
Members of the North Korean hacker group Lazarus posing as recruiters are baiting Python builders with coding take a look at mission for password administration merchandise that embrace malware.
The assaults are a part of the ‘VMConnect marketing campaign’ first detected in August 2023, the place the risk actors focused software program builders with malicious Python packages uploaded onto the PyPI repository.
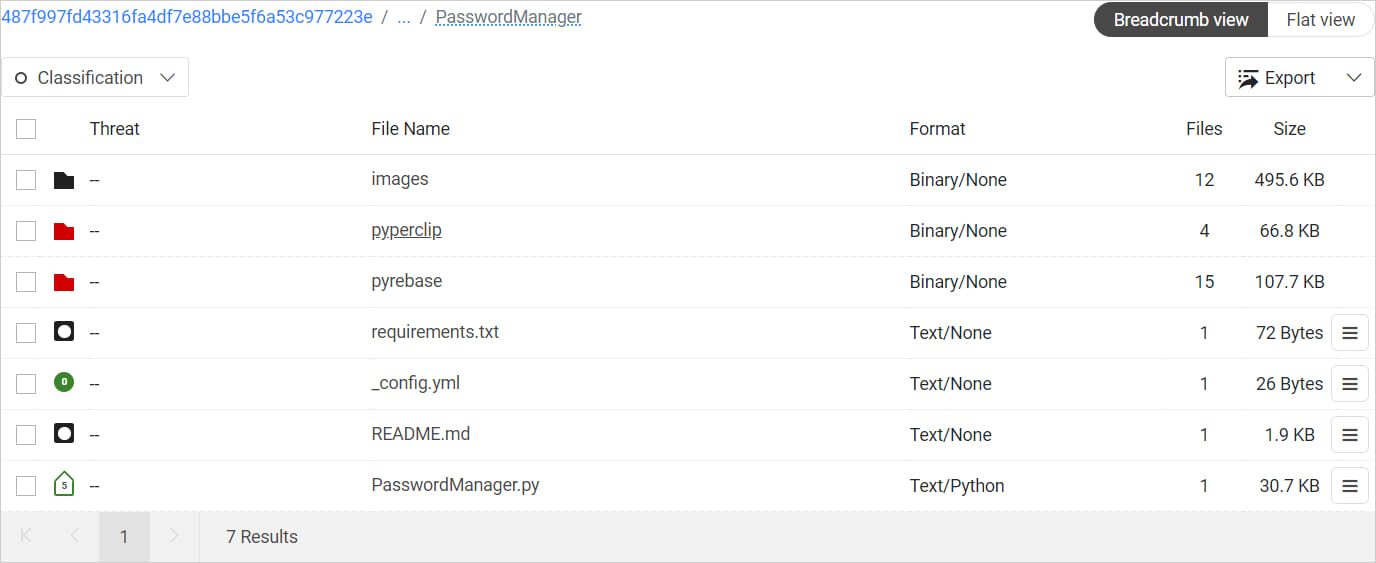
In response to a report from ReversingLabs, which has been monitoring the marketing campaign for over a yr, Lazarus hackers host the malicious coding tasks on GitHub, the place victims discover README information with directions on how you can full the take a look at.
The instructions are supposed to present a way professionalism and legitimacy to the entire course of, in addition to a way of urgency.
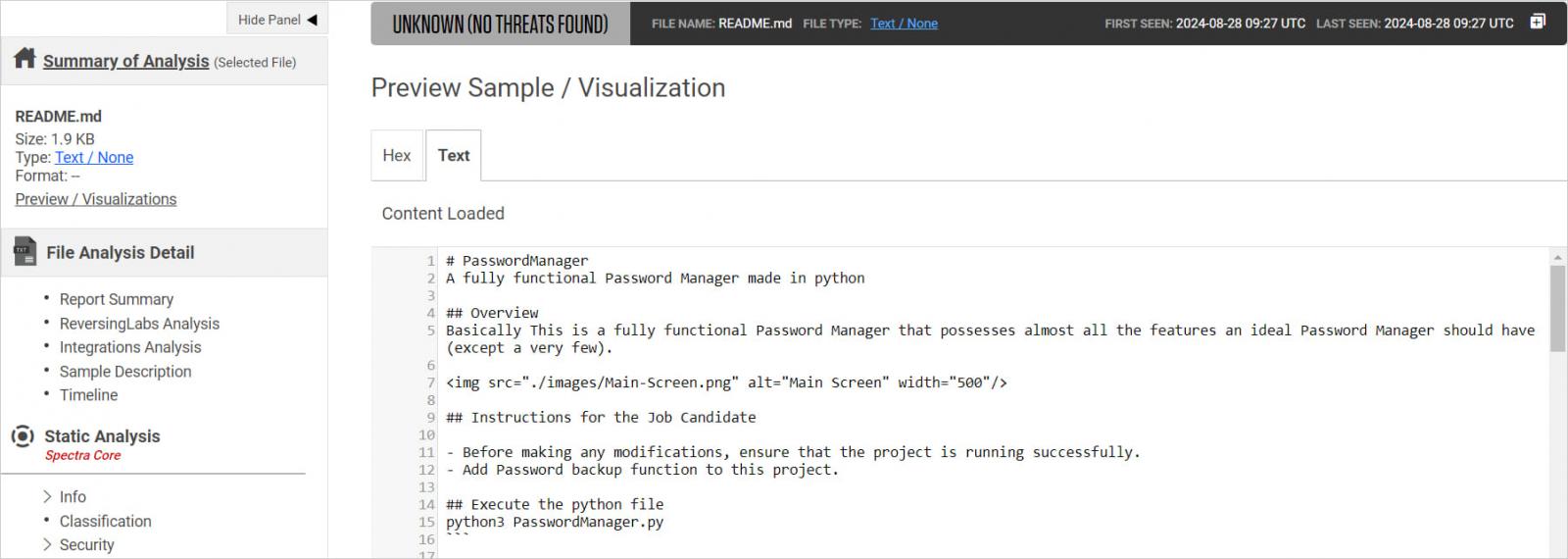
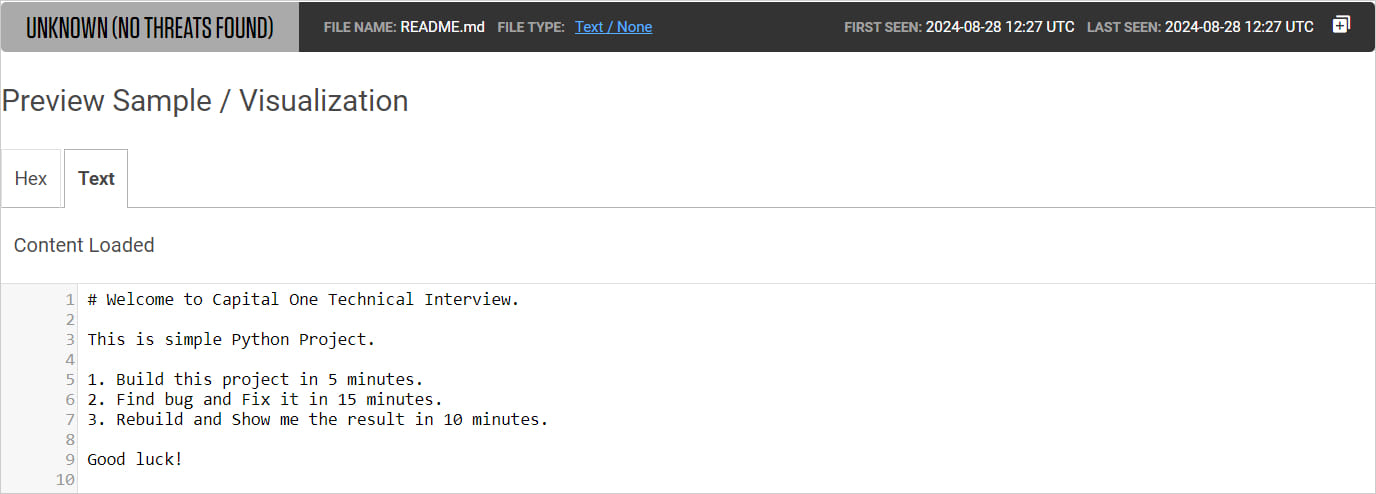
ReversingLabs discovered that the North Koreans impersonate giant U.S. banks like Capital One to draw job candidates, possible providing them an attractive employment bundle.
Additional proof retrieved from one of many victims means that Lazarus actively approaches their targets over LinkedIn, a documented tactic for the group.
Discover the bug
The hackers direct candidates to discover a bug in a password supervisor software, submit their repair, and share a screenshot as proof of their work.
Supply: ReversingLabs
The README file for the mission instruct the sufferer first to execute the malicious password supervisor software (‘PasswordManager.py’) on their system after which begin searching for the errors and fixing them.
Supply: ReversingLabs
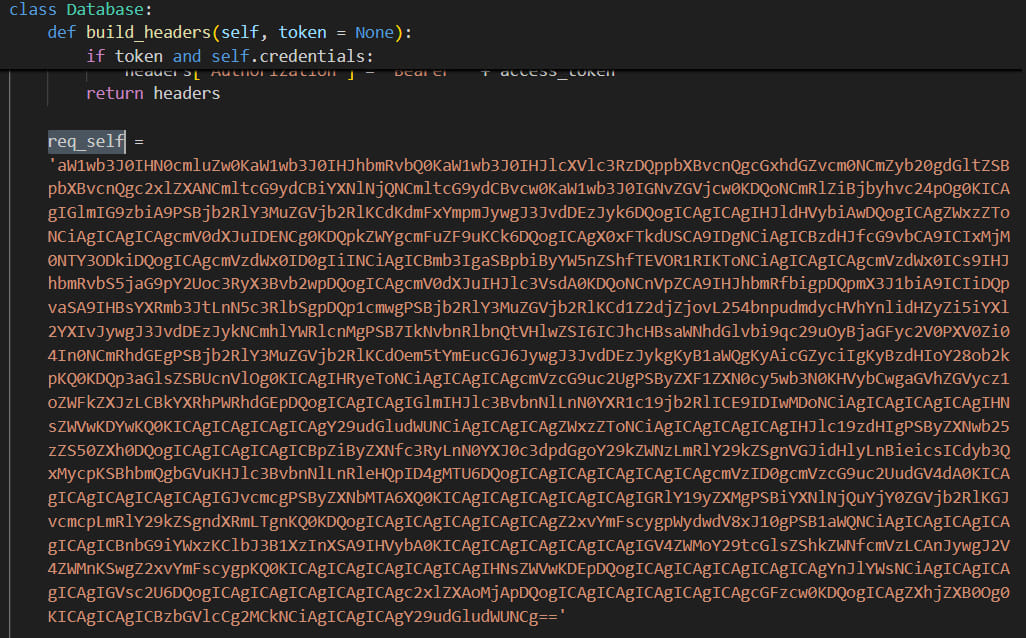
That file triggers the execution of a base64 obfuscated module hidden within the’_init_.py’ information of the ‘pyperclip’ and ‘pyrebase’ libraries.
The obfuscated string is a malware downloader that contacts a command and management (C2) server and awaits for instructions. Fetching and operating further payloads is inside its capabilities.
Supply: ReversingLabs
To ensure that the candidates will not verify the mission information for malicious or obfuscated code, the README file require the duty to be accomplished shortly: 5 minutes for constructing the mission, quarter-hour to implement the repair, and 10 minutes to ship again the ultimate consequence.
That is purported to show the developer’s experience in working with Python tasks and GitHub, however the objective is to make the sufferer skip any safety checks which will reveal the malicious code.
Supply: ReversingLabs
ReversingLabs has discovered proof that the marketing campaign was nonetheless lively on July 31 and imagine that it’s ongoing.
Software program builders receiving job software invitations from customers on LinkedIn or elsewhere must be cautious about the potential for deception and take into accounts that the profiles contacting them could possibly be faux.
Earlier than receiving the project, attempt to confirm the opposite individual’s id and independently affirm with the corporate {that a} recruitment spherical is certainly underway.
Take the time to scan or fastidiously overview the given code and solely execute it in protected environments akin to digital machines or sandboxing functions.
