On Jan. 29, U.S.-based Wiz Analysis introduced it responsibly disclosed a DeepSeek database beforehand open to the general public, exposing chat logs and different delicate data. DeepSeek locked down the database, however the discovery highlights potential dangers with generative AI fashions, significantly worldwide initiatives.
DeepSeek shook up the tech trade over the past week because the Chinese language firm’s AI fashions rivaled American generative AI leaders. Particularly, DeepSeek’s R1 competes with OpenAI o1 on some benchmarks.
How did Wiz Analysis uncover DeepSeek’s public database?
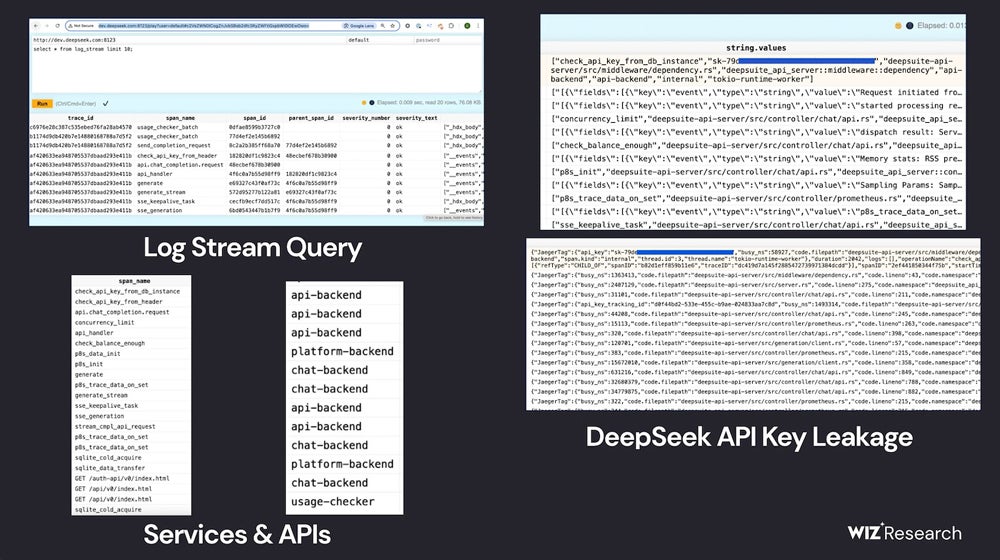
In a weblog publish disclosing Wiz Analysis’s work, cloud safety researcher Gal Nagli detailed how the staff discovered a publicly accessible ClickHouse database belonging to DeepSeek. The database opened up potential paths for management of the database and privilege escalation assaults. Contained in the database, Wiz Analysis may learn chat historical past, backend knowledge, log streams, API Secrets and techniques, and operational particulars.
The staff discovered the ClickHouse database “inside minutes” as they assessed DeepSeek’s potential vulnerabilities.
“We have been shocked, and likewise felt an awesome sense of urgency to behave quick, given the magnitude of the invention,” Nagli mentioned in an electronic mail to TechRepublic.
They first assessed DeepSeek’s internet-facing subdomains, and two open ports struck them as uncommon; these ports result in DeepSeek’s database hosted on ClickHouse, the open-source database administration system. By shopping the tables in ClickHouse, Wiz Analysis discovered chat historical past, API keys, operational metadata, and extra.
The Wiz Analysis staff famous they didn’t “execute intrusive queries” in the course of the exploration course of, per moral analysis practices.
What does the publicly obtainable database imply for DeepSeek’s AI?
Wiz Analysis knowledgeable DeepSeek of the breach and the AI firm locked down the database; subsequently, DeepSeek AI merchandise shouldn’t be affected.
Nevertheless, the chance that the database may have remained open to attackers highlights the complexity of securing generative AI merchandise.
“Whereas a lot of the eye round AI safety is concentrated on futuristic threats, the true risks typically come from primary dangers—like unintentional exterior publicity of databases,” Nagli wrote in a weblog publish.
IT professionals ought to concentrate on the hazards of adopting new and untested merchandise, particularly generative AI, too rapidly — give researchers time to search out bugs and flaws within the methods. If potential, embody cautious timelines in firm generative AI use insurance policies.
SEE: Defending and securing knowledge has grow to be extra sophisticated within the days of generative AI.
“As organizations rush to undertake AI instruments and providers from a rising variety of startups and suppliers, it’s important to do not forget that by doing so, we’re entrusting these firms with delicate knowledge,” Nagli mentioned.
Relying in your location, IT staff members may want to concentrate on laws or safety issues that will apply to generative AI fashions originating in China.
“For instance, sure information in China’s historical past or previous will not be offered by the fashions transparently or totally,” famous Unmesh Kulkarni, head of gen AI at knowledge science agency Tredence, in an electronic mail to TechRepublic. “The info privateness implications of calling the hosted mannequin are additionally unclear and most international firms wouldn’t be prepared to try this. Nevertheless, one ought to do not forget that DeepSeek fashions are open-source and could be deployed domestically inside an organization’s non-public cloud or community setting. This is able to tackle the information privateness points or leakage issues.”
Nagli additionally advisable self-hosted fashions when TechRepublic reached him by electronic mail.
“Implementing strict entry controls, knowledge encryption, and community segmentation can additional mitigate dangers,” he wrote. “Organizations ought to guarantee they’ve visibility and governance of all the AI stack to allow them to analyze all dangers, together with utilization of malicious fashions, publicity of coaching knowledge, delicate knowledge in coaching, vulnerabilities in AI SDKs, publicity of AI providers, and different poisonous danger combos that will exploited by attackers.”

