ESET researchers have mapped the latest actions of the CosmicBeetle risk actor, documenting its new ScRansom ransomware and highlighting connections to different well-established ransomware gangs.
CosmicBeetle actively deploys ScRansom to SMBs in numerous elements of the world. Whereas not being prime notch, the risk actor is ready to compromise attention-grabbing targets.
CosmicBeetle changed its beforehand deployed ransomware, Scarab, with ScRansom, which is frequently improved. We now have additionally noticed the risk actor utilizing the leaked LockBit builder and making an attempt to leech off LockBit’s fame by impersonating the notorious ransomware gang each in ransom notes and leak website.
Apart from LockBit, we consider with medium confidence that CosmicBeetle is a brand new affiliate of RansomHub, a brand new ransomware gang energetic since March 2024 with quickly rising exercise.
On this blogpost, we look at CosmicBeetle’s actions through the previous yr and analyze the connections to different well-established ransomware gangs. We additionally present perception into ScRansom.
Key factors of the blogpost:
- CosmicBeetle stays energetic in 2024, frequently enhancing and distributing its customized ransomware, ScRansom.
- We offer an evaluation of ScRansom, emphasizing that it’s unimaginable to revive some encrypted recordsdata.
- CosmicBeetle has been experimenting with the leaked LockBit builder and has been making an attempt to abuse its model.
- CosmicBeetle could also be a latest affiliate of the ransomware-as-a-service actor RansomHub.
- CosmicBeetle exploits years-old vulnerabilities to breach SMBs all around the world.
Overview
CosmicBeetle, energetic since no less than 2020, is the title ESET researchers assigned to a risk actor found in 2023. This risk actor is most identified for the utilization of its customized assortment of Delphi instruments, generally referred to as Spacecolon, consisting of ScHackTool, ScInstaller, ScService, and ScPatcher. In August 2023, ESET researchers printed their insights into CosmicBeetle. Shortly earlier than publishing, new customized ransomware we named ScRansom appeared that we consider, with excessive confidence, is expounded to CosmicBeetle. We now have since discovered additional causes to extend our confidence of this relation and consider that ScRansom is now that group’s ransomware of selection, changing the beforehand utilized Scarab ransomware.
On the time of that publication in 2023, we had not noticed any exercise within the wild. That, nevertheless, modified shortly thereafter. CosmicBeetle has since been spreading ScRansom to SMBs, primarily in Europe and Asia.
ScRansom just isn’t very refined ransomware, but CosmicBeetle has been in a position to compromise attention-grabbing targets and trigger nice hurt to them. Largely as a result of CosmicBeetle is an immature actor within the ransomware world, issues plague the deployment of ScRansom. Victims affected by ScRansom who resolve to pay ought to be cautious. Whereas the decryptor itself works as anticipated (on the time of writing), a number of decryption keys are sometimes required and a few recordsdata could also be completely misplaced, relying on how CosmicBeetle proceeded throughout encryption. We go into extra particulars later on this blogpost. In line with our expertise relating to CosmicBeetle, an attention-grabbing research of immature ransomware teams just lately printed by GuidePoint Safety exhibits corresponding outcomes.
CosmicBeetle partially tried to handle, or moderately cover, these points by impersonating the just lately disrupted LockBit, most likely probably the most notorious ransomware gang of the previous few years. By abusing the LockBit model title, CosmicBeetle hoped to raised persuade victims to pay. CosmicBeetle additionally utilized the leaked LockBit Black builder to generate its customized samples with a ransom observe in Turkish.
Lately, we’ve got investigated an attention-grabbing case that leads us to consider that CosmicBeetle could also be a brand new affiliate of RansomHub. RansomHub is a reasonably just lately emerged ransomware-as-a-service gang that rapidly gained the general public’s eye when Notchy, the infamous affiliate of the BlackCat ransomware gang who claimed duty for the assault on Change Healthcare, complained that BlackCat stole Notchy’s ransom fee and can due to this fact be partnering with the rival gang RansomHub as an alternative.
This blogpost paperwork the evolution of ScRansom for the previous yr and CosmicBeetle’s method to compromising victims. We additionally dive deeper into the risk actor’s relations to different ransomware gangs.
Attribution
We consider with excessive confidence that ScRansom is the most recent addition to CosmicBeetle’s customized toolset. On this part, we clarify our reasoning.
ESET telemetry exhibits a number of instances the place ScRansom deployment overlaps with different instruments generally utilized by CosmicBeetle. Moreover, a ZIP archive uploaded to VirusTotal incorporates two embedded archives, each most likely containing samples from an intrusion. Each archives comprise ScRansom, ScHackTool, and different instruments generally utilized by CosmicBeetle, additional supporting our suspicions.
There may be a number of code similarity between ScRansom and former CosmicBeetle tooling, specifically:
- Delphi because the programming language of selection,
- IPWorks library for encryption,
- equivalent Turkish strings within the code,
- utilizing areas after colons in strings, which earned the Spacecolon toolset its title, and
- GUI similarity with ScHackTool.
All of those similarities additional strengthen our attribution. Though Zaufana Trzencia Strona analysts just lately printed a blogpost about CosmicBeetle the place they attributed CosmicBeetle to an precise individual – a Turkish software program developer, ESET researchers don’t assume this attribution is correct. That attribution relies on the customized encryption scheme utilized in ScHackTool (not ScRansom). Particularly, they discovered a malicious pattern (SHA‑1: 28FD3345D82DA0CDB565A11C648AFF196F03D770) that incorporates this algorithm and is signed by a Turkish software program growth firm VOVSOFT with a strange-looking headquarters.
However the talked about pattern doesn’t belong to VOVSOFT; it’s truly a malicious patched model of Disk Monitor Gadget, one in all many merchandise developed by VOVSOFT signed correctly (SHA-1: 2BA12CD5E44839EA67DE8A07734A4E0303E5A3F8). Furthermore, the digital signature was copied from the legit model and easily appended to the patched model, ensuing within the malicious pattern apparently being signed, however not having a legitimate signature.
Apparently, ScHackTool’s encryption scheme is used within the legit Disk Monitor Gadget too. Zaufana Trzencia Strona analysts found that the algorithm possible originates from this Stack Overflow thread from 13 years in the past. For the reason that creator of the submit, MohsenB, has been an energetic consumer of Stack Overflow since 2012 – and, primarily based on profile footage, just isn’t the VOVSOFT developer himself – it’s possible that this algorithm was tailored by VOVSOFT and, years later, CosmicBeetle stumbled upon it and used it for ScHackTool.
Preliminary entry and victimology
CosmicBeetle typically makes use of brute-force strategies to breach its targets. Apart from that, the next vulnerabilities are being exploited by the risk actor:
SMBs from all kinds of verticals all around the world are the commonest victims of this risk actor as a result of that’s the section most probably to make use of the affected software program and to not have sturdy patch administration processes in place. CosmicBeetle’s leak website is, as we are going to display shortly, very unreliable and inconsistent; due to this fact we confer with ESET telemetry. Determine 1 demonstrates CosmicBeetle’s victims in accordance with ESET telemetry.
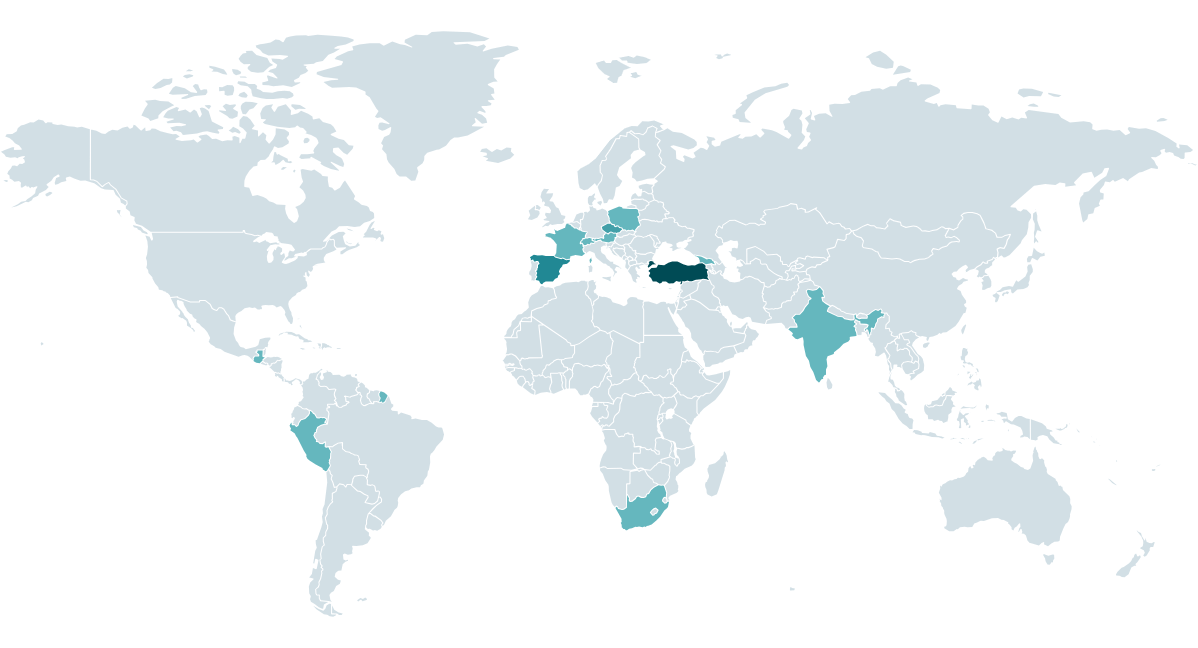
We noticed assaults on SMBs within the following verticals:
- manufacturing,
- prescribed drugs,
- authorized,
- schooling,
- healthcare,
- expertise,
- hospitality leisure,
- monetary companies, and
- regional authorities.
Model
Most ransom notes dropped by ScRansom don’t assign a reputation to the ransomware. CosmicBeetle depends primarily on e-mail and qTox, an on the spot messaging utility utilized by many ransomware gangs, primarily as a result of its utilization of the Tox protocol. The Tox protocol offers peer-to-peer end-to-end encrypted communication.
The one title CosmicBeetle selected for its customized ransomware is, satirically, NONAME, because the risk actor briefly branded the ransomware, which we talk about within the following part. As a result of chaotic nature of the branding, for the aim of this blogpost, we are going to proceed to confer with the ransomware as ScRansom.
LockBit copycat
In September 2023, CosmicBeetle determined to arrange a devoted leak website (DLS) on Tor, which it named NONAME. This website, illustrated in Determine 2, is a rip-off of LockBit’s leak website (see Determine 3).
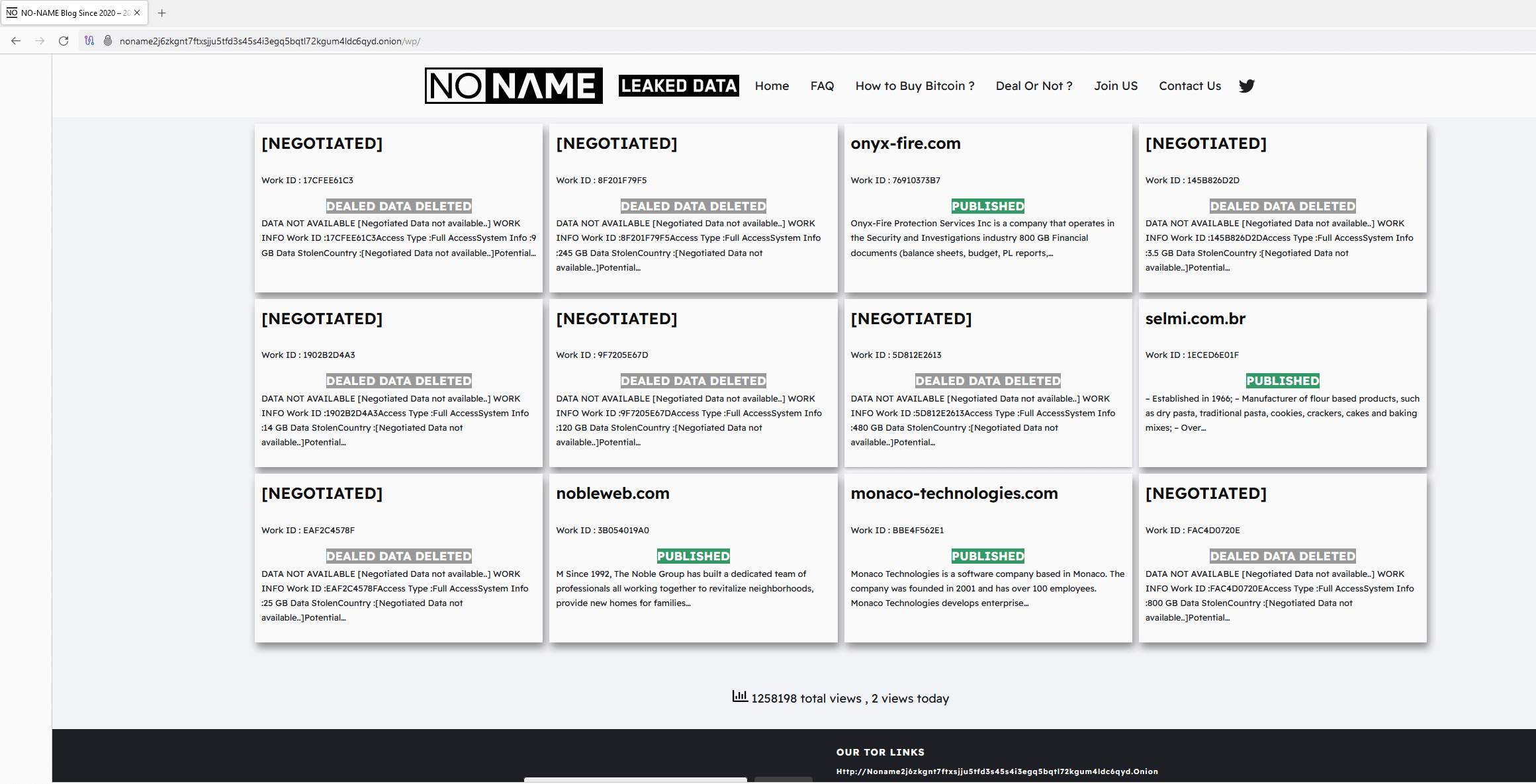
Whereas a couple of graphical modifications have been made, the inspiration remains to be clear. Furthermore, the design just isn’t the one similarity with LockBit. The entire victims seen in Determine 2 had been truly compromised by LockBit, not ScRansom. This may be verified by utilizing DLS monitoring companies, similar to RansomLook. The entire victims had been posted on LockBit’s leak website, most of them in September 2023, shortly earlier than the NONAME DLS appeared. The Work ID string is added to extend the phantasm of being associated to ScRansom, as that is how victims are recognized in ransom notes.
