was positioned on how every SIEM instrument may very well be of use to sure use circumstances and companies. This takes under consideration specializations per product and what forms of organizations can finest maximize their function set.
Lastly, the range and variety of integrations with third-party safety providers had been additionally thought of for this shortlist. That is to make sure the graceful adoption of the SIEM resolution inside a enterprise’ current structure and the seamless monitoring of information factors throughout the group’s IT infrastructure for the SIEM itself.
