Microsoft’s August 2024 Patch Tuesday launch was, in a single sense, a respite from July’s 138-CVE torrent of fixes, with simply 85 CVEs addressed in the primary launch. Nonetheless, with over two dozen advisories, quite a lot of “informational” notices regarding materials launched in June and July, two high-profile points for which the fixes are nonetheless a piece in progress, and over 85 Linux-related CVEs coated within the launch, directors might discover their patch prioritization particularly advanced this month.
At patch time, 5 of the problems addressed are recognized to be underneath exploit within the wild. Three extra are publicly disclosed. Microsoft assesses that 11 CVEs, all in Home windows, are by the corporate’s estimation extra prone to be exploited within the subsequent 30 days. 9 of this month’s points are amenable to detection by Sophos protections, and we embrace info on these in a desk under.
Along with these patches, the discharge consists of advisory info on 12 patches from Adobe, 9 for Edge through Chrome (along with three Edge patches from Microsoft), and the often launched servicing stack replace (ADV990001). The corporate additionally supplied info on 5 CVEs addressed earlier this summer season however not introduced of their respective months (one in June, 4 in July). We’ll record these in Appendix D under; those that have already utilized the patches for these months are already protected and needn’t apply them once more. (It needs to be famous that one subject patched in June, CVE-2024-38213, is underneath energetic assault within the wild – argument for making use of patches as quickly as potential after launch.) Microsoft additionally took pains this month to flag three different CVEs for which fixes have already gone out, however which are included in Patch Tuesday info for transparency’s sake; we record these in Appendix D as properly. We’re as at all times together with on the finish of this publish further appendices itemizing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product household.
Lastly, this month’s launch consists of a big cohort of CVEs associated to CBL-Mariner, or in some circumstances to each Mariner and Azure Linux. (Mariner was renamed Azure Linux earlier this yr, however the info supplied by Microsoft on these CVEs differentiates between the 2.) The CVEs come from a timespan from 2007 to 2024; the CVSS base scores vary from 3.2 to a “good” 10. These CVEs usually are not included within the knowledge in the primary a part of this publish, however we have now listed all 84 CVEs in Appendix E on the finish of this text for reference. Two further Mariner / Azure Linux CVEs additionally contact Home windows, and people two are included within the statistics in the primary article in addition to in Appendix E’s record.
The info in the primary a part of this publish displays solely the 85 CVEs within the non-Mariner, non-advisory portion of the discharge.
By the numbers
- Complete CVEs: 85
- Complete Edge / Chrome advisory points coated in replace: 9 (plus 3 non-advisory Edge points)
- Complete non-Edge Microsoft advisory points coated in replace: 9
- Complete Adobe points coated in replace: 12
- Publicly disclosed: 3