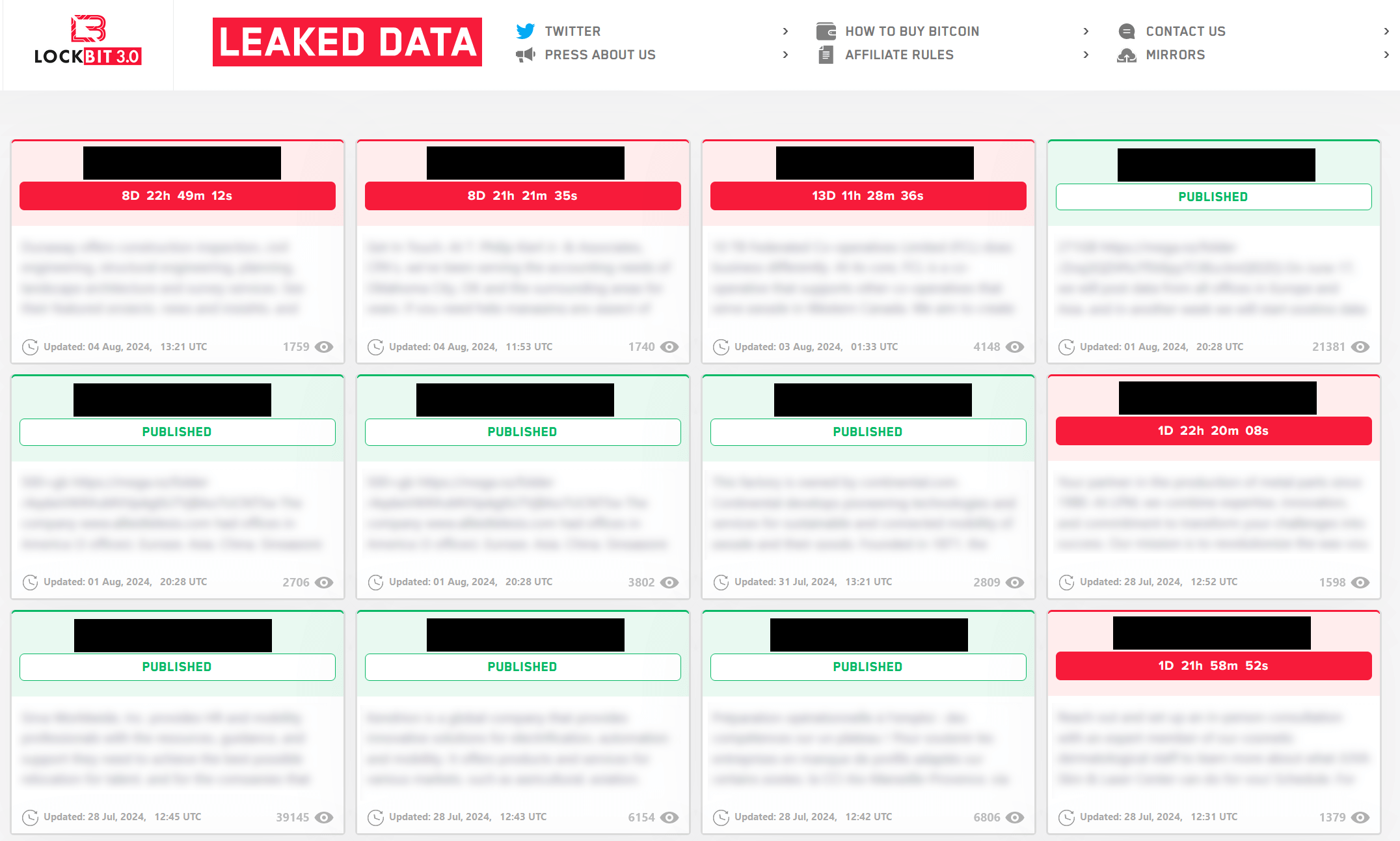
In early November 2023, CosmicBeetle determined to maneuver even additional and determined to impersonate LockBit utterly. They did so by registering the area lockbitblog[.]information and utilizing the identical method as for the NONAME DLS, solely this time, they included the LockBit brand as effectively (see Determine 4). Then, for a time, ScRansom’s ransom notes linked to this web site. The identical inspiration is seen and the graphical similarity to the NONAME DLS (Determine 2) is simple.
