
A brand new malicious bundle known as ‘SteelFox’ mines for cryptocurrency and steals bank card knowledge through the use of the “carry your personal susceptible driver” method to get SYSTEM privileges on Home windows machines.
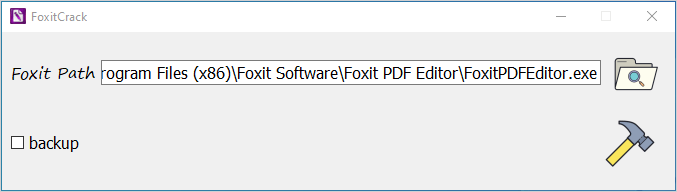
The malware bundle dropper is distributed via boards and torrent trackers as a crack device that prompts authentic variations of varied software program like Foxit PDF Editor, JetBrains and AutoCAD.
Utilizing a susceptible driver for privilege escalation is widespread for state-sponsored menace actors and ransomware teams. Nevertheless, the method now seems to increase to info-stealing malware assaults.
Kaspersky researchers found the SteelFox marketing campaign in August however say that the malware has been round since February 2023 and elevated distribution these days utilizing a number of channels (e.g. torrents, blogs, and posts on boards).
Based on the corporate, its merchandise detected and blocked SteelFox assaults 11,000 instances.
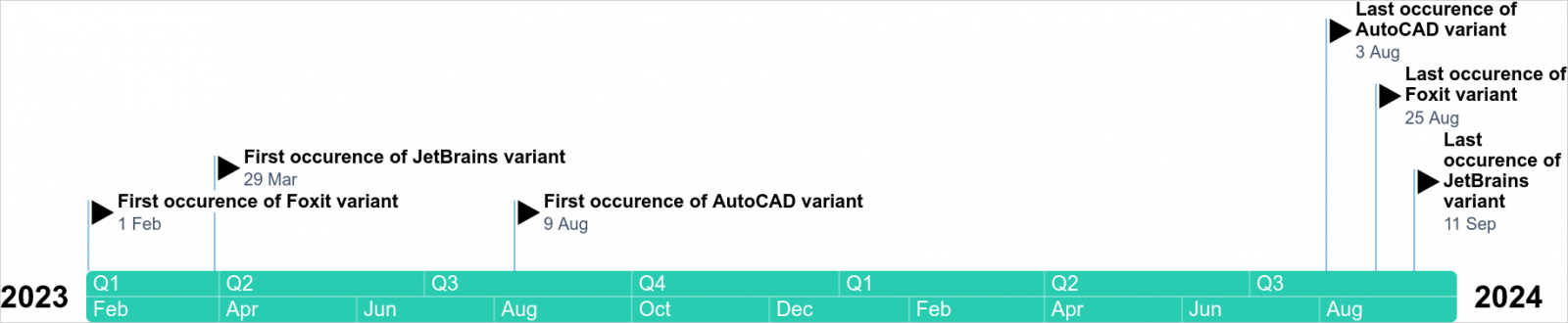
Supply: Kaspersky
SteelFox an infection and privilege escalation
Kaspersky experiences that malicious posts selling the SteelFox malware dropper include full directions on easy methods to illegally activate the software program. Under is a pattern of such a put up offering instructions on easy methods to activate JetBrains:
.jpg)
Supply: Kaspersky
The researchers say that whereas the dropper does have the marketed performance, customers additionally infect their methods with malware.
For the reason that software program focused for unlawful activation is often put in within the Program Information, including the crack requires administrator entry, a permission that the malware makes use of later within the assault.
Supply: Kaspersky
Kaspersky researchers say that “the execution chain appears to be like authentic till the second the recordsdata are unpacked.” They clarify {that a} malicious operate is added throughout the course of, which drops on the machine code that masses SteelFox.
Having secured admin rights, SteelFox creates a service that runs WinRing0.sys inside, a driver susceptible to CVE-2020-14979 and CVE-2021-41285, which might be exploited to acquire privilege escalation to NT/SYSTEM degree.
Such permissions are the best on a neighborhood system, extra highly effective than an administrator’s, and permit unrestricted entry to any useful resource and course of.
The WinRing0.sys driver can be used for cryptocurrency mining, as it’s a part of the XMRig program for mining Monero cryptocurrency. Kaspersky researchers say that the menace actor makes use of a modified model of the miner executable that connects to a mining pool with hardcoded credentials.
The malware then establishes a reference to its command-and-control (C2) server utilizing SSL pinning and TLS v1.3, which protects the communication from being intercepted.
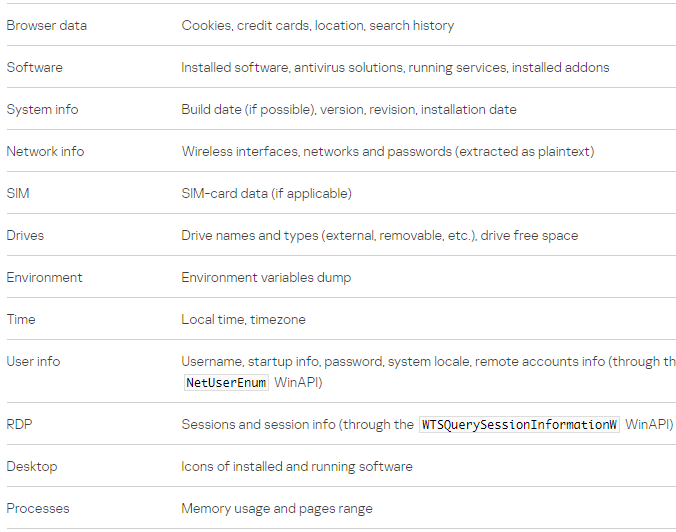
It additionally prompts the info-stealer element that extracts knowledge from 13 internet browsers, details about the system, community, and RDP connection.
Supply: Kaspersky
The researchers word that SteelFox collects from the browsers knowledge like bank cards, looking historical past, and cookies.
Kaspersky says that though the C2 area SteelFox makes use of is hardcoded, the menace actor manages to cover it by switching its IP addresses and resolving them via Google Public DNS and DNS over HTTPS (DoH).
SteelFox assaults don’t have particular targets however seem to deal with customers of AutoCAD, JetBrains, and Foxit PDF Editor. Based mostly on Kaspersky’s visibility, the malware compromises methods in Brazil, China, Russia, Mexico, UAE, Egypt, Algeria, Vietnam, India, and Sri Lanka.
Though SteelFox is pretty new, “it’s a full-featured crimeware bundle,” the researchers say. Evaluation of the malware signifies that it is developer is expert in C++ programming and so they managed to create formidable malware by integrating exterior libraries.
