Current analysis signifies that organizational insiders perpetrate 35 p.c of information breaches, and malicious insider incidents price organizations a mean of $701,500 yearly. The examine and administration of insider menace and danger stay areas of more and more rising consideration, prevalence, and concern, however capturing and sharing details about insider incidents in a standardized manner has been a problem for practitioners. A regular of incident classification and knowledge sharing might enable practitioners to construct, keep, deidentify, and share insider menace case knowledge with an eye fixed towards constructing extra strong knowledge for evaluation and insights that profit their organizations and the entire group. On this publish, we introduce the Insider Incident Knowledge Change Customary (IIDES) schema for insider incident knowledge assortment, present an instance use case, and invite you to collaborate with us on its improvement.
The sphere of insider menace is itself nonetheless comparatively younger, encompassing many alternative fields, disparate sources of authorized and coverage mandates, and a number of other colleges of thought relating to ideas of operation. The latest version of The CERT Frequent Sense Information to Mitigating Insider Threats was printed in 2022, and it builds on greater than 20 years of information assortment, analysis, and partnering by the SEI CERT Division. In a lot the identical manner that analysis round insider menace continues to be rising and coalescing, practitioners are nonetheless constructing on expertise to work out greatest practices round technical defenses, behavioral and human components mitigations, and strategies for storing and exchanging incident knowledge.
These targets have all motivated the CERT Insider Threat Crew to develop a brand new customary for storing and exchanging insider menace case knowledge. Whereas there have been some makes an attempt at standardizing varied elements of insider menace terminology through the years, none have been complete sufficient to satisfy our personal knowledge assortment wants, and none present a selected schema for interconnecting items of information. The Insider Incident Knowledge Change Customary (IIDES) contains constructions for gathering and analyzing quite a lot of technical, non-technical, organizational, and incident response data to satisfy the numerous wants of researchers and practitioners, and will likely be accompanied by a corresponding software suite. We hope that IIDES helps a extra constant mapping of suggestions and greatest practices for response, detection, and mitigation of insider threats sooner or later.
IIDES improvement, as is the case with many requirements, required a tradeoff between a completely articulated, tightly constrained schema and a language versatile sufficient to be helpful throughout a spread of potential purposes and customers. We used the guiding ideas of simplicity, experience, flexibility, and interoperability to steadiness these tradeoffs.
The IIDES Schema
IIDES supplies a schema, coded in JSON, to gather and categorize insider menace incidents. The schema contains 4 sections: the core elements, extra subcomponents, relationships, and vocabularies.
Core Elements in IIDES
There are seven core elements within the IIDES schema:
- Incident—a abstract and outline of the safety menace
- Insider—the particular person concerned within the incident
- Group—the group concerned within the incident
- Job—the employment relationship between a person and a company
- Detection—particulars about how, when, and by whom the incident was found
- Response—the group’s response to the incident
- Tactic, Method, and Process (TTP)—an motion taken by an insider throughout an incident
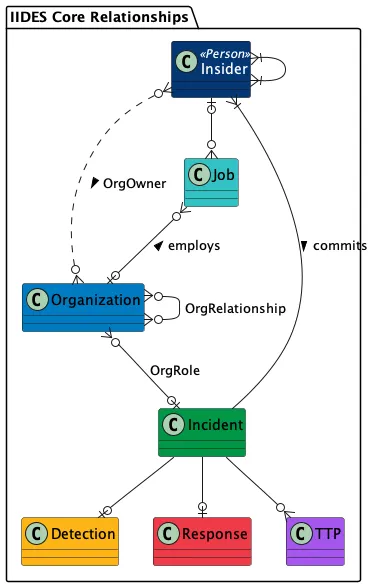
Determine 1: The core elements in IIDES
Extra Subcomponents
Some elements have extra subcomponents. For instance, the Response part can have a Authorized Response subcomponent, which could embrace a number of Courtroom Case elements. Determine 2 extra absolutely illustrates these relationships.
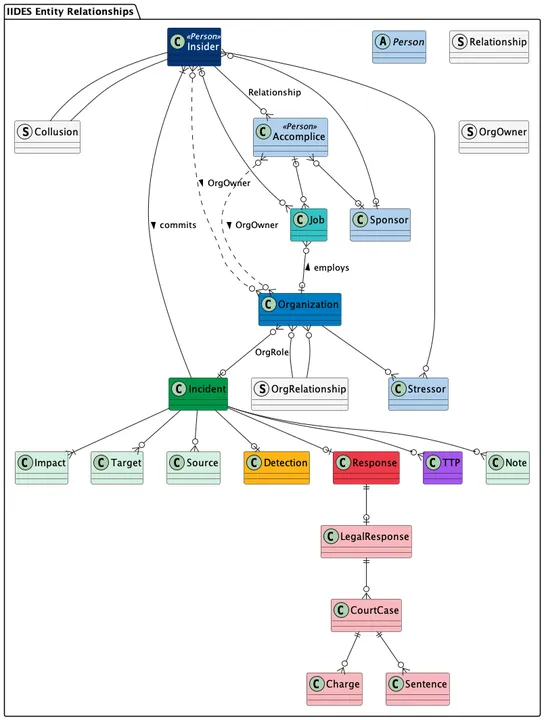
Determine 2: A diagram of all elements and subcomponents in IIDES
Relationships
A relationship connects two entities in IIDES. For instance, an Insider could have a relationship to an confederate who helped commit the incident. The Insider additionally doubtless has a relationship with a Job part. Specifying relationships is likely one of the main variations between IIDES and different requirements which have been proposed through the years. Reasonably than a listing of potential phrases, IIDES supplies all the construction of an incident, and the way every bit of details about the insider, the group, and the insider’s actions join collectively to type an entire image of the insider menace.
Vocabularies
Most of the elements in IIDES have related vocabularies that additional describe entities and supply constant terminology for discussing incidents throughout completely different organizations. The Insider part, for instance, features a vocabulary for the insider’s motive, akin to monetary acquire or curiosity. These vocabularies will doubtless change over time as IIDES develops additional and customers counsel additions.
IIDES in Motion
We now have offered a lot of instance instances with fictitious knowledge for example how IIDES can work in follow. In a single instance, we created a case with the following abstract:
The insider, a former army member, labored as a cybersecurity specialist for a authorities company in Might 2003. Throughout this time, she printed a report from her work laptop that detailed unauthorized entry makes an attempt by a international hacking group towards municipal election techniques and voter databases. She then shared this Prime Secret data with a tech weblog. This report revealed the methods and instruments used to assemble the knowledge contained within the report, which, if disclosed, might be detrimental to the USA. A authorities company investigated her, and the insider pleaded responsible in June 2004 to at least one felony depend of unauthorized transmission of nationwide protection data and was convicted.
The pattern instances embrace a JSON file matching IIDES, a better to learn markdown illustration of the identical knowledge, and a visualization of the elements generated from the schema.
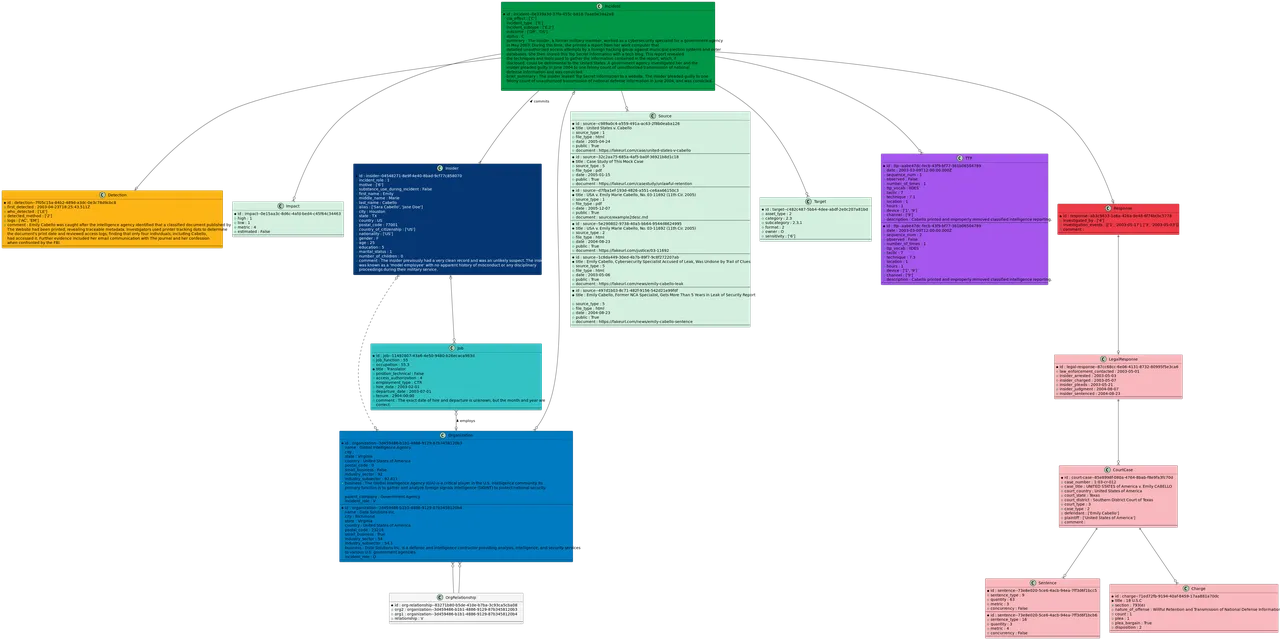
Determine 3: IIDES kinds the incident knowledge right into a structured schema for simple assortment, evaluation, and sharing. The decrease left blocks are magnified in Determine 4.
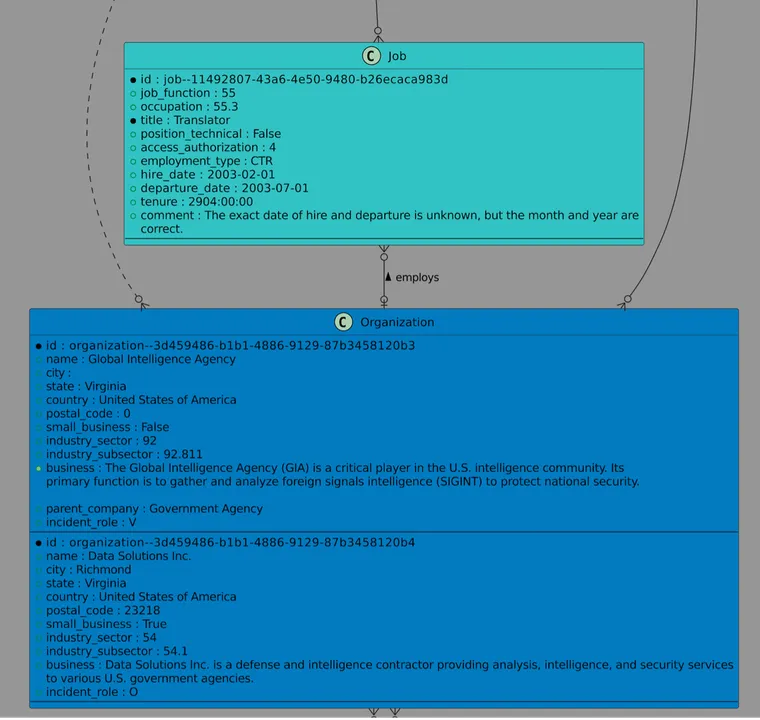
Determine 4: An excerpt of a visualization of a pattern case in IIDES. Every bit of case data suits into the organized schema.
These examples illustrate the insider’s actions, their relationships, and the result of the incident in a format that allows simpler storage and sharing of insider incidents.
Work with the SEI
We anticipate IIDES will profit those that create fashions and simulations for coaching, schooling, and greatest practices by offering a constant vocabulary throughout organizations. Practitioners akin to analysts, investigators, and people answerable for danger administration stand to learn from constructing inner case corpora that may be simply analyzed, searched, and measured. For these with a must share case knowledge with different practitioners, different comparable companies or entities, and third-party organizations, akin to legislation enforcement, governmental companies, or analysis organizations, IIDES supplies a constant format for a shared understanding.
We’re very fascinated with getting suggestions from the group relating to IIDES and plan to include the suggestions we obtain earlier than releasing an official 1.0 model. How do you see your group utilizing IIDES? Are there particular additions or modifications you want to see? Are there use instances or advantages that we haven’t anticipated? Do we have to make clear something within the documentation or vocabularies? You possibly can overview the IIDES white paper for extra details about IIDES improvement and its core performance or go straight to the schema or documentation for every of the courses.
You possibly can submit your suggestions to information@sei.cmu.edu or straight on GitHub by means of the points tab.
