This weblog is continuation of the earlier weblog on utilizing Cisco Safe Community Analytics. On this half, we cowl leveraging public Cisco Talos blogs and third-party menace intelligence information with Cisco Safe Community Analytics. Remember to learn the primary half as this half makes references again to Host Group and Customized Safety Occasion directions coated within the authentic weblog.
Cisco Talos Blogs
The gifted researchers at Cisco Talos commonly publish blogs on threats and vulnerabilities. These blogs break down the techniques, strategies and procedures (TTPs) utilized by menace actors. Talos’ analysis publications typically embrace pattern supply code, phishing emails, reverse engineering of malicious binaries, instruments, scripts, command and management methodology, attacker infrastructure, file hashes, domains and IP addresses utilized in malicious operations. The indications of compromise (IOCs) are revealed on GitHub as JSON and plain textual content information. We are able to use these blogs and GitHub information to construct Customized Safety Occasions in Cisco Safe Community Analytics.
Let’s take a look at a weblog: MoonPeak malware from North Korean actors unveils new particulars on attacker infrastructure. This weblog focuses on a state-sponsored group from North Korea. The group leverages an open-source distant entry trojan (RAT) from a household being known as MoonPeak.

Scroll by means of the article and take note of the extent of element supplied. Close to the very backside of the weblog discover the part titled IOCs.
Click on on the hyperlink to the GitHub repository. You may be taken to the Cisco Talos GitHub repository the place you can find the IOCs can be found as JSON and plain textual content information, and are sorted by the month the weblog was revealed in. Be happy to discover different information, months, and years to get conversant in the symptoms commonly supplied.
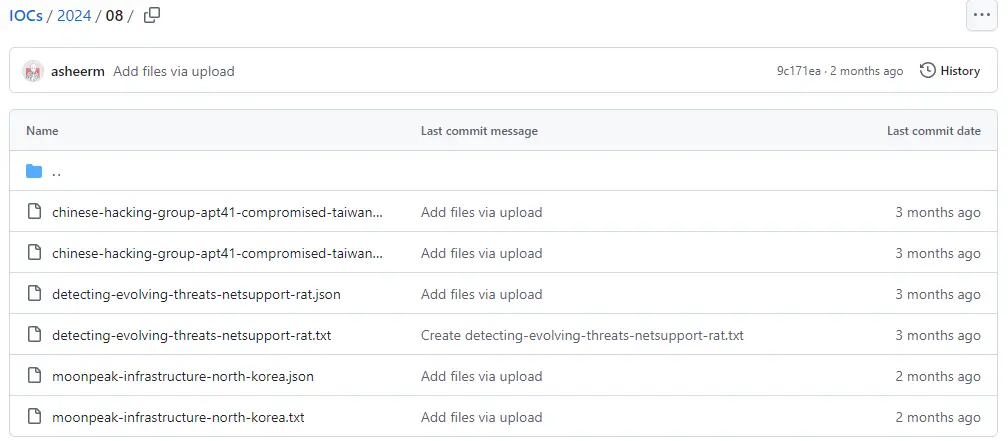
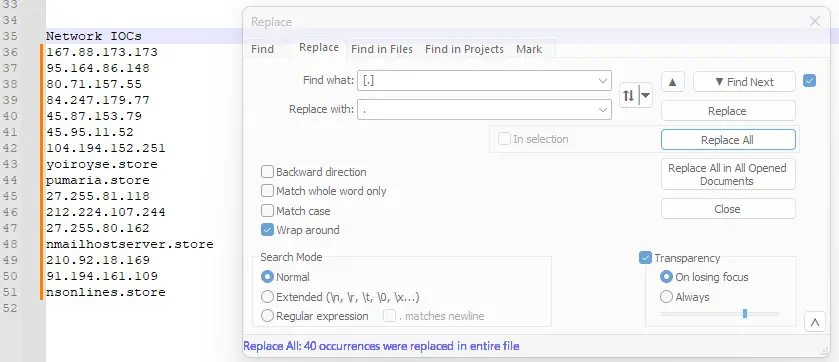
Click on on the file “moonpeak-infrastructure-north-korea.txt” or comply with the direct hyperlink. Scroll all the way down to line 35 of the file the place the Community IOCs start. This record incorporates twelve IP addresses we’re keen on. Observed that the IP addresses and domains have been defanged with sq. brackets across the dots so you can not by chance click on on them.
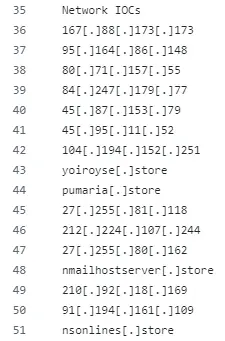
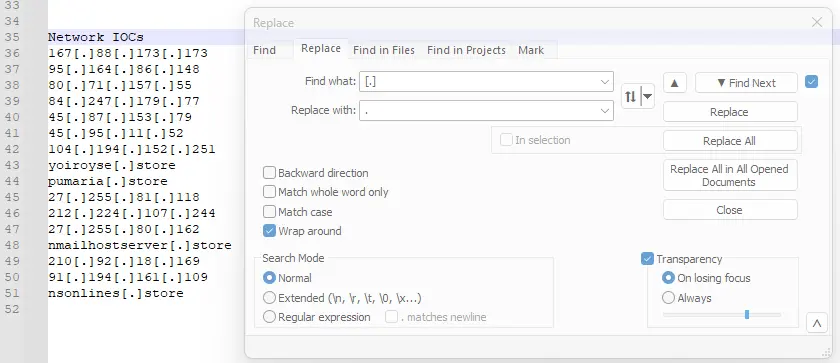
You possibly can both manually delete the sq. brackets or use the discover and substitute performance in your favourite textual content editor to do the job. I favor to make use of Notepad++ when coping with textual content information. I set the “Discover and Substitute” to search for the sq. brackets across the dot and substitute all cases with a dot.
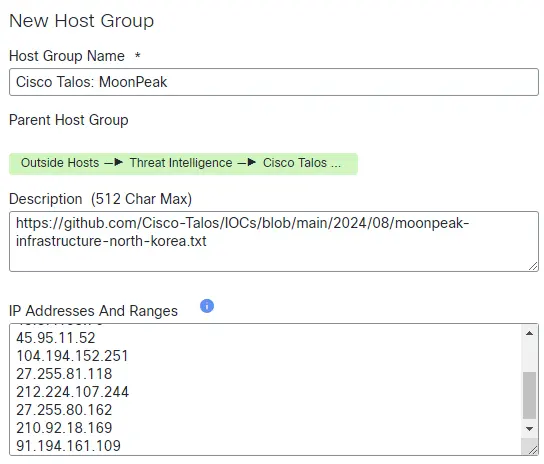
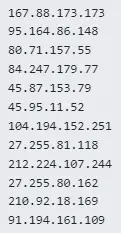
Delete the domains from the record and replica and paste these IP addresses right into a New Host Group utilizing the strategies described within the first a part of this weblog.
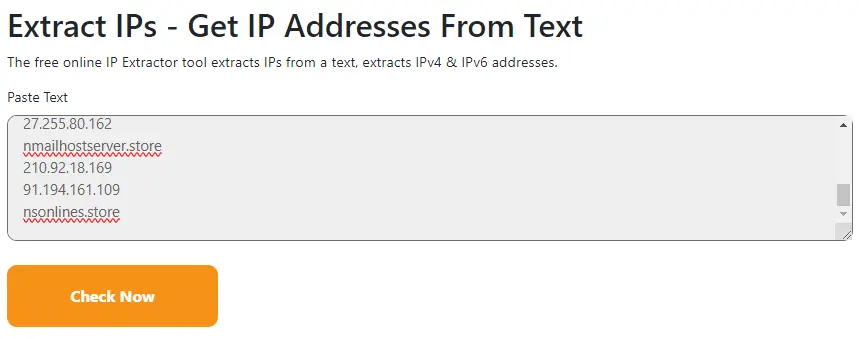
You might also think about using a instrument to extract IP addresses from textual content. I actually like iplocation IP Extractor. You possibly can paste in a block of textual content with IPv4 and IPv6 IP addresses and it’ll extract them to allow them to be simply reviewed and pasted into a bunch group. The IPs you paste into this instrument can’t be defanged. It requires full and proper IP addresses to work.
All the time take into account the sensitivity of the knowledge you present to public instruments earlier than utilizing them. You need to take into account a regionally hosted instrument for delicate info
Third-party menace intelligence
If you happen to take part in any Info Sharing and Evaluation Facilities (ISACs), subscribe to industrial feeds or commonly make the most of bulletins and blogs geared in the direction of your business, you can even make the most of their indicators in Cisco Safe Community Analytics. They work the identical method we dealt with inside menace intelligence within the first a part of this weblog or Cisco Talos blogs proven above. Watch out when scraping menace intelligence to make certain you’re solely together with indicators you plan to make use of. For instance, if you’re scraping a complete bulletin that incorporates IP addresses you have an interest in, be sure you don’t by chance copy an IP deal with from an adjoining and unrelated entry.
You possibly can paste a block of IP addresses right into a New Host Group or use a instrument to drag them out of a block of textual content after which paste them. Watch out in case your supply defangs IP addresses, as this is quite common. You should use the identical strategies I illustrated for the Cisco Talos GitHub entries above.
Host group mum or dad/baby relationships
A great observe for constructing mum or dad and baby host teams is to create a brand new mum or dad host group for any distinct sources. Then create a toddler host group for every new report. This lets you simply monitor again each to the unique supply or the menace intelligence and determine which marketing campaign or menace actor is concerned. I like to incorporate a hyperlink to the supply within the host group description. That is particularly useful if you’re using a number of menace intelligence sources in your safety controls. Arrange your host teams in a fashion that makes essentially the most sense to you.
You possibly can both create a brand new Customized Safety Occasion (see the primary a part of this weblog) for every baby host group with a definite title or create one Customized Safety Occasion for the mum or dad host group with a generic title. Both case may have you coated, and the host group title within the alarm will aid you rapidly determine the supply of menace intelligence.
Different Concerns
You at all times need to carry out a Move Search (Examine -> Move Search) first earlier than constructing any Customized Safety Occasions. It will stop you from flooding your self with alerts should you by chance embrace the flawed IP deal with or are already commonly speaking with an IP deal with you plan to incorporate in a brand new host group.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Related with Cisco Safe on social!
Cisco Safety Social Channels
Share:
