
WordPress websites are being hacked to put in malicious plugins that show faux software program updates and errors to push information-stealing malware.
Over the previous couple of years, information-stealing malware has turn out to be a scourge to safety defenders worldwide as stolen credentials are used to breach networks and steal knowledge.
Since 2023, a malicious marketing campaign known as ClearFake has been used to show faux internet browser replace banners on compromised web sites that distribute information-stealing malware.
In 2024, a brand new marketing campaign known as ClickFix was launched that shares many similarities with ClearFake however as an alternative pretends to be software program error messages with included fixes. Nonetheless, these “fixes” are PowerShell scripts that, when executed, will obtain and set up information-stealing malware.
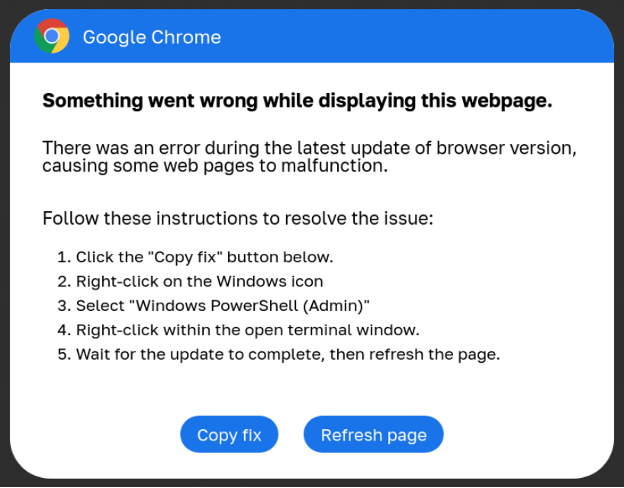
Supply: BleepingComputer
ClickFix campaigns have turn out to be more and more frequent this 12 months, with menace actors compromising websites to show banners displaying faux errors for Google Chrome, Google Meet conferences, Fb, and even captcha pages.
Malicious WordPress plugins
Final week, GoDaddy reported that the ClearFake/ClickFix menace actors have breached over 6,000 WordPress websites to put in malicious plugins that show the faux alerts related to these campaigns.
“The GoDaddy Safety staff is monitoring a brand new variant of ClickFix (often known as ClearFake) faux browser replace malware that’s distributed through bogus WordPress plugins,” explains GoDaddy safety researcher Denis Sinegubko.
“These seemingly professional plugins are designed to seem innocent to web site directors however include embedded malicious scripts that ship faux browser replace prompts to end-users.”
The malicious plugins make the most of names much like professional plugins, similar to Wordfense Safety and LiteSpeed Cache, whereas others use generic, made-up names.
The record of malicious plugins seen on this marketing campaign between June and September 2024 are:
| LiteSpeed Cache Traditional | Customized CSS Injector |
| MonsterInsights Traditional | Customized Footer Generator |
| Wordfence Safety Traditional | Customized Login Styler |
| Search Rank Enhancer | Dynamic Sidebar Supervisor |
| website positioning Booster Professional | Straightforward Themes Supervisor |
| Google website positioning Enhancer | Kind Builder Professional |
| Rank Booster Professional | Fast Cache Cleaner |
| Admin Bar Customizer | Responsive Menu Builder |
| Superior Person Supervisor | website positioning Optimizer Professional |
| Superior Widget Handle | Easy Publish Enhancer |
| Content material Blocker | Social Media Integrator |
Web site safety agency Sucuri additionally famous {that a} faux plugin named “Common Popup Plugin” can be a part of this marketing campaign.
When put in, the malicious plugin will hook numerous WordPress actions relying on the variant to inject a malicious JavaScript script into the HTML of the positioning.
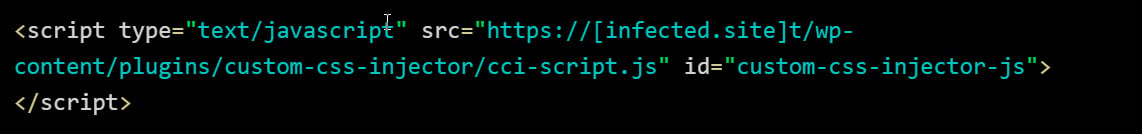
Supply: GoDaddy
When loaded, this script will try to load an additional malicious JavaScript file saved in a Binance Sensible Chain (BSC) sensible contract, which then hundreds the ClearFake or ClickFix script to show the faux banners.
From internet server entry logs analyzed by Sinegubko, the menace actors seem like using stolen admin credentials to log into the WordPress web site and set up the plugin in an automatic method.
As you may see from the picture under, the menace actors log in through a single POST HTTP request relatively than first visiting the positioning’s login web page. This means that it’s being carried out in an automatic method after the credentials have been already obtained.
As soon as the menace actor logs in, they add and set up the malicious plugin.
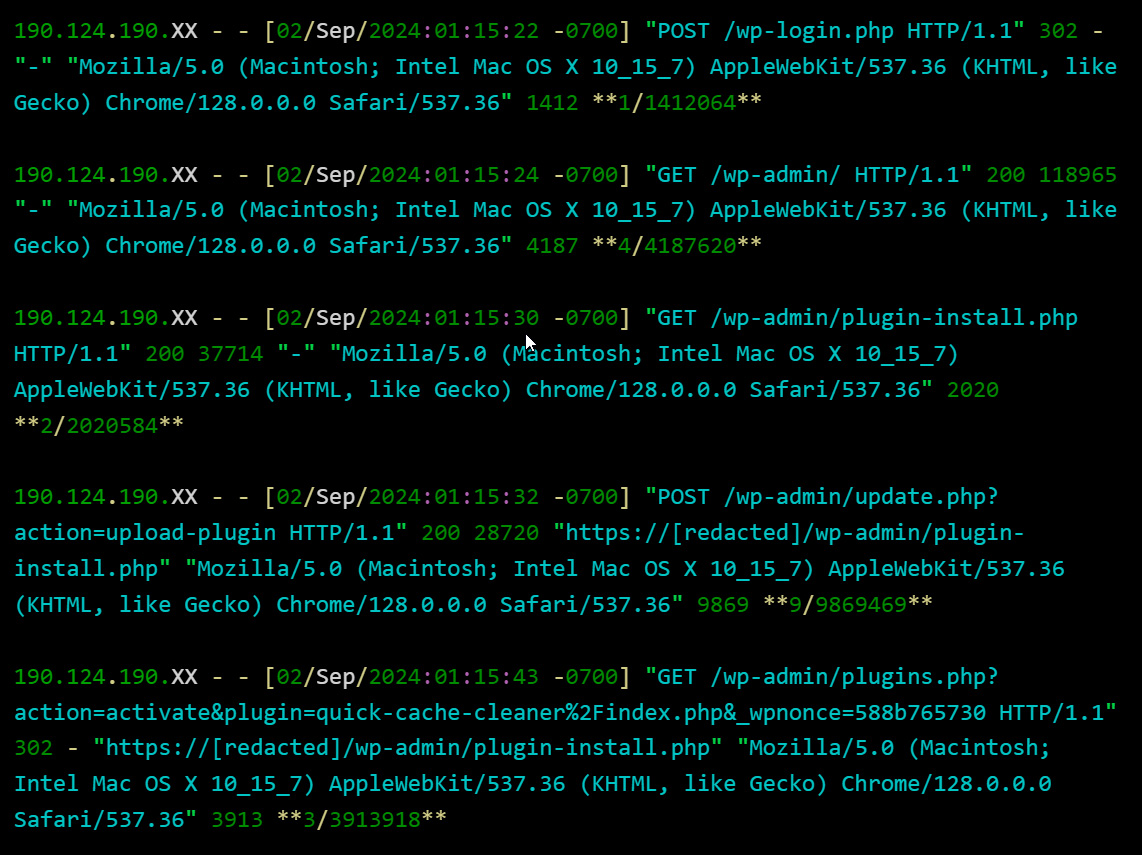
Supply: GoDaddy
Whereas it’s unclear how the menace actors are acquiring the credentials, the researcher notes it may very well be by earlier brute pressure assaults, phishing, and information-stealing malware.
In case you are a WordPress operation and are receiving reviews of pretend alerts being exhibited to guests, you need to instantly look at the record of put in plugins, and take away any that you just didn’t set up your self.
When you discover unknown plugins, you must also instantly reset the passwords for any admin customers to a novel password solely used at your web site.

