Google fixes ninth Chrome zero-day exploited in assaults this 12 months

Right now, Google launched a brand new Chrome emergency safety replace to patch a zero-day vulnerability tagged as exploited assaults.
“Google is conscious that an exploit for CVE-2024-7971 exists within the wild,” the corporate stated in an advisory printed on Wednesday.
This high-severity zero-day vulnerability is attributable to a sort confusion weak point in Chrome’s V8 JavaScript engine. Safety researchers with the Microsoft Menace Intelligence Heart (MSTIC) and Microsoft Safety Response Heart (MSRC) reported it on Monday.
Though such safety flaws can generally allow attackers to set off browser crashes after knowledge allotted into reminiscence is interpreted as a distinct sort, they will additionally exploit them for arbitrary code execution on focused units working unpatched browsers.
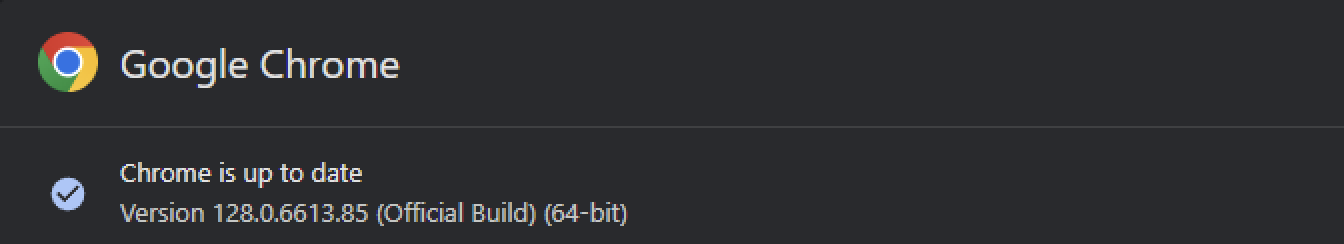
Google has fastened the zero-day with the discharge of 128.0.6613.84/.85 for Home windows/macOS and 128.0.6613.84 (Linux), variations that can roll out to all customers within the Secure Desktop channel over the approaching weeks.
Whereas Chrome updates routinely when safety patches can be found, customers can even velocity up the method by going to the Chrome menu > Assist > About Google Chrome, letting the replace end, and clicking the ‘Relaunch’ button to put in it.
Right now’s replace was instantly out there when BleepingComputer regarded for brand spanking new updates at present.
Regardless that Google confirmed the CVE-2024-7971 vulnerability was utilized in assaults, the corporate has but to share further data concerning in-the-wild exploitation.
“Entry to bug particulars and hyperlinks could also be saved restricted till a majority of customers are up to date with a repair,” Google stated.
“We may also retain restrictions if the bug exists in a 3rd occasion library that different tasks equally rely upon, however have not but fastened.”
CVE-2024-7971 is the ninth actively exploited Chrome zero-day patched by Google in 2024, with the entire record of zero-days fastened this 12 months together with:
- CVE-2024-0519: A high-severity out-of-bounds reminiscence entry weak point inside the Chrome V8 JavaScript engine, permitting distant attackers to take advantage of heap corruption through a specifically crafted HTML web page, resulting in unauthorized entry to delicate data.
- CVE-2024-2887: A high-severity sort confusion flaw within the WebAssembly (Wasm) commonplace. It might result in distant code execution (RCE) exploits leveraging a crafted HTML web page.
- CVE-2024-2886: A use-after-free vulnerability within the WebCodecs API utilized by net purposes to encode and decode audio and video. Distant attackers exploited it to carry out arbitrary reads and writes through crafted HTML pages, resulting in distant code execution.
- CVE-2024-3159: A high-severity vulnerability attributable to an out-of-bounds learn within the Chrome V8 JavaScript engine. Distant attackers exploited this flaw utilizing specifically crafted HTML pages to entry knowledge past the allotted reminiscence buffer, leading to heap corruption that might be leveraged to extract delicate data.
- CVE-2024-4671: A high-severity use-after-free flaw within the Visuals element that handles the rendering and displaying of content material within the browser.
- CVE-2024-4761: An out-of-bounds write downside in Chrome’s V8 JavaScript engine, which is accountable for executing JS code within the software.
- CVE-2024-4947: Kind confusion weak point within the Chrome V8 JavaScript engine enabling arbitrary code execution on the goal system.
- CVE-2024-5274: A sort confusion Chrome’s V8 JavaScript engine that may result in crashes, knowledge corruption, or arbitrary code execution
macos – Twin-Boot MacBook Professional 2015 caught loading into GNU GRUB model 2.04
In the event you used the Disk Utility or diskutil command to take away a Linux partition, then there’s a pretty good probability the sort for the partition containing macOS was modified to FFFFFFFF-FFFF-FFFF-FFFF-FFFFFFFFFFFF. Apparently, you didn’t take away the Ubuntu boot (GRUB) information from the EFI partition. Once you boot your Mac, the firmware will solely detect these Ubuntu boot information which is why your Mac is booting to GRUB. Because the partition containing macOS is the improper sort, you’ll not be allowed as well to common macOS Restoration. Booting to Web Restoration shouldn’t be the one option to appropriate the partition sort. For instance, you may make a bootable Ubuntu Dwell flash drive. After booting from the flash drive, you should utilize the gdisk command to appropriate sort partition sort. Notice that gdisk makes use of codes to characterize sort partition sort GUIDs. In your case, you will have the code for APFS which is AF0A. Or, you’ll be able to enter the precise APFS GUID of 7C3457EF-0000-11AA-AA11-00306543ECAC.
Tips on how to Use the gdisk Command
-
Enter the
lsblkcommand. From the output, decide the title of the interior drive the place Ubuntu is put in. This often can be bothsdaornvme0n1. Right here I’ll assumenvme0n1. -
Enter the next command. In case your title from from the earlier step is completely different from
nvme0n1, then make the suitable substitution.sudo gdisk /dev/nvme0n1 -
The
gdiskcommand is interactive. Enter the values proven within the first column of the desk.Entry Kind Remark pcommand Print the partition desk tcommand Change a partition’s sort code 2parameter Partition quantity (In case your partition quantity is completely different, then make the suitable substitution.) af0aparameter Hex code wcommand Write desk to disk and exit yparameter Affirm to proceed
Don’t get Mad, get smart – Sophos Information
The Sophos X-Ops Incident Response staff has been inspecting the ways of a ransomware group referred to as Mad Liberator. This can be a pretty new menace actor, first rising in mid-July 2024. On this article, we’ll take a look at sure methods the group is utilizing, involving the favored remote-access utility Anydesk. We’ll doc the attention-grabbing social-engineering ways the group has used and supply steerage each as to methods to reduce your danger of turning into a sufferer and, for investigators, to methods to see potential exercise by this group.
Earlier than we begin, we should always be aware that Anydesk is reputable software program that the attackers are abusing on this scenario. The attackers misuse that utility within the method we’ll present beneath, however presumably any distant entry program would go well with their functions. Additionally, we’ll be aware up entrance that SophosLabs has a detection in place, Troj/FakeUpd-Okay, for the binary described.
What’s Mad Liberator?
The exercise that Sophos X-Ops has noticed up to now signifies that Mad Liberator focuses on information exfiltration; in our personal expertise, we now have not but seen any incidents of knowledge encryption traceable to Mad Liberator. That stated, data on watchguard.com does counsel that the group makes use of encryption sometimes, and in addition undertakes double extortion (stealing information, then encrypting the sufferer’s methods and threatening to launch the stolen information if the sufferer doesn’t pay to decrypt).
Typical of menace actors who carry out information exfiltration, Mad Liberator operates a leak web site on which it publishes sufferer particulars, in an effort to place extra strain on victims to pay. The positioning claims that the recordsdata will be downloaded “free of charge.”
Determine 1: Mad Liberator’s disclosure web site
Apparently, Mad Liberator makes use of social engineering methods to acquire setting entry, focusing on victims who use distant entry instruments put in on endpoints and servers. Anydesk, as an illustration, is popularly utilized by IT groups to handle their environments, notably when working with distant customers or units.
How the assault works
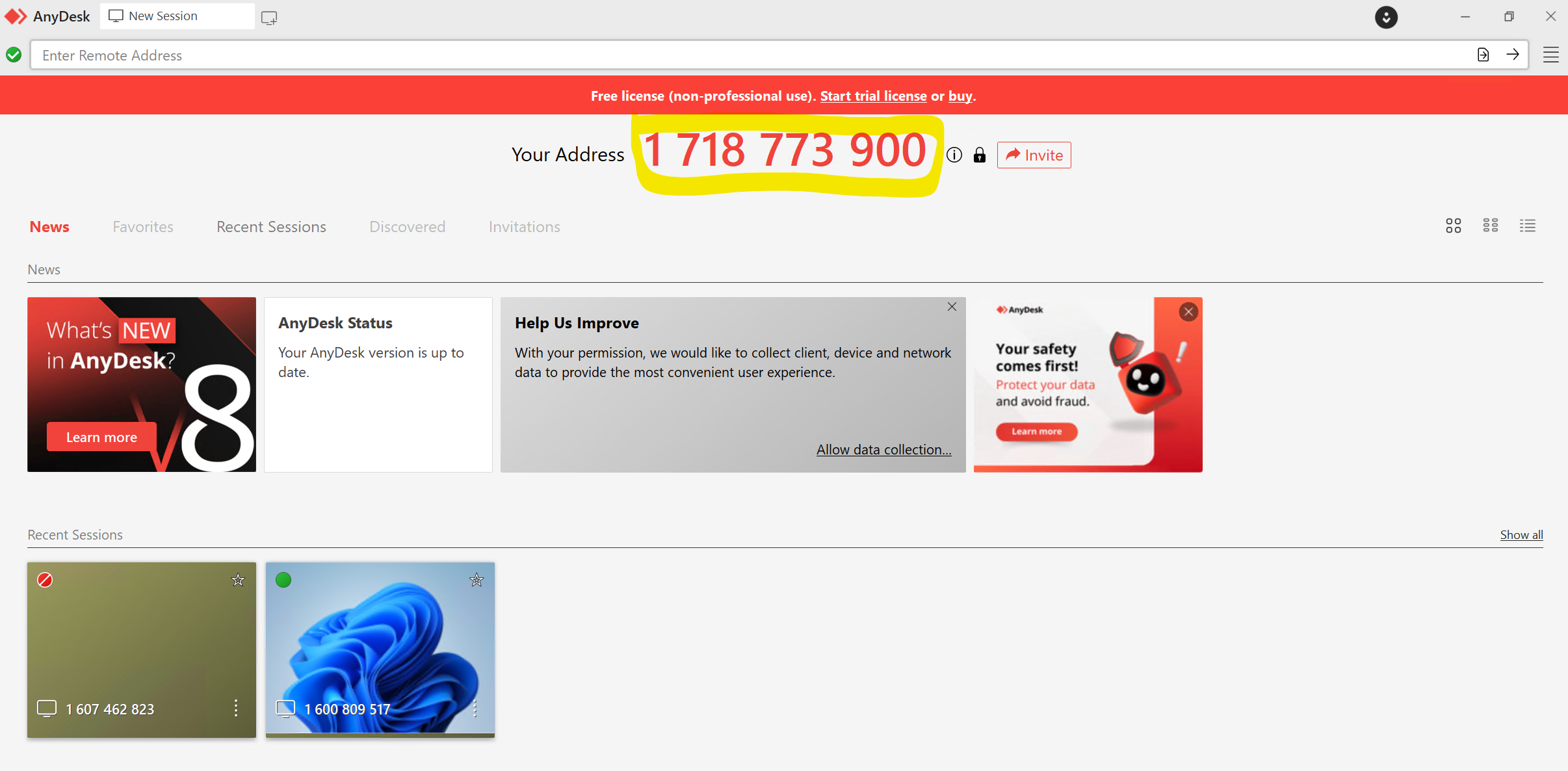
Anydesk works by allocating a singular ID, on this a case a ten-digit deal with, to every machine it’s put in on. As soon as the appliance is put in on a tool, a person can both request to entry a distant machine to take management by coming into the ID, or a person can invite one other person to take management of their machine through a distant session.
Determine 2: An Anydesk session with the ten-digit deal with prominently displayed
We don’t know at this level how, or if, the attacker targets a specific Anydesk ID. In concept it’s attainable to only cycle via potential addresses till somebody accepts a connection request; nevertheless, with probably 10 billion 10-digit numbers, this appears considerably inefficient. In an occasion that the Incident Response staff investigated, we discovered no indications of any contact between the Mad Liberator attacker and the sufferer previous to the sufferer receiving an unsolicited Anydesk connection request. The person was not a distinguished or publicly seen member of workers and there was no identifiable cause for them to be particularly focused.
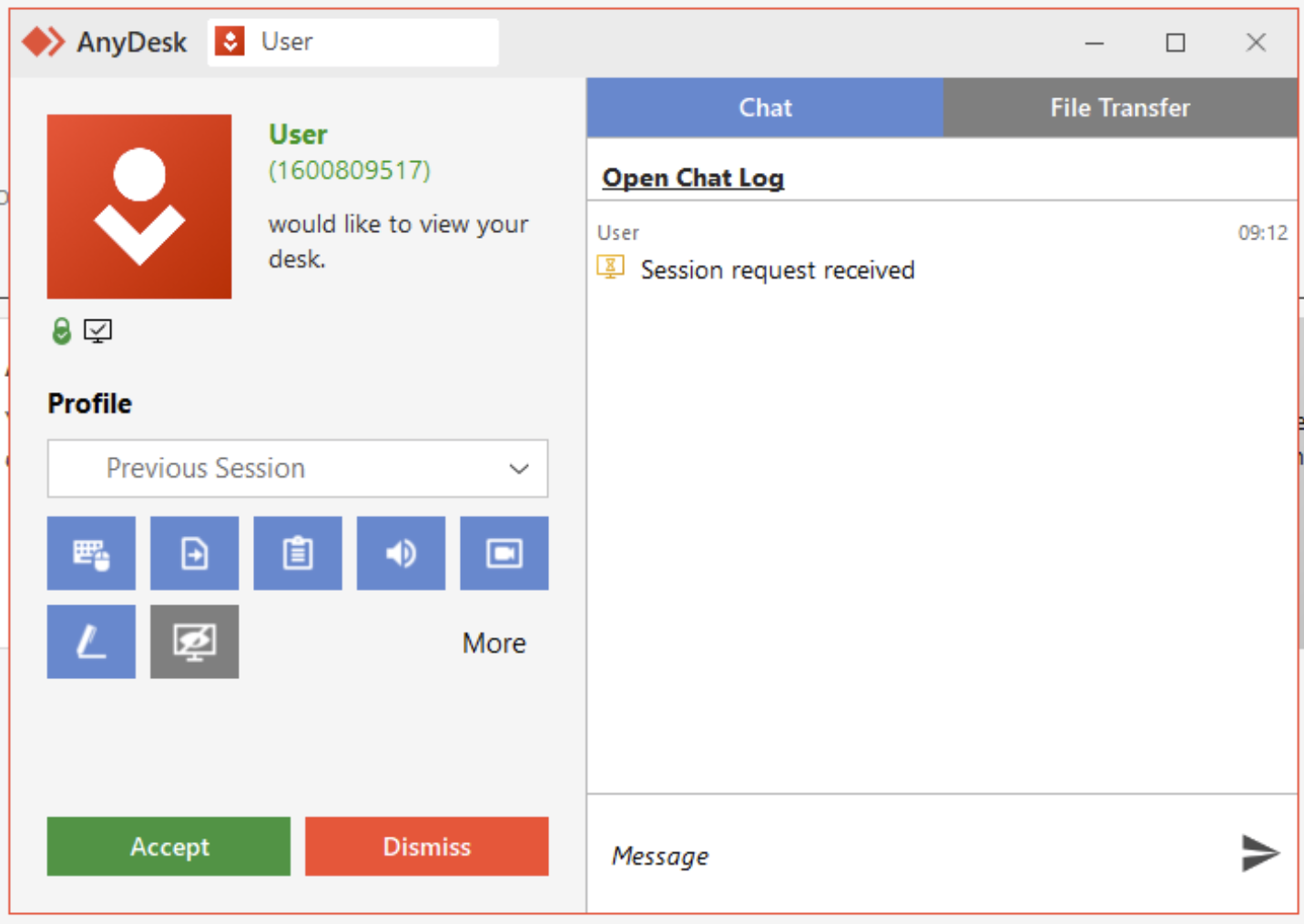
