Chris Love, co-author of the ebook Core Kubernetes, joins host Robert Blumen for a dialog about kubernetes safety. Chris identifies the node layer, secrets and techniques administration, the community layer, incorporates, and pods as probably the most essential areas to be addressed. The dialog explores a variety of subjects, together with when to just accept defaults and when to override; variations between self-managed clusters and cloud-service provider-managed clusters; and what can go fallacious at every layer — and how one can deal with these points. They additional focus on managing the node layer; community safety finest practices; kubernetes secrets and techniques and integration with cloud-service supplier secrets and techniques; container safety; pod safety, and Chris affords his views on policy-as-code frameworks and scanners.
Delivered to you by IEEE Laptop Society and IEEE Software program journal.
Present Notes
References
 Associated Episodes
Associated Episodes
Transcript
Transcript dropped at you by IEEE Software program journal.
This transcript was mechanically generated. To counsel enhancements within the textual content, please contact [email protected] and embody the episode quantity and URL.
Robert Blumen 00:00:19 For Software program Engineering Radio, that is Robert Blumen. I’ve with me Chris Love. Chris works at Modernize as a distinguished engineer. Chris and Jay Vyas are co-authors of the ebook Core Kubernetes, and Chris is a Google Cloud licensed fellow. Chris, welcome to Software program Engineering Radio.
Chris Love 00:00:40 Thanks Robert. Actually respect you having me come and converse with you of us at present.
Robert Blumen 00:00:45 Blissful to have you ever. We’re going to reap the benefits of your being right here to speak about Kubernetes safety. Now, Kubernetes is a distributed system besides exterior site visitors. It makes use of compute sources. Is there such a factor as Kubernetes safety or is it nearly following finest practices which can be well-known for a majority of these techniques?
Chris Love 00:01:09 I believe it’s each. I consider course it’s finest practices like replace your software program dependencies, replace your dependencies out of your working system. It’s that, however now you’re working a containerized system, so it’s a must to bear in mind to replace the dependencies within the container in addition to replace your host model of Bash. So after all there’s intricacies to it. We’re working a pleasant distributed system that enables us to do sophisticated stuff like scaling and we now have failover, however due to that, we’ve received somewhat bit extra sophisticated networking that may trigger some challenges from a safety standpoint. However we now have different distributed techniques that we’ve been utilizing for some time. Most of them are primarily based round containers, however there’s undoubtedly some wrinkles. However such as you stated, on the finish of the day, it’s an API layer. You’ve received a bunch of compute nodes, that are both your servers or your EC2 situations or your GKE situations and also you’ve received a bunch of containers working round. So I’d say it’s non-trivial, but it surely’s not rocket science. It’s not as difficult as catching a rocket with a pair chopsticks.
Robert Blumen 00:02:15 The general umbrella of Kubernetes safety, it has many subtopics greater than we will cowl in an hour. In the event you have been to choose a number of which can be most necessary to concentrate on, what’s your brief checklist?
Chris Love 00:02:28 I’d attempt to group them into, I form of go from a big world inner, so we might discuss what to anticipate when organising a Kubernetes cluster. So total safety, then you may go all the way down to a no stage safety from there, community safety, from there pod safety, and from there container safety. Container safety is properly documented, however I believe some of us both don’t have the money and time to place these in place. Working system safety, I’m not going to speak to you about. There’s a lot of different references that people can go to that I all the time take a look at myself as a Lego engineer, proper? We’ve received constructing blocks. Some are distinctive to Kubernetes, and such as you stated, some working system safety is working system safety, however sometimes on an working system you aren’t working two completely different community layers and that’s what you get inside Kubernetes.
Robert Blumen 00:03:20 So it’d be a very good time for me to let the listeners know we did a whole episode on Kubernetes Networking quantity 619. We’ll return to that somewhat bit later. Let’s go down your checklist, Chris, and hit these items so as. Beginning with organising Kubernetes total safety, what are among the details that ought to be addressed?
Chris Love 00:03:41 Proper. You wish to take into consideration from a community layer, from a node setup layer, and from an total like account permissions layer. Once more, in case you’re working in an information heart, this can be a little bit completely different, proper? However I’d say majority of individuals which can be working in Kubernetes are working inside AWS or GKE or Azure or choose your Cloud supplier. So there’s all the time some gotchas round these Cloud environments. For example, you wish to be sure that the function that you just’re organising your cluster with and the function that the cluster’s working with are the right roles. You don’t wish to set your cluster up with a task that’s an account stage admin. You wish to give your Kubernetes cluster and your Kubernetes nodes the suitable stage of permissions. So meaning organising a person earlier than you arrange Kubernetes. From there additionally, take a look at a personal community.
Chris Love 00:04:33 Don’t expose your nodes to the general public. In different phrases, Port22 on node A shouldn’t be accessible by way of an exterior community. You’re going to want to VPN into your nodes, and realistically, builders and admins shouldn’t essentially must at a node stage. Additionally, your API layer or net API must also be behind a firewall that ought to be networked in. It ought to be on a personal community the place of us aren’t capable of entry it. And folks, we’ve had bugs in Kubernetes the place authentication for very brief period of time was damaged on the API layer. And luckily, the parents that maintained Kubernetes fastened it fairly quick. Nevertheless it was in a single day the place in case you had a publicly uncovered API and also you had X, Y, Z model of Kubernetes, folks might simply do a coup management command proper to it. So doing a little primary setup earlier than you’re considering by way of your safety mannequin and your safety setup earlier than you arrange a cluster is actually necessary. IP spacing, as an illustration, that will get of us in hassle as properly. So that you wish to make sure that the subnet you’re working on is personal.
Robert Blumen 00:05:40 Details there could be use the Cloud service suppliers entry administration. Use a personal VPC and put your complete cluster behind some form of firewall or proxy to chop it off from the net. Did I miss something?
Chris Love 00:05:55 No. And then you definately’re some type of public ingress, proper? You’re having to keep up some type of ingress controller that’ll permit exterior site visitors to go in internally into your cluster, which makes it somewhat bit extra sophisticated, however I’d relatively not have nodes uncovered to the web personally.
Robert Blumen 00:06:11 Would any of the final set of solutions change? If you’re working the cluster on the corporate’s personal computer systems,
Chris Love 00:06:19 You may give it some thought in the identical approach, proper? You’d have some type of router arrange the place you once more, have inner IP addresses and exterior IP addresses. It’s simply extra work. You need to arrange your air quote, VPC community or community that’s inner by hand as and preserve it. And you may’t simply make a terraform name to your Cloud supplier’s API to set it up for you. You need to have your self or any individual else set these routers up. However similar sort of mannequin exists. Networking is networking, is networking. Now we have an IP addresses right here and there.
Robert Blumen 00:06:53 Do you have got any tales from a time you have been organising a cluster, one thing you missed or from auditing one other setup the place you discovered one thing that wanted to be locked down?
Chris Love 00:07:04 Yeah, a lot of these I’ve discovered, just about the whole lot that I’ve talked about arrange incorrectly. A number of the instances folks arrange their cluster and expose the API server and/or the nodes or each publicly. It’s extra sophisticated to arrange a VPN sort mechanism to get into your nodes. It’s a lot simpler to not have it that approach, proper? In addition to I’ve seen many clusters that have been created utilizing, like I’ve a Cloud entry, a Cloud admin account, and I incorrectly arrange my cluster and it’s utilizing Chris Love’s Cloud admin account. That’s not good. Having the ability to have a Kubernetes cluster artistic VPC or create different elements isn’t an effective way to do safety inside Kubernetes. I’m each authorization and each off and off Z are sophisticated sufficient. You don’t wish to add a layer the place you’re working your cluster as a Chris Love person.
Robert Blumen 00:08:04 I’ve arrange a cluster, I went by way of my guidelines, accomplished all of the issues we talked about. Are there any both open-source frameworks or testing instruments that might run by way of and confirm that the issues that want entry have and the issues which shouldn’t have entry can not?
Chris Love 00:08:21 I imagine the CNCF has a testing instrument that goes by way of your cluster soup to nuts, form of provides it a as soon as over. Additionally, frankly, a documentation on Kubernetes. Safety on the Kubernetes websites, super. So I’m going by way of it nearly drills down in the identical order that I’ve been utilizing in a very long time, and I can’t say I’ve written any of the safety documentation there, but it surely has a guidelines of what to do. You’ve received instruments which can be owned or been donated and maintained by different corporations that CNCF have, and there’s loads of corporations there outdoors that may both enable you set them up or check them after the very fact.
Robert Blumen 00:08:58 Sounds nice. I believe we will transfer on to the following layer that you just deal with, which is node safety. What are among the frequent assaults on the node stage?
Chris Love 00:09:09 Once more, it’s occasion or server stage safety. It’s SSH assaults, proper? Luckily, our modern-day Cloud suppliers give us good authentication strategies for SSH. That’s not a username and password, however once more, it goes again to your sustaining nodes. I’d say this, except you’re on information heart, you’re not in-place upgrades. And in case you’re working in your individual information heart, you would be working virtualization as properly. And in case you’re virtualized, you have got your individual Cloud. We’re doing rollovers of an working system to improve your OS. We’re additionally working immutable working techniques, which is one other factor that I extremely suggest. Operating working techniques which have learn solely elements. It means that you can not have unhealthy guys overwrite binaries. That’s only a unhealthy factor. However once more, when it comes to how Kubernetes upgrades, relatively than upgrading your OS, you want to improve a node.
Chris Love 00:10:11 So improve your nodes by way of a rolling improve, and then you definately replace your working system. In the event you’re working on naked steel with out virtualization, then more than likely you’re looking at in place upgrades. However then you may shift round your workloads to do this. As we talked about on the high of the present, OS stage safety is OS it’s actually the, I’d say that’s in all probability the best-known safety posture that we all know of, proper? As a result of system admins have been sustaining OS stage safety for the reason that starting of time, not less than the start of Unix at first of computer systems. In order that’s in all probability the best-known safety layer or the best-known safety practices that we now have. Now as we transfer into the community safety and we transfer into the pod safety and we transfer into container safety, I’d say these are all of the newer applied sciences.
Robert Blumen 00:11:01 If I’m working on a Cloud service supplier, then they handle the nodes, they’ll autoscale nodes in or out of the cluster as wanted. Can I rely on the Cloud service supplier to handle the node picture and to refresh it if vulnerabilities are found? Or is that one thing that as a cluster operator, I have to push a button or do one thing once I desire a refresh of the node picture?
Chris Love 00:11:26 It actually depends upon the way you arrange your cluster. First off, you may run your individual management airplane for Kubernetes. Plenty of corporations which can be somewhat bit extra subtle try this. They’ll nonetheless run their very own grasp situations with ETCD, et cetera, et cetera. So generally the management airplane is maintained, generally it’s not. I’d say the vast majority of corporations which can be working on high of EKS and GCP or AKS, they’re utilizing a managed management airplane. Nodes then again, you typically have choices that the Cloud supplier mechanically upgrades for you or it’s a must to improve them yourselves. What corporations are discovering that it’s typically needed so that you can improve your nodes. Workloads are usually not sometimes such as you nonetheless have sophisticated workloads that aren’t, I’d say Cloud native pleasant essentially. And due to that, the improve course of can have a pair bumps right here and there.
Chris Love 00:12:22 There’s many corporations that also have outages once they do upgrades and you’ll’t have a Cloud supplier mechanically improve for you essentially. Good theoretical world, we’d have the ability to have that. There’s different packages inside Cloud suppliers the place the Cloud suppliers are sustaining your nodes for you. After which after all upgrades do occur within the background. You’re capable of arrange, right here’s the window, I need my upgrades to occur between 2:00 and 4:00 AM jap time on Saturdays as an illustration, or on Tuesdays as a result of that’s the bottom site visitors day of the yr or every week that you’ve. So once more, there’s choices going again to what you’re speaking about initially, Robert, these are choices you want to make earlier than you arrange your cluster. Do you wish to preserve your individual management airplane? Please don’t. Please don’t. Until you actually know what you’re doing. Do you wish to preserve your individual node swimming pools? 50/50 on that relies upon the quantity of employees you have got. Or would you like your Cloud supplier to fully preserve the whole lot for you? And on high of that, then you definately’re much less work, however you lose management. There are trade-offs there. Positively trade-offs.
Robert Blumen 00:13:23 Give some extra particulars of what can go fallacious throughout an improve. Theoretically, Kubernetes will reschedule site visitors off of the nodes you wish to take away and onto the brand new ones. However when does that not work as meant?
Chris Love 00:13:37 Lengthy working jobs, as an illustration, that don’t restart. So stateful purposes that aren’t really Cloud native. You may run into issues with extra sophisticated stateful purposes throughout an improve course of. It’s worthwhile to do one thing to the database, as an illustration, put it right into a sure sort of mode earlier than you improve, earlier than you evict the pod. So generally you’ve received to do three steps earlier than you improve after which three steps after you improve. In order that makes it somewhat bit extra sophisticated. Older database techniques which were made extra Cloud pleasant nonetheless have some challenges. So stateful purposes, lengthy working purposes that don’t essentially restart themselves or you have got a 60-minute job you undergo an improve shouldn’t be upgrading at the moment as a result of these jobs are working. Now you’ve received to rerun a 60-minute job and if it’s a essential course of, it’s form of difficult and you’ll run not solely in upgrades, however you may run the identical factor while you’re working or run into the identical sort of downside while you’re working auto scaling.
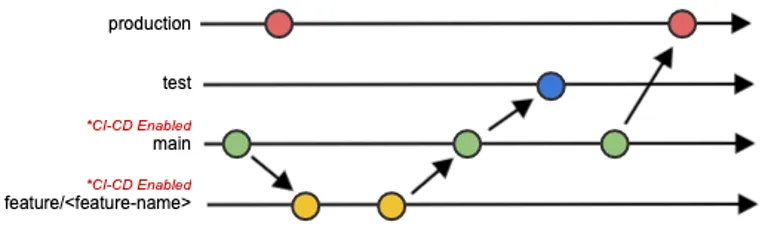
Chris Love 00:14:37 So you probably have an extended working job reminiscent of a CI construct, your autoscaler sizes down the node pool, which in impact is identical sort of conduct you do while you improve a Kubernetes cluster, you’ll have that job kicked off. Hopefully you need that job to restart, however generally they don’t. From safety perspective, the improve course of is necessary that it goes shortly to be able to remediate safety points shortly. In the event you’re redeploying workloads, you’re pushing out new workloads. It’s a mixture of the processes that you’ve in-house to run upgrades, how sophisticated your workload is, in addition to if you want to roll out new workload. Say you’ve received a spring dependency concern the place there’s a CV in spring and you want to roll out a completely new software due to that or 40 purposes, once more, your CI wants to have the ability to deal with that sort of rollout.
Robert Blumen 00:15:29 I’ve been concerned in database migrations some years in the past. This sometimes includes a number of runbooks guide steps such as you described. Had been the three stuff you do earlier than and the three stuff you do after. I’m conscious that there are some choices within the database world the place they’ve created Kubernetes operators that to some extent can take over the function of a human system admin. Are most issues in Kubernetes world now aiming to be fairly automated in face of every kind of disruptions? Or is it nonetheless form of old-fashioned the place database goes to be migrated and we’re going to have downtime and we’re going to babysit it?
Chris Love 00:16:08 Nicely, it depends upon what you’re working, proper? It’s software and operator dependent, not essentially Kubernetes cluster dependent is the way in which I’d put it. If the workload can restart itself properly, you flip a button ham fault tolerance mode and that your fault tolerance works as anticipated, you ought to be advantageous. It’s working the improve in dev first to just be sure you’re advantageous relatively than having a 40-step runbook and playbook. Are we there but? No. In the event you can afford it, have any individual else preserve your databases for you. Have folks like I’d say most corporations aren’t Google, aren’t Apple, aren’t Fb, proper? They don’t have lots of of engineers that preserve their databases for them essentially. If you’re that firm, then yeah, you may have the ability to get away with it. The factor with working databases in different stateful purposes is it’s a must to perceive how that stateful software really runs on high of Kubernetes rather well.
Chris Love 00:17:04 It’s not simply I’m working an software and it runs nice, it’s, I’m working an software on high of Kubernetes due to the way in which it fails over. And it mainly if it says, okay, you bought 60 seconds to go away software ABC or duplicate ABC is a greater strategy to put it. You’ve got 60 seconds and also you’re out of right here. I don’t care what’s happening, this node’s happening and your pit goes to get terminated. So your software has to deal with that. And realistically although, Robert, your software must deal with that anyhow as a result of it’s the identical sample that occurs throughout outages. Once more, it goes again, if your organization can afford RDS, why not use RDS? If your organization can afford working SQL server on Azure, let the specialists deal with it, it turns over some management. You need to run their model of Postgres relatively than you might need three variations of Postgres which you could run.
Chris Love 00:17:58 So in case you want a a lot older model, then you definately is perhaps working it your self. However that’s an entire one other story the place let’s have Postgres up to date in your organization. It goes again to money and time, proper? The story I inform about safety is, you’re going to get hacked. Almost definitely you’re large, you’re going to get hacked and or individuals are going to be knocking in your door quite a bit. Nevertheless it goes again to enterprise danger and money and time. As a lot as we discuss these safety choices and what to do, all of it goes again to what number of hours a day we now have to engineer it, what number of palms we now have on keyboards. And I’d say now we’ve undoubtedly have some assist from AI. I don’t assume it’s fairly there but, however supposedly we’re going to be out of a job right here fairly quickly, Robert. So I don’t imagine that. However that’s an entire one other matter that we don’t want to enter. However like I stated, it’s all money and time we will do that. It’s not rocket science. There’s a broad vary of issues you want to take a look at, but it surely goes again to just about what we’ve been saying over its chat.
Robert Blumen 00:18:51 Would you settle for one of many normal node photographs that’s really helpful by the Cloud service vendor or would you begin from uh, long run or steady launch of your favourite working system after which batten down the hatches to get it much more safe than the off the shelf?
Chris Love 00:19:10 I’d say use off the shelf. And the reason is is that they’ve a employees of 100 folks or extra which can be sustaining that picture. What most corporations, they’re fortunate if they’ve two. Most corporations don’t have those who write kernel stage code and the Cloud suppliers do. A superb instance, this occurred a very long time in the past, was the problem with the Intel processors the place we bumped into some processor points, CVEs throughout the working system itself within the kernel. So the CVE was introduced the day after Google launched new photographs that contained the fixes. So we’re speaking nearly rapid, it took Debian and Ubuntu a pair weeks to catch up if not longer. So that you’re that sort of lag with CVEs the place AWS, the large of us are speaking concerning the CVEs earlier than you even learn about them and so they’re popping out actually quick with patches the place us the identical approach.
Chris Love 00:20:08 And I’m not saying there’s something fallacious with Debian or Ubuntu or XYZ working system. There’s undoubtedly of us that even supply working techniques which can be constructed for Kubernetes these days. So do you want one? I don’t know. Do you have got a use case and is there a enterprise worth in your firm to have one? Nice. Nicely I run on high of like I do work with photographs and I get pissed off that there are some CVEs working round in a pair distributions and so they say, no, these aren’t CVEs and we’re not going to repair them. A number of safety folks don’t like that. However I am going to Amazon Linux as an illustration, and I do know if I’m going to place one thing on Amazon Linux and get it screened, I’d say about 90% of the time, if it’s Amazon Linux preserve packages, it’s going to cross screening. Identical factor with, I overlook the title of the working system that GCP runs, which is totally immutable by the way in which, which is fairly cool.
Chris Love 00:21:05 And once more, I can’t even display that in a number of methods. However once more, it’s leveraging you pay sufficient for a Cloud supplier as it’s, use their toys, leverage their information as a lot as you may in a smart approach. In case you have use instances the place you have got XYZ software program that has to run on the node stage and it’s a must to have this, then I perceive you bought to run that particular working system. However once more, it’s form of like working your individual electronic mail server these days, Robert, working your individual picture registry. Use the companies that do it rather well. Like I don’t wish to run my very own logging. I wish to use any individual to ship my logs off to and or an answer that’s inhouse that I ship my very own logs off to. I don’t wish to do it myself. I’ve an admin and electronic mail server and I don’t know the way lengthy we wish to use the specialists.
Robert Blumen 00:21:57 Let’s swap subjects now and transfer on to the following layer of your stack of the highest safety points. That will be the community. What are the primary points within the community safety space?
Chris Love 00:22:10 It’s entry. So inside a Kubernetes cluster, any pod can entry every other pod except you arrange community restrictions. You both wish to use community insurance policies or a service mesh like Istio. That is in all probability one of many areas that I see the least maturity in throughout the of us that I work with. I’d say just lately I’ve seen way more maturity the place of us are utilizing service mesh that they wish to use or they’re utilizing community safety insurance policies the place you’re restricted to name outdoors site visitors. In different phrases, your pod can not get to Google in addition to your duplicate A can not get to a special namespace with duplicate B. And that’s undoubtedly one thing that you want to take a look at and management and it’s a number of work to be sincere. Inside a namespace most pods will have the ability to discuss to different pods in addition to, so there’s two other ways which you could arrange a pod when it comes to which community it runs on.
Chris Love 00:23:08 As a result of we now have our host community, proper? And it’s how all the opposite hosts discuss to one another. It’s the standard networking sample that we take a look at. Then we now have some type of pod community, whether or not it’s digital or it’s IPed a special approach. They’ve accomplished it about 15 other ways sideways. However in case you run your pod on the host community, it could actually entry the whole lot within the host. Then relying on the permissions you give it. So undoubtedly preserve your pods on the pod community. There are some Damon units and controllers that do host stage operations. For example, you want Nvidia drivers put in, proper? There’s Damon units that can run in your host. So when your host begins Nvidia drivers get put in. So it’s a must to run them on the host community, however in case you can, and majority of your workloads ought to be in your pod community in addition to community site visitors.
Chris Love 00:23:58 I’d discuss, you talked about operators. Operators want to speak to the management airplane, the API server. And due to that you just’re RBAC safety by default don’t mount the service account token, which permits so that you can authenticate or at instances in case you misconfigure it means that you can authenticate with the API server. So it’s controlling entry there. Additionally, you’re DNS as properly. That’s one other consideration at a community layer. All the pieces mainly inside Kubernetes is all in DNS while you’re speaking to the servers, that’s DNS, while you’re speaking to a different pod that’s DNS and that’s actually necessary with in a Kubernetes cluster itself. However yeah, one of many key issues you may take a look at with intrusions is you go from pod to both a secret you shouldn’t have the ability to get at otherwise you go from pod to your API server. Secrets and techniques is one other factor we should always focus on, Robert. If you wish to throw that within the checklist, we will discuss that after we discuss networks, however there have been some actually good enhancements in retaining Secrets and techniques secret as it will be.
Robert Blumen 00:25:01 I wish to return by way of, you made various factors there and to delve into them a bit extra element. Community safety coverage controls, which namespace talk with different namespace and repair mesh is extra granular. They’re related however completely different. Would you employ one or each? And for what objective each?
Chris Love 00:25:23 Certain. Community service insurance policies management each inbound and outbound site visitors, proper? Ingress and egress from a pod that the community safety coverage is certain to. So you may prohibit speaking to docker.io from a pod stage, or you may prohibit docker.io speaking to the pod, or you may prohibit pod A speaking to duplicate B. You are able to do additionally all of that inside Istio or no matter service mesh of the month you choose up. I’m not a service mess professional. There are very legitimate use instances for service mesh. And there’s one superb safety use instances the place you have got all of your site visitors inside your clusters encrypted. That’s undoubtedly a use case while you’re delicate info that’s touring in between pods. In the event you’re not utilizing encrypted trans, like your software doesn’t assist encrypted transmission throughout community layers, you’re all of your community site visitors’s unencrypted. So you have got a PHB net software that makes authentication to a job engine inside your cluster and it’s password protected.
Chris Love 00:26:30 That password’s going over the wire. However you probably have Istio put in proper, that password’s now encrypted or one other service mesh after all. So it’s utilizing, that’s one of many issues, that is drop-in, proper? That’s one of many big advantages you get. I’m not a service mesh professional, I’ve different good pals which can be actually good with that stuff. There’s undoubtedly use instances, however as soon as once more, you’re sustaining or you find yourself paying for any individual to keep up a service mesh for you, which is one more software, you’re extra load in your system. The CNI supplier that’s put in, offers your community safety insurance policies. So that you’re actually not trying as a lot overhead in comparison with working a service mesh. And there’s really fairly a little bit of overhead these days. Operating service meshes nonetheless is, it’s getting quite a bit higher than it was initially and improve challenges as properly with service mesh. And also you’re working one other software Robert, proper? You get CVS in it. So attempt to restrict the variety of purposes you’re working so that you’re limiting your, the variety of entry factors you have got from a safety normal.
Robert Blumen 00:27:33 I’ll let our listeners know that we did Episode 600 on Service Mesh. Chris, now again to our dialog. You talked about that the operator wants to have the ability to entry CAPI and so it wants our again, whereas most purposes you’re working don’t want the API then would you default to the typical pod shouldn’t have any entry in any respect to the API and due to this fact shouldn’t have any credentials out there? I believe I’m simply at this level restating what you stated. Do you have got something so as to add to that?
Chris Love 00:28:06 Nicely, it’s on by default is what I’ve so as to add. And I’ve had conversations with safety of us earlier than about that, which have coded it and that look your canine provides you when it form of turns your head and goes, huh? That’s the form of look I typically have the place the service account token is mechanically mounted in order that that’s not one thing you need. Now that’s most like additionally a pod by default. We’ll use the service account for the namespace. So once more, create a service account like most Helm charts otherwise you create your individual deployments by hand could have service accounts. Such as you’ll wish to create your individual service account. So there’s actually two issues, proper? Does it have a service account token? What group and or permissions does that service account token have? And are you limiting, like even in case you mount the service account token, as an illustration, in case you don’t permit a pod to speak to the API server, you take away that path utilizing community safety coverage.
Chris Love 00:29:05 Doesn’t matter if that safety token, however yeah, don’t mount it. It’s a nasty factor in case you don’t want it. And let’s look again to operators to provide somewhat bit extra coloration to that. Sometimes operators create pods, preserve them, want to have the ability to entry pods, do different cool issues with pods. So that they require entry to the API server so as to try this. In essence, they’re making coup management calls if you wish to give it some thought in that approach. And that’s how they preserve, say you’re working cockroach database. Labored with them on their operator really, humorous sufficient.
Robert Blumen 00:29:35 We did one other whole episode. So quantity 634 about Kyverno, which is a coverage as code layer that allows you to create insurance policies for issues like each pod will need to have a non-default service account or a lot of these items that you’re recommending may very well be was a coverage. Do you all have a view about Kyverno or instruments like that and the place they’ve their place in your total safety profile?
Chris Love 00:30:04 Certain. And I assume that Kyverno is an admission controller?
Robert Blumen 00:30:08 So you have got a coverage as code, which is only a textual content file and it goes in a config map and integrates with the controllers to implement the insurance policies on, I imagine on each single API name.
Chris Love 00:30:22 Certain. And that’s really, so I discussed PSPs, proper? Pod Safety Insurance policies, they now have a pod safety admission controller and that’s more than likely the sample that they’re utilizing for that element as properly. Sure, I do suggest that as a result of as an illustration, you, I by no means suggest working a docker picture out of Docker hub, proper? You wish to, in case you’re a sufficiently big firm, you need to have the ability to display the Bash picture that you want to run inside your system. So what admission controller can say is, you want your individual distinctive service account for this deployment. It’s worthwhile to use the distinctive service account for this namespace. You can’t launch a pod that incorporates a picture from docker.io with out an admission controller. Prefer it’s form of two methods, proper? You have to be screening your YAML earlier than it’s put in in Kubernetes after which you ought to be screening your YAML as soon as it’s working in Kubernetes. As a result of any individual can are available, unhealthy actor can are available, get coup management, entry, edit the YAML on a deployment after which it fires up their very own picture.
Chris Love 00:31:31 Nicely, in case your community coverage doesn’t can help you obtain a picture apart from a picture inside your system from ECR or Docker no matter docker registry of the month you’re utilizing or container registry, then you definately forestall these items. However once more, a mission controller is actually good. It’s a number of maturity although. I’ve labored with a number of a bigger corporations that don’t have safety and mission controllers. I’d say that’s in all probability one of the vital mature, like in case you’re folks which can be crawling, strolling or working, that’s undoubtedly with the folks which can be working with safety, they’re working their mission controllers. The pod safety and mission controller now could be a part of Kubernetes. And that, it goes again to the assertion you’ve made. What have they tried to make less complicated? It provides you three inventory out of the field profiles you would run along with your workloads that enforces a majority of these issues that you just talked about, Robert. So, and I’m certain the instrument that you just talked about earlier as properly offers some out of the field configurations and a few finest practices. Once more, it goes again to leveraging of us that know what they’re doing. I’m not going to jot down my very own container screener, I’m going to make use of any individual else’s, whether or not it’s open-source or closed supply I’ve received sufficient happening in my life. Most engineers received sufficient happening their life. We don’t wish to preserve some one-off superior instrument.
Robert Blumen 00:32:48 Do you have got any tales come to thoughts of a community safety concern that you just both debugged or discovered doing an audit of any individual else’s system?
Chris Love 00:32:59 Oh no, this occurred to certainly one of our techniques. One a consumer that I used to be working with, and this goes again to admission controllers, which is don’t permit exterior companies to be launched if it doesn’t should be launched. Proper? Solely route your site visitors by way of ingress. An engineer and he was one of many DevOps engineers for some motive launched a Juniper pod, Juniper Networks, large information science stuff, proper? Launched a type of, a deployment, had it on an exterior IP deal with. I believe half-hour later a Bitcoin miner was put in on it as a result of individuals are screening, are going by way of IP addresses on the Cloud supplier that we’re on. They search for, okay, that is Juniper pocket book, proper? They hit the trail the place you get the login display, then they are saying, okay, I’m going to attempt these 15 exploits on the 15 completely different variations. We had one of many variations that had an exploit in it.
Chris Love 00:33:54 half-hour later we had Bitcoin miners put in. Yeah, our CPU utilization went up just a bit bit. So once more, like how might which were averted? One, use a mission controller or community safety insurance policies the place a pod can not obtain software program, proper? In the event you don’t permit a pod to speak to exterior networks, why ought to a pod have the ability to discuss to Docker hub? Why ought to a pod have the ability to discuss to Google? Why ought to a pod have the ability to discuss to XYZ FTP website? Shouldn’t. So in case you don’t permit that site visitors, in case you don’t permit a pod to start out up with a picture that may be a international picture, pod received’t even begin, proper? So that you received’t run into that downside in case you don’t have a set of base photographs that you just’re continually screening for. In different phrases, you may solely run firm ACME’s Python picture while you’re working a Python software. In the event you permit any Python picture, you’re going to get CVEs in in-house. And it’s actually tempting to do this. It’s actually tempting to go to docker hub and obtain, use Python slim 312. Nice product by the way in which. I’m not knocking them in any respect, however I do know as an illustration it received’t cross CV screening.
Robert Blumen 00:35:06 Love that story, Chris. Let’s transfer on to the following layer within the stack, which we inserted in the midst of the present, secrets and techniques. What are your details throughout the secrets and techniques safety and what’s gotten higher in that space?
Chris Love 00:35:20 So again within the day, secrets and techniques weren’t secrets and techniques and so they’re nonetheless not, in case you use default secrets and techniques, it’s base 64 encoded or base I overlook precisely which encoding they use on it. Nevertheless it’s plain textual content. However now most Cloud suppliers and a few of us inside on-prem can help you mount a, so you have got a Cloud supplier secret. Kubernetes means that you can mount that secret as a quantity. So that you’re on the working system, it’s really a mount level in your container. And that’s how the key is both injected or turns into a file retailer. It’s sometimes a file stage secret which you could then entry along with your software. That’s in all probability the slickest and it’s certainly one of, it’s the identical sort of spec the place we now have completely different, like CSI CNI, all of the completely different file suppliers. Nicely now we now have a container file supplier reference. Like I stated, Amazon offers it, Google offers it, I’m certain Azure offers it as properly.
Chris Love 00:36:20 So all the large suppliers are utilizing that sample now. And nonetheless your secrets and techniques unclear textual content, you crack into the pod stage, you’ll have entry to it, proper? However pod duplicate A can not discuss to secret C that it shouldn’t be speaking to and entry it, proper? You’re not capable of begin a pod and mount any secret now. It’s this pod has to have this profile and have the ability to entry this secret. And it goes again to pod id throughout the Cloud. So as an illustration, say your pod is accessing the Cloud elements, proper? Usually CI must obtain photographs, it must push photographs into registries. So once more, it goes again to secrets and techniques administration. You don’t wish to put a Cloud stage admin. I can push into ECR password and a daily password. You wish to use pod id administration, which binds a Cloud function to a pod itself.
Chris Love 00:37:23 You then authenticate with that pod function. So it’s a few various things. It’s worthwhile to have your GitHub token or your token for XYZ SaaS that your software talks to. You set that into your Cloud supplier secret, you may then simply roll it. There are classes, it may be refreshed. You then put it in by way of a file system mounted secret in addition to you probably have, you’re accessing your native Cloud supplier. You wish to use a rule on the pod and authenticate in that method relatively than accessing a secret out of a plain textual content secret. All people is utilizing encryption at REST. So inside etcd and inside management airplane, all of the secrets and techniques at the moment are encrypted. Particularly in case you’re utilizing which what I like to recommend is the Cloud suppliers sustaining your management airplane. You’re not working etcd your self. That’s the large gotcha, I’m glad that improved. However, with the enhancements it grew to become somewhat bit trickier and getting pod stage identities working accurately is it’s somewhat bit extra enjoyable. So that you not solely have to know Kubernetes, it’s form of like wiring, it’s Russian doll, proper? You’ve received one egg that should match inside one other egg that should match inside one other egg. Then you have got your secret mounted accurately.
Robert Blumen 00:38:40 Yeah, that rush into all issues, that’s completely how I really feel about Kubernetes. Now, this final level, I needed to undergo it as a result of it’s somewhat bit sophisticated to verify I received all of the items. Say I’m attempting to entry a service by way of the Cloud supplier, which is perhaps for instance ECR. There could also be an choice to have password authentication and you would put the password in a secret and mount it onto the pod. What you’re saying is don’t try this. Create an id throughout the Cloud service supplier and assign it a task that has a coverage that granted entry to ECR after which bind that id to your pod. So it’s occurring. Now there’s nonetheless some token, but it surely’s outdoors of the pod. So any individual will get into the pod, they will’t actually simply get the credential. Did I get that proper?
Chris Love 00:39:26 You bought most of it proper? Okay, so let’s go there. It’s really not, it nonetheless is a token throughout the pod, but it surely’s a task that exists in your Cloud supplier. You don’t have the username and password within a secret. It’s not clear textual content, proper? There’s a token that’s mounted once more contained in the pod and that’s the place your credentials exist and that’s managed by your Cloud supplier. So that you don’t have to fret about 15 completely different factors accessing that very same password. Pod A has service account A, that service account has an annotation on it that features the function binding as a result of that exists. And since there’s an operator or a controller that runs inside your Cloud occasion of EKS say, it realizes okay, this annotation exists on this service account. This service account exists to this pod. I mount this token, this AWS authentication token throughout the pod when it begins, now you can use AWS CLI and you’ve got the function.
Chris Love 00:40:29 So I create FU function in AIM, I give it this grant, which is checklist ECR photographs on this repo, on this account solely. I then have advantageous inexperienced management over the place it’s speaking. It’s the identical factor, proper? I’ve to keep up these IM roles someplace, however now it really exists. The supply of fact is the Cloud relatively than the supply of fact being it’s a Cloud. Oh yeah, I received to have a password too that I received to go change. For example. You may mechanically set it up that it has to roll, like it should reset itself. You don’t must undergo and reset stuff.
Robert Blumen 00:41:06 Certain, we want credentials to be short-lived. Does this imply all of us should be coding our companies or utilizing libraries which both get some form of a notification if a secret adjustments beneath and refresh or reread it from the file system each couple of minutes to make sure that we’re all the time utilizing the newest?
Chris Love 00:41:29 And that’s the DNS controller that runs with, really, it’s not the DNS controller. I overlook which one it’s. Nevertheless it has a config map mounted to it and it intentionally refreshes that config map. In order that’s the kind of sample that you just’re speaking about the place, hey, did my meta to get information get up to date? Sure. However the factor is with most Cloud libraries, not less than they try this refresh mechanically, proper? In the event you’re utilizing an internet token in AWS with their API, they perceive it refreshes. However sure, it’s a brief lived token. It’s session primarily based. There’s a period on it. So sure, you do must refresh it, however once more, I’ve even seen libraries that permit authentication from a database right into a Cloud database that uniquely binds into the pod id. So sure, you have got to pay attention to it as a Cloud native software engineer, this is identical sort of factor that it’s a must to take into consideration as the truth that you’ve received to know you’re going to restart. You’re going to go away your server inside 60 seconds. That’s the kind of software that you just wish to design. You wish to be pretty stateless. And it goes again to that. In the event you’re utilizing a, you’re working an extended job for CI. You’ve received 60-minute job, you’re session token is for half-hour, guess what? Midway by way of you higher test to verify your session token is energetic earlier than you attempt once more, proper?
Robert Blumen 00:42:55 Completely. The final main space, we’re going to hit presumably two areas, container and pod safety. Is that one or two distinct subjects, Chris?
Chris Love 00:43:04 There actually two completely different distinct subjects. Pod safety, and we’ve already been overlaying a little bit of pod safety since you introduced up the service account token. We talked about RBAC. That’s immediately built-in into whether or not you run a stateful set, a deployment, a job, a pod, whether or not you’re mounting that. And we talked about pod safety once we’re speaking about selecting which community the pod runs on high of. That’s one other one more configuration, whether or not it’s a bunch community or pod community, it’s in really in a deployment or a pod YAML. So we’ve already been speaking a couple of bunch of that. What we haven’t talked about are specialised pods. Some pods you need to have the ability to run. For example, system stage Linux instructions. In the event you’re putting in Nvidia drivers with XYZ pod, that pod goes to must have run the host community.
Chris Love 00:43:53 It’s additionally going to must have particular capabilities by way of your container engine that you just’re working. Doc run C no matter you’re working to run your photographs. You really outline these Unix stage permissions throughout the pod. Additionally you may take a look at stuff like SE Linux and you’ll take a look at App Armor. All of that may be derived by way of the newer pod safety emission controller. So now that form of stuff, you wish to discuss once more, folks which can be crawling, strolling, working, that’s like sprinting, proper? I do know only a few folks, not less than I’ve run into only a few folks which can be working app armor profiles as an illustration. But when you realize that your workloads are going to be attacked, your Nginx servers are going to be attacked on a reasonably robust foundation. Won’t be a nasty thought to lookup how one can run App Armor for Nginx. That approach your workload is remoted higher.
Robert Blumen 00:44:48 I some studying on this space, which mentioned a way the place pods are granted briefly the flexibility to carry out operations at route stage and even then solely to a subset of system calls? May you go into extra what’s that about and how one can use it?
Chris Love 00:45:05 In order that’s really simply low-level Linux stuff. It’s been round ceaselessly. What you’re speaking about now could be we’re granting, so at a Linux kernel stage, a course of is you introduced up route, proper? It is best to by no means run your pod as route. So inside, and that’s one other configuration inside Kubernetes is whether or not you run your course of inside your container as which person. It is best to all the time use a special person. In the event you run as route, you additionally wish to see what permissions, like generally I’ve recognized controllers that restart nodes. Sort of loopy, however there’s use instances for it, proper? Again within the day, I do know of us over Comcast have been mounting two completely different video playing cards to a node and it will require restart at instances. As a result of that is really a bodily video card. After they’re streaming and encrypting motion pictures, you’d be speaking to an precise video card that might be streaming you that film.
Chris Love 00:46:03 I’m certain it’s modified a bit through the years. However, restarting, there are use instances. That’s really one of many Linux stage permissions, whether or not you have got permission to restart Linux. So once more, you’re in a position to do this advantageous grain sort specification inside a pod on what sort of permissions it has. And it goes again to don’t run as route inside a container, however that’s each pod configurations in addition to container configurations. So don’t and there’s lots of people which can be quite a bit higher specialists than I’m relating to container stage safety as a result of that’s such a broad matter now. However there’s just a few fundamentals as properly, with container stage safety. However yeah, you’re capable of undergo, do App Armor Professional profiles, SE Linux profiles. There’s a number of advantageous tuning you are able to do to isolate your workloads and specify the workloads which can be given. Elevated permissions are managed with solely the elevated permissions they want.
Robert Blumen 00:47:02 Within the brief quantity that we now have left. I’d love to do a pair fast hits on container safety. We did already focus on some points round containers, reminiscent of whether or not they comprise recognized vulnerabilities, the place you get them from, who can pull them down. One different concern I had in my define is the thought of container escape into the host. How large of an issue is that and what are you able to do about it?
