COMMENTARY
Greater than half of chief data safety officers (CISOs) wrestle to successfully talk cyber-risk to their management groups, in line with FTI Consulting. If you happen to’re a part of this majority, you are not alone. I spend numerous hours every month in dialog with CISOs, speaking about their considerations and challenges. Again and again, I hear the identical frustration: translating advanced cyber-risks right into a digestible narrative for management is an uphill battle.
The problem is multifaceted:
-
CISOs are competing for consideration in a sea of enterprise dangers. In lots of fashionable enterprise organizations, safety groups exist alongside enterprise danger administration (ERM) or governance, danger, and compliance (GRC) groups that monitor enterprise danger holistically. Cyber considerations are only one merchandise on a prolonged checklist of priorities, together with financials, broader financial elements, geopolitics, local weather points, and personnel challenges.
-
Conventional danger communication instruments aren’t efficient storytelling automobiles. When ERM or GRC groups assessment danger with management, they usually current warmth maps that scale back complexity, or danger registers that overwhelm with lots of, if not hundreds, of strains of content material. In both case, the nuances of cyber-risk get misplaced within the information, which signifies that leaders are disconnected from the main points that matter.
-
The stakes are increased than ever. With the common price of an information breach reaching $4.88 million in 2024, the necessity for clear, compelling danger communication has by no means been extra vital.
Decoding Cyber-Threat: What Goes Right into a Proximity Resilience Graph
Within the face of rising cyber threats and communication challenges, how can CISOs current their information to management in a clearer, extra compelling means? I like to recommend making a proximity resilience graph — a robust visible device that transforms summary danger information into an enticing, actionable narrative.
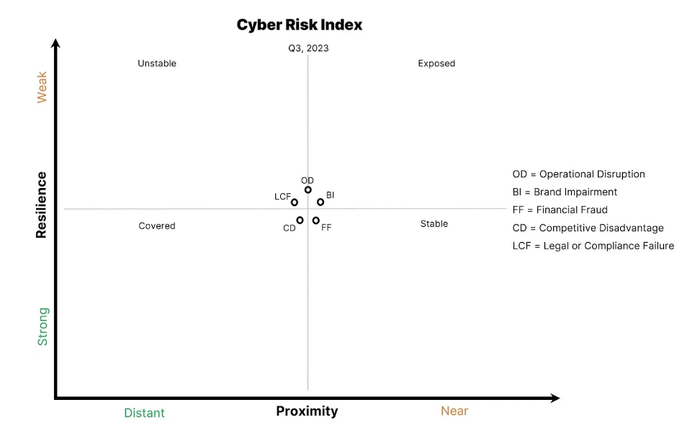
Supply: Recorded Future
Let’s break down the elements of the graph to see why it is so helpful:
The Y-axis, labeled Resilience, represents a company’s cybersecurity muscle. It encompasses all controls, efforts, plans, processes, applied sciences, and assets, going effectively past commonplace GRC checklists. For instance, think about implementing a gamified phishing coaching program. As worker engagement and resilience in opposition to social engineering enhance, you’d see this mirrored in a downward motion alongside the Y-axis. This axis is essential as a result of it showcases the tangible impression of a company’s safety investments and initiatives.
The X-axis, labeled Proximity (as in Assault Proximity), captures the totality of threats surrounding a company. When mapping this axis, a CISO ought to use all the safety and risk information out there to them from inner safety telemetry, exterior risk telemetry, and public cyberattack occasions. As an illustration, if a healthcare firm discovers a spike in ransomware assaults concentrating on its sector, assault proximity would shift proper. Equally, if a producing agency’s safety operations middle (SOC) detects a surge in phishing makes an attempt, that inner telemetry sign would transfer proximity to the suitable as effectively. This axis supplies very important context, exhibiting how inner and exterior elements affect a company’s danger posture.
The graph midlines assist viewers visualize motion, and the highest label is absolutely the reference to anchor time increments. The quantity of motion and the midline labels are versatile, turning it right into a dynamic story that reveals the evolution of a company’s safety posture. A CISO ought to select a time phase that is giant sufficient to point out motion. In the event that they meet quarterly with their board or administrators, they will use the beginning of 1 / 4 because the label.
The quadrant labels — Unstable, Steady, Uncovered, and Lined — are easy and expressive, however a CISO can modify or eradicate them as wanted after seeing their impact on viewers engagement and comprehension.
Lastly, the info factors symbolize the 5 key danger impacts: Operational Disruption, Model Impairment, Monetary Fraud, Aggressive Drawback, and Authorized or Compliance Failure. In the end, the proximity resilience graph supplies worth by highlighting motion, exhibiting whether or not resilience is bettering or getting worse for a selected danger impression. For instance, after a profitable ransomware tabletop train, the Operational Disruption level would shift down on the Y-axis, indicating improved resilience. This granular method permits for nuanced discussions about particular danger areas, somewhat than generalizing all cyber-risk.
On the X-axis, risk classes gas danger impression motion, and it is as much as CISOs to translate how risk classes map to varied danger impacts. For instance, a enterprise e mail compromise (BEC) primarily creates a Monetary Fraud danger impression, however it may additionally set off Model Impairment if the occasion turns into public.
Bridging the Communication Hole: Construct Your Proximity Resilience Graph
Not solely does a proximity resilience graph provide a extra correct illustration of danger than warmth maps and danger registers, it additionally permits CISOs to inform a fancy story in a single visualization. It avoids subjective labels and permits for various interpretations so leaders can see the place and the way resilience is altering and begin asking knowledgeable questions. It additionally eliminates the possibility of cyber-risk getting misplaced within the noise of broader enterprise danger.
A proximity resilience graph enhances leaders’ danger comprehension and engagement, boosts their confidence within the timing of current and future cybersecurity investments, and improves perceptions of the safety workforce’s worth.
_Andriy_Popov_Alamy.jpg?disable=upscale&width=1200&height=630&fit=crop&w=696&resize=696,0&ssl=1)