When an Anydesk connection request is acquired, the person sees the pop-up proven in Determine 3. The person should authorize the connection earlier than it may be absolutely established.
Determine 3: A request from “Person” to attach through Anydesk; as Anydesk admins know however finish customers might not, anybody can select any username when establishing Anydesk, so an attacker might even name itself “Tech Assist” or one thing comparable
Within the case our IR staff dealt with, the sufferer was conscious that Anydesk was utilized by their firm’s IT division. They subsequently assumed that the incoming connection request was only a normal occasion of the IT division performing upkeep, and so clicked Settle for.
As soon as the connection was established, the attacker transferred a binary to the sufferer’s machine and executed it. In our investigations this file has been titled “Microsoft Home windows Replace,” with the SHA256 hash:
f4b9207ab2ea98774819892f11b412cb63f4e7fb4008ca9f9a59abc2440056fe
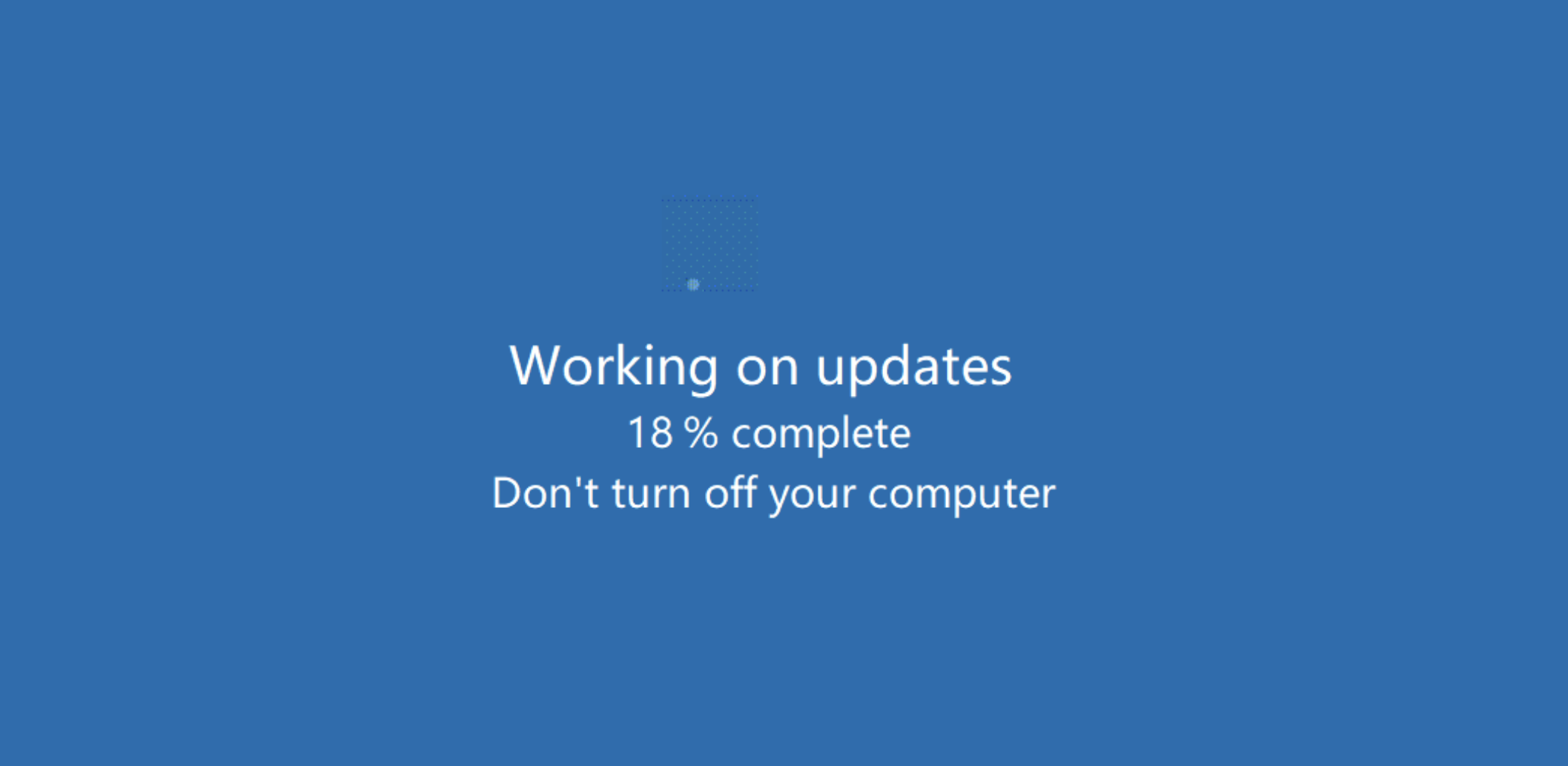
This binary was a quite simple program that displayed a splash display mimicking a Home windows Replace display. The display was animated, making it seem that the system was updating, as proven in Determine 4.
Determine 4: An all-too-unremarkable Home windows Replace display… or is it?
This program didn’t carry out another exercise, which made it unlikely to be instantly detected as malicious by most antimalware packages. (Sophos has developed a detection [Troj/FakeUpd-K] for this specific binary and can proceed to watch developments on this.)
At this level, to guard the ruse from being found and stopped, the attacker took an additional step. Since this easy program might have been exited ought to the person occur to press the “Esc” key, the attacker utilized a function inside Anydesk to disable enter from the person’s keyboard and mouse.
Because the sufferer was not ready to make use of their keyboard, and because the above display seemed to be one thing unremarkable to any Home windows person, they had been unaware of the exercise that the attacker was performing within the background – and couldn’t have stopped it simply even when they had been suspicious.