Chris Love 00:47:27 Don’t run a bunch community. So in case you’re not on the host community, the aptitude to flee to the host reduces tremendously due to how the networking and the virtualization nearly quasi virtualization works. The routing isn’t there. In order that’s it. Additionally, there’s some container techniques present the aptitude of isolating the workloads in addition to you probably have workloads. You may isolate workloads to run on particular nodes. So in case you do get to the host, you don’t like, say you have got workload A that can’t discuss to workload B, proper? It simply can’t occur, proper? So don’t put workload A on the identical nodes that workload B is on. Fairly easy. I knew of a financial institution that each software had its personal Kubernetes cluster. Actually attention-grabbing sample. Not a nasty factor. If you want to isolate your workloads at such a low stage, then presumably take a look at that.
Chris Love 00:48:21 There’s additionally Kubernetes virtualization inside Kubernetes now, the place you may run a Kubernetes cluster within Kubernetes, as a result of that’s multi-homing. However I’ve digressed. Let’s return to picture stage safety and container safety improve. Have the aptitude the place you run CI and CD typically, have a set of base photographs in case your store works in Python, works in Go, works in Java, have base photographs in your builders. Have your golden Java picture. Have your golden Python picture. Have these screened frequently. Have these upgraded frequently. It’s actually necessary. Folks, I am going into giant corporations and individuals are nonetheless not screening their photographs. They display their working techniques. So goodness gracious, their nodes are being screened, however Bash within a picture isn’t being screened. Additionally, don’t set up Bash in case you don’t want it. Don’t set up, who’s in case you don’t want it, proper?
Chris Love 00:49:17 For example, Golang is without doubt one of the neat languages the place you may compile and have it run on nearly nothing. The much less binaries which can be in a picture use it. Use multilayer photographs in your builds, proper? So you have got a construct picture the place you have got your libraries that your shared construct libraries that you just want for Python dependencies. However within the subsequent picture that you just’re really deploying into manufacturing and utilizing, don’t have these libraries in it. Don’t have Git put in, don’t have Curl put in, don’t have W Git put in. Simply don’t, proper? However generally you have got photographs CI’s in all probability the worst, proper? As a result of CI photographs have to, as an illustration, discuss to GitHub. They should do XYZ. They should do all these various things. So be rigorous about sustaining your individual photographs and upgrades. Don’t run photographs as route, as we talked about.
Chris Love 00:50:09 Don’t permit your photographs to do quite a bit. It ought to be run software. That’s it. In the event you run Python 312 when you have got time and just be sure you have a backlog to improve to Python 313. There’s a motive that you just wish to preserve upgrading. Even have it easy as doable to redeploy your whole stack. It’s good for DR but it surely’s additionally good when there’s an enormous bug that comes out that enables to do distant execution and also you run that library in all places. Log4J involves thoughts. You’ve received to have the ability to push a button and as shortly as doable, redeploy your whole stack. Kubernetes is actually good for permitting to you to do this, don’t get me fallacious. Nevertheless it’s nonetheless all the way down to different ideas, which is your CI and CD system. Make it possible for that’s tuned in so you are able to do it. And the way in which you get to do this extra typically is, is upgrading typically, proper? So in case you’re upgrading repeatedly you realize you may redeploy your workloads repeatedly as properly.
Robert Blumen 00:51:10 We’ve hit on some fairly large mountains within the panorama of Kubernetes safety, Chris. Within the time that we now have left to wrap up, is there any parting phrases you’d just like the listeners to have of high three issues to consider in securing your Kubernetes cluster?
Chris Love 00:51:26 Upgrades, defend your management airplane and step again and ensure such as you do what you may while you set your cluster initially, these are in all probability the three issues. Improve your nodes, preserve updated. I’ve walked into environments the place they’re working a management airplane that isn’t even supported anymore. It’s so previous. It’s over a yr previous and gosh, that’s not that previous, proper? However over a year-old Kubernetes is, won’t be supported anymore relying on what model you rolled out at the moment. Improve your Python, improve. In the event you received Bash in your picture, improve it. And in addition to and we actually haven’t talked about this, however there’s different techniques the place you’ve received Apple stage safety, you bought to be involved about. You’ve received Kubernetes stage safety, you’ve received intrusion detection. All of that issues in case you’re on the sort, at a stage of group the place you’ve received the time, staffing, and cash to do this sort of labor.
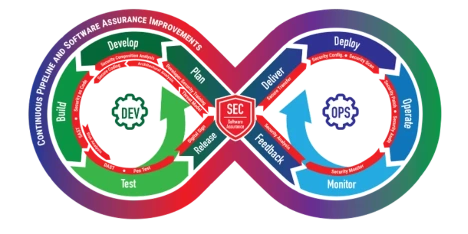
Chris Love 00:52:21 It’s a reasonably broad matter. And leverage specialists, proper? There’s a motive I run Kubernetes. It’s written by folks which can be quite a bit smarter than me and I notice that I’m not the one which’s going to go write the newest AI instrument. As a result of that’s simply not my experience. I am going again to, I’m a constructing form of a building engineer for computer systems. I’ll construct a cool place that cool purposes can run on high of. However so as to try this, I’ve received to have some groundwork. I’ve received to have some base layers. I’ve received to have some base techniques that’ll assist me. And it form of goes again to a DevSecOps or DevOps precept the place we would have liked to automate stuff. It retains me out of hassle.
Robert Blumen 00:52:58 The place can listeners discover your ebook, Core Kubernetes ?
Chris Love 00:53:01 It’s out there on the Manning’s web site. Simply go to Manning.com and sort in Core Kubernetes. Actually wish to thank Jay for dragging me in to jot down a ebook. It was fairly an expertise. It might take quite a bit for me to jot down one other ebook, in addition to, they will discover me on Chris Love, CNM on all of the completely different socials.
Robert Blumen 00:53:20 Another place on the web you’d wish to level folks to?
Chris Love 00:53:23 Certain. Fantastic firm I work for, which is Modernize.io. Love working there. It’s been an actual blessing. We’re a consulting firm. Consider us as a boutique model of Deloitte, as you’ll say. And glad, actually glad to affix you right here at present, Robert. Admire the time that and the good questions you’ve requested me at present.
Robert Blumen 00:53:44 Thanks, Chris. It’s been a pleasure. Thanks for chatting with Software program Engineering Radio and for Software program Engineering Radio, this has been Robert Blumen. Thanks for listening. [End of Audio]