- Exploited: 5
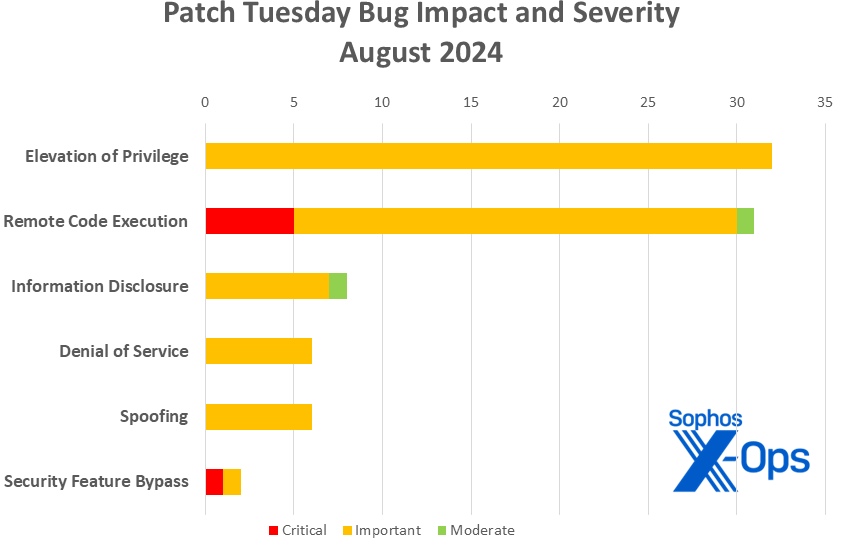
- Severity
- Essential: 6
- Vital: 77
- Average: 2
- Impression
- Elevation of Privilege: 32
- Distant Code Execution: 31
- Info Disclosure: 8
- Denial of Service: 6
- Spoofing: 6
- Safety Characteristic Bypass: 2
Determine 1: The six critical-severity vulnerabilities addressed in August’s Patch Tuesday launch embrace the second this yr involving safety function bypass. (This chart doesn’t signify the Mariner-related points mentioned elsewhere on this article)
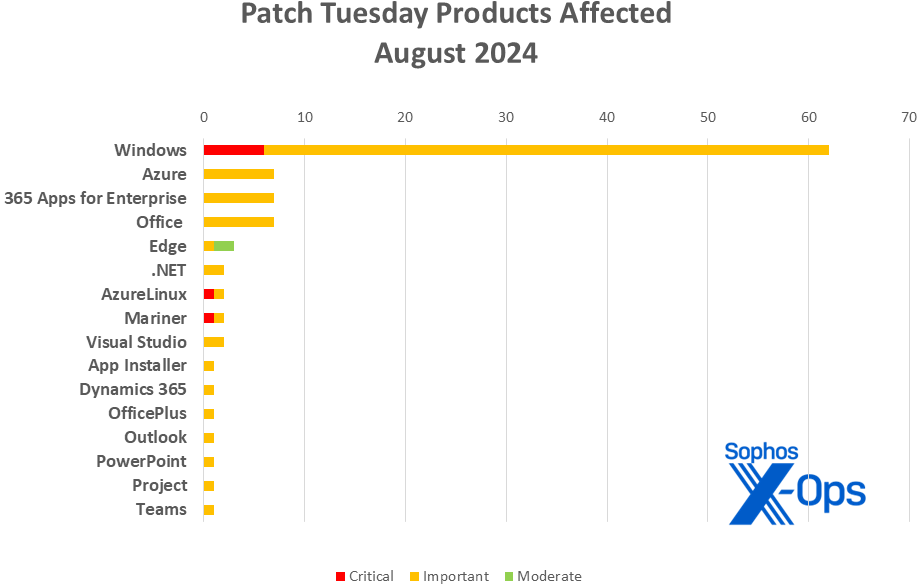
Merchandise
- Home windows: 62
- Azure: 7
- 365 Apps for Enterprise: 7
- Workplace: 7
- Edge: 3 (plus 9 advisories through Chrome)
- .NET: 2
- Azure Linux: 2
- CBL-Mariner: 2
- Visible Studio: 2
- App Installer: 1
- Dynamics 365: 1
- OfficePlus: 1
- Outlook: 1
- PowerPoint: 1
- Mission: 1
- Groups: 1
As is our customized for this record, CVEs that apply to a couple of product household are counted as soon as for every household they have an effect on.
Determine 2: All kinds of product households are affected by August’s patches; at the least one, App Installer, is so obscure that Microsoft has included a hyperlink to info on it within the launch itself, together with info on updating it through winget. Nonetheless, Home windows as ever guidelines the roost
Notable August updates
Along with the problems mentioned above, quite a lot of particular objects advantage consideration.
CVE-2024-21302 – Home windows Safe Kernel Mode Elevation of Privilege Vulnerability
CVE-2024-38202 – Home windows Replace Stack Elevation of Privilege Vulnerability
These two Vital-severity issued have been debuted by researcher Alon Leviev final week at Black Hat final week after a protracted responsible-disclosure course of. Microsoft has been engaged on the answer for six months, however it wants a bit of extra time to untangle this advanced subject with Virtualization-Primarily based Safety (VBS). For now, Microsoft is publishing mitigation info for each CVE-2024-21302 and CVE-2024-38202 on their web site.
CVE-2024-38063 – Home windows TCP/IP Distant Code Execution Vulnerability
There are three CVEs on this launch with a 9.8 CVSS base rating, however solely this one has the excellence of additionally being, in Microsoft’s estimation, extra prone to be exploited within the subsequent thirty days. That’s unlucky, as a result of this critical-severity RCE bug requires neither privileges nor consumer interplay. An attacker might exploit this subject by repeatedly sending IPv6 packets, with specifically crafted IPv6 packets combined in, to a Home windows machine with IPv6 enabled. (Machines which have IPv6 disabled wouldn’t be affected by this assault.) Sophos has launched protections (Exp/2438063-A) for this subject, as famous within the desk under.
CVE-2024-38213 – Home windows Mark of the Net Safety Characteristic Bypass Vulnerability
This subject is without doubt one of the 5 famous above that was truly patched months in the past (on this case, June 2024). Those that have utilized the patches launched in June are protected; those that haven’t utilized the patches ought to achieve this, as the difficulty is at the moment underneath energetic assault.
