Background: The Distinctive Panorama of the Black Hat NOC
Working the Black Hat Safety and Community Operations Heart (NOC) presents a novel set of challenges and expectations. Not like a typical company atmosphere the place any hacking exercise is straight away deemed malicious, the Black Hat convention is a nexus for cybersecurity analysis, coaching, and moral hacking. Consequently, we anticipate and even count on a major quantity of exercise that, in different contexts, can be thought of extremely suspicious or outright hostile. This consists of numerous types of scanning, exploitation makes an attempt, and different adversarial simulations, usually performed as a part of official trainings or impartial analysis.
Including to this complexity is the Convey Your Personal Machine (BYOD) nature of the convention community. Attendees join a big selection of private units, making conventional endpoint telemetry (like EDR options) a major problem for complete monitoring. As such, our main focus was on strong network-based telemetry for detection and menace looking.
Overview
This writeup particulars a latest investigation inside the Black Hat Safety and Community Operations Heart (SNOC), highlighting the vital function of built-in safety instruments and early detection in mitigating potential threats, notably when originating from inside a high-profile coaching atmosphere.
On August 4, 2025, a Cisco XDR analytics alert flagged “Suspected Port Abuse: Exterior – Exterior Port Scanner.” The alert indicated an inner host from the “Defending Enterprises – 2025 Version” coaching room was actively concentrating on an exterior IP deal with, which resolved to a site belonging to the Def Con cybersecurity convention. This exercise aligned with the MITRE ATT&CK framework’s Reconnaissance tactic (TA0043), particularly the Lively Scanning method (T1595).
Investigation Workflow: A Multi-Instrument Strategy to Speedy Response
Section 1: Assault Triage With Cisco XDR
The Cisco XDR analytics incident supplied the preliminary alert and connection flows, providing speedy visibility into the suspicious community exercise. Detecting this on the reconnaissance part is essential, as early detection within the MITRE ATT&CK chain considerably reduces the danger of an adversary progressing to extra impactful phases.
We noticed a excessive confidence incident involving two IP addresses from an inner subnet connecting with a single exterior IP deal with. The related alert was categorized as a suspected port abuse by Cisco XDR.
Cisco XDR’s ‘Examine’ function then allowed us to additional drill down into and visualized the connection flows related to that exterior IP deal with. It additionally searched towards a number of menace intelligence sources for any popularity related to the observables. The exterior host was not discovered to have a malicious popularity.
Section 2: Goal Identification With Cisco Umbrella
We used Cisco Umbrella (DNS resolver) to verify that the goal IP resolves to a single area. The area seems to be owned by Def Con and hosted in the USA, by Comcast. The direct affiliation with the Def Con Cybersecurity Convention instantly raised considerations about unauthorized reconnaissance towards one other main occasion’s infrastructure.
Cisco Umbrella sensible search lookup of the area confirmed that the area has a low threat and is classed below the “Hacking/Conventions” class. It was confirmed by Cisco Umbrella to belong to the Def Con conference.
Section 3: Visitors Evaluation
Inspecting the NetFlow visitors in XDR analytics offers us a direct perception that port scanning has seemingly occurred.
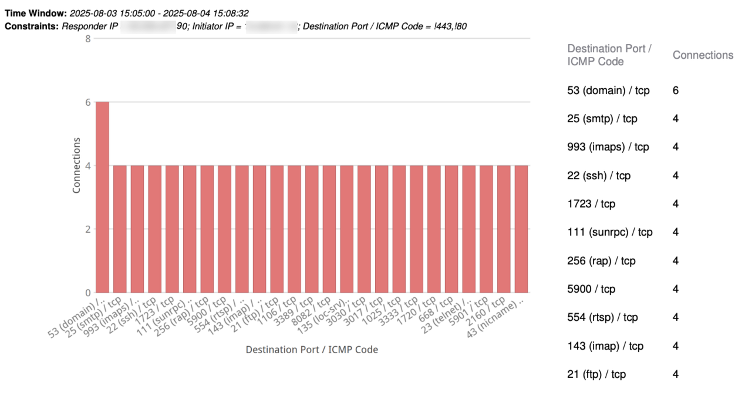
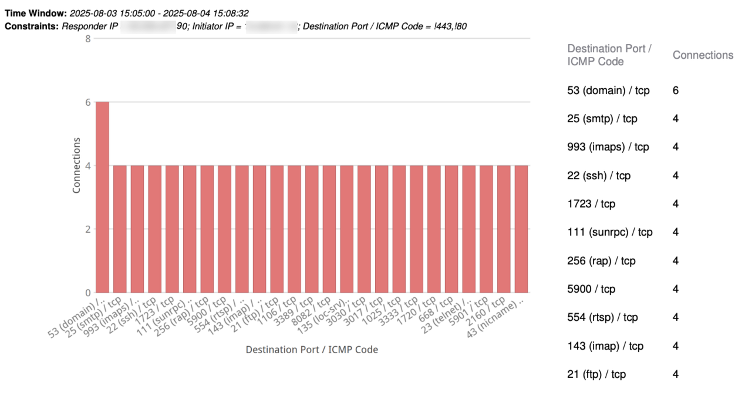
Pivoting into Cisco Firepower Administration Console (FMC), we ran a report of the related visitors from the Cisco Firepower Administration Console.
The report graphed the highest 100 vacation spot ports related to the visitors and painted a really clear image. It confirmed that the inner host was systematically scanning numerous ports on the exterior goal. Notably, we excluded widespread internet ports like 80 and 443, which helped us keep away from doubtlessly reputable visitors. Every port was scanned exactly 4 occasions, indicating a methodical, automated exercise, fully according to a devoted port scan.
For additional validation and quantification, we then queried Palo Alto Networks firewall logs in Splunk Enterprise Safety (ES). The Splunk question confirmed 3,626 scanning occasions between 2025/08/04 17:47:07 and 2025/08/04 18:20:29.
Constant port counts additional validated automated scanning.
Section 4: Wrongdoer Identification
Using our crew’s Slack Bot API, which is built-in with Palo Alto Cortex XSIAM, we had been capable of rapidly establish the supply machine. This included its MAC deal with and hostname, and we pinpointed it as working instantly from the Black Hat coaching room, particularly ‘Defending Enterprises – 2025 Version’:
Lastly, we had been capable of seize the total PCAP of the visitors as further proof, utilizing our full packet seize device, Endace Imaginative and prescient. This investigation confirmed that the unauthorized scanning originated from a pupil in a coaching room. The offender was rapidly recognized and instructed to stop the exercise. The incident was then closed, with continued monitoring of the coaching room and its individuals.
Potential Dangers Highlighted by the Incident
- Reputational Injury: Such incidents can harm the popularity of Black Hat as a premier cybersecurity occasion, eroding belief amongst individuals, companions, and the broader safety group.
- Facilitating illegal Exercise: Extra critically, if left unchecked, these actions may result in Black Hat infrastructure being leveraged for illegal exercise towards exterior third events, doubtlessly leading to authorized repercussions and extreme operational disruptions. Swift detection and remediation are important to uphold belief and stop such outcomes.
Decision and Key Takeaways: Implementing Coverage and the Worth of Swift Motion
The investigation confirmed unauthorized scanning originating by a pupil. Following this, the offender was rapidly recognized and made to stop the exercise. The incident was closed, with continued monitoring of the coaching room.
- The Criticality of Early Detection: This case exemplifies the worth of detecting adversarial exercise on the Reconnaissance part (TA0043) by way of strategies like Lively Scanning (T1595). By figuring out and addressing this conduct early, we prevented potential escalation to extra damaging ways towards an exterior goal.
- Built-in Tooling: The seamless integration of Cisco XDR, Cisco Umbrella, Cisco FMC, Splunk ES, Slack API integration, Endace Imaginative and prescient and Palo Alto Cortex XSIAM enabled fast detection, detailed evaluation, and exact attribution.
- Vigilance in Coaching Environments: Even in managed, academic settings like Black Hat, steady monitoring and swift response are paramount. The dynamic nature of such environments necessitates strong safety controls to stop misuse and preserve community integrity.
- Coverage Enforcement: Clear communication and constant enforcement of community utilization insurance policies are important to handle expectations and stop unauthorized actions, whether or not intentional or experimental.
About Black Hat
Black Hat is the cybersecurity trade’s most established and in-depth safety occasion sequence. Based in 1997, these annual, multi-day occasions present attendees with the most recent in cybersecurity analysis, growth, and traits. Pushed by the wants of the group, Black Hat occasions showcase content material instantly from the group via Briefings shows, Trainings programs, Summits, and extra. Because the occasion sequence the place all profession ranges and tutorial disciplines convene to collaborate, community, and focus on the cybersecurity subjects that matter most to them, attendees can discover Black Hat occasions in the USA, Canada, Europe, Center East and Africa, and Asia. For extra data, please go to the Black Hat web site.
We’d love to listen to what you assume! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media
Share:
