The Cisco Reside Community Operations Middle (NOC) deployed Cisco Umbrella for Area Identify Service (DNS) queries and safety. The Safety Operations Middle (SOC) group built-in the DNS logs into Splunk Enterprise Safety and Cisco XDR.
To guard the Cisco Reside attendees on the community, the default Safety profile was enabled, to dam queries to identified malware, command and management, phishing, DNS tunneling and cryptomining domains. There are events when an individual must go to a blocked area, such a stay demonstration or coaching session.
In the course of the Cisco Reside San Diego 2025 convention, and different conferences we now have labored previously, we now have noticed domains which might be two to 3 phrases in a random order like “alphabladeconnect[.]com” for example. These domains are linked to a phishing marketing campaign and are generally not but recognized as malicious.
Ivan Berlinson, our lead integration engineer, created XDR automation workflows with Splunk to determine Prime Domains seen within the final six and 24 hours from the Umbrella DNS logs, as this can be utilized to alert to an an infection or marketing campaign. We seen that domains that adopted the three random names sample began to exhibiting up, like 23 queries to shotgunchancecruel[.]com in 24 hours.


This acquired me pondering, “Might we catch these domains utilizing code and with our push to make use of AI, may we leverage AI to search out them for us?”
The reply is, “Sure”, however with caveats and a few tuning. To make this attainable, I first wanted to determine the classes of knowledge I wished. Earlier than the domains get marked as malicious, they’re normally categorized as purchasing, ads, commerce, or uncategorized.
I began off operating a small LLM on my Mac and chatting with it to find out if the performance I would like is there. I informed it the necessities of needing to be two-three random phrases, and to inform me if it thinks it’s a phishing area. I gave it a number of domains that we already knew had been malicious, and it was in a position to inform that they had been phishing in line with my standards. That was all I wanted to start out coding.
I made a script to drag down the allowed domains from Umbrella, create a de-duped set of the domains after which ship it to the LLM to course of them with an preliminary immediate being what I informed it earlier. This didn’t work out too properly for me, because it was a smaller mannequin. I overwhelmed it with the quantity of knowledge and rapidly broke it. It began returning solutions that didn’t make sense and totally different languages.
I rapidly modified the habits of how I despatched the domains over. I began off sending domains in chunks of 10 at a time, then acquired as much as 50 at a time since that appeared to be the max earlier than I believed it could develop into unreliable in its habits.