[42 CVEs] Home windows 11 24H2 patches, already
Although Home windows 11 24H2 is just not but typically launch, just below half of the problems addressed this month apply to that working system. Customers of the brand new Copilot+ PCs who don’t ingest their patches mechanically ought to be sure you replace their gadgets; those that do ought to have taken all of the related patches with the most recent cumulative replace, which elevates these gadgets to Construct 26100.1457.
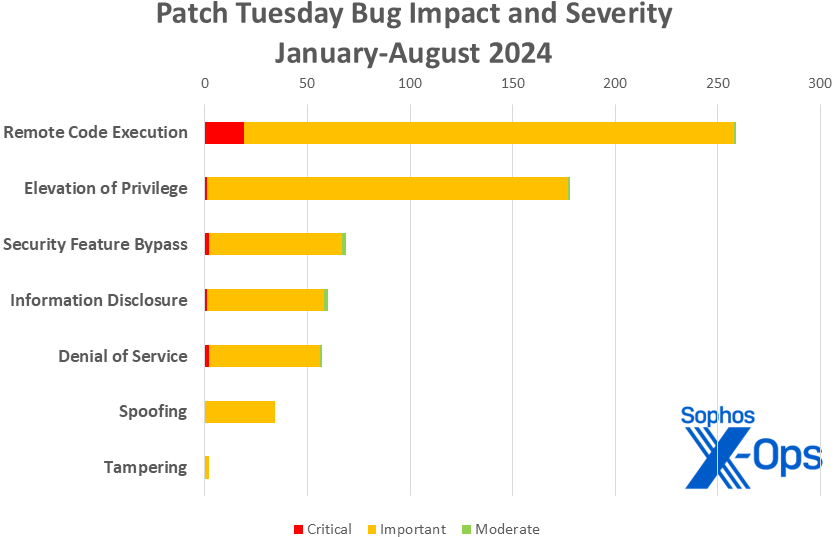
Determine 3: With a complete of 659 CVEs addressed in Patch Tuesday releases to this point in 2024, Microsoft’s coping with a far heavier quantity than they have been at this level in 2023 (491 patches), however a bit lower than they dealt with in 2022 (690 patches). That stated, this desk doesn’t embrace the 84 Mariner-released CVEs mentioned elsewhere on this publish
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2024-38063 | Exp/2438063-A | |
| CVE-2024-38106 | Exp/2438106-A | |
| CVE-2024-38141 | Exp/2438141-A | |
| CVE-2024-38144 | Exp/2438144-A | |
| CVE-2024-38147 | Exp/2438147-A | |
| CVE-2024-38150 | Exp/2438150-A | |
| CVE-2024-38178 | 2309977 | |
| CVE-2024-38193 | Exp/2438193-A | |
| CVE-2024-38196 | Exp/2438196-A |
As you possibly can each month, in case you don’t need to wait in your system to tug down Microsoft’s updates itself, you possibly can obtain them manually from the Home windows Replace Catalog web site. Run the winver.exe device to find out which construct of Home windows 10 or 11 you’re operating, then obtain the Cumulative Replace package deal in your particular system’s structure and construct quantity.
Appendix A: Vulnerability Impression and Severity
It is a record of August patches sorted by impression, then sub-sorted by severity. Every record is additional organized by CVE.
