Microsoft Risk Intelligence has uncovered a brand new assault marketing campaign by Russian risk actor Midnight Blizzard, focusing on 1000’s of customers throughout over 100 organizations. The assault leverages spear-phishing emails with RDP configuration recordsdata, permitting attackers to connect with and probably compromise the focused methods.
The assault marketing campaign focused 1000’s of customers in increased schooling, protection, non-governmental organizations, and authorities businesses. Dozens of nations have been impacted, notably within the U.Ok., Europe, Australia, and Japan, which is in keeping with earlier Midnight Blizzard phishing campaigns.
Phishing emails contained RDP configuration file
Within the newest Midnight Blizzard assault marketing campaign, victims obtained extremely focused emails that used social engineering lures regarding Microsoft, Amazon Net Companies, and the idea of Zero Belief.
In keeping with Microsoft Risk Intelligence, the emails had been despatched utilizing e-mail addresses belonging to respectable organizations, gathered by the risk actor throughout earlier compromises. All emails contained a RDP configuration file, signed with a free LetsEncrypt certificates, that included a number of delicate settings.
When a consumer opened the file, an RDP connection could be established to an attacker-controlled system. The configuration of the established RDP connection would then enable the risk actor to gather details about the focused system, similar to recordsdata and folders, related community drives, peripherals together with printers, microphones, and sensible playing cards.
It might additionally allow the gathering of clipboard information, internet authentication utilizing Home windows Hi there, passkeys and safety keys, and even Level-of-Sale gadgets. Such a connection may additionally enable the risk actor to put in malware on the focused system or on mapped community share(s).
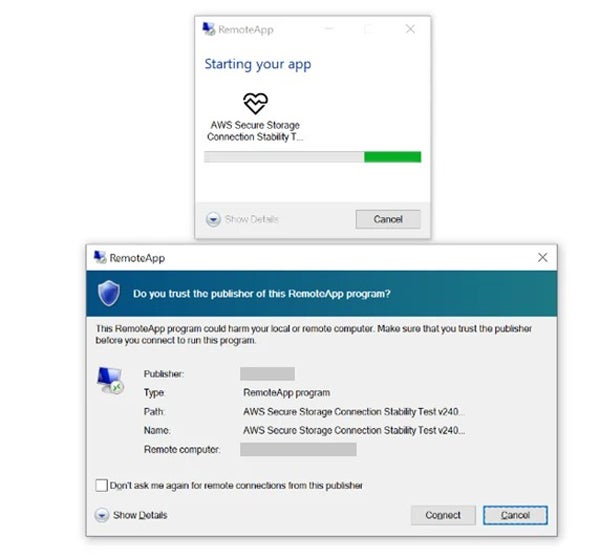
The outbound RDP connections had been established to domains created to trick the goal into believing they had been AWS domains. Amazon, working with the Ukrainian CERT-UA on preventing the risk, instantly initiated the method of seizing affected domains to disrupt the operation. In the meantime, Microsoft straight notified impacted prospects which have been focused or compromised.
Midnight Blizzard has focused varied sectors lately
In keeping with a joint cybersecurity advisory, Midnight Blizzard, in addition to risk actors APT29, Cozy Bear, and the Dukes, are related to the Russian Federation Overseas Intelligence Service.
Since at the least 2021, Midnight Blizzard has routinely focused U.S., European, and world entities within the Protection, Expertise, and Finance sectors, pursuing cyberespionage functions and enabling additional cyber operations, together with in help of Russia’s ongoing invasion of Ukraine.
SEE: Find out how to Create an Efficient Cybersecurity Consciousness Program (TechRepublic Premium)
In January 2024, the group focused Microsoft and Hewlett Packard Enterprise, getting access to e-mail packing containers of a number of workers. Following the incident, Microsoft said that the cybercriminals had been initially focusing on e-mail accounts for data associated to Midnight Blizzard itself.
Then, in March 2024, the risk actor reportedly tailored its ways to focus on extra cloud environments.
In keeping with Microsoft, Midnight Blizzard is likely one of the stealthiest cyberattackers. As a separate Microsoft report famous, the group had beforehand disabled the group’s Endpoint Detection and Response options after a system reboot. They then waited quietly for a month for computer systems to reboot and took benefit of weak computer systems that had not been patched.
The risk actor can also be extremely technical, because it has been noticed deploying MagicWeb, a malicious DLL positioned on Energetic listing Federated Companies servers to remain persistent and steal data. The instrument additionally permits the Midnight Blizzard to generate tokens that enable it to bypass AD FS insurance policies and register as any consumer.
Find out how to shield in opposition to Midnight Blizzard
A number of actions may be taken to guard from this risk:
- Outbound RDP connections to exterior or public networks must be forbidden or restricted.
- RDP recordsdata must be blocked from e-mail shoppers or webmail.
- RDP recordsdata must be blocked from being executed by customers.
- Multi-factor authentication have to be enabled the place potential.
- Phishing-resistant authentication strategies must be deployed, similar to utilizing FIDO tokens. SMS-based MFA shouldn’t be used, as it might be bypassed by SIM-jacking assaults.
- Conditional Entry Authentication Energy have to be carried out to require phishing-resistant authentication.
Moreover, Endpoint Detection and Response (EDR) have to be deployed to detect and block suspicious exercise. Organizations must also take into account deploying antiphishing and antivirus options to assist detect and block the risk.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.