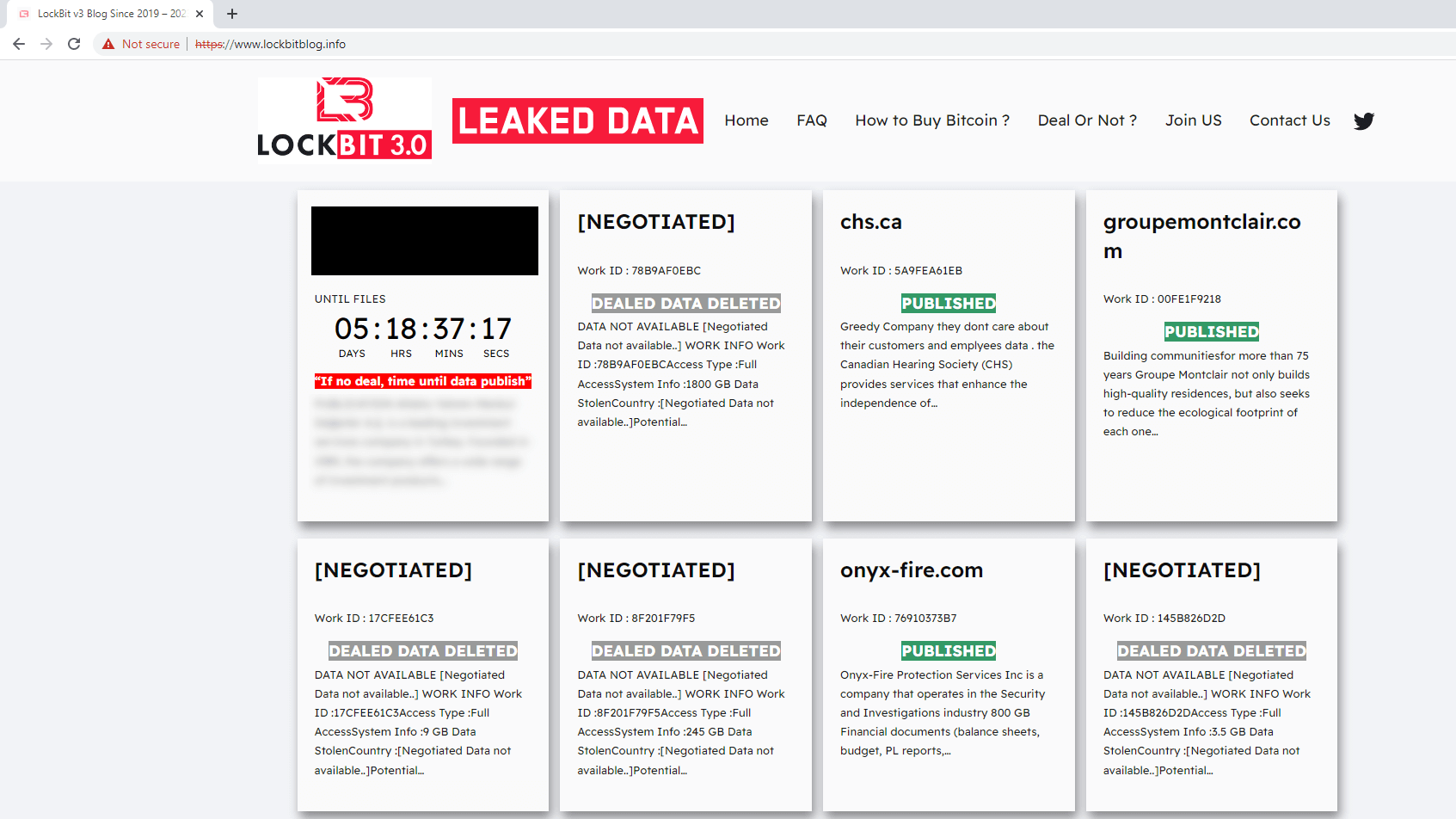
A pattern constructed utilizing the leaked LockBit 3.0 builder was uploaded to VirusTotal in August 2024 from Türkiye. What makes this pattern distinctive is that it makes use of a ransom message (see Determine 5) in Turkish and the qTox ID it mentions is one we conclusively linked to CosmicBeetle. ESET telemetry corroborates this connection, as we’ve got investigated a case the place deployment of LockBit overlapped with CosmicBeetle’s toolset.
|
I’ve encrypted your knowledge and for the charge you’ll pay, I’ll reconnect to your system, decrypt it and ship it to you. We want you to know that you just can not get your knowledge again with identified knowledge restoration strategies. These strategies will solely trigger you to lose time. If a return just isn’t made inside 48 hours, the password used within the system will probably be deleted and your knowledge won’t ever be returned. Your disks are encrypted with Full disk encryption, unauthorized intervention will trigger everlasting knowledge loss! Don’t consider the pc guys who say they won’t open even when you pay them or the folks round you who say they may take your cash and never provide you with your recordsdata I’ve sufficient references to belief you I have no idea you, so there is no such thing as a level in having dangerous emotions in direction of you or doing you hurt, I’ll hook up with your server as quickly as attainable to revive your knowledge. I may also clarify methods to safe your system after this course of in order that such incidents won’t ever occur to you once more. Private Key e-mail 1 : sunucuverikurtarma@gmail[.]com Backup e-mail : serverdatakurtarma@mail[.]ru QTOX : A5F2F6058F70CE5953DC475EE6AF1F97FC6D487ABEBAE76915075E3A53525B1D863102EDD50E |
Determine 5. Ransom observe that incorporates a TOX ID utilized by CosmicBeetle, dropped by a LockBit pattern. Textual content was machine translated from Turkish.
Relation to RansomHub
Utilizing leaked builders is a typical follow for immature ransomware gangs. It permits them to abuse the model of their well-established rivals whereas additionally offering them with a ransomware pattern that normally works correctly. The LockBit connection, nevertheless, just isn’t the one one we’ve got noticed.
In June, we investigated an incident involving ScRansom. From our telemetry, we had been in a position to collect the next:
- On June 3rd, 2024 CosmicBeetle tried to compromise a producing firm in India with ScRansom.
- After failing, CosmicBeetle tried quite a lot of process-killing instruments to take away EDR safety, specifically:
- On June 8th, 2024, RansomHub’s EDR killer was executed on the identical machine.
- On June 10th, 2024, RansomHub was executed on the identical machine.
The best way RansomHub’s EDR killer was executed could be very uncommon. It was manually extracted by way of WinRAR from an archive saved at C:UsersAdministratorMusic1.0.8.zip and executed. Such execution could be very uncommon for RansomHub associates. Then again, utilizing the Music folder and manually extracting and executing payloads actually is typical CosmicBeetle conduct.
To our data, there aren’t any public leaks of RansomHub code or its builder (although RansomHub itself might be primarily based on code purchased from Knight, one other ransomware gang). Subsequently, we consider with medium confidence that CosmicBeetle enrolled itself as a brand new RansomHub affiliate.
Technical evaluation
Just like the remainder of CosmicBeetle’s customized arsenal, ScRansom is written in Delphi. The earliest samples we had been in a position to acquire had been compiled on the finish of March 2023, although, to the very best of our data, in-the-wild assaults didn’t begin earlier than August. ScRansom is underneath ongoing growth.
The GUI is typical for Delphi functions, although not a lot for ransomware. All ScRansom samples comprise a structured GUI. The older samples, normally named “Static” by the builders, require consumer interplay to truly encrypt something. Whereas this may increasingly appear a complication, it could be one of many explanation why ScRansom evaded detection for a while, as operating such samples in evaluation sandboxes doesn’t show any malicious exercise.
Launching such an encryptor requires the risk actor to have entry to the sufferer’s display and be capable to manipulate their mouse. This isn’t the primary time CosmicBeetle has used this method – ScHackTool can be a instrument that must be executed on the sufferer’s machine and requires handbook interplay. We’re not fully certain how CosmicBeetle achieves this purpose, however guessing from the opposite instruments used, we consider utilizing VPN entry with beforehand stolen credentials and RDP is probably the most possible situation.
CosmicBeetle additionally has experimented with a hardly ever seen variant named “SSH”. The encryptor logic is equivalent to the opposite variants, however as an alternative of encrypting native recordsdata, it encrypts recordsdata over FTP.
Newer builds make the most of automation, although solely by simulating clicking the right buttons from code. These automated builds, named “Auto” by the builders, are normally bundled inside an MSI installer along with small instruments or scripts to delete shadow copies. The GUI is hidden by default; its most up-to-date model is illustrated in Determine 6.
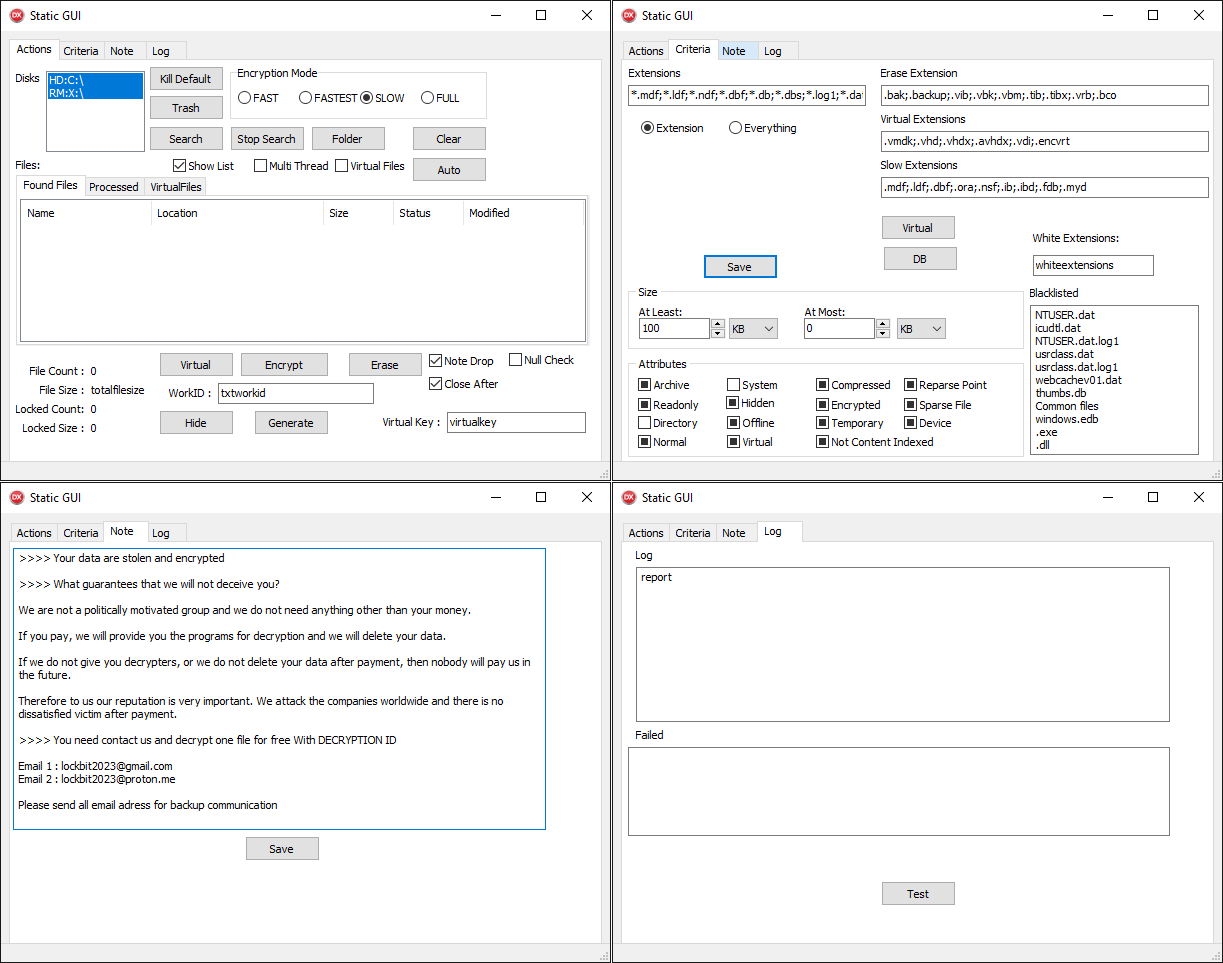
A posh GUI with a number of buttons, a few of which do nothing, is typical for CosmicBeetle. Whereas the GUI with 4 tabs appears to be like advanced, the performance is definitely very simple. ScRansom encrypts recordsdata on all fastened, distant, and detachable drives primarily based on a hardcoded checklist of extensions (see Appendix A: Focused file extensions) – this checklist might be modified by way of the textual content field labeled Extensions.
ScRansom employs partial encryption – solely elements of the file are encrypted. 5 encryption modes are supported:
- FAST
- FASTEST
- SLOW
- FULL
- ERASE
The primary 4 modes merely differ in how the ransomware decides what parts of the file to encrypt. Their utilization appears to nonetheless be partially in growth, as not the entire modes are used. The final mode, ERASE, is necessary, nevertheless – when utilized, chosen parts of focused recordsdata aren’t encrypted however their contents are changed with a relentless worth, rendering these recordsdata unrecoverable. Which mode is utilized for a given file is set both by way of the radio buttons within the Actions tab or by way of the inclusion of its extension within the Standards tab. The extensions checklist labeled Digital Extensions triggers a unique encryption perform that, nevertheless, is equivalent to the common one. As you most likely guessed, White Extensions ought to outline a listing of extensions excluded from encryption, although this characteristic just isn’t carried out.
Apart from encrypting, ScRansom additionally kills numerous processes and companies (see Appendix B: Processes killed and Appendix C: Companies killed). Lately, a brand new Delphi pattern was break up off from ScRansom into a component that we named ScKill, whose sole function is to kill processes. ScRansom additionally employs debug-like options like loading a listing of extensions to encrypt from an ext.txt file and ransom observe content material from a observe.txt file.