The attacker proceeded to entry the sufferer’s OneDrive account, which was linked to the machine, in addition to recordsdata that had been saved on a central server and accessible through a mapped community share. Utilizing the Anydesk FileTransfer facility, the attacker stole and exfiltrated these firm recordsdata. The attacker then used Superior IP Scanner to find out if there have been different units of curiosity that might be exploited throughout the identical subnet. (They didn’t, in the long run, laterally transfer to another units.)
As soon as the stolen recordsdata had been beneath its management, the attacker then ran one other program that created quite a few ransom notes. Apparently, these ransom notes had been generated in a number of places on a shared community location which was mapped to the machine, slightly than on the sufferer’s machine itself. These ransom notes introduced that information had been stolen and offered particulars as to how the sufferer ought to pay the ransom to forestall disclosure of these stolen recordsdata. (Techniques corresponding to these will probably be all too acquainted to readers of our investigation of strain ways presently in use by ransomware gangs.)
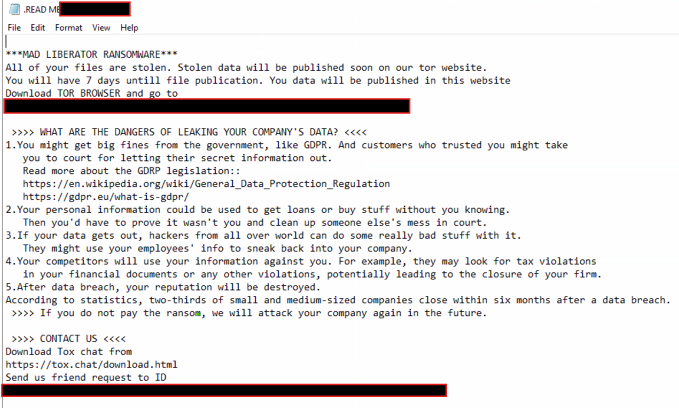 Determine 5: The ransom be aware acquired by the sufferer; be aware the threats of reputational and regulatory harm, and be aware additionally that no ransom quantity is cited
Determine 5: The ransom be aware acquired by the sufferer; be aware the threats of reputational and regulatory harm, and be aware additionally that no ransom quantity is cited
The pretend Home windows Replace display shielded the attacker’s actions from being seen on the sufferer’s display. The assault lasted nearly 4 hours, on the conclusion of which the attacker terminated the pretend replace display and ended the Anydesk session, giving management of the machine again to the sufferer. We did be aware that the binary was manually triggered by the attacker; with no scheduled process or automation in place to execute it once more as soon as the menace actor was gone, the file merely remained on the affected system.
Classes and mitigations
This was an easy assault that relied on the sufferer believing that the Anydesk request was a part of day-to-day exercise. So far as our investigators might decide, the assault didn’t contain any extra social engineering efforts by the attacker — no electronic mail contact, no phishing makes an attempt, and so forth. As such it highlights the significance of ongoing, up-to-date workers coaching, and it signifies that organizations ought to set and make identified a transparent coverage relating to how IT departments will contact and prepare distant classes.
Past person schooling, we extremely advocate that directors implement the Anydesk Entry Management Lists to solely enable connections from particular units with a purpose to vastly reduce the danger of such a assault, AnyDesk present some very invaluable steerage and the way to do that in addition to extra safety measures within the following hyperlink:
With extra recommendation accessible right here:
Procedural notes for investigators comply with the conclusion of this text.
Conclusion
Ransomware teams rise and fall consistently, and Mad Liberator might show to be a major new participant, or simply one other flash within the pan. Nevertheless, the social-engineering ways the group used within the case described above are noteworthy – however they aren’t distinctive. Attackers will all the time proceed to develop and make use of quite a lot of ways to try to exploit each the human ingredient and the technical safety layers.
It may be a tough process to steadiness safety in opposition to usability when implementing instruments inside an setting, particularly when these instruments assist facilitate distant entry for the very folks tasked with caring for business-critical methods. Nevertheless, we all the time advocate that when purposes are deployed throughout a community, particularly ones that may be leveraged to acquire distant entry to units, that cautious overview of the safety suggestions by the seller is taken into account. The place these suggestions usually are not adopted, that alternative must be documented as a part of your danger administration course of in order that it may be regularly reviewed, or so different mitigations will be put in place to make sure it stays throughout the danger urge for food of your group.
Appendix: Investigating Mad Liberator
In case you are investigating an incident through which you believe you studied that attackers might have leveraged Anydesk, search for helpful occasion and connection information saved within the following recordsdata:
- C:ProgramDataAnyDeskconnection_trace.txt
- C:ProgramDataAnyDeskad_svc.hint
- C:UserspercentAppDataRoamingAnyDeskad.hint
The connection_trace.txt file solely incorporates the Handle ID of latest connections and might not be all that helpful by itself. However it does at the least let you slender down the offending ID.
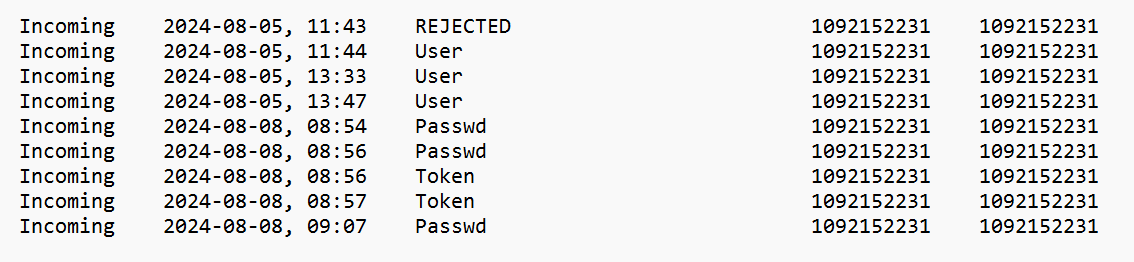
Determine 6: A take a look at connection_trace.txt, with data on the results of every occasion
There are 4 attainable states for every connection:
- REJECTED – the end-user rejected a connection request
- Person – the end-user accepted a connection request
- Passwd – password entered by the distant system to achieve entry
- Token – ‘Login Robotically’ choice checked by the distant system
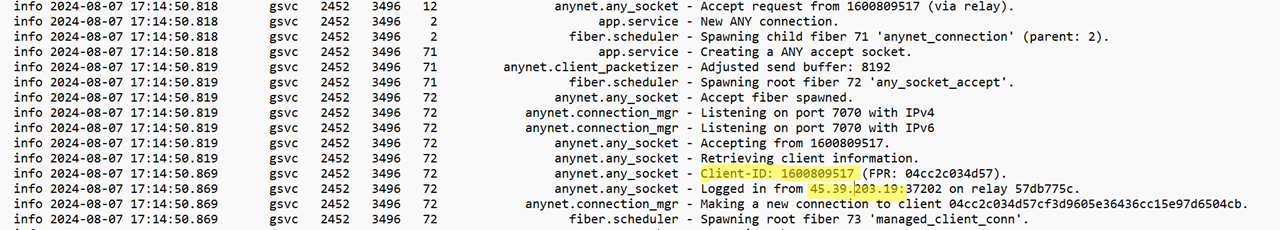
The ad_svc.hint and advert.hint recordsdata comprise various granular element. These will be opened and considered with a textual content editor corresponding to Notepad and together with different occasions additionally incorporates connection information. The ad_svc.hint file incorporates particulars of the supply IP addresses of distant connections.
Determine 7: A take a look at ad_svc.hint; a questionable connection is highlighted within the picture
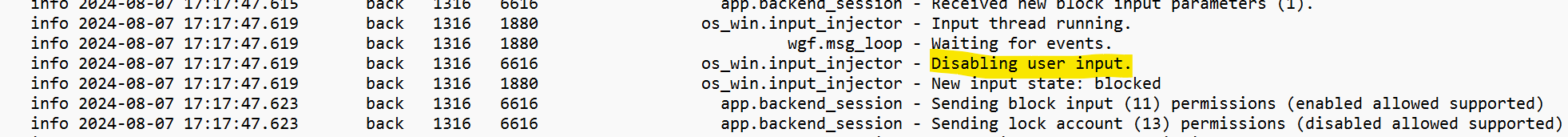
The advert.hint file incorporates logs regarding file transfers, and occasions corresponding to the place person enter is disabled.
Determine 8: The person’s enter choices are disabled
Determine 9: The file-transfer occasions
Though the logs will point out the folder and what number of recordsdata had been transferred throughout information exfiltration, sadly the logs is not going to element every file title.
When you have Sophos Intercept X put in, amassing this information is simplified. The next OSquery can be utilized inside Dwell Uncover within the Sophos Central Dashboard:
SELECT
strftime('%Y-%m-%dTpercentH:%M:%S', substr(grep.line, instr(grep.line, 'information') + 5, 19)) AS Datetime,
grep.path,
CASE
WHEN grep.sample = 'Logged in from' THEN 'Login'
WHEN grep.sample = 'Getting ready recordsdata' THEN 'File Switch from this Host'
WHEN grep.sample = 'Accepting from' THEN 'Accepted Connection Request'
WHEN grep.sample = 'Incoming session request:' THEN 'Incoming Session Request'
WHEN grep.sample = 'Distant OS:' THEN 'Distant OS'
WHEN grep.sample = 'Disabling person enter.' THEN 'Disable Mouse and Keyboard'
WHEN grep.sample = 'Obtain began' THEN 'File Switch to this Host'
WHEN grep.sample = 'Obtained a sysinfo request.' THEN 'System Data Request'
WHEN grep.sample = 'Authenticated with everlasting token' THEN 'Authenticated with Token'
WHEN grep.sample = 'Authenticated with appropriate passphrase' THEN 'Authenticated with Password'
WHEN grep.sample = 'Profile was used:' THEN 'Profile Assigned'
END AS 'Operation',
grep.line as Knowledge
FROM file
CROSS JOIN grep ON (grep.path = file.path)
WHERE
(
file.path LIKE 'C:ProgramDataAnyDeskad_svc.hint'
OR file.path LIKE 'C:UserspercentAppDataRoamingAnyDeskad.hint'
)
AND
(
--AnyDesk
grep.sample = 'Logged in from'
OR grep.sample = 'Getting ready recordsdata'
OR grep.sample = 'Accepting from'
OR grep.sample = 'Incoming session request:'
OR grep.sample = 'Distant OS:'
OR grep.sample = 'Disabling person enter.'
OR grep.sample = 'Obtain began'
OR grep.sample = 'Obtained a sysinfo request.'
OR grep.sample = 'Authenticated with everlasting token'
OR grep.sample = 'Authenticated with appropriate passphrase'
OR grep.sample = 'Profile was used:'
)
ORDER BY Datetime DESC
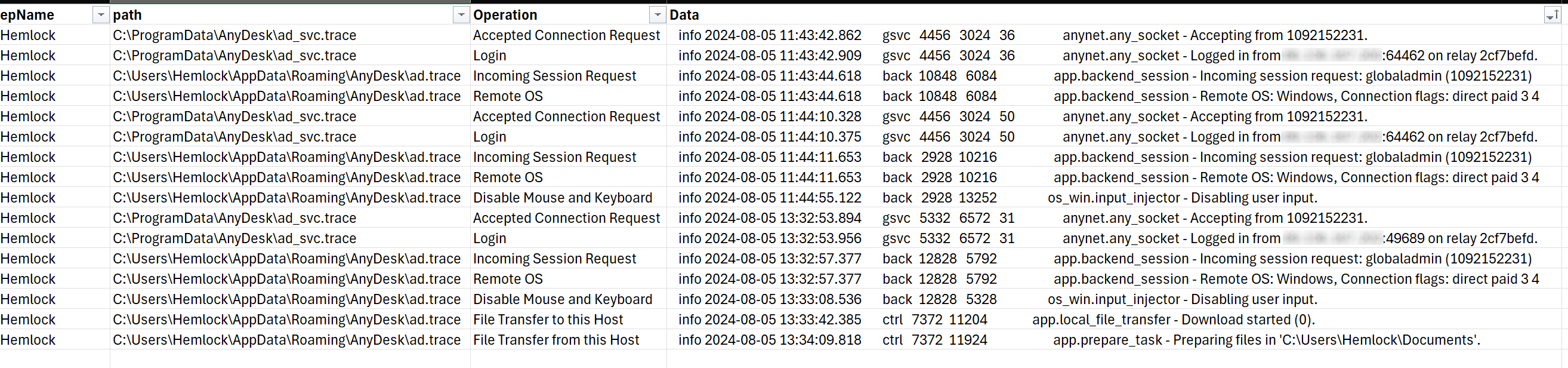
The question even helps to kind the info right into a usable desk, as seen in Determine 10.
