
A brand new JavaScript obfuscation technique using invisible Unicode characters to signify binary values is being actively abused in phishing assaults concentrating on associates of an American political motion committee (PAC).
Juniper Risk Labs that noticed the assault reviews that it happened in early January 2025 and carries indicators of sophistication similar to using:
- Personalised personal data to focus on victims,
- Debugger breakpoint and timing checks to evade detection,
- Recursively wrapped Postmark monitoring hyperlinks to obscure closing phishing locations.
JavaScript developer Martin Kleppe first disclosed the obfuscation approach in October 2024, and its fast adoption in precise assaults highlights how rapidly new analysis turns into weaponized.
Making JS payloads “invisible”
The brand new obfuscation approach exploits invisible Unicode characters, particularly Hangul half-width (U+FFA0) and Hangul full-width (U+3164).
Every ASCII character within the JavaScript payload is transformed into an 8-bit binary illustration, and the binary values (ones and zeros) in it are changed with invisible Hangul characters.
The obfuscated code is saved as a property in a JavaScript object, and since Hangul filler characters are rendered as clean area, the payload within the script appears empty, as proven by the clean area on the finish of the picture under.
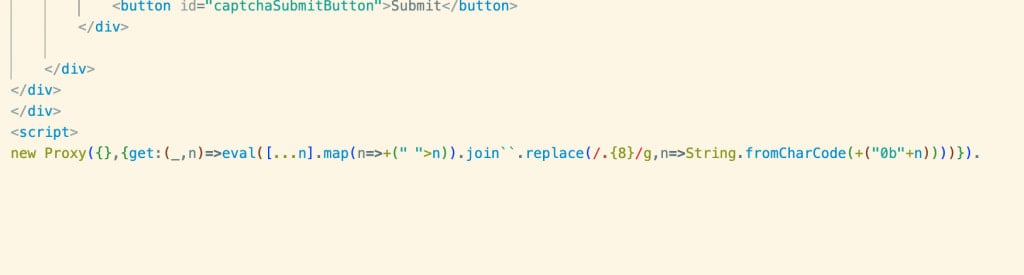
Supply: Juniper
A brief bootstrap script retrieves the hidden payload utilizing a JavaScript Proxy ‘get() lure.’ When the hidden property is accessed, the Proxy converts the invisible Hangul filler characters again into binary and reconstructs the unique JavaScript code.
Juniper analysts report that the attackers use additional concealment steps along with the above, like encoding the script with base64 and utilizing anti-debugging checks to evade evaluation.
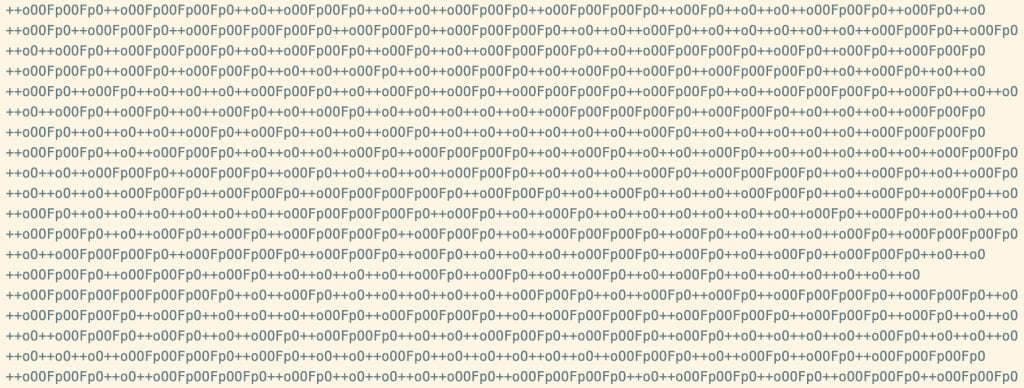
Supply: Juniper
“The assaults had been extremely personalised, together with personal data, and the preliminary JavaScript would attempt to invoke a debugger breakpoint if it had been being analyzed, detect a delay, after which abort the assault by redirecting to a benign web site,” explains Juniper.
The assaults are robust to detect as empty whitespace reduces the probability that even safety scanners will flag it as malicious.
For the reason that payload is only a property in an object, it might be injected into professional scripts with out elevating suspicion; plus, the entire encoding course of is straightforward to implement and does not require superior information.
Juniper says two of the domains used on this marketing campaign had been beforehand linked to the Tycoon 2FA phishing equipment.
If that’s the case, we are going to seemingly see this invisible obfuscation technique adopted by a broader vary of attackers sooner or later.