Throughout this course of I seen variations in its responses to the info. It is because I used to be giving it the preliminary immediate I created each time I despatched a brand new chunk of domains, and it could interpret that immediate otherwise every time. This led me to switch the mannequin’s modelfile. This file is used as the foundation of how the mannequin will behave. It may be modified to alter how a mannequin will reply, analyze knowledge, and be constructed. I began modifying this file from being a basic objective, useful assistant, to being a SOC assistant, with consideration to element and responding solely in JSON.
This was nice, as a result of now it was persistently responding to how I wished it to, however there have been many false positives. I used to be getting a few 15–20% false optimistic (FP) fee. This was not acceptable to me, as I wish to have excessive constancy alerts and fewer analysis when an alert is available in.
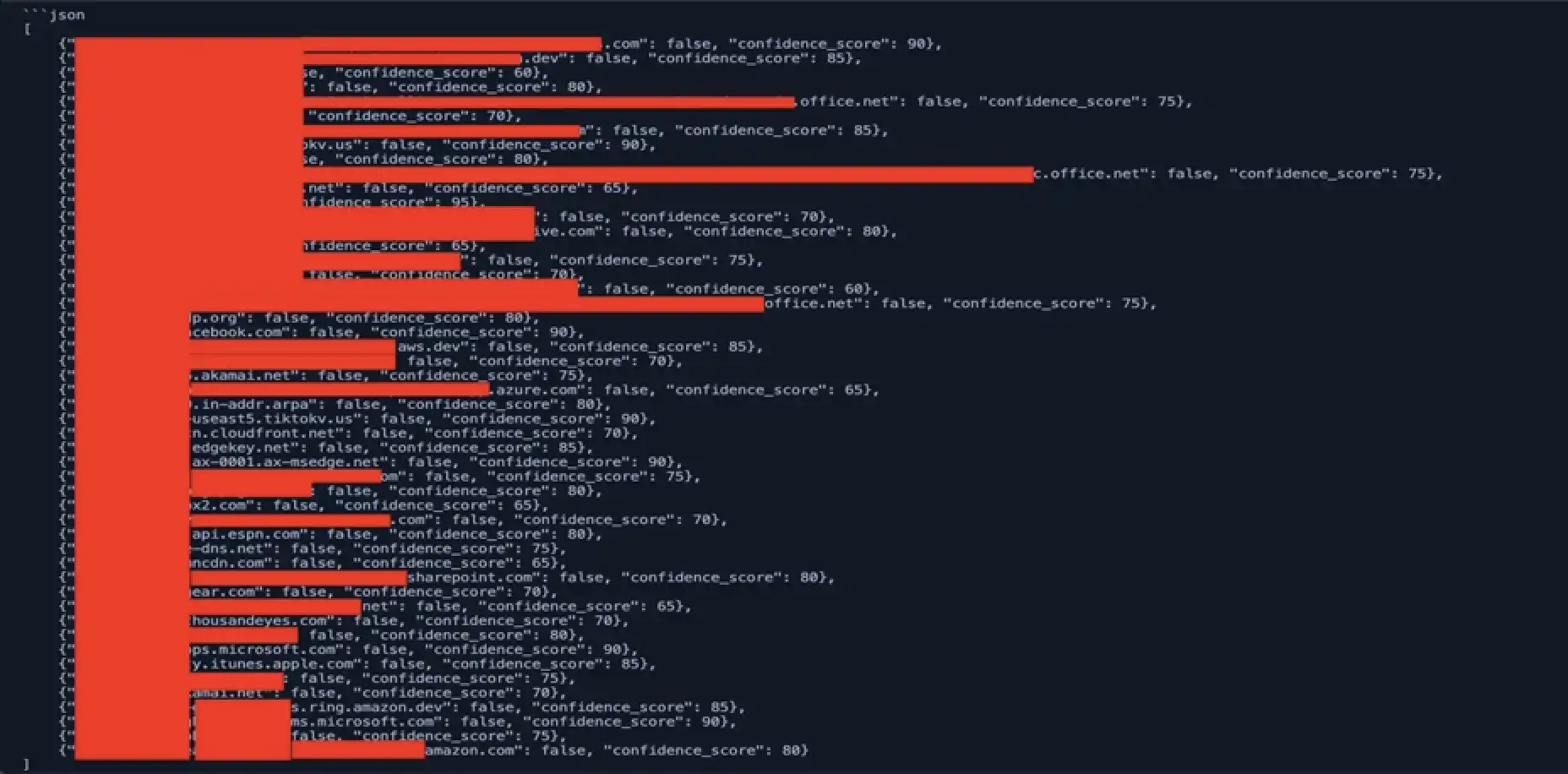
Right here is an instance of the FP fee for 50 at this level and it was oftentimes a lot greater:
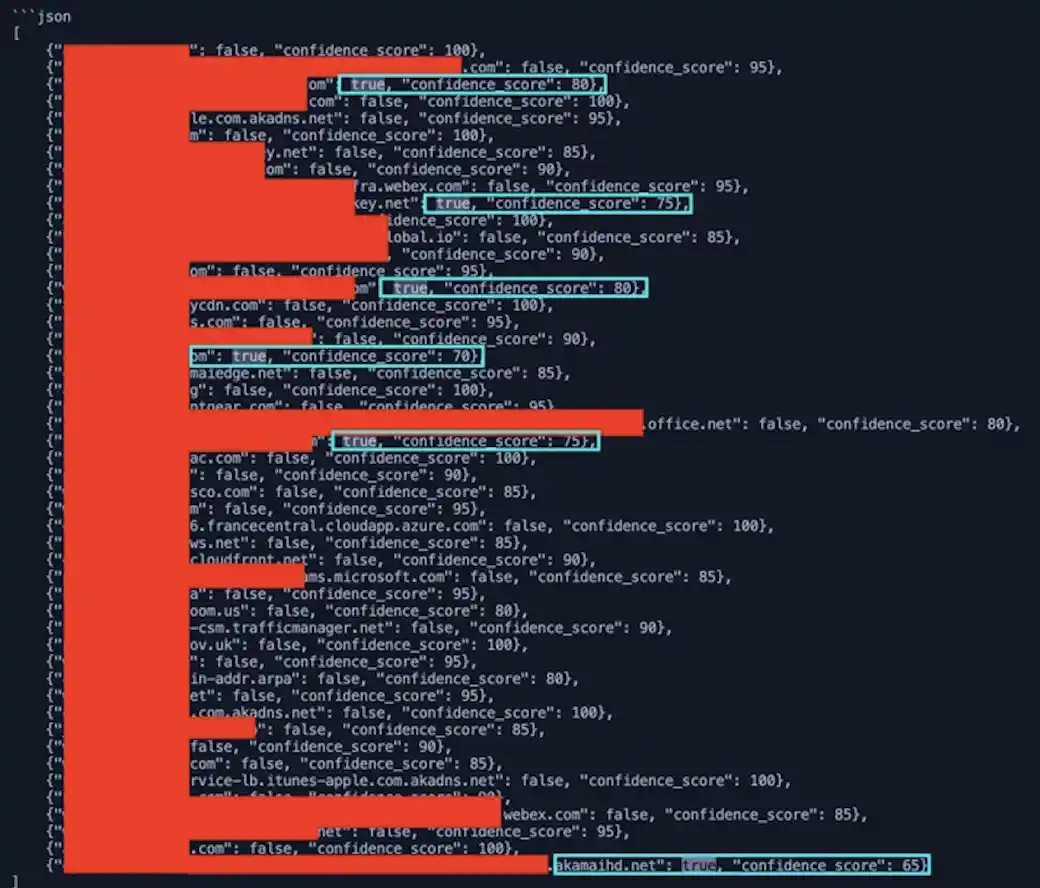
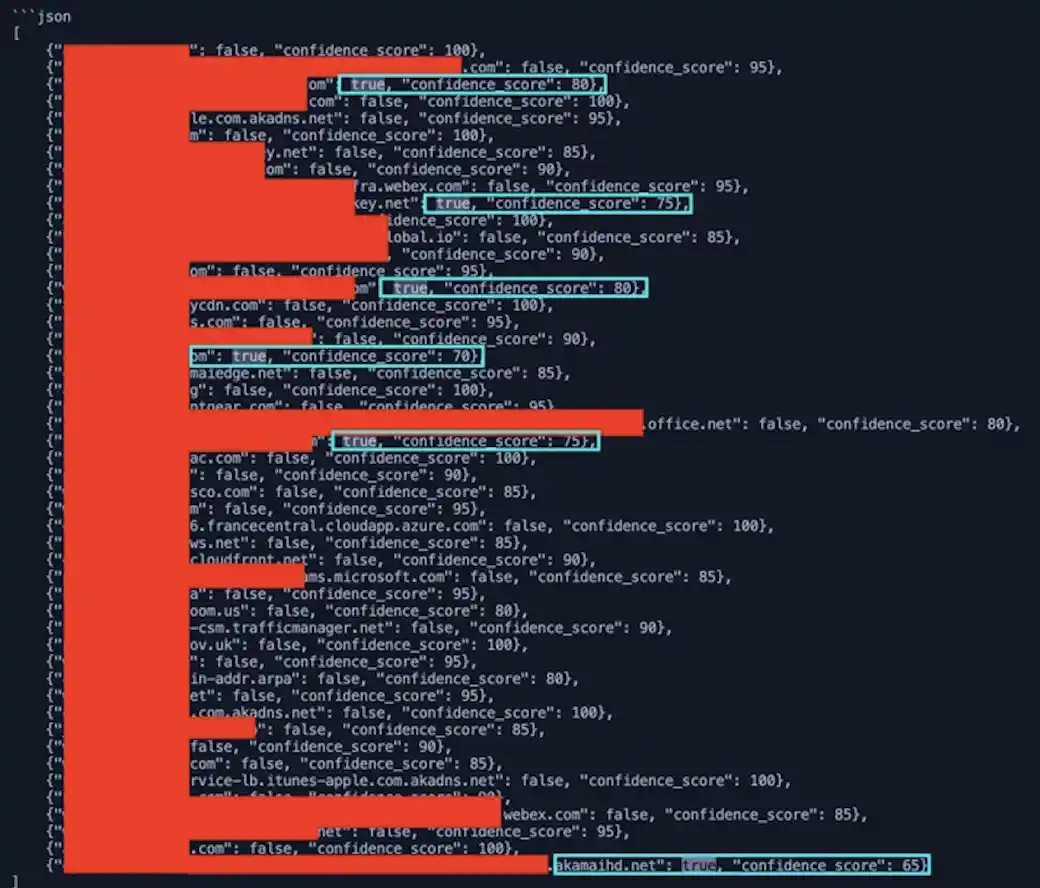
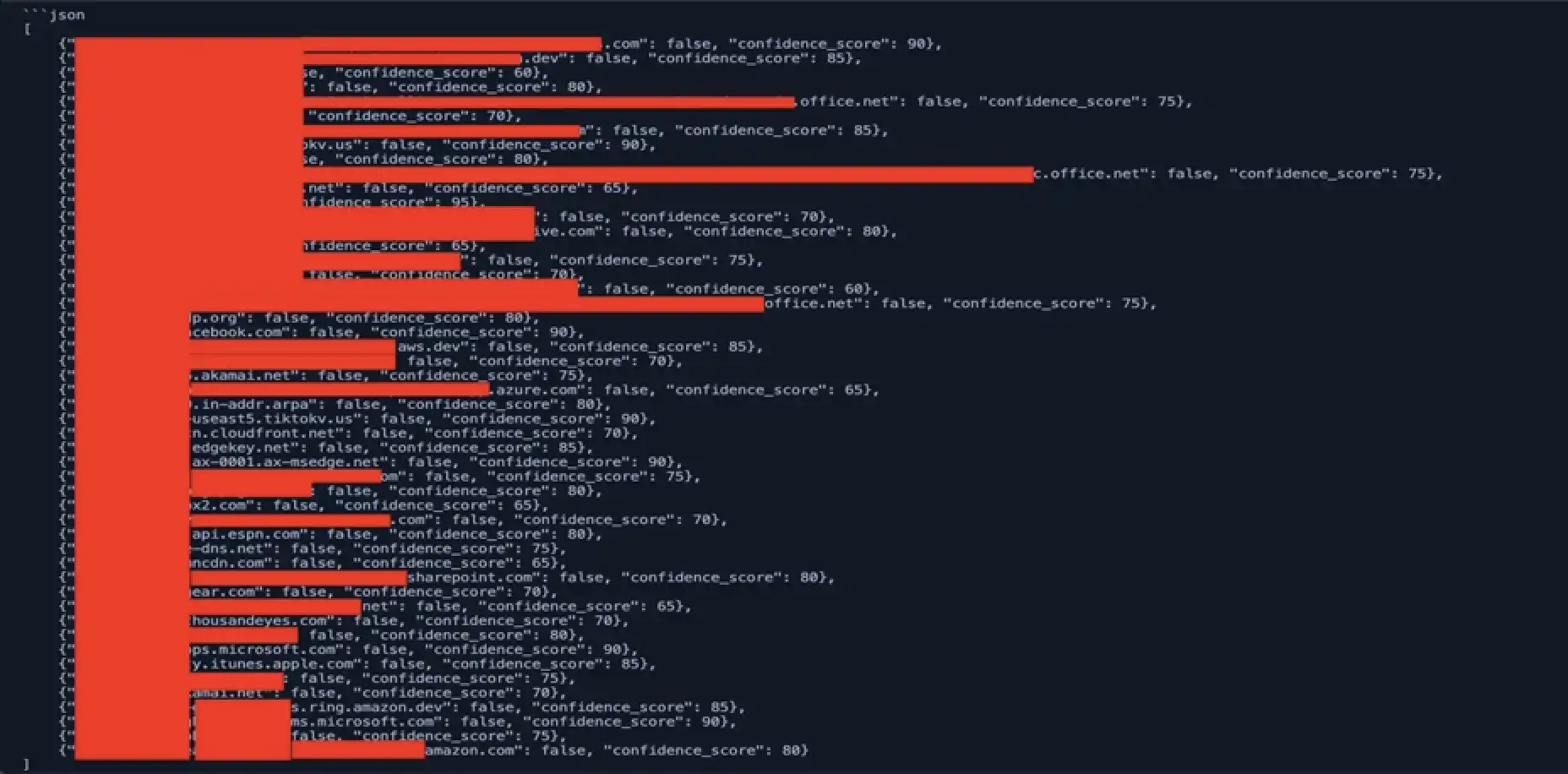
I began tuning the modelfile to inform the mannequin to provide me a confidence rating as properly. Now I used to be in a position to see how assured it was in its willpower. I used to be getting a ton of 100% on domains for AWS, CDNs, and the like. Tuning the modelfile ought to repair that although. I up to date the modelfile to be extra particular in its evaluation. I added that there shouldn’t be any delimiters, like a dot or sprint between the phrases. And I gave it destructive and optimistic samples it may use as examples when analyzing the domains fed to it.
This labored wonders. We went from a 15–20% FP fee to about 10%. 10% is significantly better than earlier than, however that’s nonetheless 100 domains out of 1000 which may must verify. I attempted modifying the modelfile extra to see if I may get the FP fee down, however with no success. I swapped to a more moderen mannequin and was in a position to drop the FP fee to 7%. This exhibits that the mannequin you begin with won’t all the time be the mannequin you find yourself with or will fit your wants probably the most.
At this level, I used to be pretty pleased with it however ideally wish to get the FP fee down even additional. However with the mannequin’s present capabilities, it was in a position to efficiently determine phishing domains that weren’t marked as malicious, and we added them to our block listing. Later, they had been up to date in Umbrella to be malicious.
This was a fantastic feat for me, however I wanted to go additional. I labored with Christian Clasen, our resident Umbrella/Safe Entry knowledgeable and was in a position to get a slew of domains related to the phishing marketing campaign and I curated a coaching set to fantastic tune a mannequin.
This activity proved to be more difficult than I believed, and I used to be not in a position to fantastic tune a mannequin earlier than the occasion ended. However that analysis remains to be ongoing in preparation for Black Hat USA 2025.
We’d love to listen to what you assume! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media
Share:
