Bringing an current codebase into compliance with the SEI CERT Coding Commonplace requires a price of effort and time. The standard approach of assessing this value is to run a static evaluation device on the codebase (noting that putting in and sustaining the static evaluation device might incur its personal prices). A easy metric for estimating this value is subsequently to depend the variety of static evaluation alerts that report a violation of the CERT tips. (This assumes that fixing anyone alert usually has no impression on different alerts, although typically a single challenge might set off a number of alerts.) However those that are conversant in static evaluation instruments know that the alerts are usually not at all times dependable – there are false positives that should be detected and disregarded. Some tips are inherently simpler than others for detecting violations.
This 12 months, we plan on making some thrilling updates to the SEI CERT C Coding Commonplace. This weblog publish is about one among our concepts for enhancing the usual. This alteration would replace the requirements to higher harmonize with the present state-of-the-art for static evaluation instruments, in addition to simplify the method of supply code safety auditing.
For this publish, we’re asking our readers and customers to supply us with suggestions. Would the adjustments that we suggest to our Threat Evaluation metric disrupt your work? How a lot effort would they impose on you, our readers? If you need to remark, please ship an e-mail to data@sei.cmu.edu.
The premise for our adjustments is that some violations are simpler to restore than others. Within the SEI CERT Coding Commonplace, we assign every guideline a Remediation Price metric, which is outlined with the next textual content:
|
Worth |
Which means |
Detection |
Correction |
|
1 |
Excessive |
Guide |
Guide |
|
2 |
Medium |
Computerized |
Guide |
|
3 |
Low |
Computerized |
Computerized |
Moreover, every guideline additionally has a Precedence metric, which is the product of the Remediation Price and two different metrics that assess severity (how consequential is it to not adjust to the rule) and probability (how seemingly that violating the rule results in an exploitable vulnerability?). All three metrics might be represented as numbers starting from 1 to three, which may produce a product between 1 and 27 (that’s, 3*3*3), the place low numbers indicate larger value.
The above desk could possibly be alternately represented this manner:
|
Is Routinely… |
Not Repairable |
Repairable |
|
Not Detectable |
1 (Excessive) |
1 (Excessive) |
|
Detectable |
2 (Medium) |
3 (Low) |
This Remediation Price metric was conceived again in 2006 when the SEI CERT C Coding Commonplace was first created. We didn’t use extra exact definitions of detectable or repairable on the time. However we did assume that some tips can be routinely detectable whereas others wouldn’t. Likewise, we assumed that some tips can be repairable whereas others wouldn’t. Lastly, a suggestion that was repairable however not detectable can be assigned a Excessive value on the grounds that it was not worthwhile to restore code if we couldn’t detect whether or not or not it complied with a suggestion.
We additionally reasoned that the questions of detectability and repairability ought to be thought-about in concept. That’s, is a passable detection or restore heuristic potential? When contemplating if such a heuristic exists, you may ignore whether or not a business or open supply product claims to implement the heuristic.
As we speak, the state of affairs has modified, and subsequently we have to replace our definitions of detectable and repairable.
Detectability
A latest main change has been so as to add an Automated Detection part to each CERT guideline. This identifies the evaluation instruments that declare to detect – and restore – violations of the rule. For instance, Parasoft claims to detect violations of each rule and suggestion within the SEI CERT C Coding Commonplace. If a suggestion’s Remediation Price is Excessive, indicating that the rule is non-detectable, does that create incompatibility with all of the instruments listed within the Automated Detection part?
The reply is that the instruments in such a suggestion could also be topic to false positives (that’s, offering alerts on code that really complies with the rule), or false negatives (that’s, failing to report some really noncompliant code), or each. It’s straightforward to assemble an analyzer with no false positives (merely by no means report any alerts) or false negatives (merely alert that each line of code is noncompliant). However for a lot of tips, detection with no false positives and no false negatives is, in concept, undecidable. Some attributes are simpler to research, however on the whole sensible analyses are approximate, affected by false positives, false negatives, or each. (A sound evaluation is one which has no false negatives, although it may need false positives. Most sensible instruments, nevertheless, have each false negatives and false positives.) For instance, EXP34-C, the C rule that forbids dereferencing null pointers, will not be routinely detectable by this stricter definition. As a counterexample, violations of rule EXP45-C (don’t carry out assignments in choice statements) might be detected reliably.
An appropriate definition of detectable is: Can a static evaluation device decide if code violates the rule with each a low false constructive charge and low false destructive charge? We don’t require that there can by no means be false positives or false negatives, however we are able to require that they each be small, which means {that a} device’s alerts are full and correct for sensible functions.
Most tips, together with EXP34-C, will, by this definition, be undetectable utilizing the present crop of instruments. This doesn’t imply that instruments can’t report violations of EXP34-C; it simply implies that any such violation may be a false constructive, the device may miss some violations, or each.
Repairability
Our notation of what’s repairable has been formed by latest advances in Automated Program Restore (APR) analysis and know-how, such because the Redemption venture. Particularly, the Redemption venture and power take into account a static evaluation alert repairable no matter whether or not it’s a false constructive. Repairing a false constructive ought to, in concept, not alter the code conduct. Moreover, in Redemption, a single restore ought to be restricted to a neighborhood area and never distributed all through the code. For example, altering the quantity or varieties of a perform’s parameter checklist requires modifying each name to that perform, and performance calls might be distributed all through the code. Such a change would subsequently not be native.
With that stated, our definition of repairable might be expressed as: Code is repairable if an alert might be reliably mounted by an APR device, and the one modifications to code are close to the location of the alert. Moreover, repairing a false constructive alert should not break the code. For instance, the null-pointer-dereference rule (EXP34-C) is repairable as a result of a pointer dereference might be preceded by an routinely inserted null verify. In distinction, CERT rule MEM31-C requires that every one dynamic reminiscence be freed precisely as soon as. An alert that complains that some pointer goes out of scope with out being freed appears repairable by inserting a name to free(pointer). Nevertheless, if the alert is a false constructive, and the pointer’s pointed-to reminiscence was already freed, then the APR device might have simply created a double-free vulnerability, in essence changing working code into susceptible code. Due to this fact, rule MEM31-C will not be, with present capabilities, (routinely) repairable.
The New Remediation Price
Whereas the earlier Remediation Price metric did deal with detectability and repairability as interrelated, we now imagine they’re unbiased and attention-grabbing metrics by themselves. A rule that was neither detectable nor repairable was given the identical remediation value as one which was repairable however not detectable, and we now imagine these two guidelines ought to have these variations mirrored in our metrics. We’re subsequently contemplating changing the outdated Remediation Price metric with two metrics: Detectable and Repairable. Each metrics are easy sure/no questions.
There’s nonetheless the query of methods to generate the Precedence metric. As famous above, this was the product of the Remediation Price, expressed as an integer from 1 to three, with two different integers from 1 to three. We will subsequently derive a brand new Remediation Price metric from the Detectable and Repairable metrics. The obvious resolution can be to assign a 1 to every sure and a 2 to every no. Thus, we’ve got created a metric just like the outdated Remediation Price utilizing the next desk:
|
Is Routinely… |
Not Repairable |
Repairable |
|
Not Detectable |
1 |
2 |
|
Detectable |
2 |
4 |
Nevertheless, we determined {that a} worth of 4 is problematic. First, the outdated Remediation Price metric had a most of three, and having a most of 4 skews our product. Now the very best precedence can be 3*3*4=36 as a substitute of 27. This might additionally make the brand new remediation value extra vital than the opposite two metrics. We determined that changing the 4 with a 3 solves these issues:
|
Is Routinely… |
Not Repairable |
Repairable |
|
Not Detectable |
1 |
2 |
|
Detectable |
2 |
3 |
Subsequent Steps
Subsequent will come the duty of analyzing every guideline to interchange its Remediation Price with new Detectable and Repairable metrics. We should additionally replace the Precedence and Stage metrics for tips the place the Detectable and Repairable metrics disagree with the outdated Remediation Price.
Instruments and processes that incorporate the CERT metrics might want to replace their metrics to replicate CERT’s new Detectable and Repairable metrics. For instance, CERT’s personal SCALe venture offers software program safety audits ranked by Precedence, and future rankings of the CERT C guidelines will change.
Listed below are the outdated and new metrics for the C Integer Guidelines:
|
Rule |
Detectable |
Repairable |
New REM |
Outdated REM |
Title |
|
INT30-C |
No |
Sure |
2 |
3 |
Guarantee that unsigned integer operations don’t wrap |
|
INT31-C |
No |
Sure |
2 |
3 |
Guarantee that integer conversions don’t end in misplaced or misinterpreted knowledge |
|
INT32-C |
No |
Sure |
2 |
3 |
Guarantee that operations on signed integers don’t end in overflow |
|
INT33-C |
No |
Sure |
2 |
2 |
Guarantee that division and the rest operations don’t end in divide-by-zero errors |
|
INT34-C |
No |
Sure |
2 |
2 |
Do not shift an expression by a destructive variety of bits or by larger than or equal to the variety of bits that exist within the operand |
|
INT35-C |
No |
No |
1 |
2 |
Use appropriate integer precisions |
|
INT36-C |
Sure |
No |
2 |
3 |
Changing a pointer to integer or integer to pointer |
On this desk, New REM (Remediation Price) is the metric we might produce from the Detectable and Repairable metrics, and Outdated REM is the present Remediation Price metric. Clearly, solely INT33-C and INT34-C have the identical New REM values as Outdated REM values. Because of this their Precedence and Stage metrics stay unchanged, however the different guidelines would have revised Precedence and Stage metrics.
As soon as we’ve got computed the brand new Threat Evaluation metrics for the CERT C Safe Coding Guidelines, we might subsequent deal with the C suggestions, which even have Threat Evaluation metrics. We might then proceed to replace these metrics for the remaining CERT requirements: C++, Java, Android, and Perl.
Auditing
The brand new Detectable and Repairable metrics additionally alter how supply code safety audits ought to be performed.
Any alert from a suggestion that’s routinely repairable may, in actual fact, not be audited in any respect. As an alternative, it could possibly be instantly repaired. If an automatic restore device will not be obtainable, it may as a substitute be repaired manually by builders, who might not care whether or not or not it’s a true constructive. A corporation might select whether or not to use all the potential repairs or to evaluation them; they might apply additional effort to evaluation computerized repairs, however this will solely be essential to fulfill their requirements of software program high quality and their belief within the APR device.
Any alert from a suggestion that’s routinely detectable also needs to, in actual fact, not be audited. It ought to be repaired routinely with an APR device or despatched to the builders for guide restore.
This raises a possible query: Detectable tips ought to, in concept, nearly by no means yield false positives. Is that this truly true? The alert may be false attributable to bugs within the static evaluation device or bugs within the mapping (between the device and the CERT guideline). We may conduct a sequence of supply code audits to verify {that a} guideline really is routinely detectable and revise tips that aren’t, in actual fact, routinely detectable.
Solely tips which are neither routinely detectable nor routinely repairable ought to truly be manually audited.
Given the large variety of SA alerts generated by most code within the DoD, any optimizations to the auditing course of ought to end in extra alerts being audited and repaired. This can reduce the hassle required in addressing alerts. Many organizations don’t deal with all alerts, and so they consequently settle for the danger of un-resolved vulnerabilities of their code. So as a substitute of decreasing effort, this improved course of reduces danger.
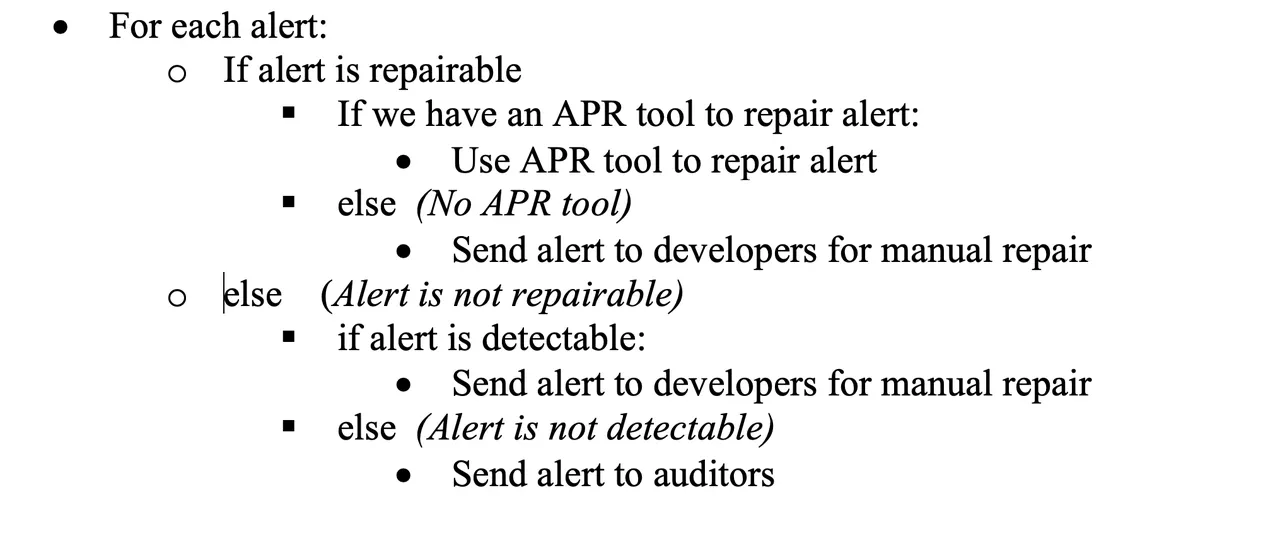
This improved course of might be summed up by the next pseudocode:
Your Suggestions Wanted
We’re publishing this particular plan to solicit suggestions. Would these adjustments to our Threat Evaluation metric disrupt your work? How a lot effort would they impose on you? If you need to remark, please ship an e-mail to data@sei.cmu.edu.