Encryption
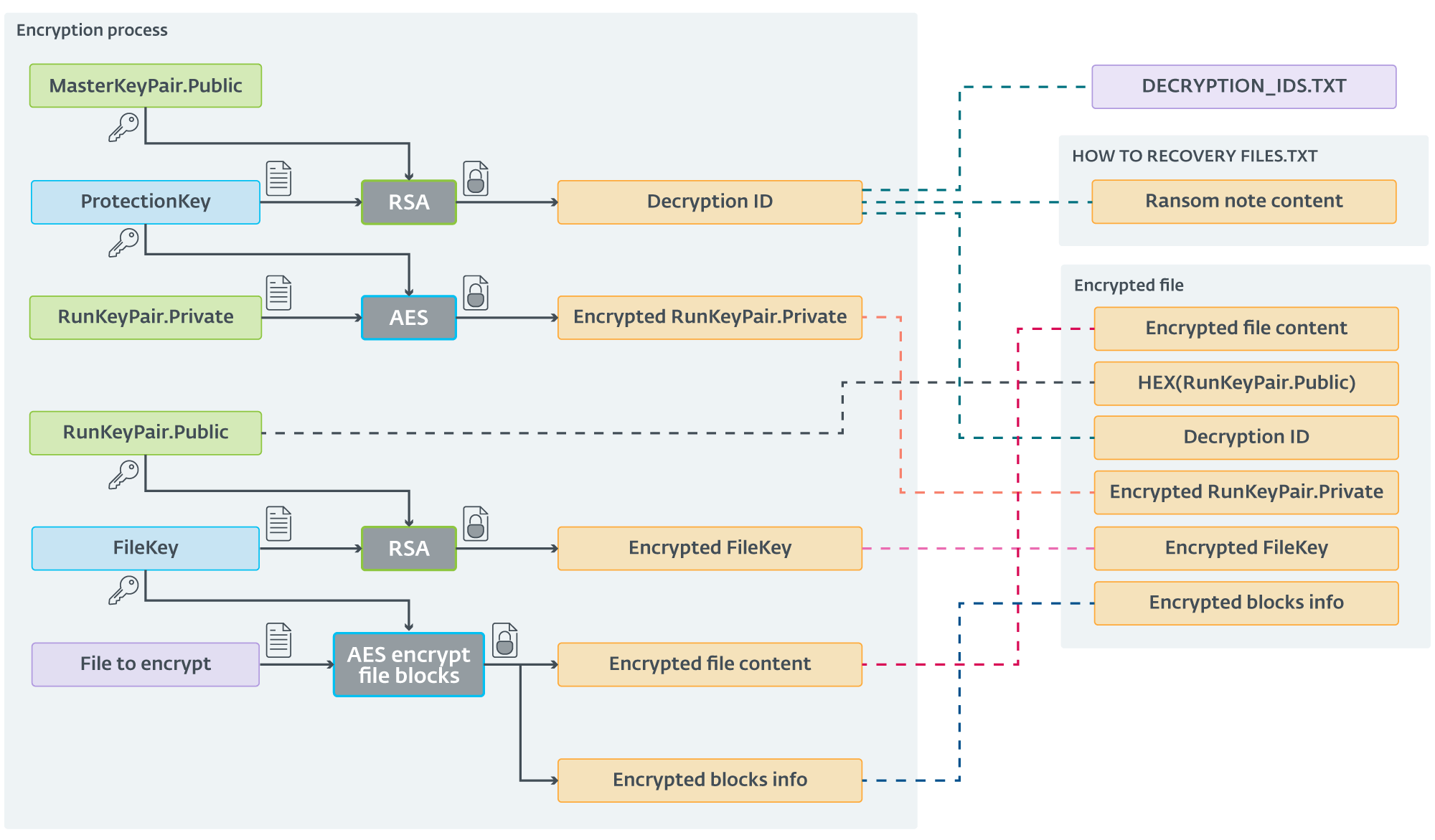
Preliminary ScRansom samples utilized easy symmetric encryption utilizing AES-CTR-128. Since December 2023, the encryption scheme has been up to date. The brand new scheme is sort of (unnecessarily) advanced. ScRansom, at the beginning, generates an AES key we are going to name ProtectionKey, and an RSA-1024 key pair we are going to name RunKeyPair.
Each ScRansom pattern utilizing this new scheme incorporates a hardcoded public RSA key from a pair we are going to name MasterKeyPair. This public secret is encrypted utilizing RSA into what CosmicBeetle calls Decryption ID.
For each file, an AES-CTR-128 key that we’ll name FileKey is generated. Parts of the file are then encrypted utilizing AES with FileKey. When ScRansom finishes encrypting a file, it appends knowledge to its finish, particularly:
- The string TIMATOMA (or TIMATOMAFULL if the entire file was encrypted).
- The string TBase64EncodingButton12ClickTESTB64@#$% (TESTB64 in older builds), encrypted by AES utilizing FileKey.
- The next entries, delimited by $ (a greenback signal):
- Hex-encoded RunKeyPair.Public,
- Decryption ID,
- RunKeyPair.Non-public, encrypted utilizing AES-CTR-128 with ProtectionKey, and
- FileKey, encrypted utilizing RSA with RunKeyPair.Public.
- Details about encrypted blocks begin and their size (absent if the complete file is encrypted).
Lastly, Decryption ID is saved right into a textual content file named DECRYPTION_IDS.TXT and in addition written within the ransom observe named HOW TO RECOVERY FILES.TXT. Decryption ID is totally different every time the encryptor is executed. On subsequent execution(s), the Decryption IDs are appended to the DECRYPTION_IDS.TXT file, however not up to date within the ransom observe.
The filename (together with extension) is then base64 encoded and the .Encrypted extension appended. Regardless of the complexity of the entire course of, we’ve got summarized it in Determine 7.
Decryption
We had been in a position to acquire a decryptor carried out by CosmicBeetle for this latest encryption scheme. CosmicBeetle doesn’t present its victims with the MasterKeyPair.Non-public key however with the already decrypted ProtectionKey (that must be entered within the discipline labeled CPriv Aes Key). Moreover, the decryptor expects the Decryption ID, which is ineffective, because the personal key just isn’t supplied; certainly, the decryptor ignores its worth. The GUI of the decryptor is illustrated in Determine 8.