Elevation of Privilege (32 CVEs)
| Vital severity | |
| CVE-2024-21302 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-29995 | Home windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-38084 | Microsoft OfficePlus Elevation of Privilege Vulnerability |
| CVE-2024-38098 | Azure Linked Machine Agent Elevation of Privilege Vulnerability |
| CVE-2024-38106 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38107 | Home windows Energy Dependency Coordinator Elevation of Privilege Vulnerability |
| CVE-2024-38117 | Home windows Named Pipe Filesystem Elevation of Privilege Vulnerability |
| CVE-2024-38125 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38127 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2024-38133 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38134 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38135 | Home windows Resilient File System (ReFS) Elevation of Privilege Vulnerability |
| CVE-2024-38136 | Home windows Useful resource Supervisor PSM Service Extension Elevation of Privilege Vulnerability |
| CVE-2024-38137 | Home windows Useful resource Supervisor PSM Service Extension Elevation of Privilege Vulnerability |
| CVE-2024-38141 | Home windows Ancillary Operate Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-38142 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-38143 | Home windows WLAN AutoConfig Service Elevation of Privilege Vulnerability |
| CVE-2024-38144 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38147 | Microsoft DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2024-38150 | Home windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2024-38153 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38162 | Azure Linked Machine Agent Elevation of Privilege Vulnerability |
| CVE-2024-38163 | Home windows Replace Stack Elevation of Privilege Vulnerability |
| CVE-2024-38184 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
| CVE-2024-38191 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38193 | Home windows Ancillary Operate Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-38196 | Home windows Frequent Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2024-38198 | Home windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2024-38201 | Azure Stack Hub Elevation of Privilege Vulnerability |
| CVE-2024-38202 | Home windows Replace Stack Elevation of Privilege Vulnerability |
| CVE-2024-38215 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2024-38223 | Home windows Preliminary Machine Configuration Elevation of Privilege Vulnerability |
Distant Code Execution (31 CVEs)
| Essential severity | |
| CVE-2022-3775 | Redhat: CVE-2022-3775 grub2 – Heap based mostly out-of-bounds write when rendering sure Unicode sequences |
| CVE-2024-38063 | Home windows TCP/IP Distant Code Execution Vulnerability |
| CVE-2024-38140 | Home windows Dependable Multicast Transport Driver (RMCAST) Distant Code Execution Vulnerability |
| CVE-2024-38159 | Home windows Community Virtualization Distant Code Execution Vulnerability |
| CVE-2024-38160 | Home windows Community Virtualization Distant Code Execution Vulnerability |
| Vital severity | |
| CVE-2024-38114 | Home windows IP Routing Administration Snapin Distant Code Execution Vulnerability |
| CVE-2024-38115 | Home windows IP Routing Administration Snapin Distant Code Execution Vulnerability |
| CVE-2024-38116 | Home windows IP Routing Administration Snapin Distant Code Execution Vulnerability |
| CVE-2024-38120 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38121 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38128 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38130 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38131 | Clipboard Digital Channel Extension Distant Code Execution Vulnerability |
| CVE-2024-38138 | Home windows Deployment Providers Distant Code Execution Vulnerability |
| CVE-2024-38152 | Home windows OLE Distant Code Execution Vulnerability |
| CVE-2024-38154 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38157 | Azure IoT SDK Distant Code Execution Vulnerability |
| CVE-2024-38158 | Azure IoT SDK Distant Code Execution Vulnerability |
| CVE-2024-38161 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-38169 | Microsoft Workplace Visio Distant Code Execution Vulnerability |
| CVE-2024-38170 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-38171 | Microsoft PowerPoint Distant Code Execution Vulnerability |
| CVE-2024-38172 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-38173 | Microsoft Outlook Distant Code Execution Vulnerability |
| CVE-2024-38178 | Scripting Engine Reminiscence Corruption Vulnerability |
| CVE-2024-38180 | SmartScreen Immediate Distant Code Execution Vulnerability |
| CVE-2024-38189 | Microsoft Mission Distant Code Execution Vulnerability |
| CVE-2024-38195 | Azure CycleCloud Distant Code Execution Vulnerability |
| CVE-2024-38199 | Home windows Line Printer Daemon (LPD) Service Distant Code Execution Vulnerability |
| CVE-2024-38218 | Microsoft Edge (HTML-based) Reminiscence Corruption Vulnerability |
| Average severity | |
| CVE-2024-38219 | Microsoft Edge (Chromium-based) Distant Code Execution Vulnerability |
Info Disclosure (8 CVEs)
| Vital severity | |
| CVE-2024-38118 | Microsoft Native Safety Authority (LSA) Server Info Disclosure Vulnerability |
| CVE-2024-38122 | Microsoft Native Safety Authority (LSA) Server Info Disclosure Vulnerability |
| CVE-2024-38123 | Home windows Bluetooth Driver Info Disclosure Vulnerability |
| CVE-2024-38151 | Home windows Kernel Info Disclosure Vulnerability |
| CVE-2024-38155 | Safety Heart Dealer Info Disclosure Vulnerability |
| CVE-2024-38167 | .NET and Visible Studio Info Disclosure Vulnerability |
| CVE-2024-38214 | Home windows Routing and Distant Entry Service (RRAS) Info Disclosure Vulnerability |
| Average severity | |
| CVE-2024-38222 | Microsoft Edge (Chromium-based) Info Disclosure Vulnerability |
Denial of Service (6 CVEs)
| Vital severity | |
| CVE-2024-38126 | Home windows Community Deal with Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-38132 | Home windows Community Deal with Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-38145 | Home windows Layer-2 Bridge Community Driver Denial of Service Vulnerability |
| CVE-2024-38146 | Home windows Layer-2 Bridge Community Driver Denial of Service Vulnerability |
| CVE-2024-38148 | Home windows Safe Channel Denial of Service Vulnerability |
| CVE-2024-38168 | .NET and Visible Studio Denial of Service Vulnerability |
Spoofing (6 CVEs)
| Vital severity | |
| CVE-2024-37968 | Home windows DNS Spoofing Vulnerability |
| CVE-2024-38108 | Azure Stack Spoofing Vulnerability |
| CVE-2024-38177 | Home windows App Installer Spoofing Vulnerability |
| CVE-2024-38197 | Microsoft Groups for iOS Spoofing Vulnerability |
| CVE-2024-38200 | Microsoft Workplace Spoofing Vulnerability |
| CVE-2024-38211 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Safety Characteristic Bypass (2 CVEs)
| Essential severity | |
| CVE-2023-40547 | Redhat: CVE-2023-40547 Shim – RCE in HTTP boot assist might result in safe boot bypass |
| Vital severity | |
| CVE-2022-2601 | Redhat: CVE-2022-2601 grub2 – Buffer overflow in grub_font_construct_glyph() can result in out-of-bound write and potential safe boot bypass |
Appendix B: Exploitability
It is a record of the August CVEs judged by Microsoft to be both underneath exploitation within the wild or extra prone to be exploited within the wild throughout the first 30 days post-release. The record is organized by CVE. This desk doesn’t embrace CVE-2024-38213, which was launched in June.
