
The North Korean Lazarus hacking group exploited a Google Chrome zero-day tracked as CVE-2024-4947 by way of a faux decentralized finance (DeFi) recreation concentrating on people within the cryptocurrency house.
Kaspersky found the assaults on Might 13, 2024, and reported the Chrome zero-day flaw to Google.
Google issued a repair for CVE-2024-4947 on Might 25, with Chrome model 125.0.6422.60/.61.
Lazarus tank video games
Kaspersky found the marketing campaign, which began in February 2024, after detecting a brand new variant of the “Manuscrypt” backdoor malware on the non-public laptop of certainly one of its clients in Russia.
Lazarus has been utilizing Manuscrypt for years, however the researchers had been intrigued by the risk actor’s atypical concentrating on scope, which seemingly included random people.
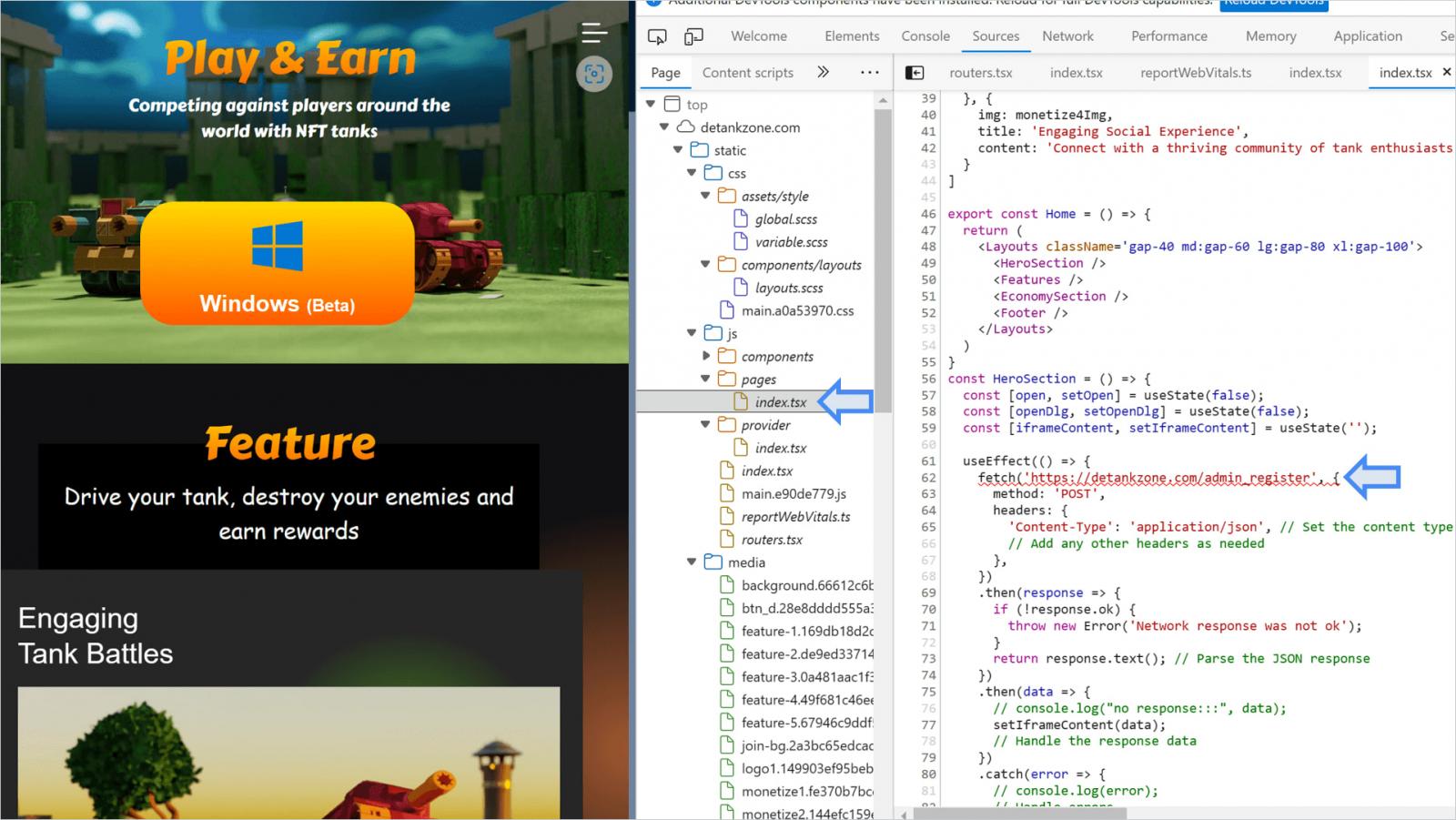
Additional telemetry confirmed that Google Chrome was exploited previous to the detection of the brand new Manuscrypt payload, with the exploitation originating from the “detankzone[.]com” web site. This web site promoted an NFT-based multiplayer on-line battle enviornment (MOBA) recreation themed round tanks named DeTankZone.
Lazarus promoted the sport closely by way of promoting campaigns on social media platforms like X, spear-phishing emails, and premium LinkedIn accounts utilized in direct assaults on high-value targets.
Upon downloading and reserve engineering the sport, Kaspersky found the sport was primarily based on stolen supply code from a professional recreation named DeFiTankLand, which Lazarus had merely rebranded for his or her functions.
The 400MB ZIP obtain launches as anticipated, but it surely doesn’t work previous the login/registration display screen because the backend infrastructure for the sport was shut down. Moreover, it didn’t carry out any malicious actions on the goal’s system.
The Google Chrome exploitation occurs on the detankzone[.]com web site itself, which contained a hidden script (index.tsx) designed to set off an exploit for CVE-2024-4947, a sort confusion in V8, Chrome’s Javascript engine.
Supply: Kaspersky
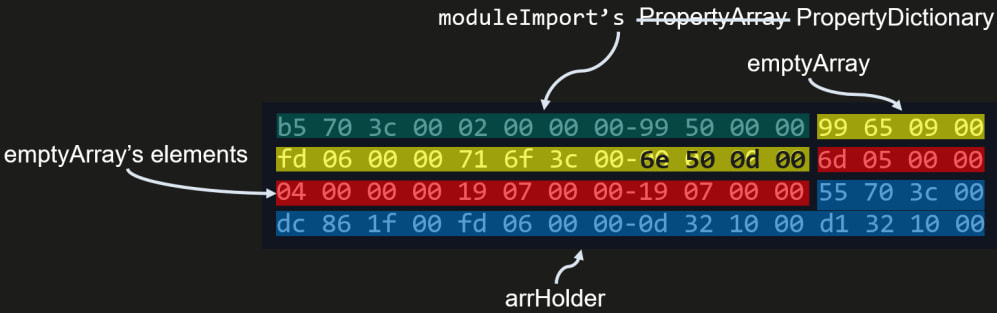
Lazarus’ exploit script corrupted Chrome’s reminiscence by leveraging the app’s JIT compiler, Maglev, overwriting sections that ultimately gave them entry to all the deal with house of Chrome’s course of.
At this stage, the attackers may entry cookies, authentication tokens, saved passwords, and shopping historical past.
Supply: Kaspersky
Chrome’s V8 sandbox isolates JavaScript execution from the remainder of the system, so Lazarus used a second flaw in V8 to flee it and obtain distant code execution, executing shellcode within the system’s reminiscence.
“This concern (330404819) was submitted and stuck in March 2024,” explains Kaspersky concerning the V8 escape flaw.
“It’s unknown whether or not it was a bug collision and the attackers found it first and initially exploited it as a 0-day vulnerability, or if it was initially exploited as a 1-day vulnerability.”
The shellcode Lazarus used serves as a reconnaissance device, serving to the attackers decide if the compromised machine is efficacious sufficient to proceed the assault.
It collected CPU, BIOS, and OS data, carried out anti-VM and anti-debugging checks, and despatched the data to Lazarus’ command-and-control (C2) server.
Kaspersky didn’t have the possibility to look at the next assault steps, as, by the point of their evaluation, Lazarus had eliminated their exploit from the decoy website.
Nonetheless, primarily based on the folks the malicious marketing campaign focused and their previous historical past, the assault’s final objective was prone to steal cryptocurrency.
