
Underneath sure situations, attackers can chain a set of vulnerabilities in a number of elements of the CUPS open-source printing system to execute arbitrary code remotely on weak machines.
Tracked as CVE-2024-47076 (libcupsfilters), CVE-2024-47175 (libppd), CVE-2024-47176 (cups-browsed) and CVE-2024-47177 (cups-filters) and found by Simone Margaritelli, these safety flaws do not have an effect on techniques of their default configuration.
CUPS (quick for Frequent UNIX Printing System) is probably the most broadly used printing system on Linux techniques, and it is usually typically supported on gadgets operating Unix-like working techniques comparable to FreeBSD, NetBSD, and OpenBSD and their derivates.
Certainly one of its elements is the cups-browsed daemon, which searches the native community for marketed community or shared printers and makes them accessible for printing on the machine. That is just like how Home windows and Macs can search the community for distant community printers to print to.
Margaritelli discovered that if the cups-browsed daemon is enabled, which isn’t on most techniques, it is going to hear on UDP port 631. It can additionally, by default, permit distant connections from any gadget on the community to create a brand new printer.
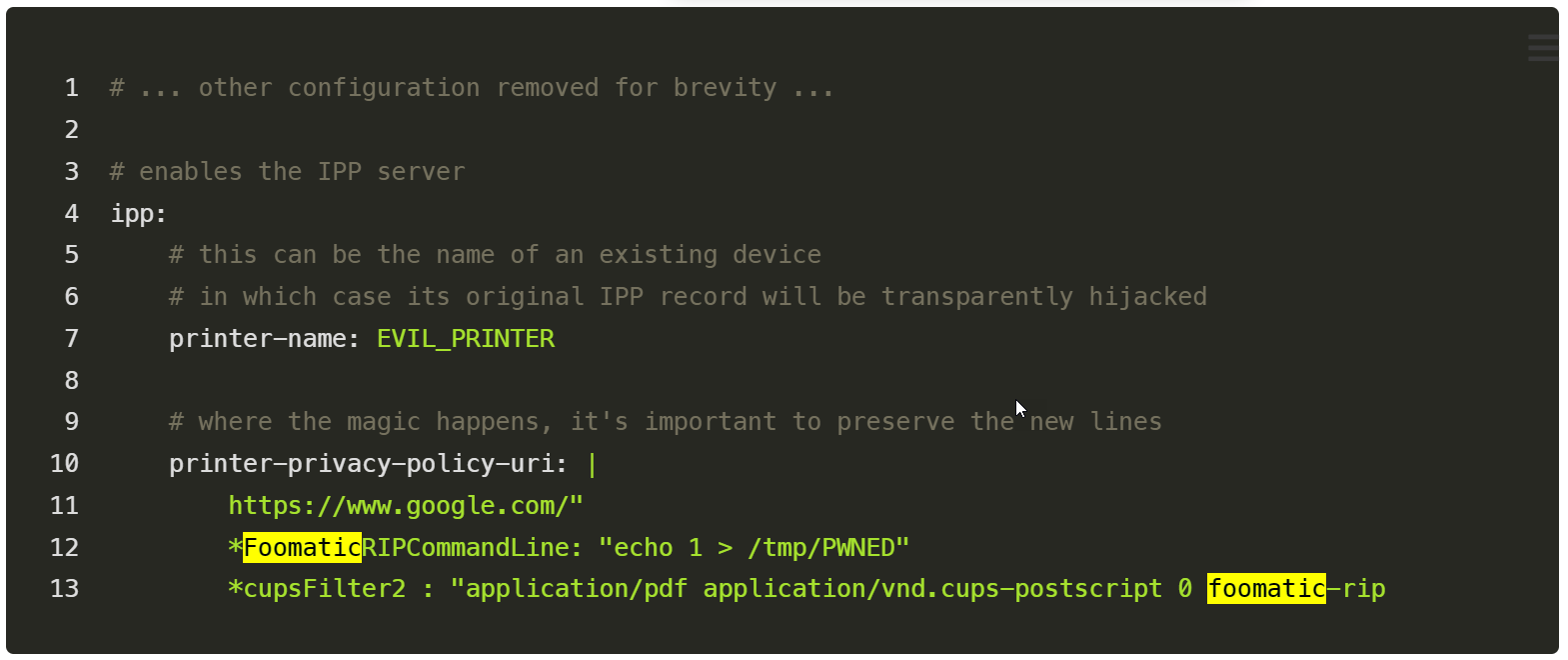
He found he might create a malicious PostScript Printer Description (PPD) printer that might be manually marketed to an uncovered cups-browsed service operating on UDP port 631.
This causes the distant machine to mechanically set up the malicious printer and make it accessible for printing. If the person on that uncovered server prints to the brand new printer, the malicious command within the PPD can be executed domestically on the pc.
The command to execute when printing is added by a foomatic-rip filter, which executes instructions on a tool so {that a} print job is rendered appropriately.
Restricted world affect
Whereas this can be a distant code execution chain, it must be famous from the beginning that attackers should overcome some obstacles to take advantage of the vulnerabilities and really obtain distant code execution.
The primary is that the focused techniques will need to have the cups-browsed daemon enabled, which is often not enabled by default, to show their UDP ports on a community. Then, the attacker has to trick a person into printing from a malicious printer server on their native community that immediately seems on their machine.
“It’s a chain of bugs that depend on spoofing a printer in your native community that’s mechanically added through community discovery whether it is turned on in any respect – often not in its default configuration. Then an unverified variable that’s used to take advantage of different vulnerabilities within the CUPS system to execute code, however solely when a print job is triggered,” stated Ilkka Turunen, Discipline CTO at Sonatype.
“Excellent news then – it’s an RCE however with a number of mitigations, together with the very fact the attacker wants to have the ability to connect with a pc through UDP which is broadly disabled on community ingress and the service is often not on by default. It looks as if the true world affect is low.”
For these causes, Crimson Hat has rated the failings as having an “Vital” severity affect as an alternative of essential.
Whereas BleepingComputer’s checks confirmed that the majority of our Linux servers didn’t have the service enabled by default, one among our Ubuntu VMs did. Others have additionally famous on Twitter that cups-browsed was enabled by default on their Linux gadgets.
No patches, however mitigation measures can be found
Whereas patches are nonetheless in growth, Crimson Hat shared mitigation measures requiring admins to cease the cups-browsed service from operating and forestall it from being began on reboot utilizing the next instructions to interrupt the exploit chain:
sudo systemctl cease cups-browsed
sudo systemctl disable cups-browsedCrimson Hat customers can even use the next command to seek out out if cups-browsed is operating on their techniques:
sudo systemctl standing cups-browsedIf the end result shows “Energetic: inactive (lifeless),” then the exploit chain is halted, and the system just isn’t weak. If the end result exhibits “operating” or “enabled,” and the “BrowseRemoteProtocols” directive accommodates the worth “cups” within the configuration file /and so forth/cups/cups-browsed.conf, then the system is weak.