| Exploitation detected | |
| CVE-2024-38106 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38107 | Home windows Energy Dependency Coordinator Elevation of Privilege Vulnerability |
| CVE-2024-38178 | Scripting Engine Reminiscence Corruption Vulnerability |
| CVE-2024-38189 | Microsoft Mission Distant Code Execution Vulnerability |
| CVE-2024-38193 | Home windows Ancillary Operate Driver for WinSock Elevation of Privilege Vulnerability |
| Exploitation extra seemingly throughout the subsequent 30 days | |
| CVE-2024-38063 | Home windows TCP/IP Distant Code Execution Vulnerability |
| CVE-2024-38125 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38133 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38141 | Home windows Ancillary Operate Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-38144 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38147 | Microsoft DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2024-38148 | Home windows Safe Channel Denial of Service Vulnerability |
| CVE-2024-38150 | Home windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2024-38163 | Home windows Replace Stack Elevation of Privilege Vulnerability |
| CVE-2024-38196 | Home windows Frequent Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2024-38198 | Home windows Print Spooler Elevation of Privilege Vulnerability |
Appendix C: Merchandise Affected
It is a record of August’s patches sorted by product household, then sub-sorted by severity. Every record is additional organized by CVE. Patches which are shared amongst a number of product households are listed a number of instances, as soon as for every product household.
Home windows (62 CVEs)
| Essential severity | |
| CVE-2022-3775 | Redhat: CVE-2022-3775 grub2 – Heap based mostly out-of-bounds write when rendering sure Unicode sequences |
| CVE-2023-40547 | Redhat: CVE-2023-40547 Shim – RCE in HTTP boot assist might result in safe boot bypass |
| CVE-2024-38063 | Home windows TCP/IP Distant Code Execution Vulnerability |
| CVE-2024-38140 | Home windows Dependable Multicast Transport Driver (RMCAST) Distant Code Execution Vulnerability |
| CVE-2024-38159 | Home windows Community Virtualization Distant Code Execution Vulnerability |
| CVE-2024-38160 | Home windows Community Virtualization Distant Code Execution Vulnerability |
| Vital severity | |
| CVE-2022-2601 | Redhat: CVE-2022-2601 grub2 – Buffer overflow in grub_font_construct_glyph() can result in out-of-bound write and potential safe boot bypass |
| CVE-2024-21302 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-29995 | Home windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-37968 | Home windows DNS Spoofing Vulnerability |
| CVE-2024-38106 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38107 | Home windows Energy Dependency Coordinator Elevation of Privilege Vulnerability |
| CVE-2024-38114 | Home windows IP Routing Administration Snapin Distant Code Execution Vulnerability |
| CVE-2024-38115 | Home windows IP Routing Administration Snapin Distant Code Execution Vulnerability |
| CVE-2024-38116 | Home windows IP Routing Administration Snapin Distant Code Execution Vulnerability |
| CVE-2024-38117 | Home windows Named Pipe Filesystem Elevation of Privilege Vulnerability |
| CVE-2024-38118 | Microsoft Native Safety Authority (LSA) Server Info Disclosure Vulnerability |
| CVE-2024-38120 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38121 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38122 | Microsoft Native Safety Authority (LSA) Server Info Disclosure Vulnerability |
| CVE-2024-38123 | Home windows Bluetooth Driver Info Disclosure Vulnerability |
| CVE-2024-38125 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38126 | Home windows Community Deal with Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-38127 | Home windows Hyper-V Elevation of Privilege Vulnerability |
| CVE-2024-38128 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38130 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38131 | Clipboard Digital Channel Extension Distant Code Execution Vulnerability |
| CVE-2024-38132 | Home windows Community Deal with Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-38133 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38134 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38135 | Home windows Resilient File System (ReFS) Elevation of Privilege Vulnerability |
| CVE-2024-38136 | Home windows Useful resource Supervisor PSM Service Extension Elevation of Privilege Vulnerability |
| CVE-2024-38137 | Home windows Useful resource Supervisor PSM Service Extension Elevation of Privilege Vulnerability |
| CVE-2024-38138 | Home windows Deployment Providers Distant Code Execution Vulnerability |
| CVE-2024-38141 | Home windows Ancillary Operate Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-38142 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-38143 | Home windows WLAN AutoConfig Service Elevation of Privilege Vulnerability |
| CVE-2024-38144 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38145 | Home windows Layer-2 Bridge Community Driver Denial of Service Vulnerability |
| CVE-2024-38146 | Home windows Layer-2 Bridge Community Driver Denial of Service Vulnerability |
| CVE-2024-38147 | Microsoft DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2024-38148 | Home windows Safe Channel Denial of Service Vulnerability |
| CVE-2024-38150 | Home windows DWM Core Library Elevation of Privilege Vulnerability |
| CVE-2024-38151 | Home windows Kernel Info Disclosure Vulnerability |
| CVE-2024-38152 | Home windows OLE Distant Code Execution Vulnerability |
| CVE-2024-38153 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38154 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38155 | Safety Heart Dealer Info Disclosure Vulnerability |
| CVE-2024-38161 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-38163 | Home windows Replace Stack Elevation of Privilege Vulnerability |
| CVE-2024-38178 | Scripting Engine Reminiscence Corruption Vulnerability |
| CVE-2024-38180 | SmartScreen Immediate Distant Code Execution Vulnerability |
| CVE-2024-38184 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
| CVE-2024-38191 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability |
| CVE-2024-38193 | Home windows Ancillary Operate Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-38196 | Home windows Frequent Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2024-38198 | Home windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2024-38199 | Home windows Line Printer Daemon (LPD) Service Distant Code Execution Vulnerability |
| CVE-2024-38202 | Home windows Replace Stack Elevation of Privilege Vulnerability |
| CVE-2024-38214 | Home windows Routing and Distant Entry Service (RRAS) Info Disclosure Vulnerability |
| CVE-2024-38215 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
| CVE-2024-38223 | Home windows Preliminary Machine Configuration Elevation of Privilege Vulnerability |
Azure (7 CVEs)
| Vital severity | |
| CVE-2024-38098 | Azure Linked Machine Agent Elevation of Privilege Vulnerability |
| CVE-2024-38108 | Azure Stack Spoofing Vulnerability |
| CVE-2024-38157 | Azure IoT SDK Distant Code Execution Vulnerability |
| CVE-2024-38158 | Azure IoT SDK Distant Code Execution Vulnerability |
| CVE-2024-38162 | Azure Linked Machine Agent Elevation of Privilege Vulnerability |
| CVE-2024-38195 | Azure CycleCloud Distant Code Execution Vulnerability |
| CVE-2024-38201 | Azure Stack Hub Elevation of Privilege Vulnerability |
365 Apps for Enterprise (7 CVEs)
| Vital severity | |
| CVE-2024-38169 | Microsoft Workplace Visio Distant Code Execution Vulnerability |
| CVE-2024-38170 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-38171 | Microsoft PowerPoint Distant Code Execution Vulnerability |
| CVE-2024-38172 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-38173 | Microsoft Outlook Distant Code Execution Vulnerability |
| CVE-2024-38189 | Microsoft Mission Distant Code Execution Vulnerability |
| CVE-2024-38200 | Microsoft Workplace Spoofing Vulnerability |
Workplace (7 CVEs)
| Vital severity | |
| CVE-2024-38169 | Microsoft Workplace Visio Distant Code Execution Vulnerability |
| CVE-2024-38170 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-38171 | Microsoft PowerPoint Distant Code Execution Vulnerability |
| CVE-2024-38172 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-38173 | Microsoft Outlook Distant Code Execution Vulnerability |
| CVE-2024-38189 | Microsoft Mission Distant Code Execution Vulnerability |
| CVE-2024-38200 | Microsoft Workplace Spoofing Vulnerability |
Edge (3 CVE)
| Vital severity | |
| CVE-2024-38218 | Microsoft Edge (HTML-based) Reminiscence Corruption Vulnerability |
| Average severity | |
| CVE-2024-38219 | Microsoft Edge (Chromium-based) Distant Code Execution Vulnerability |
| CVE-2024-38222 | Microsoft Edge (Chromium-based) Info Disclosure Vulnerability |
.NET (2 CVE)
| Vital severity | |
| CVE-2024-38167 | .NET and Visible Studio Info Disclosure Vulnerability |
| CVE-2024-38168 | .NET and Visible Studio Denial of Service Vulnerability |
Azure Linux (2 CVE)
| Essential severity | |
| CVE-2022-3775 | Redhat: CVE-2022-3775 grub2 – Heap based mostly out-of-bounds write when rendering sure Unicode sequences |
| Vital severity | |
| CVE-2022-2601 | Redhat: CVE-2022-2601 grub2 – Buffer overflow in grub_font_construct_glyph() can result in out-of-bound write and potential safe boot bypass |
CBL-Mariner (2 CVE)
| Essential severity | |
| CVE-2022-3775 | Redhat: CVE-2022-3775 grub2 – Heap based mostly out-of-bounds write when rendering sure Unicode sequences |
| Vital severity | |
| CVE-2022-2601 | Redhat: CVE-2022-2601 grub2 – Buffer overflow in grub_font_construct_glyph() can result in out-of-bound write and potential safe boot bypass |
Visible Studio (2 CVE)
| Vital severity | |
| CVE-2024-38167 | .NET and Visible Studio Info Disclosure Vulnerability |
| CVE-2024-38168 | .NET and Visible Studio Denial of Service Vulnerability |
App Installer (1 CVE)
| Vital severity | |
| CVE-2024-38177 | Home windows App Installer Spoofing Vulnerability |
Dynamics 365 (1 CVE)
| Vital severity | |
| CVE-2024-38211 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
OfficePlus (1 CVE)
| Vital severity | |
| CVE-2024-38084 | Microsoft OfficePlus Elevation of Privilege Vulnerability |
Outlook (1 CVE)
| Vital severity | |
| CVE-2024-38173 | Microsoft Outlook Distant Code Execution Vulnerability |
PowerPoint (1 CVE)
| Vital severity | |
| CVE-2024-38171 | Microsoft PowerPoint Distant Code Execution Vulnerability |
Mission (1 CVE)
| Vital severity | |
| CVE-2024-38189 | Microsoft Mission Distant Code Execution Vulnerability |
Groups (1 CVE)
| Vital severity | |
| CVE-2024-38197 | Microsoft Groups for iOS Spoofing Vulnerability |
Appendix D: Advisories and Different Merchandise
It is a record of advisories and data on different related CVEs within the August Microsoft launch, sorted by product.
Related to Edge / Chromium (9 CVEs)
| CVE-2024-6990 | Chromium: CVE-2024-6990 Uninitialized Use in Daybreak |
| CVE-2024-7255 | Chromium: CVE-2024-7255 Out of bounds learn in WebTransport |
| CVE-2024-7256 | Chromium: CVE-2024-7256 Inadequate knowledge validation in Daybreak |
| CVE-2024-7532 | Chromium: CVE-2024-7532 Out of bounds reminiscence entry in ANGLE |
| CVE-2024-7533 | Chromium: CVE-2024-7533 Use after free in Sharing |
| CVE-2024-7534 | Chromium: CVE-2024-7534 Heap buffer overflow in Structure |
| CVE-2024-7535 | Chromium: CVE-2024-7535 Inappropriate implementation in V8 |
| CVE-2024-7536 | Chromium: CVE-2024-7536 Use after free in WebAudio |
| CVE-2024-7550 | Chromium: CVE-2024-7550 Sort Confusion in V8 |
Servicing Stack Updates (1 merchandise)
| ADV990001 | Newest Servicing Stack Updates |
Beforehand Launched; Info Lacking from Earlier Patch Tuesday Knowledge (5 CVEs)
| Launched June 2024 | |
| CVE-2024-38213 | Home windows Mark of the Net Safety Characteristic Bypass Vulnerability |
| Launched July 2024 | |
| CVE-2024-38165 | Home windows Compressed Folder Tampering Vulnerability |
| CVE-2024-38185 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
| CVE-2024-38186 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
| CVE-2024-38187 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
Beforehand Launched (Cloud); Info Offered as Advisory Solely (3 objects)
| CVE-2024-38109 | Azure Well being Bot Elevation of Privilege Vulnerability |
| CVE-2024-38166 | Microsoft Dynamics 365 Cross-site Scripting Vulnerability |
| CVE-2024-38206 | Microsoft Copilot Studio Info Disclosure Vulnerability |
Related to Adobe (non-Microsoft launch) (12 CVEs)
| APSB24-57 | CVE-2024-39383 | Use After Free (CWE-416) |
| APSB24-57 | CVE-2024-39422 | Use After Free (CWE-416) |
| APSB24-57 | CVE-2024-39423 | Out-of-bounds Write (CWE-787) |
| APSB24-57 | CVE-2024-39424 | Use After Free (CWE-416) |
| APSB24-57 | CVE-2024-39425 | Time-of-check Time-of-use (TOCTOU) Race Situation (CWE-367) |
| APSB24-57 | CVE-2024-39426 | Entry of Reminiscence Location After Finish of Buffer (CWE-788) |
| APSB24-57 | CVE-2024-41830 | Use After Free (CWE-416) |
| APSB24-57 | CVE-2024-41831 | Use After Free (CWE-416) |
| APSB24-57 | CVE-2024-41832 | Out-of-bounds Learn (CWE-125) |
| APSB24-57 | CVE-2024-41833 | Out-of-bounds Learn (CWE-125) |
| APSB24-57 | CVE-2024-41834 | Out-of-bounds Learn (CWE-125) |
| APSB24-57 | CVE-2024-41835 | Out-of-bounds Learn (CWE-125) |
Appendix E: CVEs Related to CBL-Mariner / Azure Linux
The knowledge on these CVEs, which originated with an assortment of CNAs, is commonly relatively completely different in nature from that supplied for CVEs addressed in Microsoft’s Patch Tuesday course of. Typically such CVEs haven’t any title, or no accessible CVSS scoring. For this desk, we have now chosen to easily record the CVEs as famous in Microsoft’s personal abstract info.
| CVE-2007-4559 | CVE-2022-36648 | CVE-2024-37370 | CVE-2024-40898 |
| CVE-2017-17522 | CVE-2022-3775 | CVE-2024-37371 | CVE-2024-40902 |
| CVE-2017-18207 | CVE-2022-3872 | CVE-2024-38428 | CVE-2024-41110 |
| CVE-2019-20907 | CVE-2022-4144 | CVE-2024-38571 | CVE-2024-42068 |
| CVE-2019-3816 | CVE-2022-41722 | CVE-2024-38583 | CVE-2024-42070 |
| CVE-2019-3833 | CVE-2022-48788 | CVE-2024-38662 | CVE-2024-42071 |
| CVE-2019-9674 | CVE-2022-48841 | CVE-2024-38780 | CVE-2024-42072 |
| CVE-2021-23336 | CVE-2023-29402 | CVE-2024-39277 | CVE-2024-42073 |
| CVE-2021-3750 | CVE-2023-29404 | CVE-2024-39292 | CVE-2024-42074 |
| CVE-2021-3929 | CVE-2023-3354 | CVE-2024-39331 | CVE-2024-42075 |
| CVE-2021-4158 | CVE-2023-45288 | CVE-2024-39473 | CVE-2024-42076 |
| CVE-2021-4206 | CVE-2023-52340 | CVE-2024-39474 | CVE-2024-42077 |
| CVE-2021-4207 | CVE-2024-0397 | CVE-2024-39475 | CVE-2024-42078 |
| CVE-2021-43565 | CVE-2024-0853 | CVE-2024-39476 | CVE-2024-42080 |
| CVE-2022-0358 | CVE-2024-2004 | CVE-2024-39480 | CVE-2024-42082 |
| CVE-2022-2601 | CVE-2024-23722 | CVE-2024-39482 | CVE-2024-42083 |
| CVE-2022-26353 | CVE-2024-2398 | CVE-2024-39483 | CVE-2024-42237 |
| CVE-2022-26354 | CVE-2024-2466 | CVE-2024-39484 | CVE-2024-6104 |
| CVE-2022-29526 | CVE-2024-26461 | CVE-2024-39485 | CVE-2024-6257 |
| CVE-2022-2962 | CVE-2024-26900 | CVE-2024-39489 | CVE-2024-6655 |
| CVE-2022-3165 | CVE-2024-36288 | CVE-2024-39493 | |
| CVE-2022-35414 | CVE-2024-37298 | CVE-2024-39495 |