Determine 10: The output of the OSquery proven above, in helpful tabular format
Acknowledgements
Harshal Gosalia, Ollie Jones, and Andy French contributed to this analysis.
SaaS Safety Posture—It’s not you, it’s me!
In enterprise, it’s not unusual to take a software-as-a-service (SaaS)-first method. It is smart—there’s no must take care of the infrastructure, administration, patching, and hardening. You simply activate the SaaS app and let it do its factor.
However there are some downsides to that method.
The Drawback with SaaS
Whereas SaaS has many advantages, it additionally introduces a number of latest challenges, a lot of which don’t get the protection they warrant. On the prime of the checklist of challenges is safety. So, whereas there are some very actual advantages of SaaS, it’s additionally vital to acknowledge the safety danger that comes with it. Once we speak about SaaS safety, we’re not often speaking in regards to the safety of the underlying platform, however quite how we use it.
Keep in mind, it’s not you, it’s me!
The Shared Duty Mannequin
Within the phrases and situations of most SaaS platforms is the “shared duty mannequin.” What it often says is that the SaaS vendor is answerable for offering a platform that’s strong, resilient, and dependable—however they don’t take duty for a way you employ and configure it. And it’s in these configuration modifications that the safety problem lives.
SaaS platforms typically include a number of configuration choices, akin to methods to share knowledge, methods to ask exterior customers, how customers can entry the platform, what components of the platform they will use, and so forth. And each configuration change, each nerd knob turned, is the potential to take the platform away from its optimum safety configuration or introduce an surprising functionality. Whereas some purposes, like Microsoft 365, provide steerage on safety settings, this isn’t true for all of them. Even when they do, how straightforward is that to handle whenever you get to 10, 20, and even 100 SaaS apps?
Too Many Apps
Are you aware what number of SaaS apps you could have? It’s not the SaaS apps about which are the problem, it’s those you don’t. As a result of SaaS is so accessible, it might probably simply evade administration. There are apps that folks use however a corporation will not be conscious of—just like the app the gross sales staff signed up for, that factor that advertising makes use of, and naturally, everybody needs a GenAI app to play with. However these aren’t the one ones; there are additionally the apps which are a part of the SaaS platforms you join. Sure, even those about can comprise further apps you don’t find out about. That is how a median enterprise will get to greater than 100 SaaS purposes. How do you handle every of these? How do you guarantee they exist and they’re configured in a manner that meets good safety practices and protects your data? Therein lies the problem.
Introducing SSPM
SSPM may be the reply. It’s designed to initially combine together with your managed SaaS purposes to supply visibility into how they’re configured, the place configurations current dangers, and tackle them. It would regularly monitor them for brand new threats and configuration modifications that introduce danger. It would additionally uncover unmanaged SaaS purposes which are in use, consider their posture and current danger profiles of each the appliance and the SaaS vendor itself. It centralizes the administration and safety of a SaaS infrastructure and the place its administration and configuration current danger.
Overlap with CASB and DLP
There may be some overlap out there, significantly with cloud entry safety dealer (CASB) and knowledge loss prevention (DLP) instruments. However these instruments are a bit like capturing the thief as he runs down the driveway, quite than ensuring the doorways and home windows have been secured within the first place.
SSPM is yet one more safety instrument to handle and pay for. However is it a instrument we want? Nicely, that’s as much as you; nevertheless, our use of SaaS, for all the advantages it brings, has introduced a brand new complexity and a brand new set of dangers. We have now so many extra apps than we have now ever had, a lot of them we don’t handle centrally, and so they have many configuration knobs to show. With out oversight of all of them, we do run safety dangers.
Subsequent Steps
SaaS safety posture administration (SSPM) is one other entry into the rising catalog of safety posture administration instruments. They’re typically straightforward to check out, and plenty of provide free assessments that may give you an concept of the dimensions of the problem you face. SaaS safety is difficult and sometimes doesn’t get the protection it deserves, so getting an concept of the place you stand may very well be useful.
Earlier than you end up on the mistaken finish of a safety incident and your SaaS vendor tells you it’s you, not me, it could be value seeing what an SSPM instrument can do for you. To study extra, check out GigaOm’s SSPM Key Standards and Radar experiences. These experiences present a complete overview of the market, define the factors you’ll wish to think about in a purchase order resolution, and consider how a lot of distributors carry out towards these resolution standards.
In case you’re not but a GigaOm subscriber, enroll right here.

 Evaluation of a
Evaluation of a