Breaking Down Info Silos with Atlan
The Energetic Metadata Pioneers sequence options Atlan prospects who’ve not too long ago accomplished a radical analysis of the Energetic Metadata Administration market. Paying ahead what you’ve realized to the following information chief is the true spirit of the Atlan neighborhood! So that they’re right here to share their hard-earned perspective on an evolving market, what makes up their trendy information stack, progressive use instances for metadata, and extra.
On this installment of the sequence, we meet Pranav Gandhi, Head of Information & Analytics at Signifyd, a pacesetter in eCommerce Fraud Safety expertise supporting hundreds of shops in over 100 nations. Pranav shares how an organization constructed on information science will use Atlan to interrupt down data silos, driving quick, assured decision-making for technical and enterprise customers, alike.
This interview has been edited for brevity and readability.
Might you inform us a bit about your self, your background, and what drew you to Information & Analytics?
I lead Analytics Engineering and Information Analytics at Signifyd, and have been on the firm for about 4 and a half years now.
I received began in Information & Analytics once I joined Jet.com, an eCommerce retailer that was acquired by Walmart. Once we moved to Walmart, I pivoted into pricing analytics, which aligned with my background in Economics. It fascinated me to see how information might be utilized in so some ways and totally different features.
Would you thoughts describing your information crew?
Signifyd is exclusive in that we’re a Information Science firm first. It’s our product, and isn’t a method to an finish. We earn money once we present choices. Our crew is uniquely organized, and there are lively conversations about working as a knowledge product crew.
So, we’ve a Determination Science crew, sitting in a unique a part of the group however using loads of information to assist make these choices. Our information crew is basically a part of our product group, and we deal with information as a first-class citizen inside our group, akin to a product.
My crew is made up for Analytics Engineers, who’re hands-on with information and creating fashions for others to make use of. Then there are Analysts, a few of whom are centralized and assist groups like Product, Advertising and marketing, Information Science, and Finance. We’ve already begun decentralizing some analytical features in a hub-and-spoke kind of mannequin, they usually’re already reaching the size the place their coordination with our centralized Enterprise Analysts and Analytics Engineers is working properly.
Why seek for an Energetic Metadata Administration resolution? What was lacking?
The best way our groups had been initially arrange was creating silos in how we managed our data. Root Trigger Evaluation might additionally add further complexity for our information groups, even with easy asks. We’re additionally consistently testing and releasing new merchandise, which implies the best way prospects ship us information adjustments regularly. The info crew sits far on the “proper” of all this, and a few context was typically lacking, so we must ask questions in Product and Engineering channels on Slack. That took time and put strain on our analysts, particularly those that work to make our prospects profitable.
If the client isn’t being served in an optimum means, that may be a drag on their enterprise. So, ensuring individuals had entry to the best data and understood it was paramount. We additionally realized that there have been so many siloed methods of organizing information, that it was even more durable to have a transparent method to change data throughout them.
So, we began to have a look at centralized cataloging instruments. We thought of Looker, as a result of that was the first place the place our information landed, however discovered it was too “late” within the information workflow for that data to dwell. That’s once we began to contemplate Atlan.
If you had been evaluating the market, what stood out to you? What was vital?
Within the Energetic Metadata Administration market, I feel there’s an identification disaster from loads of distributors. Are you fixing for technical customers to grasp their workflows higher, or are you fixing for enterprise customers who don’t have any clue what these ideas are?
What was robust for us is that we wished our selection to resolve as many use instances as doable, as a result of we need to be cost-efficient as a way to scale in an optimized method. We couldn’t afford to have a device that solely solves Information Engineering and Analysts’ ache factors, whereas leaving the enterprise customers in their very own silo once they’re the customers who may gain advantage essentially the most.
Once we talked to totally different distributors in the course of the analysis, the largest factor we realized was that for those who aren’t fixing for each personas, then you need to assume the enterprise consumer isn’t going to enter the device. With Atlan, there’s the Chrome Extension, so enterprise customers don’t have to fret about needing to signal into a brand new device. With the opposite approaches, you may create personas, however utilization isn’t going to be nice all the best way to the best.
For our extra technical customers, we knew they might use it. However we appreciated that Atlan had assist for non-technical customers, and it made it a lot simpler for even a Information Analyst to do enrichment, versus asking them to grasp all of the technical components of how metadata is scraped earlier than they might add worth.
The place we landed in our analysis is that Atlan had the product that sat most squarely within the center between enterprise customers and technical customers.
What do you plan on creating with Atlan? Do you will have an concept of what use instances you’ll construct, and the worth you’ll drive?