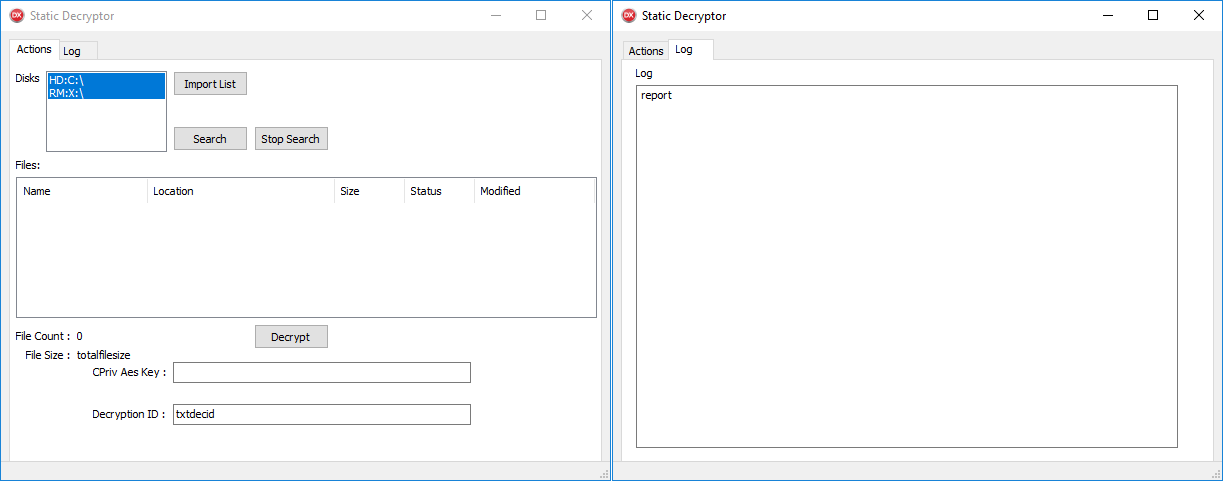
If the right ProtectionKey is entered, the decryptor works as anticipated. If victims resolve to pay the ransom, they should gather all Decryption IDs from all the machines the place ScRansom was executed. CosmicBeetle then wants to offer a unique ProtectionKey for the entire Decryption IDs. Victims then have to manually run the decryptor on each encrypted machine, enter the right ProtectionKey (or strive all of them), click on the Decrypt button and anticipate the decryption course of to complete.
Furthermore, from collaboration with one of many victims, we realized that ScRansom was executed greater than as soon as on some machines, resulting in much more Decryption IDs. This sufferer collected 31 totally different Decryption IDs, requiring 31 ProtectionKeys from CosmicBeetle. Even with these, they had been unable to completely get better all of their recordsdata. Assuming the encrypted recordsdata weren’t tampered with, this can be the results of lacking some Decryption IDs, CosmicBeetle not offering the entire required ProtectionKeys, or ScRansom destroying some recordsdata completely by utilizing the ERASE encryption mode. This decryption method is typical for an immature ransomware risk actor.
Seasoned gangs want to have their decryption course of as straightforward as attainable to extend the possibilities of right decryption, which boosts their fame and will increase the probability that victims pays. Sometimes (like within the case of the leaked LockBit Black builder), a decryptor is constructed along with an encryptor. When distributed to the sufferer, no further consumer effort is required, as the hot button is already contained within the binary. Moreover, one secret is ample to decrypt all encrypted recordsdata, no matter the place they’re within the sufferer’s community.
Conclusion
On this blogpost, we’ve got analyzed CosmicBeetle’s exercise over the previous yr. The risk actor remains to be deploying ransomware, although it switched from Scarab to a brand new customized household we name ScRansom. Most likely because of the obstacles that writing customized ransomware from scratch brings, CosmicBeetle tried to leech off LockBit’s fame, presumably to masks the problems within the underlying ransomware and in flip to extend the possibility that victims pays.
We additionally noticed CosmicBeetle making an attempt to deploy LockBit samples constructed utilizing the leaked builder, although solely briefly, earlier than switching again to ScRansom. The risk actor places efforts into continuous growth of ScRansom, altering encryption logic and including options.
Lately, we noticed the deployment of ScRansom and RansomHub payloads on the identical machine solely every week aside. This execution of RansomHub was very uncommon in comparison with typical RansomHub instances we’ve got seen in ESET telemetry. Since there aren’t any public leaks of RansomHub, this leads us to consider with medium confidence that CosmicBeetle could also be a latest affiliate of RansomHub.
ScRansom undergoes ongoing growth, which isn’t a superb sign up ransomware. The overcomplexity of the encryption (and decryption) course of is vulnerable to errors, making restoration of all recordsdata uncertain. Profitable decryption depends on the decryptor working correctly and on CosmicBeetle offering all essential keys, and even in that case, some recordsdata could have been destroyed completely by the risk actor. Even within the best-case situation, decryption will probably be lengthy and sophisticated.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis gives personal APT intelligence reviews and knowledge feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
Recordsdata
| SHA-1 | Filename | Detection | Description |
| 4497406D6EE7E2EF561C 949AC88BB973BDBD214B |
auto.exe | Win32/Filecoder.Spacecolon.A | Auto variant of ScRansom. |
| 3C32031696DB109D5FA1 A09AF035038BFE1EBE30 |
Project1.exe | Win32/Filecoder.Spacecolon.B | Auto variant of ScRansom. |
| 26D9F3B92C10E248B7DD 7BE2CB59B87A7A011AF7 |
New.exe | Win32/Filecoder.Spacecolon.A | Static variant of ScRansom. |
| 1CE78474088C14AFB849 5F7ABB22C31B397B57C7 |
Project1.exe | Win32/Filecoder.Spacecolon.B | Auto encryptor variant of ScRansom, Turkish ransom observe. |
| 1B635CB0A4549106D8B4 CD4EDAFF384B1E4177F6 |
Project1.exe | Win32/Filecoder.Spacecolon.A | Static SSH encryptor variant of ScRansom. |
| DAE100AFC12F3DE211BF F9607DD53E5E377630C5 |
Project1.exe | Win32/Filecoder.Spacecolon.A | Decryptor variant of ScRansom (oldest). |
| 705280A2DCC311B75AF1 619B4BA29E3622ED53B6 |
Rarlab_sib.msi | Win32/Filecoder.Spacecolon.A Win32/Filecoder.Spacecolon.B BAT/DelShad.E BAT/Agent.OPN |
MSI file with embedded ScRansom, ScKill, BAT script to cease companies, and BAT script to delete shadow copies. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 66.29.141[.]245 | www.lockbitblog[.]information | Namecheap, Inc. | 2023‑11‑04 | Faux LockBit leak website. |
Ransom observe fragments
Electronic mail addresses
- decservice@ukr[.]internet
- nonamehack2024@gmail[.]com
- tufhackteam@gmail[.]com
- nonamehack2023@gmail[.]com
- nonamehack2023@tutanota[.]com
- lockbit2023@proton[.]me
- serverrecoveryhelp@gmail[.]com
- recoverydatalife@gmail[.]com
- recoverydatalife@mail[.]ru
Tox IDs
- 91E3BA8FACDA7D4A0738ADE67846CDB58A7E32575531BCA0348EA73F6191882910B72613F8C4
- A5F2F6058F70CE5953DC475EE6AF1F97FC6D487ABEBAE76915075E3A53525B1D863102EDD50E
- F1D0F45DBC3F4CA784D5D0D0DD8ADCD31AB5645BE00293FE6302CD0381F6527AC647A61CB08D
- 0C9B448D9F5FBABE701131153411A1EA28F3701153F59760E01EC303334C35630E62D2CCDCE3
Tor hyperlinks
- http://nonamef5njcxkghbjequlibwe5d3t3li5tmyqdyarnrsryopvku76wqd[.]onion
- http://noname2j6zkgnt7ftxsjju5tfd3s45s4i3egq5bqtl72kgum4ldc6qyd[.]onion
- http://7tkffbh3qiumpfjfq77plcorjmfohmbj6nwq5je6herbpya6kmgoafid[.]onion
MITRE ATT&CK strategies
This desk was constructed utilizing model 15 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Reconnaissance | T1595.002 | Lively Scanning: Vulnerability Scanning | CosmicBeetle scans its targets for a listing of vulnerabilities it may possibly exploit. |
| T1590.005 | Collect Sufferer Community Data: IP Addresses | CosmicBeetle scans the web for IP addresses weak to the vulnerabilities it may possibly exploit. | |
| Useful resource Improvement | T1583.001 | Purchase Infrastructure: Domains | CosmicBeetle registered its personal leak website area. |
| T1587.001 | Develop Capabilities: Malware | CosmicBeetle develops its customized toolset, Spacecolon. | |
| T1588.002 | Acquire Capabilities: Instrument | CosmicBeetle makes use of a big number of third-party instruments and scripts. | |
| T1588.005 | Acquire Capabilities: Exploits | CosmicBeetle makes use of publicly out there PoCs for identified exploits. | |
| T1588.001 | Acquire Capabilities: Malware | CosmicBeetle most likely obtained ransomware from RansomHub and the leaked LockBit 3.0 builder. | |
| Preliminary Entry | T1190 | Exploit Public-Dealing with Utility | CosmicBeetle positive aspects preliminary entry by exploiting vulnerabilities in FortiOS SSL-VPNand different public-facing functions. |
| Execution | T1204 | Person Execution | CosmicBeetle depends on consumer execution for a few of its instruments, although that is normally executed by the risk actor by way of RDP. |
| T1059.003 | Command and Scripting Interpreter: Home windows Command Shell | CosmicBeetle executes numerous BAT scripts and instructions. | |
| T1059.001 | Command and Scripting Interpreter: PowerShell | CosmicBeetle executes numerous PowerShell scripts and instructions. | |
| Persistence | T1136.001 | Create Account: Native Account | CosmicBeetle typically creates an attacker-controlled administrator account. |
| Protection Evasion | T1078 | Legitimate Accounts | CosmicBeetle abuses legitimate accounts whose credentials it efficiently obtains. |
| T1140 | Deobfuscate/Decode Recordsdata or Data | ScRansom samples defend public RSA keys by encryption. | |
| Credential Entry | T1110.001 | Brute Power: Password Guessing | CosmicBeetle makes use of RDP and SMB brute-force assaults. |
| T1212 | Exploitation for Credential Entry | CosmicBeetle exploits identified vulnerabilities to acquire credentials. | |
| Impression | T1485 | Information Destruction | CosmicBeetle renders some encrypted recordsdata unrecoverable. |
| T1486 | Information Encrypted for Impression | CosmicBeetle encrypts delicate recordsdata on compromised machines. |
Appendix A: Focused file extensions
This configuration is hardcoded in each ScRansom pattern and is topic to frequent change. The next sections comprise the latest configuration on the time of writing.
Filename masks to encrypt
| *._ms *.0001 *.001 *.002 *.003 *.004 *.005 *.006 *.007 *.008 *.1* *.2* *.3* *.3dm *.3dmbak *.3ds *.4* *.5* *.6* *.7* *.7z *.8* *.9* *.a01 *.a02 *.a03 *.a06 *.accdb *.ACD *.adm *.afi *.ai *.alt *.arc *.arc *.archive *.ard *.asm *.avhdx *.avi *.axf *.b1 *.bac *.backup *.bak *.BBCK *.BBCK3 *.bck *.bco *.bdmp *.bi4 *.bik *.bin *.bkf *.bkp |
*.bkup *.mix *.field *.bpf *.btr *.bup *.c1 *.cbd *.cbu *.cdr *.cdx *.cfgbak *.cgd *.sofa *.csv *.ctf *.d0 *.d1 *.d2 *.d3 *.d4 *.da1 *.da2 *.da3 *.da4 *.hazard *.dat *.db *.db1 *.db2 *.dbc *.dbdmp *.dbf *.dbs *.dbw *.df *.dft *.diff *.dmp *.doc *.docx *.dwg *.dxf *.dxt5_2d *.ebk *.edb *.edp *.elg *.eml *.encvrt *.fbf *.fbk *.fbw *.fdb *.fmp12 |
*.fp5 *.fp7 *.frm *.ful *.full *.fxl *.gan *.gbk *.gdb *.gho *.ghs *.hbp *.hlp *.hrl *.ib *.ibd *.idx *.imd *.indd *.itdb *.iv2i *.jet *.jpg *.L5X *.lbl *.ldb *.ldf *.llp *.log *.log1 *.lst *.mat *.max *.mdb *.mdbx *.mdf *.mmo *.mov *.mp4 *.mrimg *.msg *.mtx *.myd *.myi *.nb7 *.nbf *.ndf *.ndk *.ndx *.nsf *.nsg *.ntf *.nx1 *.nyf *.obk |
*.oeb *.ol2 *.previous *.one *.ora *.ost *.ostx *.ova *.pak *.par *.pbd *.pcb *.pdb *.pod *.ppt *.pptx *.pqb *.pri *.prt *.psd *.psm *.pst *.pstx *.ptb *.qba *.qbb *.qbm *.qbw *.qic *.qrp *.qsm *.qvx *.rar *.uncooked *.rbf *.rct *.rdb *.redo *.rfs *.rman *.rpd *.rpo *.rpt *.rtf *.sai *.saj *.seq *.sev *.sic *.sko *.skp *.SLDASM *.SLDDRW *.SLDLFP |
*.SLDPRT *.sldprt *.sldrpt *.slp *.sna *.sna *.spf *.spl *.sql *.sqlaudit *.sqlite *.sqlite3 *.srd *.step *.stm *.stp *.tar *.tar.gz *.tga *.tgz *.tib *.tibx *.tif *.tiff *.tmp *.trc *.trn *.tuf *.upd *.usr *.vbk *.vbm *.vct *.vcx *.vhd *.vhdx *.vib *.vix *.vmdk *.vmsd *.vmsn *.vmx *.vmxf *.vob *.vrb *.vswp *.wim *.wt *.xls *.xlsm *.xlsx *.zip *ibdata |

