Within the late nineteenth and early twentieth century, a sequence of catastrophic fires briefly succession led an outraged public to demand motion from the budding fireplace safety {industry}. Among the many consultants, one preliminary focus was on “Hearth Evacuation Exams”. The earliest of those assessments targeted on particular person efficiency and examined occupants on their evacuation velocity, generally performing the assessments “without warning” as if the hearth drill have been an actual fireplace. These early assessments have been extra prone to end in accidents to the test-takers than any enchancment in survivability. It wasn’t till introducing higher protecting engineering – wider doorways, push bars at exits, firebreaks in development, lighted exit indicators, and so forth – that survival charges from constructing fires started to enhance. As protections advanced through the years and enhancements like necessary fireplace sprinklers grew to become required in constructing code, survival charges have continued to enhance steadily, and “assessments” have advanced into introduced, superior coaching and posted evacuation plans.
On this weblog, we’ll analyze the fashionable follow of Phishing “Exams” as a cybersecurity management because it pertains to industry-standard fireplace safety practices.
Fashionable “Phishing assessments” strongly resemble the early “Hearth assessments”
Google presently operates below laws (for instance, FedRAMP within the USA) that require us to carry out annual “Phishing Exams.” In these necessary assessments, the Safety group creates and sends phishing emails to Googlers, counts what number of work together with the e-mail, and educates them on learn how to “not be fooled” by phishing. These workouts sometimes gather reporting metrics on despatched emails and what number of workers “failed” by clicking the decoy hyperlink. Normally, additional schooling is required for workers who fail the train. Per the FedRAMP pen-testing steering doc: “Customers are the final line of protection and must be examined.”
These assessments resemble the primary “evacuation assessments” that constructing occupants have been as soon as subjected to. They require people to acknowledge the hazard, react individually in an ‘acceptable’ approach, and are informed that any failure is a person failure on their half quite than a systemic concern. Worse, FedRAMP steering requires corporations to bypass or get rid of all systematic controls throughout the assessments to make sure the chance of an individual clicking on a phishing hyperlink is artificially maximized.
Among the many dangerous negative effects of those assessments:
-
There isn’t a proof that the assessments end in fewer incidences of profitable phishing campaigns;
-
Phishing (or extra generically social engineering) stays a prime vector for attackers establishing footholds at corporations.
-
Analysis exhibits that these assessments don’t successfully stop individuals from being fooled. This research with 14,000 members confirmed a counterproductive impact of phishing assessments, exhibiting that “repeat clickers” will persistently fail assessments regardless of latest interventions.
-
Some (e.g, FedRAMP) phishing assessments require bypassing current anti-phishing defenses. This creates an inaccurate notion of precise dangers, permits penetration testing groups to keep away from having to imitate precise fashionable attacker ways, and creates a threat that the allowlists put in place to facilitate the check may very well be by chance left in place and reused by attackers.
-
There was a considerably elevated load on Detection and Incident Response (D&R) groups throughout these assessments, as customers saturate them with hundreds of pointless stories.
-
Staff are upset by them and really feel safety is “tricking them”, which degrades the belief with our customers that’s needed for safety groups to make significant systemic enhancements and once we want workers to take well timed actions associated to precise safety occasions.
-
At bigger enterprises with a number of unbiased merchandise, individuals can find yourself with quite a few overlapping required phishing assessments, inflicting repeated burdens.
However are customers the final line of protection?
Coaching people to keep away from phishing or social engineering with a 100% success price is a possible not possible process. There is worth in educating individuals learn how to spot phishing and social engineering to allow them to alert safety to carry out incident response. By making certain that even a single consumer stories assaults in progress, corporations can activate full-scope responses that are a worthwhile defensive management that may shortly mitigate even superior assaults. However, very similar to the Hearth Security skilled world has moved to common pre-announced evacuation coaching as an alternative of shock drills, the knowledge safety {industry} ought to transfer towards coaching that de-emphasizes surprises and methods and as an alternative prioritizes correct coaching of what we wish employees to do the second they spot a phishing electronic mail – with a specific deal with recognizing and reporting the phishing risk.
Briefly – we have to cease doing phishing assessments and begin doing phishing fireplace drills.
A “phishing fireplace drill” would goal to perform the next:
-
Educate our customers about learn how to spot phishing emails
-
Inform the customers on learn how to report phishing emails
-
Permit workers to follow reporting a phishing electronic mail within the method that we would favor, and
-
Acquire helpful metrics for auditors, akin to:
-
The variety of customers who accomplished the follow train of reporting the e-mail as a phishing electronic mail
-
The time between the e-mail opening and the primary report of phishing
-
Time of first escalation to the safety group (and time delta)
-
Variety of stories at 1 hour, 4 hours, 8 hours, and 24 hours post-delivery
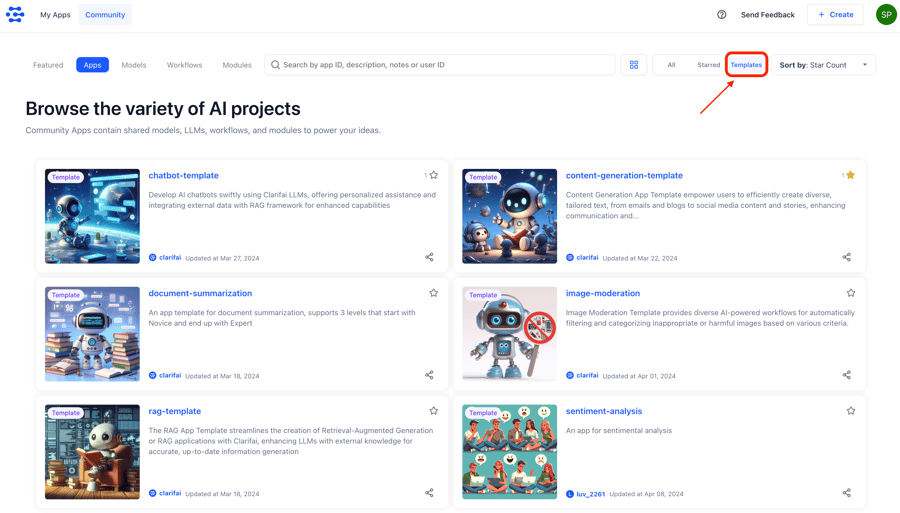
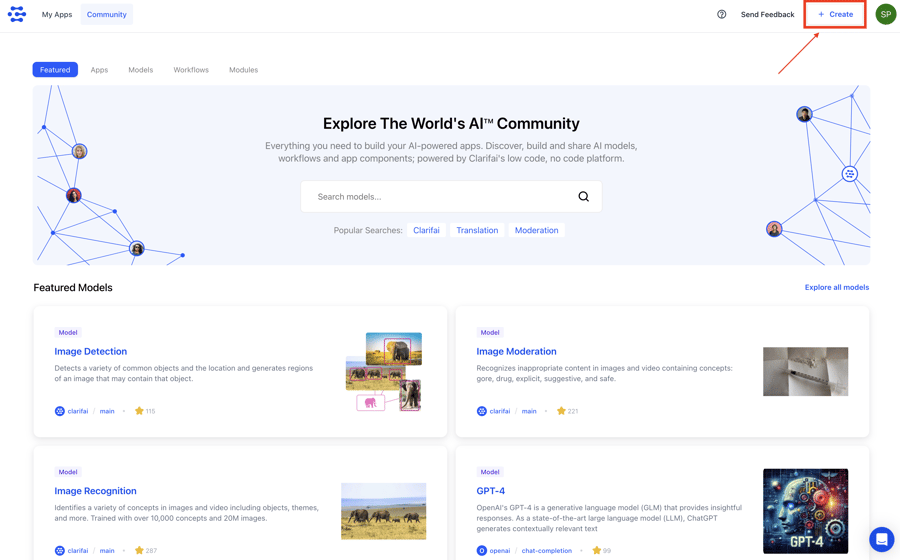
When performing a phishing drill, somebody would ship an electronic mail asserting itself as a phishing electronic mail and with related directions or particular duties to carry out. An instance textual content is supplied beneath.
You’ll be able to’t “repair” individuals, however you can repair the instruments.
Phishing and Social Engineering aren’t going away as assault strategies. So long as people are fallible and social creatures, attackers can have methods to govern the human issue. The simpler strategy to each dangers is a targeted pursuit of secure-by-default techniques in the long run, and a deal with funding in engineering defenses akin to unphishable credentials (like passkeys) and implementing multi-party approval for delicate safety contexts all through manufacturing techniques. It’s due to investments in architectural defenses like these that Google hasn’t needed to severely fear about password phishing in almost a decade.
Educating workers about alerting safety groups of assaults in progress stays a helpful and important addition to a holistic safety posture. Nevertheless, there’s no have to make this adversarial, and we don’t acquire something by “catching” individuals “failing” on the process. Let’s cease partaking in the identical outdated failed protections and comply with the lead of extra mature industries, akin to Hearth Safety, which has confronted these issues earlier than and already settled on a balanced strategy.