We’ve began with amassing some enterprise use instances and have a pair which might be fairly data-heavy the place we’re creating issues like buyer well being scores. These scores proactively assist our buyer success crew perceive details about our retailers. Getting individuals into one, central location the place they will retrieve that data goes to assist.
The best way we’re serious about that is that we’re not going to have a ton of customers on Atlan instantly. We’re going to roll it out by use case and we’re going to slowly enrich it, as a result of it’s the kind of device the place for those who transfer too shortly and issues aren’t up to date, then you definately’ve simply created extra technical debt in a unique device. At that time, you’re asking the query of whether or not dangerous information is best than no information. We don’t need that to be the case. So, we’re going to predominantly give attention to enterprise groups that come to the information crew with loads of questions.
Some groups have their very own documentation, Confluence is used sparingly, and we’re a really Slack-heavy group. We’re kicking tires proper now to see what works internally, however we’re wanting ahead to having information contextualized and tagged on Slack by way of Atlan. I feel it is going to be essential to get that arrange accurately so customers will see worth shortly. We can be extra clever, and if we see that 20 customers on Slack are asking the identical questions on an asset, then we will prioritize documenting it.
Did we miss something?
I’d simply say we’re wanting ahead to this journey. What I’m specializing in, particularly in our group the place we worth fiscal accountability, is how we present worth to the enterprise and our inner stakeholders. You want buy-in to do one thing like this, and it requires change administration. So, our crew wants to ensure we’re getting essentially the most out of Atlan, but additionally that each enterprise and technical stakeholders are benefitting, too.
Photograph by Bench Accounting on Unsplash










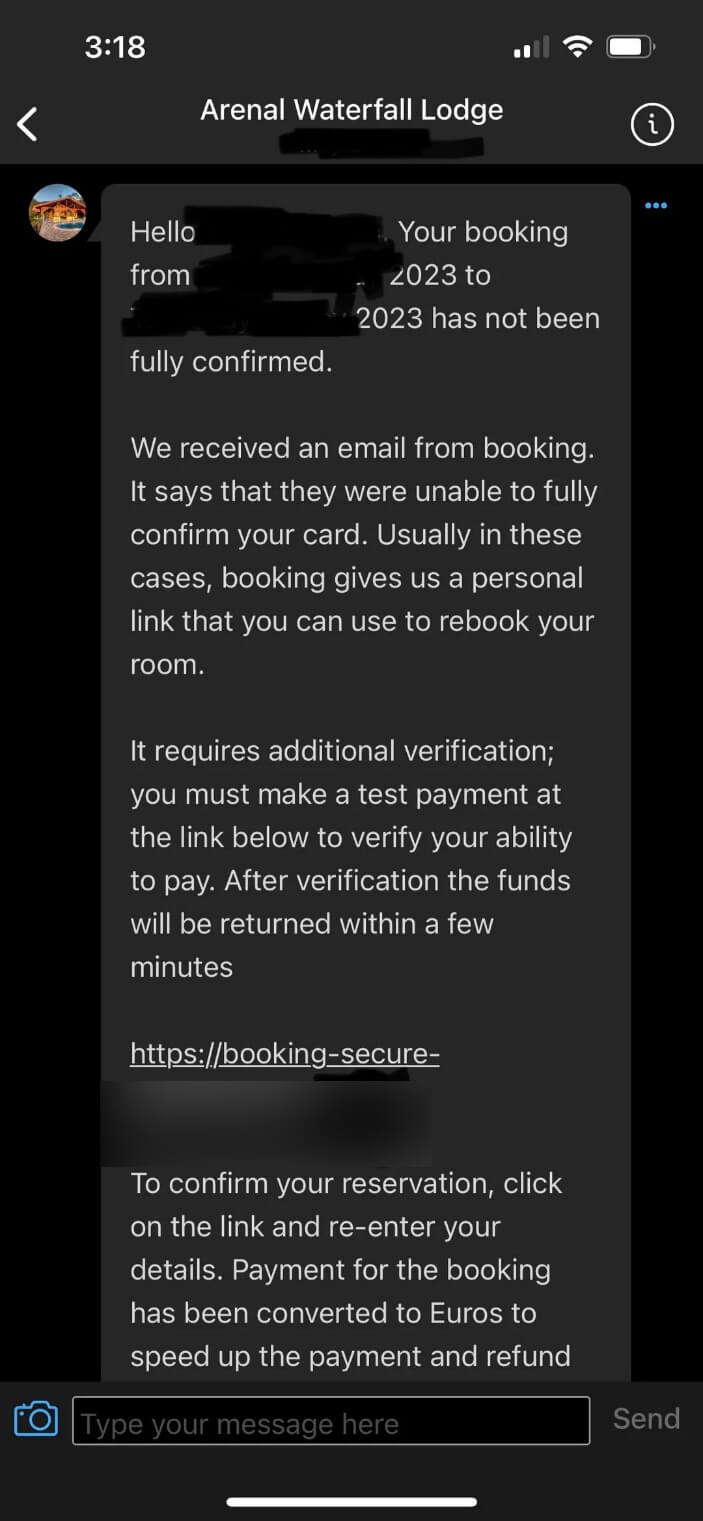
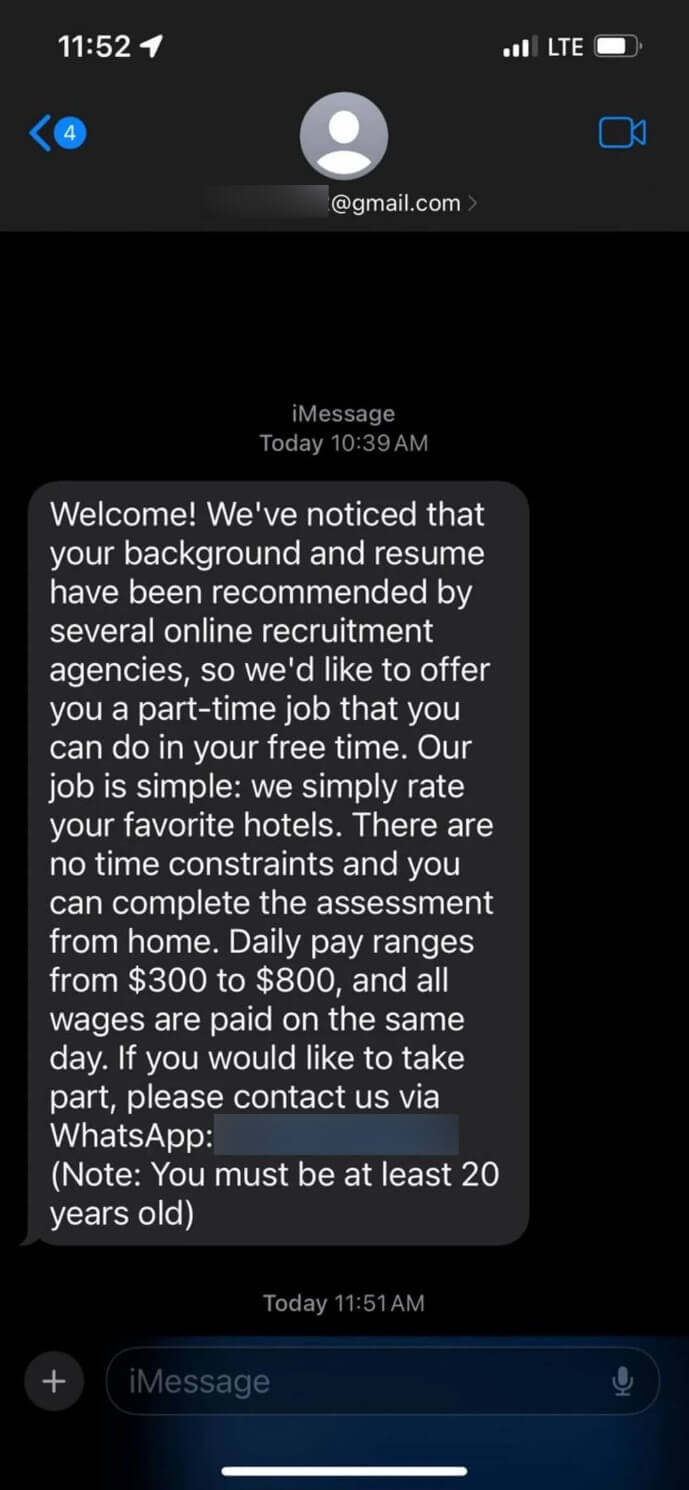
 The straightforward availability of generative AI instruments has opened the floodgates to waves of extra convincing and efficient scams. By producing phishing emails which can be grammatically right, contextually applicable, and freed from typical pink flags which may alert the recipient, they’ll simply trick folks and companies into
The straightforward availability of generative AI instruments has opened the floodgates to waves of extra convincing and efficient scams. By producing phishing emails which can be grammatically right, contextually applicable, and freed from typical pink flags which may alert the recipient, they’ll simply trick folks and companies into